To block GPS signals with fashion hats, you should seek designs incorporating conductive materials like copper or silver-infused fabrics, which disrupt electromagnetic frequencies. These hats typically create a Faraday cage effect, reflecting and absorbing signals. While they may reduce GPS tracking effectiveness, they don’t guarantee complete blockage. Durability can also diminish with use and washing, impacting performance. Exploring the nuances of materials and designs could reveal better options for enhancing personal privacy in surveillance-heavy environments.
Quick Takeaways
- Choose hats made from metallic fabrics or conductive textiles, like copper-nickel or silver mesh, for effective GPS signal disruption.
- Look for designs with multi-layered materials to enhance shielding and create a Faraday cage effect.
- Ensure a snug fit to maintain continuity of shielding layers and limit signal penetration.
- Opt for hats that feature small mesh patterns to reduce leakage of GPS signals.
- Be aware that hats provide partial signal reduction; consider combining them with other privacy accessories for enhanced protection.
What Are Fashion Hats Designed to Block GPS Signals?

Fashion hats designed to block GPS signals typically incorporate materials like metallic fabrics and conductive textiles to create shielding layers that disrupt signal reception.
These hats utilize design features such as multi-layered materials and strategic placement to effectively reduce GPS frequency penetration. Additionally, some fashion hats may function similarly to the GPS jammers offered by The Signal Jammer, providing users with enhanced privacy.
The hats often include metallic fibers like silver or copper, carbon fiber materials, and metal meshes that function as a Faraday cage. Key design aspects focus on covering the crown and sides of the head, using tight weaves to minimize signal penetration, and sometimes extending brims with shielding fabric.
Common styles include beanies, baseball caps, bucket hats, and visors, all aimed at enhancing privacy and reducing surveillance risks. Their effectiveness can vary based on material quality, but they can also unintentionally block other signals like cellular or Wi-Fi.
How Do Conductive Materials Enhance Signal Blocking in Hats?
Conductive materials enhance signal blocking in hats by creating a Faraday cage effect that reflects and absorbs electromagnetic waves.
The composition, continuity, and thickness of these materials directly impact the reduction of RF signals, including GPS frequencies.
When conductive materials like copper and nickel are woven into fabric, they form a shield that efficiently mitigates incoming signals.
Key factors influencing their effectiveness include:
- Electrical conductivity: Higher conductivity means superior signal attenuation.
- Layer continuity: A seamless or sufficiently thick conductive layer aids in maintaining shielding.
- Mesh patterns: Any openings must be small compared to the wavelength of targeted signals to prevent leakage.
These materials not only offer practical protection but also allow for stylish designs, making wearable technology both functional and appealing.
What Types of Fabrics Are Commonly Used in Signal-Blocking Hats?
Common fabrics used in signal-blocking hats include copper-nickel compositions, silver mesh, and blend fabrics that combine conductive metals with traditional textiles for comfort. These materials effectively block electromagnetic signals while maintaining flexibility and breathability.
Copper and nickel fabrics, such as TitanRF Faraday Fabric, are popular for their outstanding shielding performance against various radio signals, from cell phones to GPS.
Silver mesh fabrics offer over 50 dB of shielding effectiveness and are lightweight, making them ideal for everyday wear.
Blend fabrics combine metals like silver or stainless steel woven into cotton or polyester, ensuring both comfort and functionality.
Flexible fabrics, engineered for durability, adapt well to various hat styles, while specialty shielding textiles enhance protected layers for improved RF absorption. Additionally, anti-facial recognition gear is increasingly being integrated into everyday fashion to further enhance privacy.
How Effective Are Hats at Blocking GPS and Other RF Signals?

Hats with conductive fibers can partially reduce RF signals, including some GPS frequencies, but are generally ineffective as complete blockers against GPS tracking. Their effectiveness varies based on design, material, and fit, rendering them a limited solution for GPS interference.
While such hats may attenuate general RF radiation, they don’t provide reliable protection against low-power GPS signals due to the nature of these frequencies.
Key considerations include:
- GPS signals operate around 1.5 GHz, which can penetrate common materials.
- Complete blocking typically requires active jamming devices that emit powerful signals.
- Signal attenuation from hats is often partial and inconsistent.
- Hats are better suited for reducing general EMF exposure rather than ensuring privacy from GPS tracking.
Can Fashion Hats Shield Against All Types of Tracking Devices?
No, fashion hats with EM shielding fabrics can’t effectively block all types of tracking devices. While they reduce radio frequency emissions, limitations arise from design constraints and the broad spectrum of tracking technologies.
Fashion hats typically integrate materials like copper or silver fibers that are effective against certain radio frequencies, including those used in GPS. However, there are key limitations:
- Tracking devices vary greatly, utilizing diverse frequencies like GSM, Bluetooth, and Wi-Fi.
- Design constraints prevent hats from providing full coverage, leading to potential signal leaks.
- Technologies such as inertial sensors or optical tracking don’t rely on RF signals and remain susceptible.
- Layering and placement are essential but must achieve a balance with comfort and breathability.
Ultimately, while EM shielding hats can reduce some exposure, they can’t guarantee extensive protection against all forms of tracking. Users need to evaluate additional protective measures for greater efficacy.
What Frequency Ranges Do GPS Trackers Operate Within?
GPS trackers operate primarily on cellular network frequencies, usually within 850 MHz to 2600 MHz, depending on the technology.
They may also utilize short-range communication bands like Wi-Fi (2.4 GHz and 5 GHz) and Bluetooth (2.4 GHz).
These trackers use various frequency bands for data transmission, including GSM (850, 900, 1800, 1900 MHz), 3G (850–2100 MHz), and 4G/LTE (700–2600 MHz).
Advanced trackers can also use emerging technologies like LoRa and Sigfox, which operate between 868 MHz and 915 MHz.
Therefore, effective detection requires monitoring a broad frequency range spanning from about 13.56 MHz to 6 GHz.
Are Tin Foil Hats Effective for Signal Blocking?
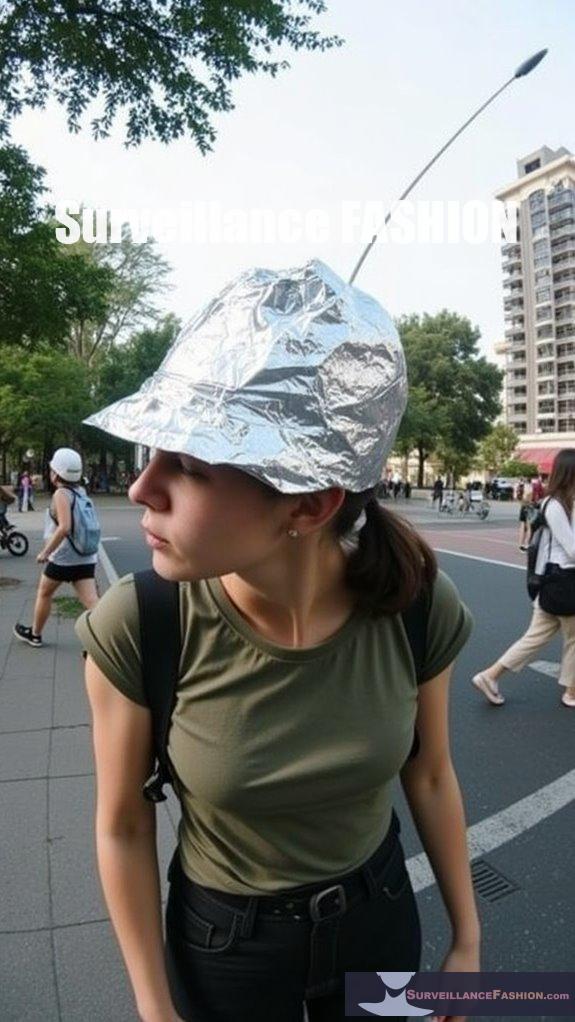
Tin foil hats can disrupt GPS signals but are unlikely to block them completely. Their effectiveness largely depends on coverage, thickness, and environmental factors.
While tin foil can reflect and absorb radio waves, it only creates a partial Faraday cage effect. Signal strength, gaps in coverage, and movement can greatly decrease its blocking efficiency.
Furthermore, environmental interference from buildings or foliage can further complicate performance. For better results, consider using a fully enclosed metal container or purpose-built Faraday cages instead of relying solely on tin foil hats.
How Do Hats Function as Partial Faraday Cages?
Hats function as partial Faraday cages by embedding conductive materials like silver or copper in their fibers, which redistribute electromagnetic waves and reduce their penetration to the scalp.
While these conductive layers interrupt incoming EM frequencies, they don’t provide complete enclosure, limiting their effectiveness to the head area.
The design of these hats typically consists of multiple fabric layers, combining breathable materials with conductive fibers.
The outer layer is often cotton or another lightweight fabric, while the inner layer features the conductive mesh. This structure aims to maintain comfort while maximizing shielding efficiency.
Key points include:
- The effectiveness can vary based on the quality of the conductive fiber and fabric density.
- Independent testing may show over 99% reduction in EMF radiation across multiple frequencies.
- Openings around the face and neck can compromise full shielding, allowing some signal leakage.
Additionally, proper conductive material selection is critical, as it determines the overall performance and comfort of the hat.
Ultimately, these hats serve to reduce exposure to radio frequency radiation in everyday environments, particularly for those concerned about non-ionizing radiation.
What Are the Limitations of Using Hats for Signal Blocking?
Hats designed for fashion with metallic fibers offer only partial GPS signal attenuation and aren’t fully effective in blocking signals due to gaps, fabric limitations, and environmental influences.
These hats can’t create a complete Faraday cage because textile materials inherently allow some signal penetration. Gaps in the fabric, seams, and the open design of hats mean that signals from other directions may still reach the GPS receiver.
Furthermore, external factors like nearby buildings or trees can further diminish blocking effectiveness.
Key limitations include:
- Reduced effectiveness due to low conductivity of materials.
- Inability to block signals from other body devices like cell phones.
- Legal standing as passive attenuators versus active jammers.
- The durability of metal-infused fabric decreases with use and washing, leading to diminished shielding over time.
Thus, while fashionable hats provide some level of protection, they don’t guarantee complete privacy from GPS tracking.
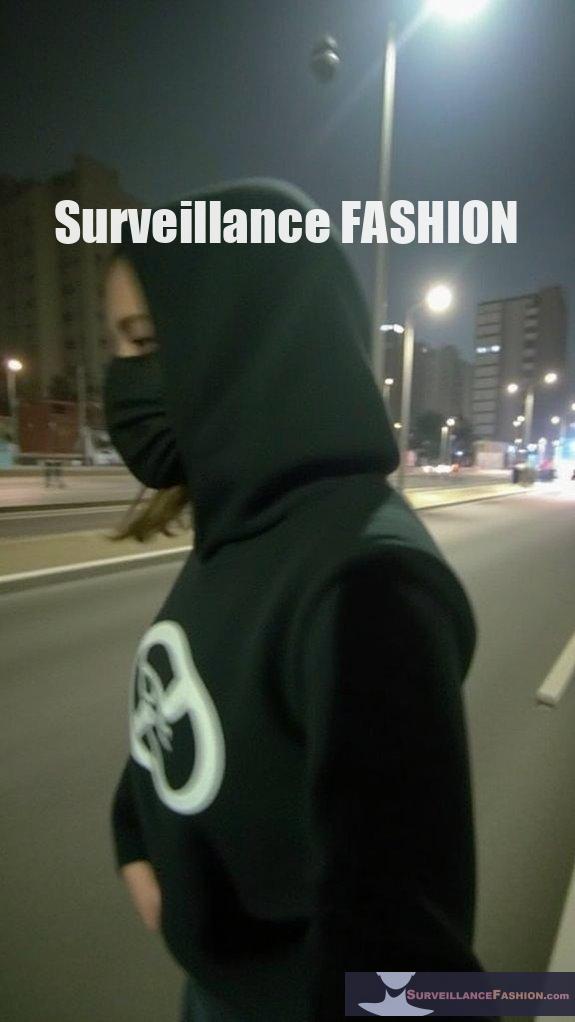
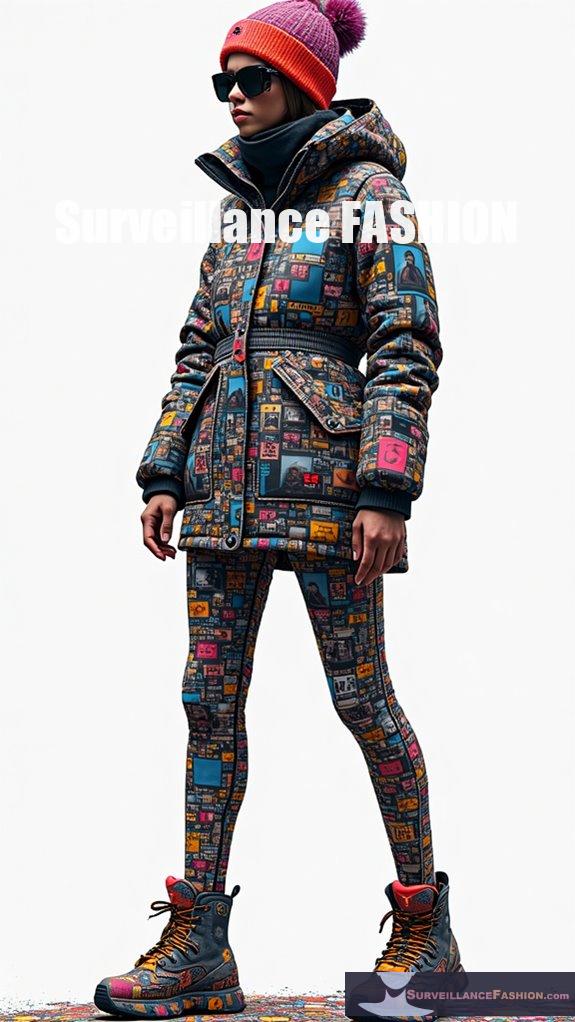
How Can Combining Fashion Items Enhance Overall Privacy Protection?
Combining fashion items enhances overall privacy protection by creating layered obstacles against various surveillance methods, including biometric identification and signal tracking.
Strategically pairing accessories with complementary materials increases coverage and effectiveness while maintaining style.
By incorporating elements like hats with signal-blocking features alongside garments with visually disruptive patterns, individuals can effectively safeguard their identity and location.
This synergy allows for:
- Distortion of facial recognition capabilities.
- Blocking GPS and wireless signals.
- Coordinated aesthetics to avoid drawing attention to privacy measures.
- Dynamic responses to detected threats, optimizing protection in real-time.
This layered approach guarantees both visual anonymity and robust data protection without compromising personal style.
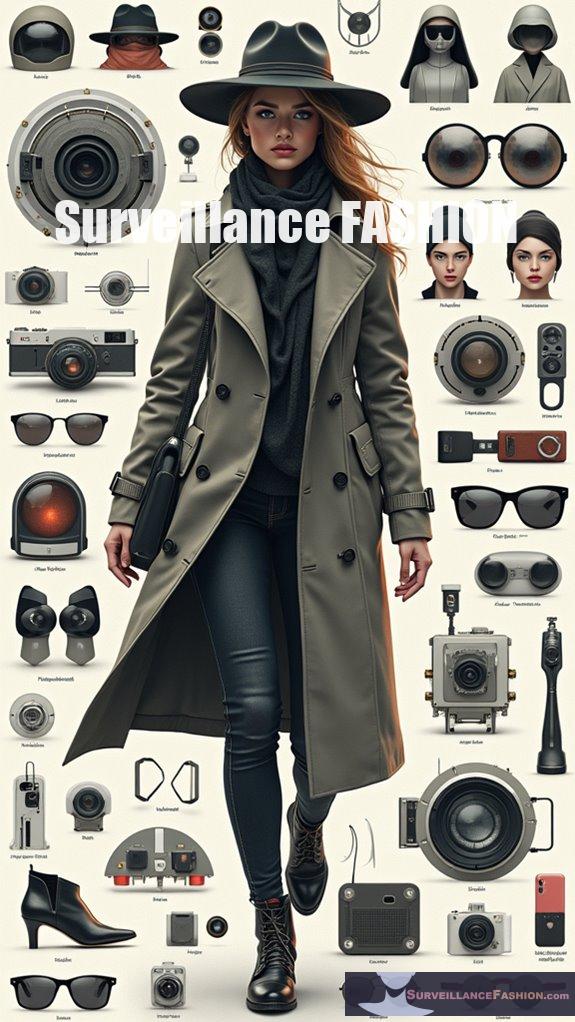
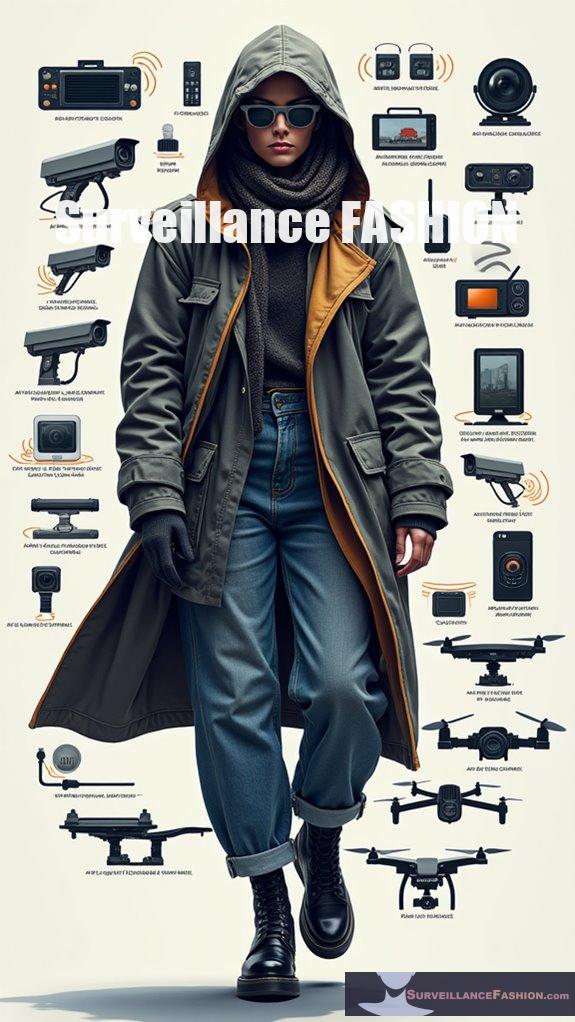
What Other Fashion Accessories Provide Signal-Blocking Benefits?
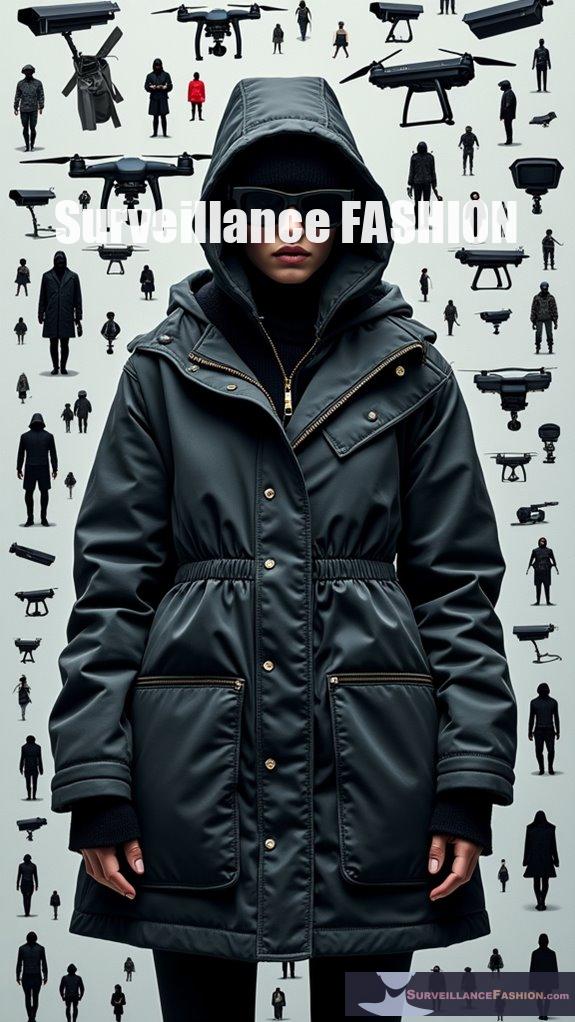
Several fashion accessories offer signal-blocking benefits, including jackets, bags, jewelry, and scarves made with conductive materials.
These items can help attenuate GPS and RF signals, enhancing privacy.
Jackets and coats embedded with metalized fibers function as wearable shields against various signals, while signal-blocking bags entirely safeguard devices when enclosed.
Jewelry can provide partial attenuation but is generally less effective due to limited coverage.
Scarves and gloves serve as fashionable supplements, creating localized barriers against tracking devices.
How Do Urban Design and Style Influence Signal Blocking Effectiveness?
Urban design and style greatly influence GPS signal blocking effectiveness through the arrangement of buildings and the choice of hat materials. Dense urban environments, characterized by high-rises and narrow streets, enhance the potential for signal attenuation. However, the actual effectiveness of a hat in blocking GPS signals depends on its material properties and design.
Urban features such as high-rise buildings create multipath effects that reflect and scatter GPS signals, leading to diminished reception. Dense urban canyons restrict the line-of-sight access to satellites, making signal dropouts more prevalent.
Hats incorporating metallic fibers, like silver or copper, can effectively block signals due to their conductive properties. However, their effectiveness is also influenced by:
- Fabric thickness and weave density, where tighter weaves block signals more efficiently.
- The presence of linings or multiple layers, which enhance absorption and reflection.
- Design coverage, like full-coverage beanies compared to partial caps, affecting the extent of signal blockage.
Additionally, urban style trends can dictate the choice of materials that may either enhance or reduce the functionality of hats in blocking GPS signals.
Data Protection vs. Public Safety
As privacy concerns rise, especially amid increasing surveillance and data collection practices, the tension between data protection and public safety becomes more pronounced, revealing the complex interplay between individual rights and communal security.
While GPS jamming serves as a method to shield personal data from unwarranted tracking, it imperils critical services reliant on accurate positioning, exemplifying the intricate legal and ethical dilemmas that arise.
Regulatory frameworks across various jurisdictions deem GPS interference illegal due to the associated risks; however, advancements in technologies like multi-constellation receivers highlight the potential for concurrent solutions that prioritize both personal privacy and the essential operational integrity of public safety infrastructures.
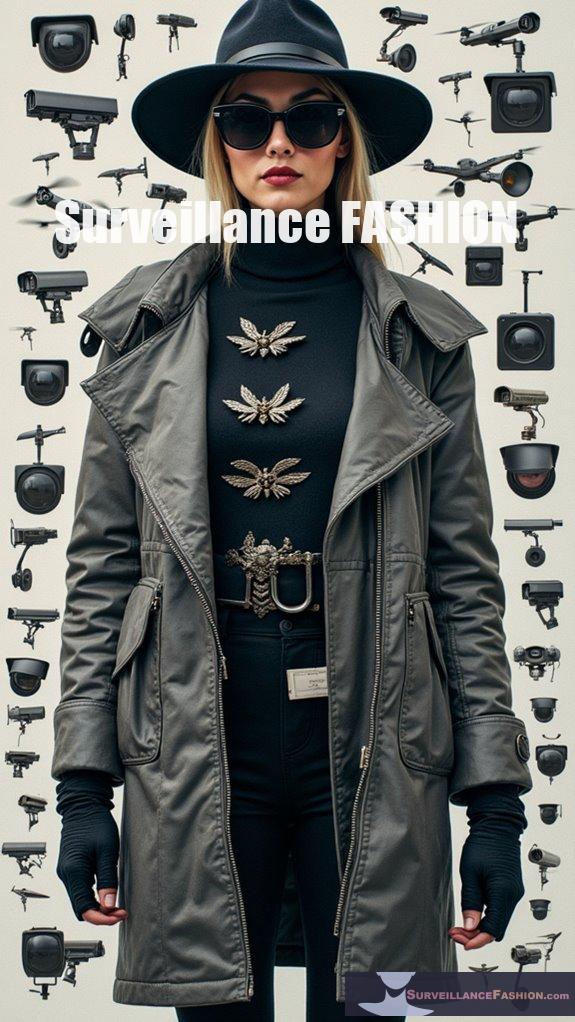
Facial Recognition Cameras Everywhere
Although you may often pass by facial recognition cameras without a second thought, their growing presence raises substantial questions regarding privacy and surveillance in contemporary society.
As governments increasingly deploy facial recognition technology in airports, schools, and law enforcement, you might consider how it affects your daily life.
With a projected market growth from USD 3.78 billion in 2025 to USD 15.73 billion by 2032, the quest for enhanced security seemingly outweighs concerns about personal privacy, particularly as 59% of Americans support its use by law enforcement.
Yet, as technology evolves, so too should our awareness of its implications.
Fashion Hats Blocking Gps Trackers
While you might enjoy the aesthetic appeal of fashion hats, they can also serve a critical function in protecting your privacy by blocking GPS trackers. Incorporating metallic fabrics—like aluminum-infused cloth—can effectively reflect or absorb GPS signals, thereby hindering accurate tracking.
Moreover, lining hats with conductive materials, such as copper threads, elevates this protective capability.
You’ll find that employing techniques based on the Faraday cage principle can physically shield signals through enclosed metallic mesh, creating a barrier against unwanted GPS communication.
Eyes Everywhere: Anti-Surveillance Ebook review
In “Eyes Everywhere,” Sarah Leah Whitson and her collaborators explore the pervasive domain of camera surveillance, dissecting its implications for societal norms and personal freedoms.
They scrutinize how governmental and corporate interests intertwine, resulting in vast data collection and digital tracking, often at the expense of individual rights.
Using whistleblower accounts and legal precedents, Whitson highlights surveillance’s subtle normalization, particularly its disproportionate targeting of marginalized groups.
As surveillance technologies proliferate—mirroring the rationale behind our website, Surveillance Fashion—resistance is critical.
Readers are urged to contemplate ethical alternatives that prioritize human rights, thereby fostering a dialogue on privacy’s future.
References
- https://surveillancefashion.com/privacy-fashion-accessories-against-surveillance/
- https://www.youtube.com/watch?v=F2fgedxCHp4
- https://interferencetechnology.com/research-proves-tin-foil-hats-do-prevent-increase-ease-of-mind-control/
- https://www.youtube.com/watch?v=PYgS0MSTWRk
- https://www.stratecta.exchange/fashion-that-can-beat-facial-recognition-systems/
- https://www.thesignaljammer.com/product-category/gps-jammers/
- https://www.youtube.com/watch?v=sAjWJbZOq6I
- https://havnwear.com
- https://www.showven.cn/?t=27835669041340&mod=7a99d93f&uri=goods.php?id=931620-238&name=gps+signal+blocking+box+for+phones
- https://www.etsy.com/market/gps_blocking
- https://mosequipment.com/products/titanrf-faraday-fabric
- https://fernwaysolutions.com/513538/Protection-Conductive-Fabric-For-Smart-Meters-Prevent-From
- https://en.wikipedia.org/wiki/Faraday_cage
- https://havnwear.com/blog/what-is-faraday-fabric-made-of
- https://supplyleader.com/emf-protection-fabric
- https://cdfs.com.au/product/mission-darkness-emf-blackout-hat/
- https://qmcc.org/Anti-Radiation-Cap-Protects-Against/511028
- https://lessemf.com/product-category/emf-shielding/fabrics-textiles/
- https://safran-navigation-timing.com/how-common-is-gps-jamming-and-how-to-protect-yourself/
- https://www.jammer-store.com/effectiveness-of-gps-jammers-and-blockers.html