Blocking signals with fashion jewelry serves as a proactive measure against unauthorized tracking and invasive surveillance. These adornments utilize conductive materials, like nickel and copper, to create miniature Faraday cages around sensitive body areas. Consequently, you may experience an enhanced sense of privacy while wearing them, as many users report reduced stress levels linked to electronic interference. However, it’s important to understand that their effectiveness varies, with many determining the balance between style and signal-blocking functionality. Discover more about this intersection of art and privacy.
Quick Takeaways
- Signal blocking jewelry disrupts wireless signals, offering enhanced privacy and security by preventing unauthorized tracking and hacking.
- These accessories use materials like nickel and copper to provide effective electromagnetic shielding while maintaining a stylish appearance.
- Wearing this jewelry can potentially reduce stress and improve mental well-being through a sense of control over EMF exposure.
- The discreet design makes it easy to integrate into daily wear, providing continuous protection as it moves with the user.
- Unlike other privacy solutions, such as plug-in devices, fashion jewelry offers lightweight and fashionable options for personal EMF shielding.
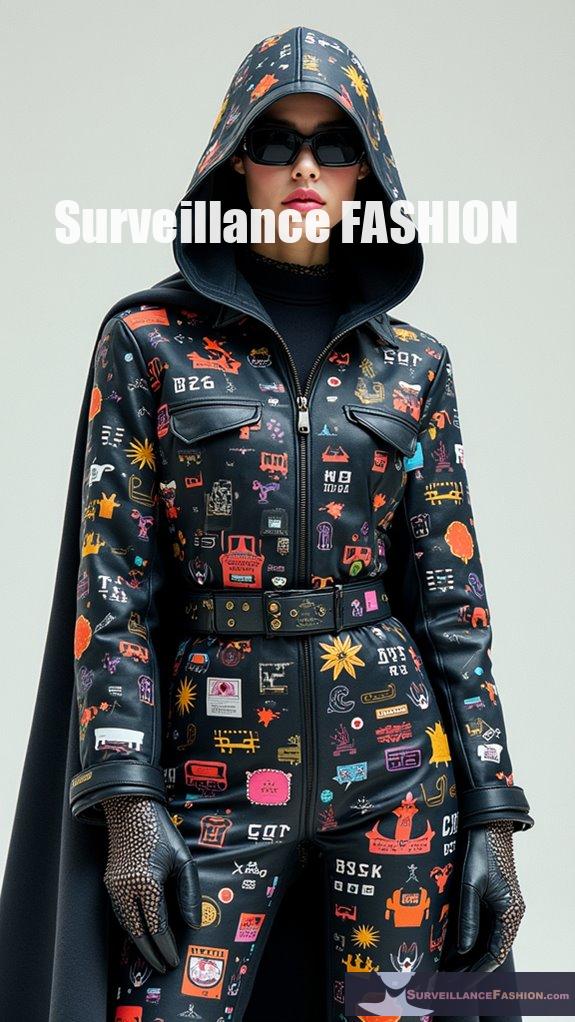
What Is Fashion Jewelry Designed for Signal Blocking?

Fashion jewelry designed for signal blocking incorporates materials and technologies that disrupt wireless signals (like RFID and Bluetooth) to enhance personal privacy and security. These pieces blend aesthetic appeal with functional shielding, preventing unauthorized tracking, hacking, and eavesdropping. This jewelry typically features multilayered conductive fabrics such as nickel and copper, which act as effective electromagnetic shields. They can include embedded microelectronics that interfere with microphones or wireless signal reception. By applying Faraday cage principles on a small scale, these designs offer nearly complete signal blocking while maintaining an attractive appearance. Users benefit from enhanced privacy and security in environments filled with smart devices, mirrored by the wearable microphone jammer’s effectiveness against hidden microphones. Additionally, the effectiveness of these pieces can be attributed to their multilayered designs that provide additional protection.
How Does Faraday Shielding Work in Jewelry?
Faraday shielding in jewelry works by utilizing a conductive layer that redistributes electromagnetic charges, canceling external electric fields and preventing electromagnetic waves from penetrating the enclosed area. This is achieved through materials like silver, copper, and stainless steel, which create localized Faraday cages around sensitive body areas. The core mechanism involves the movement of surface charges in response to external electromagnetic radiation. When radiation hits the conductive layer, it induces fields that oppose the external fields, therefore reducing their intensity within the shielded area. Freedom from gaps or holes larger than the relevant wavelengths is essential for effective shielding.
Key points include:
- Common materials are silver, copper, gold, and conductive composites.
- Shielding is most effective against frequencies from 800 MHz to 5 GHz.
- Design must balance aesthetics and functionality to maintain wearability.
- Complete shielding is rare; most jewelry offers partial protection. Additionally, the effectiveness of shielding is influenced by geometry and material properties, reflecting principles seen in traditional Faraday cages.
What Are the Benefits of Wearing Signal Blocking Jewelry?
Wearing signal blocking jewelry is claimed to reduce stress-related symptoms and support mental well-being, with users reporting benefits like improved mood and a more balanced nervous system. However, scientific evidence suggests that these effects may largely stem from placebo responses rather than direct physiological impacts. The perceived benefits of wearing EMF protective jewelry may arise from multiple factors. Users often feel a sense of control over invisible EMF exposure, which can enhance mental well-being. Furthermore, these accessories are lightweight and portable, allowing easy integration into daily life without behavioral adjustments. Some products incorporate natural materials known for their reputed protective properties:
- Black tourmaline is said to convert negative energy.
- Shungite is recognized for its effectiveness against radiation.
- Hematite is traditionally used to deflect electromagnetic waves.
In addition, dazzle makeup techniques used in anti-surveillance can also foster a sense of empowerment over personal privacy. Although users report positive experiences, it’s important to keep in mind that empirical support for the efficacy of these products remains limited, and shields produced measurable placebo effects suggest that the benefits may not be grounded in reality.
Can Fashion Jewelry Prevent Wireless Tracking?
Answer:
Fashion jewelry can’t effectively prevent wireless tracking as it lacks the specialized materials and engineering needed for signal blocking.
Fashion jewelry typically focuses on aesthetic appeal and doesn’t incorporate the necessary components for electromagnetic shielding. Without materials like specially configured metals or designs that create a Faraday cage, the jewelry allows signals such as GPS and Bluetooth to pass through freely.
As a result, while some jewelry may have anti-theft features, it doesn’t block external signals that could lead to tracking.
Key limitations include:
- Ineffective shielding due to absence of conductive materials.
- Lack of multi-layer protection against various frequency bands.
- User preference for non-bulky, stylish designs discouraging overt signal-blocking features.
Alternative solutions exist, such as specialized pouches or wallets designed specifically to block signals.
What Types of Signals Can Be Blocked by Jewelry?

Jewelry can block or interfere with several types of signals, including metal detection signals, electromagnetic fields, and spiritual energies. However, its effectiveness varies based on the materials used and the circumstances of the interference.
Metal-rich jewelry can mask or overload metal detectors, particularly when containing iron. Such materials may create false positives and hinder the detection of valuable metals like gold.
Similarly, certain jewelry designs utilizing bioresonance may harmonize EMF interactions, reducing body stress without physically blocking signals.
Moreover, spiritual jewelry aims to filter out negative energies rather than electronic signals. The effectiveness of jewelry in blocking energy signals depends largely on personal beliefs and the specific materials involved.
Examples include:
- Iron in jewelry distorting metal detector signals.
- EMF protection jewelry using bioresonance technology.
- Spiritual jewelry blocking negative vibrations and energies.
How Effective Is Signal Blocking Jewelry?
Signal blocking jewelry is largely ineffective; scientific studies show no significant reduction in electromagnetic fields or physiological changes beyond placebo effects.
Users report perceived benefits due to psychological influences rather than actual EMF shielding.
Despite claims of EMF protection, rigorous testing reveals the following:
- Pendants and stickers exhibit no measurable RF shielding.
- True shielding requires conductive materials, which jewelry typically lacks.
- Belief in the product correlates with self-reported effectiveness.
- Experts recommend proximity management and limited device usage over reliance on jewelry for RF protection.
Are There Legal Implications of Using Signal Jamming Jewelry?
The use of signal jamming jewelry can carry legal implications if it interferes with authorized communications, potentially leading to fines or criminal charges.
Such devices may violate FCC regulations, especially if they disrupt public safety or emergency response communications.
Signal jamming issues are complex and subject to regulatory scrutiny. Jewelry that blocks signals may inadvertently jam essential communications. Furthermore, law enforcement may seek access to private camera networks as part of their investigations, highlighting the potential consequences of such disruptions.
The following legal considerations apply:
- Unauthorized jamming can lead to fines up to $5,000.
- It may result in imprisonment if used in conjunction with criminal activity.
- Any interference with public safety communications is a felony.
- Law enforcement has exemptions but must adhere to specific guidelines.
Due to these considerations, individuals should be cautious about the use of signal jamming jewelry to avoid severe legal repercussions.
What Should Consumers Look for When Buying Signal Blocking Accessories?
When evaluating signal-blocking jewelry, consider the following factors:
- Materials: Opt for pieces made from metals like titanium, copper, or silver due to their conductive properties.
- Effectiveness: Confirm the product specifically targets the EMF frequencies relevant to your needs, such as those from cell phones or WiFi.
- Comfort and Design: Choose lightweight, stylish pieces for all-day wear.
- Durability: Examine construction quality and inquire about warranties to safeguard against wear and tear.
How Does Signal Blocking Jewelry Compare to Other Privacy Solutions?

Signal blocking jewelry offers lightweight and discreet protection for personal EMF exposure but generally lacks the measurable effectiveness of other solutions like RF shielding materials.
While jewelry provides continuous protection as it moves with the wearer, its claims of efficacy often rely on unverified principles rather than tangible data.
In contrast, RF shielding fabrics demonstrate clear EMF attenuation, offering superior protection.
Additionally, broader solutions, such as blocking clothing and plug-in devices, may better serve stationary environments or specific electronics, though they might sacrifice portability and comfort.
Users should be cautious, relying on proven protective technologies rather than aesthetic perceptions of jewelry.
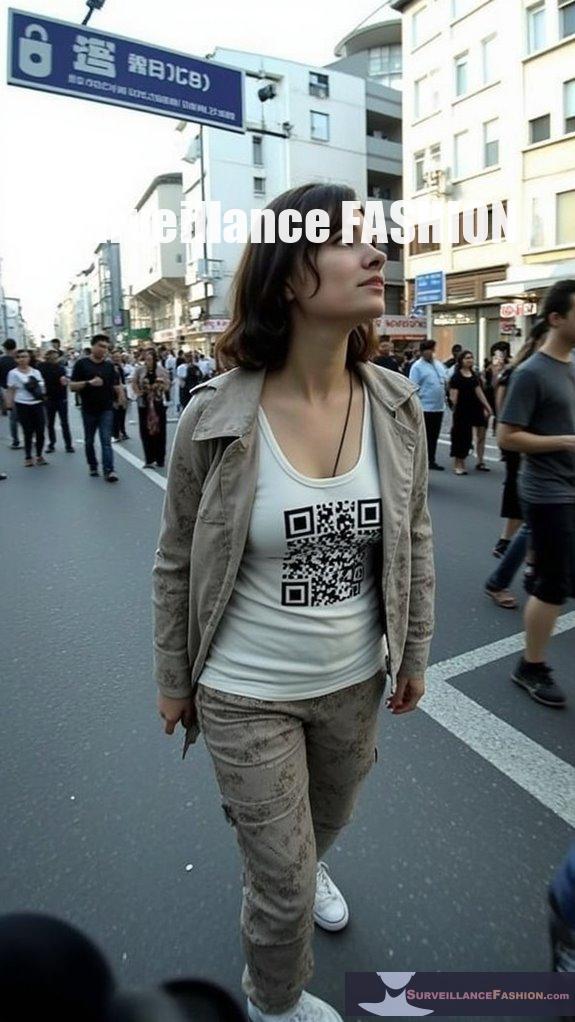
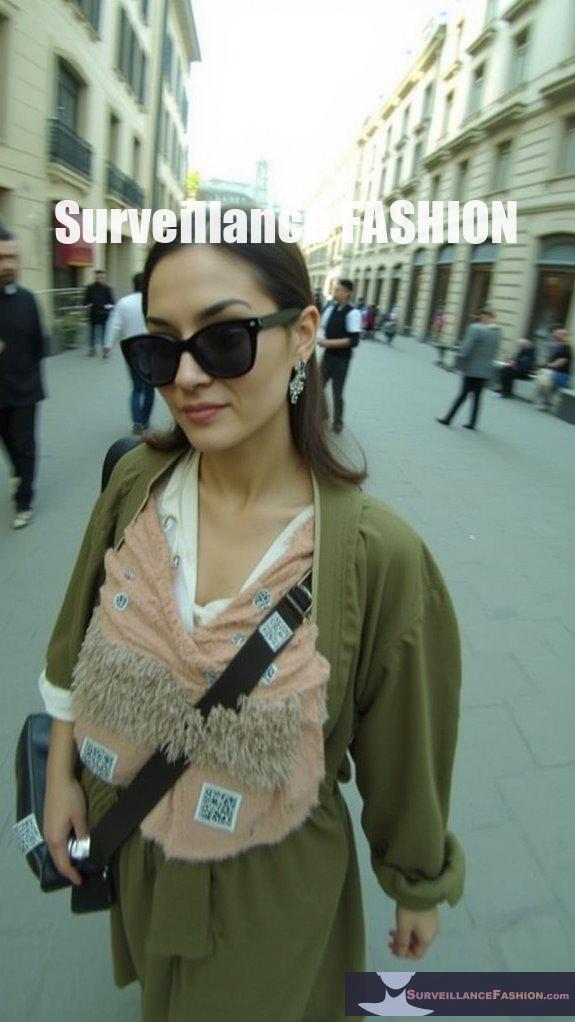
Signal Jamming Jewelry
Among the myriad innovations in personal security, signal jamming jewelry has emerged as an intriguing intersection of fashion and functionality, offering a novel approach to privacy protection.
Incorporating sophisticated signal jamming technology, these elegant accessories discreetly block signals from RFID, Bluetooth, and cellular devices, consequently enhancing your privacy.
Utilizing embedded jammers that disrupt communication by matching specific frequencies, they create a localized barrier, safeguarding you against unwanted tracking.
This marriage of style and security reflects our desire at Surveillance Fashion to empower individuals with elegant tools to navigate an increasingly surveilled world, merging aesthetic appeal and essential privacy enhancement seamlessly.
Anti Surveillance Ebook review: Eyes Everywhere
The “Eyes Everywhere” eBook offers a critical examination of the pervasive nature of surveillance in contemporary society, illuminating the multifaceted ways that technological integration has reshaped personal privacy.
Through an exploration of alarming trends, you’ll discover how:
- Camera surveillance has become globally normalized, despite its limited impact on crime deterrence.
- Government-corporate surveillance integration deepens personal data collection.
- Worker monitoring erodes collective power and well-being.
- Everyday technologies contribute to societal complacency regarding privacy concerns.
These revelations not only reflect current fashion trends but also inform your understanding, emphasizing the importance of being proactive about privacy in an increasingly surveilled world.
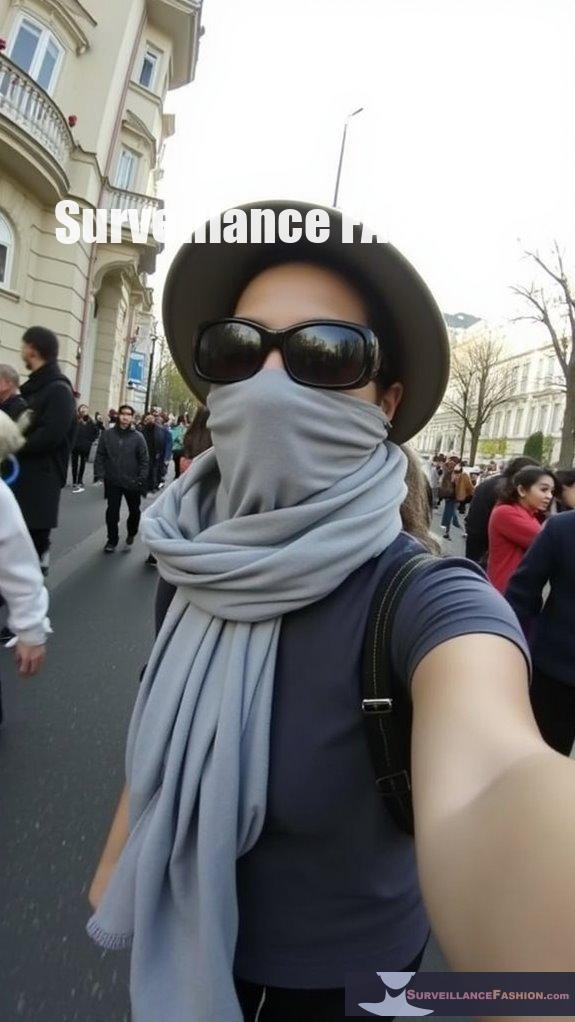
Facial Recognition Systems Deployed
Surveillance integration into daily life has increasingly manifested in the form of facial recognition systems, prompting countless responses from both individuals and artists who seek to reclaim their privacy.
With the rise of these technologies, you may face significant facial recognition risks, as your image is recorded and analyzed without your consent.
Artists like Ewa Nowak craft jewelry that disrupts these systems by altering your facial patterns, offering unique solutions amidst growing privacy concerns.
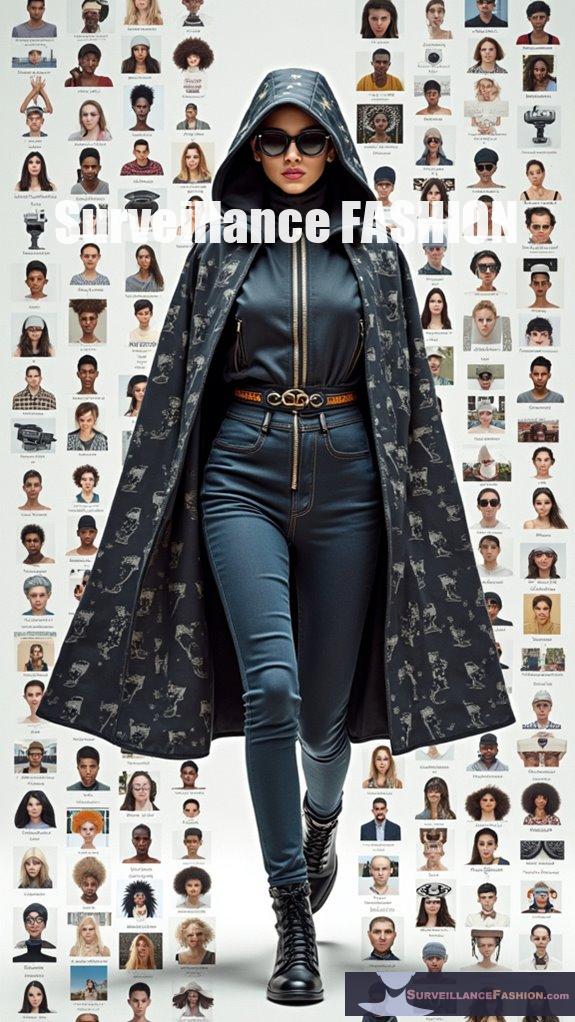
Data Surveillance Versus Personal Freedom
In an age where digital footprints are readily cataloged, individuals often grapple with the fine line separating data surveillance from personal freedom. Increasing reliance on technology makes this challenge even more pressing, leading to concerns about data rights and privacy awareness.
Here are four key points to reflect upon:
- 92% of Americans worry about online privacy.
- 87% support banning personal data sales without consent.
- Only 3% understand privacy laws.
- Two-thirds believe tech companies control personal data excessively.
Amid these issues, fashion jewelry emerges as a statement, fostering a dialogue about reclaiming one’s freedom in this digital arena.
References
- https://www.briandickersonart.com/Blocking-Bag-If-It-Does-Not-Have-These-3-Things/311923
- https://www.aliexpress.com/item/1005005966970437.html
- https://www.alibaba.com/product-detail/Anti-Tracking-Faraday-Bags-for-Cell_1601367657755.html
- https://invisawear.com
- https://www.etsy.com/market/5g_blocking_jewelry
- https://sandlab.cs.uchicago.edu/jammer/
- https://crescentconstructionservices.com/3-Layer-Signal-Blocking-Pouch-For-Phones-Electronics/712806
- https://en.wikipedia.org/wiki/Faraday_cage
- https://mosequipment.com/collections/faraday-supplies
- https://www.gamry.com/application-notes/instrumentation/faraday-cage/
- https://www.youtube.com/watch?v=GHnNC8q1w64
- https://www.etsy.com/market/emf_shield_jewelry
- https://pubmed.ncbi.nlm.nih.gov/12233804/
- https://www.getthegloss.com/health/mental-health/emf-protectors-harmoni-pendant/
- https://lessemf.com/knowledgebase/pendants-stickers-vs-rf-shielding-materials-what-works-best/
- https://ayanacrystals.com/blogs/blog/top-6-emf-protection-crystals-shield-your-space-naturally
- https://emf-harmony.com/blogs/news/do-emf-protection-stickers-work
- https://hexahash.unlimitedvisitors.io/post/general/rfid-jewelry-wearable-tech-meets-fashion
- https://ijrpr.com/uploads/V5ISSUE3/IJRPR23910.pdf
- https://www.healthday.com/health-news/general-health/healthy-fashion-earrings-that-track-your-wellness