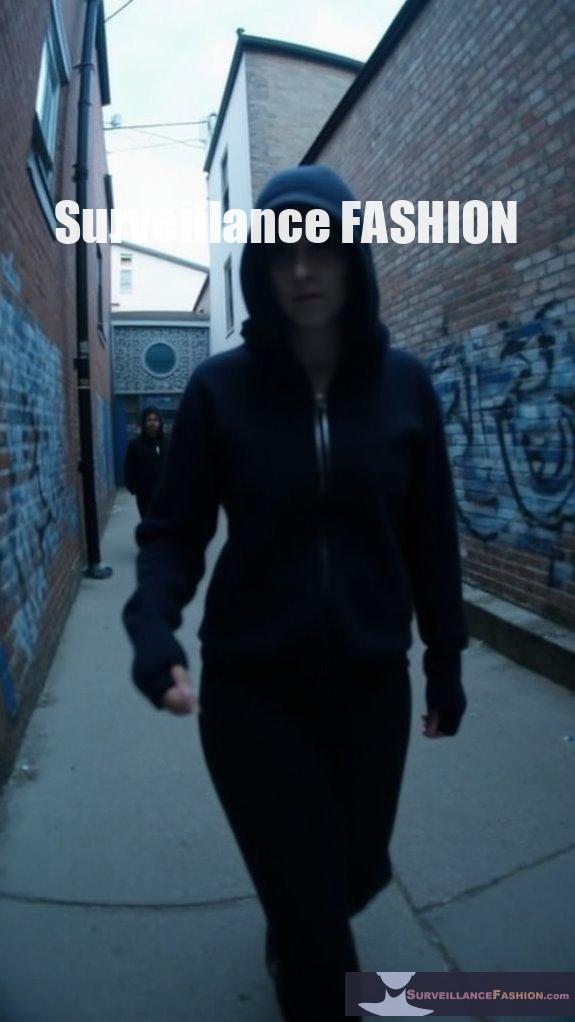
Using anti-surveillance hoodies, you can effectively shield your identity from pervasive surveillance technologies. These garments utilize infrared LEDs, which emit invisible light to disrupt camera sensors, leading to facial feature obfuscation. Furthermore, they incorporate adversarial patterns to confuse facial recognition algorithms. However, their effectiveness diminishes in daylight, as natural light overwhelms IR signals. By exploring further, you’ll uncover various functionalities and innovative designs that can enhance your privacy while traversing increasingly monitored urban environments.
Quick Takeaways
- Anti-surveillance hoodies use infrared LEDs to disrupt cameras, enhancing user anonymity in high-surveillance environments.
- Features like adversarial patterns confuse facial recognition algorithms, increasing personal privacy.
- Designed for urban settings, they protect against both daytime and nighttime surveillance techniques.
- Some models include customizable electronics and DIY options for personalized use.
- Consider limitations such as reduced effectiveness in daylight and vulnerability to biometric identification methods.
What Are Anti-Surveillance Hoodies and How Do They Work?

These hoodies typically incorporate various technologies to counteract surveillance, such as:
- Infrared (IR) LEDs that emit invisible light, overwhelming cameras,
- Adversarial patterns that disrupt AI facial recognition algorithms,
- Blocking fabrics to shield against electronic tracking,
- Design features like double-lined hoods and strategic lighting for maximum effectiveness. Additionally, some designs, like the Camera Shy Hoodie, are aimed at making the wearer unrecognizable in security footage. The integration of privacy-enhancing eyewear can further complement these hoodies, enhancing the overall effectiveness against surveillance. Their performance can vary based on the type of camera and environmental factors, highlighting the ongoing debates surrounding privacy in public spaces.
How Do Built-In Infrared LEDS Contribute to Facial Feature Obfuscation?
Built-in infrared LEDs contribute to facial feature obfuscation by emitting invisible light that saturates camera sensors, resulting in loss of detail and overexposure in captured images. This disruption hinders facial recognition algorithms from accurately identifying key features. The camera shy hoodie is designed specifically to maximize this effect by integrating high-powered infrared LEDs.
The strategic placement and operation of these IR LEDs amplify their effectiveness. When positioned near the face, they flood the camera’s view, creating overly bright regions that confuse auto-exposure settings. Additionally, using anti-surveillance techniques such as these can significantly enhance personal privacy in increasingly monitored environments.
Key points include:
- Strobing patterns create fluctuating brightness, complicating stable image capture.
- The IR halo effect isolates facial features from their surroundings.
- Placement around the hoodie facilitates consistent illumination from multiple angles.
Ultimately, this combination of techniques makes it difficult for surveillance systems to capture clear images of the wearer, effectively masking their identity.
What Is the Effectiveness of Strobing Patterns Against Facial Recognition Technology?
Strobing patterns enhance the effectiveness of liveness detection in facial recognition technology by generating unpredictable light reflections that differentiate between genuine faces and spoofing attempts. Their use in conjunction with neural networks improves spoof detection accuracy. The unpredictability of strobing patterns reduces the likelihood of successful replay attacks using static images or videos. Genuine faces reflect light uniformly, while forgeries typically show delays in reflection due to processing time. Neural networks further analyze these light reflection patterns to detect subtle discrepancies that indicate spoofing. Additionally, these techniques rely on reflected light to ensure an accurate distinction between authentic and counterfeit responses. Recent studies suggest that biometric spoofing is increasingly becoming a challenge for identification systems, highlighting the importance of such anti-surveillance measures. However, the effectiveness of strobing can be influenced by:
- Controlled illumination conditions.
- Variability in skin reflectance across different demographics.
- Advanced computational techniques that rogue actors may employ.
While strobing can detect liveness, it’s essential to combine it with other biometric measures for thorough identity verification.
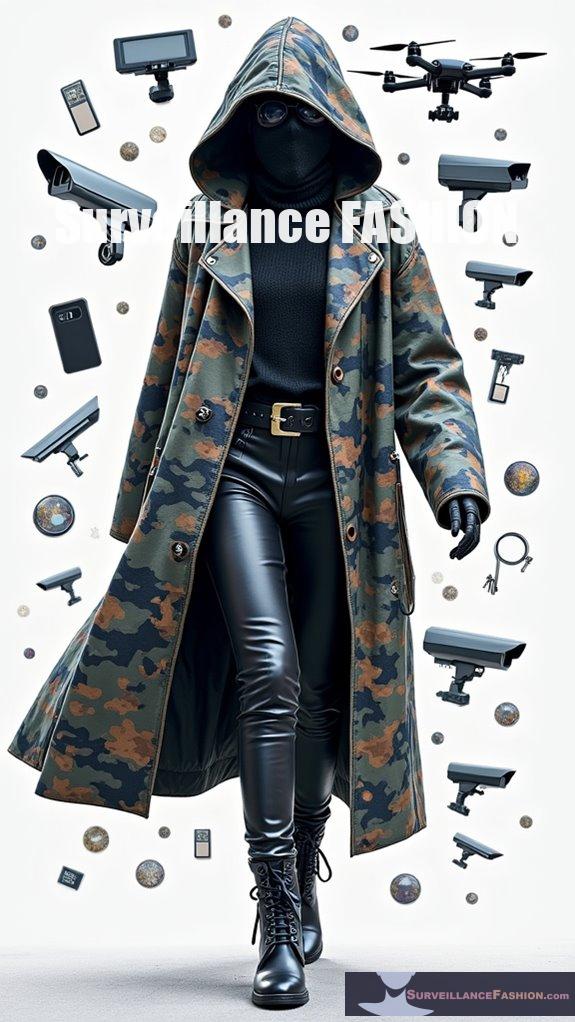
Can Anti-Surveillance Hoodies Be Used Successfully in Daylight?
Anti-surveillance hoodies utilizing infrared (IR) LEDs are ineffective in daylight due to natural IR saturation and dominance of visible light, which makes facial recognition algorithms far more operational.
In daylight conditions, the ambient light, particularly sunlight, overwhelms the IR signals emitted by the hoodies. This saturation greatly diminishes their ability to blind night vision cameras.
While these garments are designed to exploit the invisibility of IR light at night, they don’t provide any visible obstruction or protection against surveillance in bright environments.
Key points include:
- Passive adversarial clothing and visual patterns are more effective for daytime use.
- IR LEDs create no visible light during the day, offering no camouflage against visible-light cameras.
- The technology primarily serves as a nocturnal solution, with limited practical use in direct sunlight.
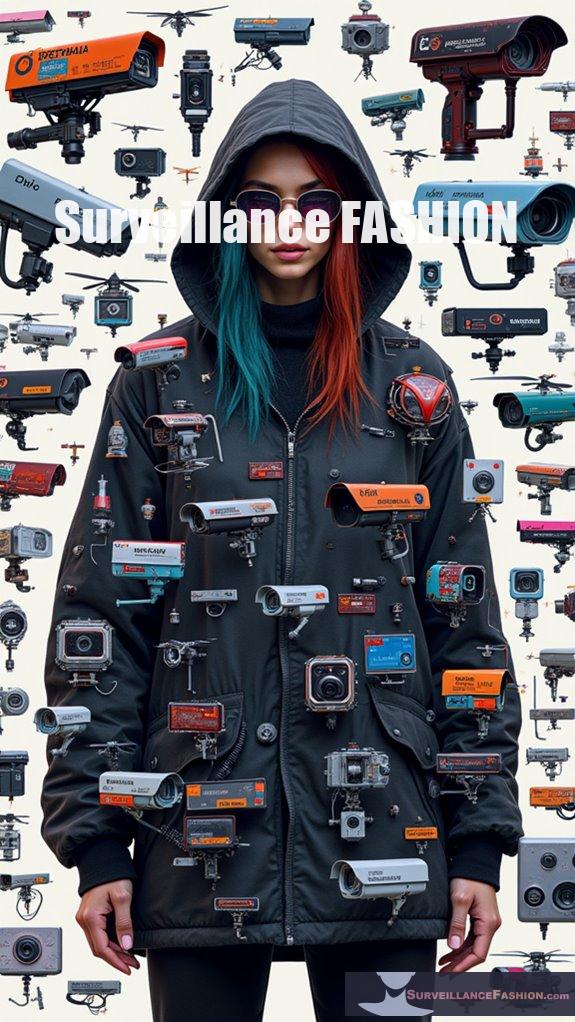
What Are the Key Features of Mac Pierce’s Camera Shy Hoodie?

The key features of Mac Pierce’s Camera Shy Hoodie include a 12-LED infrared array for blinding night vision cameras, a user-controlled IR strobe mode, and customizable DIY electronics. It requires a 15-volt power source and effectively obscures the wearer’s identity in low-light environments.
The hoodie is designed to combat surveillance by emitting infrared light that disrupts typical cameras used in security systems. The LEDs are strategically placed to cover the head and upper body, ensuring thorough coverage.
Users can activate the strobe mode via a sleeve switch, allowing for discretion and control over its use. Constructed as a DIY project, the hoodie encourages custom modifications while raising awareness about surveillance issues.
Key considerations for use include the need for an insulating layer to avoid discomfort and the efficacy being limited to low-light situations. The project is intended for ethical privacy protection rather than illegal activities.
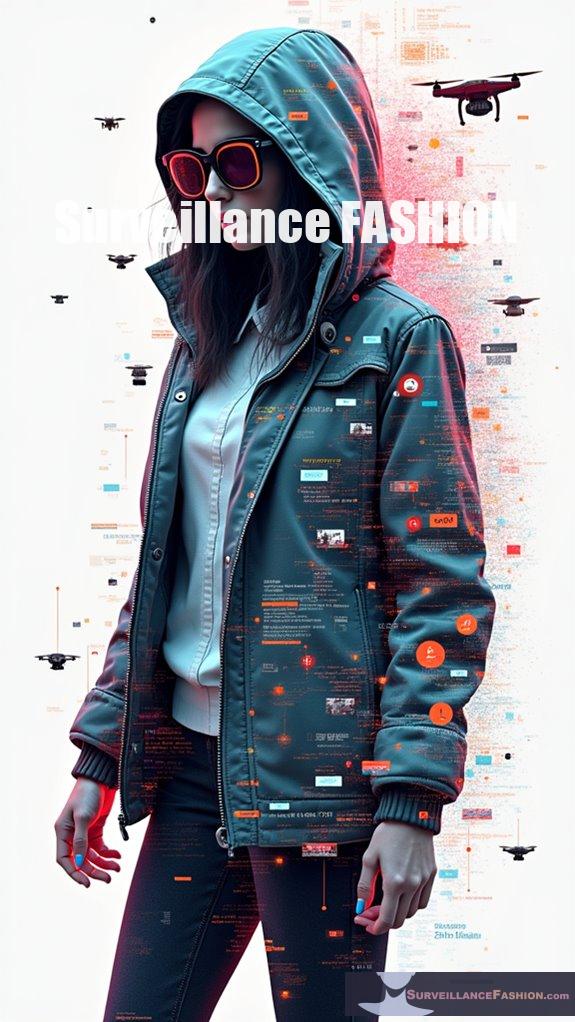
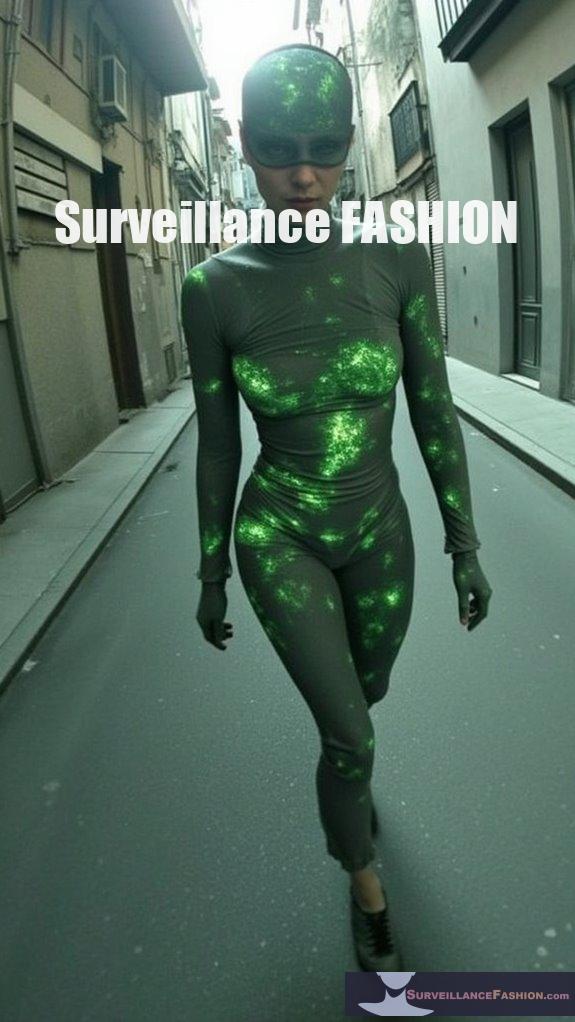
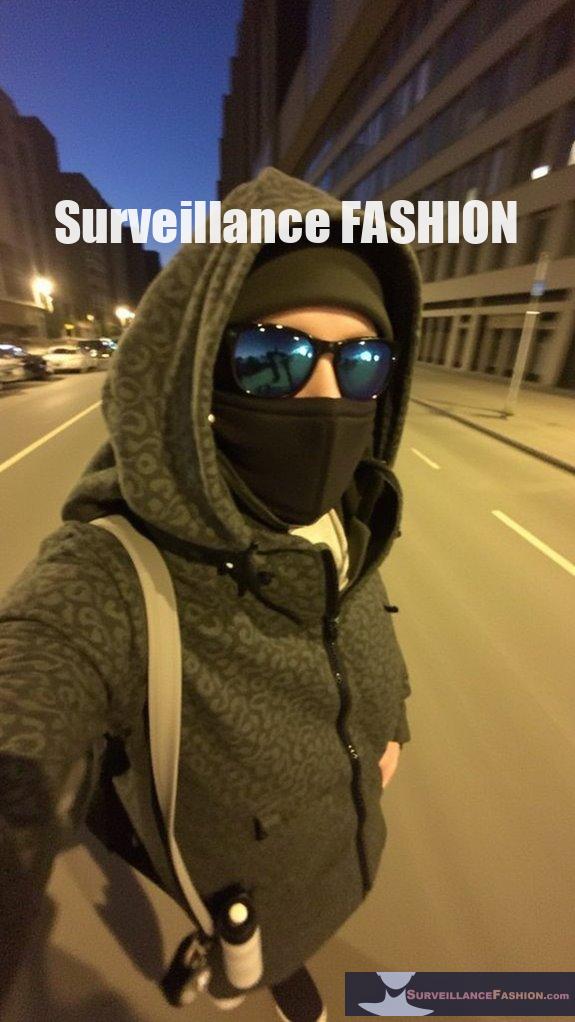
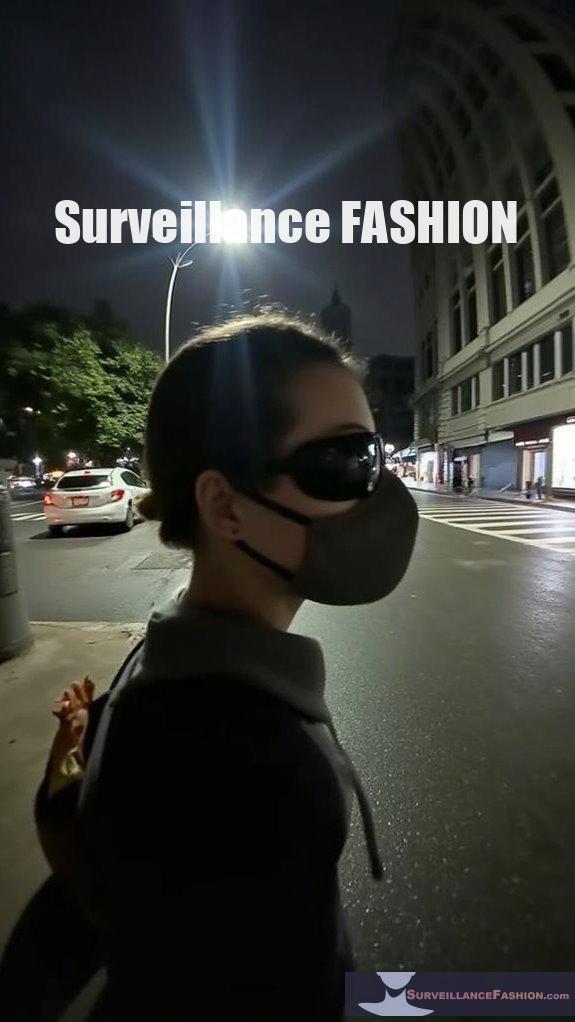
How Do Anti-Surveillance Hoodies Promote Personal Anonymity?
Anti-surveillance hoodies promote personal anonymity by utilizing embedded IR LEDs and disruptive visual patterns to obscure the wearer’s facial features from surveillance cameras. This balance allows individuals to maintain privacy without attracting undue attention in public spaces.
The integration of high-power infrared LEDs targets night-vision cameras, creating overexposure effects that anonymize the wearer’s head and face. Moreover, the printed designs on the hoodies confuse facial recognition algorithms by presenting misleading visuals.
Key features include:
- Camouflage against surveillance in monitored environments.
- Disruption of AI detection through complex patterns.
- Enhanced privacy while traversing public or activist spaces.
- A blend of technology with fashion for everyday wearability.
Ultimately, these garments offer a proactive approach to protect individual privacy in an age of increasing surveillance technology. However, their effectiveness may vary based on lighting conditions and the sophistication of detection systems.
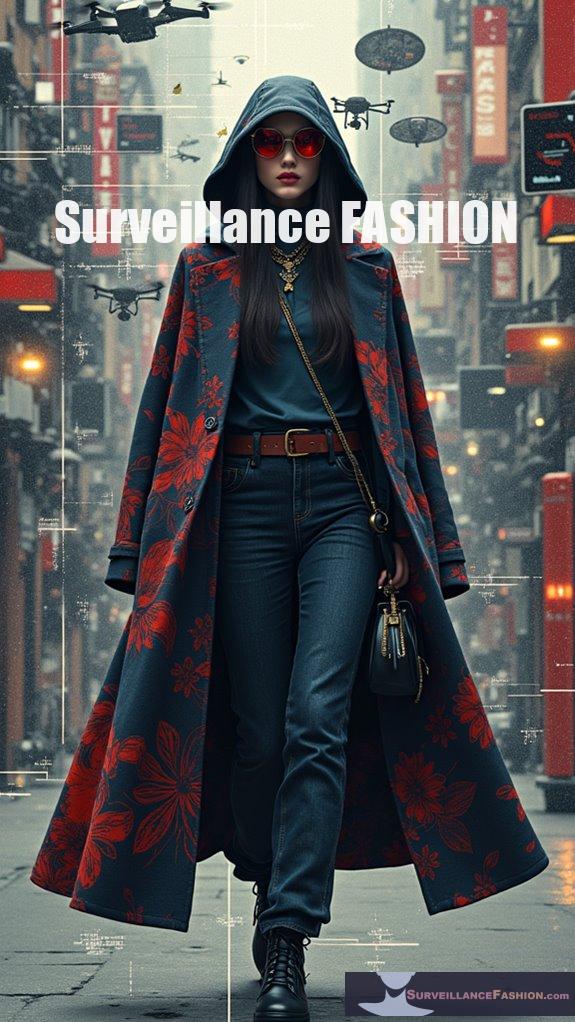
What Are the Limitations of Using These Hoodies Against Various Surveillance Systems?
Anti-surveillance hoodies have significant limitations, particularly against various surveillance systems. They mainly disrupt infrared night vision cameras in low-light environments but are ineffective in daylight conditions and face challenges against alternative tracking methods.
These hoodies rely on infrared (IR) technology, only affecting specific IR cameras while leaving conventional RGB cameras unaffected. In well-lit or sunny areas, they can attract attention instead of providing anonymity. Furthermore, biometric identification methods like gait analysis and behavior recognition can still identify individuals, undermining the hoodies’ purpose.
High-security or actively monitored environments further reduce their effectiveness, as security personnel and AI systems may easily spot the visual anomalies created by the IR lights.
In addition, their design must match specific IR wavelengths, which limits their utility across varied camera types. Factors such as environmental conditions, battery life, and user comfort also hinder their practicality, making it difficult to achieve effective anonymity solely through these garments.
Finally, they don’t address non-visual surveillance methods, such as thermal imaging or radio frequency (RF) tracking, leaving wearers vulnerable to other forms of surveillance.
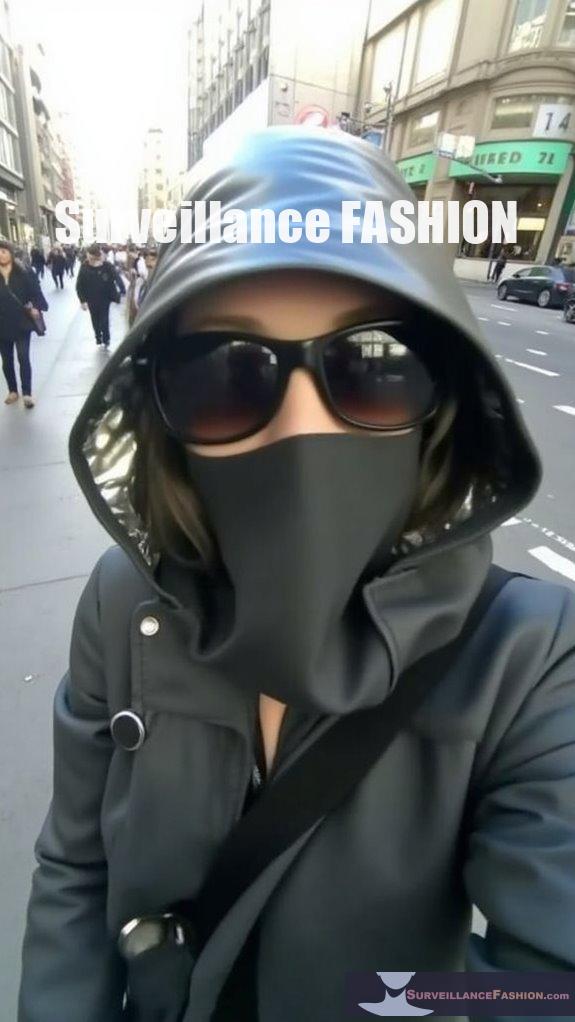
Who Is the Target Market for Anti-Surveillance Hoodies?
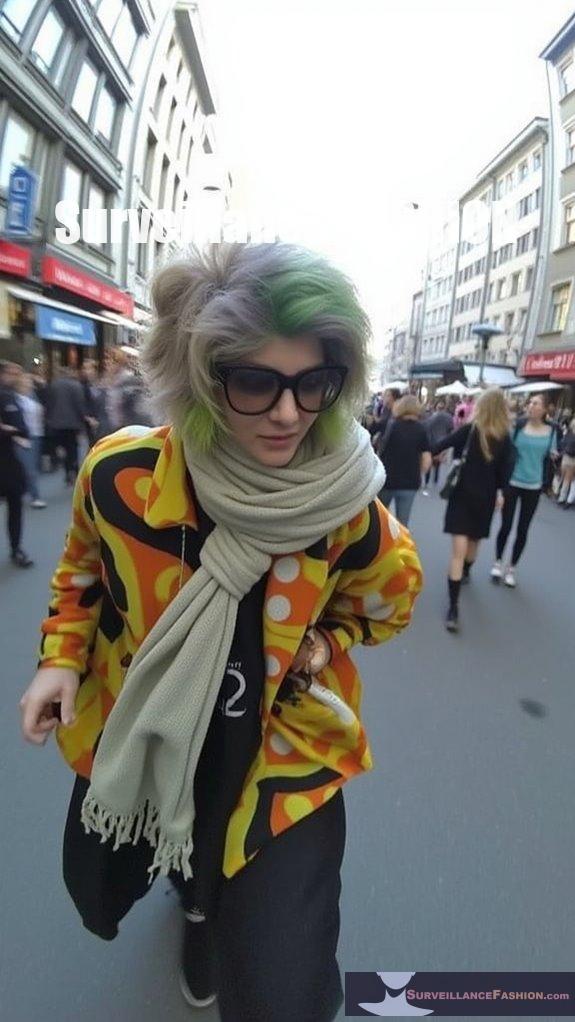
The target market for anti-surveillance hoodies includes privacy-conscious activists, tech-savvy privacy advocates, individuals in high-surveillance urban environments, privacy-focused designers, and supporters of digital rights campaigns.
These consumers seek protection from pervasive surveillance through fashionable, functional clothing. They often prioritize garments that disrupt recognition technologies, such as complex patterns and metal-infused fabrics. Furthermore, their motivation stems from a desire to maintain anonymity and push back against state and corporate overreach.
Target demographics also include:
- Grassroots activists and protesters
- Tech enthusiasts aware of biometric risks
- Urban dwellers facing ubiquitous monitoring
- Designers innovating in privacy-focused fashion
- Digital rights advocates committed to reform
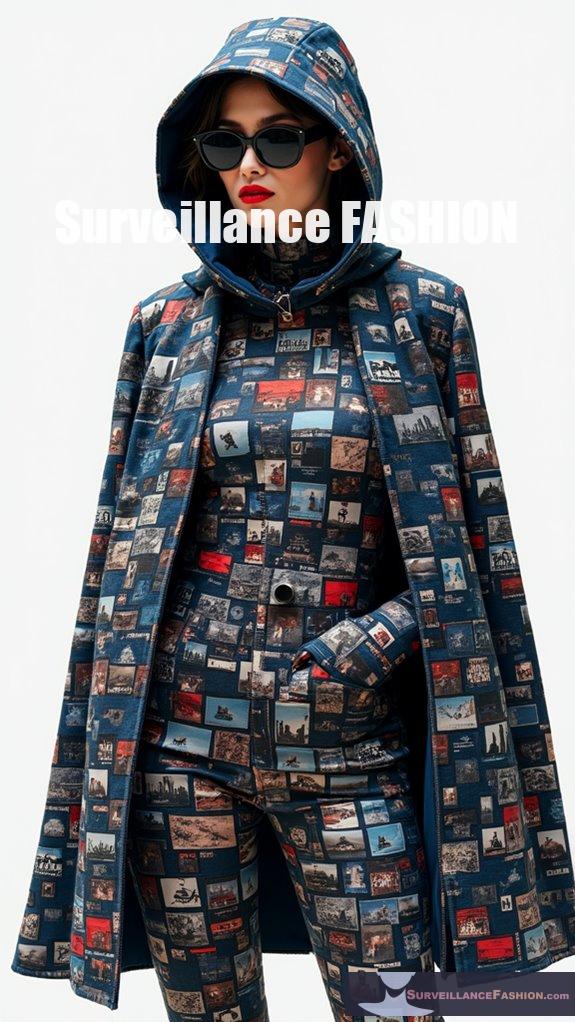
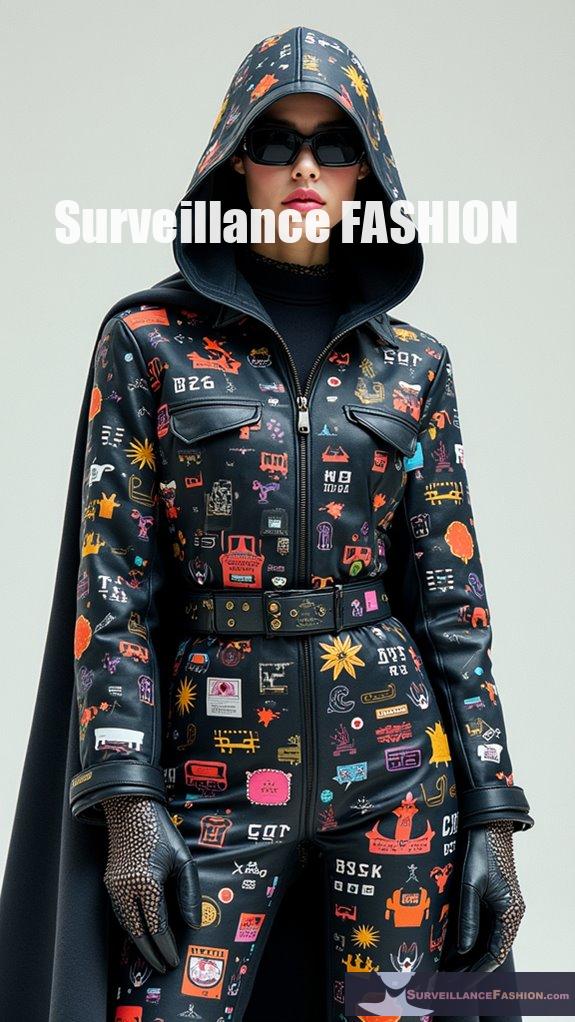
How Are Privacy Concerns Driving Innovation in Fashion Technology?

Privacy concerns are driving innovation in fashion technology by prompting the development of anti-surveillance designs, reflective materials, and AI-driven customization that protect personal data from modern surveillance systems.
This evolution in fashion addresses the increasing use of facial recognition and data extraction methods. Designers are integrating features such as:
- Patterns that confuse facial recognition algorithms
- Reflective fabrics that impair photography in low light
- AI-driven personalization enhancing privacy
- Smart textiles that adapt to surveillance threats
These innovations aim to provide stylish options that prioritize individual privacy while remaining functional.
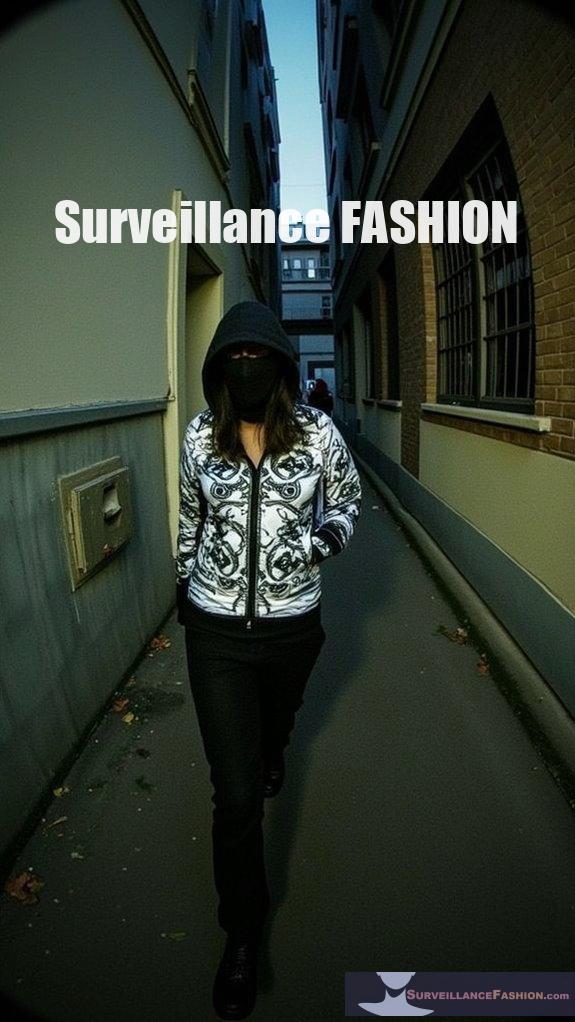
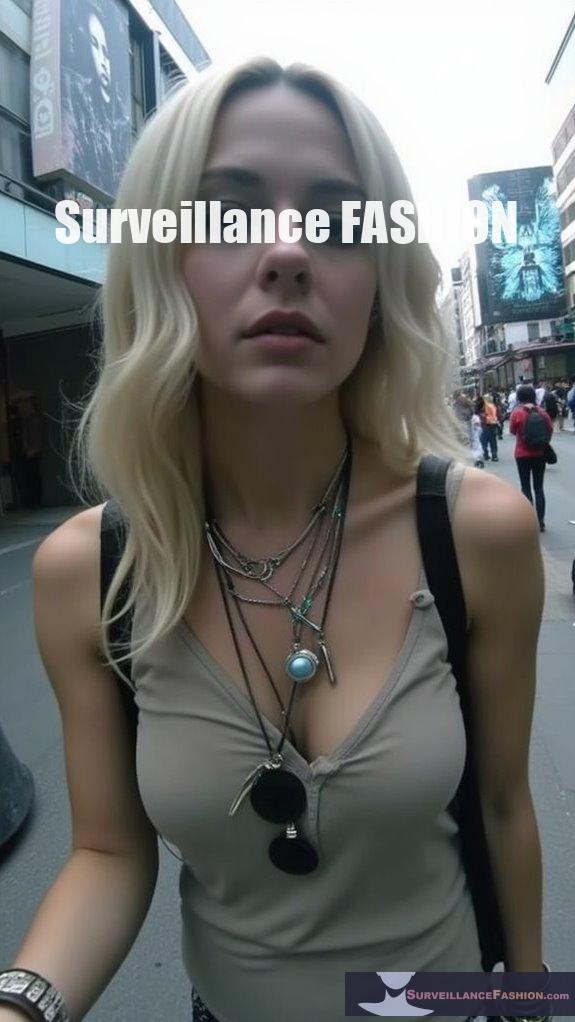
Hoodies With Obscuring Hoods
In the domain of modern fashion technology, innovative hoodies equipped with obscuring hoods represent a fascinating intersection of style and security, designed thoughtfully to counteract the pervasive threats of surveillance.
These garments ingeniously integrate high-powered infrared LEDs that disrupt night vision cameras, rendering facial recognition useless.
However, as you consider the safety implications and ethical considerations of wearing such a device, questions arise about broader surveillance practices.
While these hoodies create a unique blend of anonymity and fashion, they can’t eliminate surveillance entirely, highlighting an ongoing tension between personal privacy and technological advancement, which is why we created this website, Surveillance Fashion.
Anti Surveillance Ebook review: Eyes Everywhere
Boghosian intricately weaves stories of social movements, revealing how surveillance ethically compromises both activism and fashion privacy.
Through examining varied instances—from phone tracking to the coordinated monitoring of protests—he highlights an unsettling truth: surveillance operates as a mechanism of control rather than safety.
In a world increasingly influenced by surveillance ethics, this eBook encourages a deeper reflection on your role within this pervasive digital environment.
Crowded Urban CCTV Networks
As urban settings evolve, the proliferation of CCTV cameras transforms public spaces into a matrix of surveillance, fundamentally altering the dynamics of city life.
With over 700 million cameras globally, densely populated cities like Beijing, where there’s one camera for every two residents, exemplify this shift.
Each camera, strategically placed near transport hubs or crowded areas, forms part of a complex sensor network, often enhanced by AI analytics for facial recognition.
This elaborate web jeopardizes urban privacy, amplifying concerns about anonymity.
In such an environment, anti-surveillance fashion becomes essential, as we endeavor to reclaim a sense of privacy amidst invasive watchfulness.
Civil Liberties Against Safety Measures
While the tension between civil liberties and safety measures escalates amidst an increasingly surveilled society, one can’t ignore the complex dilemmas presented by anti-surveillance garments.
References
- https://www.vice.com/en/article/this-hacker-hoodie-uses-surveillance-camera-parts-to-blind-surveillance-cameras/
- https://www.boldbusiness.com/digital/hacker-hoodies-ai-detectors-need-for-innovations-against-innovations/
- https://hackaday.com/2023/03/06/adversarial-ir-hoodie-lets-you-own-the-night-in-anonymity/
- https://cybernews.com/privacy/anti-surveillance-fashion/
- https://www.macpierce.com/the-camera-shy-hoodie
- https://www.popsci.com/technology/camera-shy-hoodie-privacy/
- https://www.youtube.com/watch?v=zEh_pHCcOBc
- https://www.etsy.com/listing/925704585/anti-facial-recognition-hoodie-anti
- https://petapixel.com/2023/03/01/hacker-hoodie-blinds-surveillance-cameras-with-infrared-light/
- https://www.bleepingcomputer.com/news/security/new-facial-recognition-system-relies-on-the-speed-of-light-for-security/
- https://www.ndss-symposium.org/wp-content/uploads/2019/02/ndss2018_03B-5_Tang_paper-updated.pdf
- https://pmc.ncbi.nlm.nih.gov/articles/PMC8321190/
- https://openaccess.thecvf.com/content/CVPR2023W/Biometrics/papers/Wu_Face_Recognition_Accuracy_Across_Demographics_Shining_a_Light_Into_the_CVPRW_2023_paper.pdf
- https://incode.com/blog/beyond-biometrics-how-facial-recognition-technology-is-revolutionizing-security-and-personalization/
- https://www.techeblog.com/camera-shy-hoodie-ir-leds-blind-surveillance-camera/
- https://static1.squarespace.com/static/59fc78f1b07869a18edb2d7b/t/63efd3d9b1343a392f680d7e/1676661721736/CameraShyHoodie_Instructions.pdf
- https://www.cctv.supplies/hacker-hoodie-blinds-surveillance-cameras-with-infrared-light/
- https://rabbitfurcoat.substack.com/p/circumventing-the-surveillance-state
- https://www.harpersbazaar.in/fashion/story/what-is-anti-surveillance-drip-and-why-everyones-wearing-it-now-1199076-2025-04-15
- https://news.ycombinator.com/item?id=34958153