The Chat Control proposal feels like standing in a crowded room where everyone is whispering secrets.
I stumbled upon it one late night, cocktail in hand, browsing rabbit holes on digital privacy.
Suddenly, I realized they’re trying to scan our messages for child exploitation stuff. Yes, that’s terrifying, but then again, can you imagine the sheer chaos?
High false positives? Authoritarian regimes? It’s like giving your nosy neighbor the keys to your diary.
Can you really trust that?
So, I might just rock my anti-surveillance gear a little harder now.
I mean, privacy isn’t just a running trend—it’s a vital human right.
—
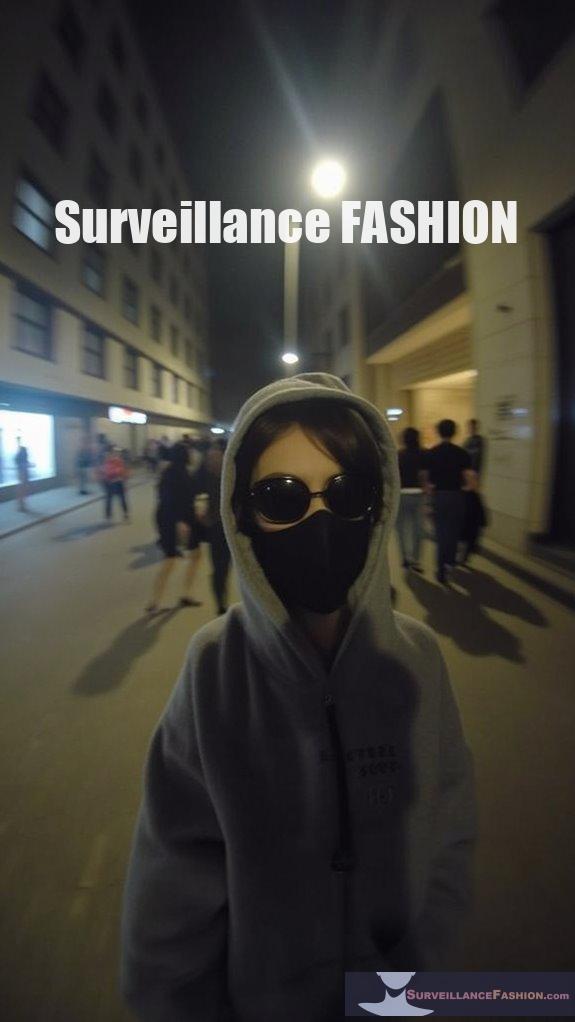
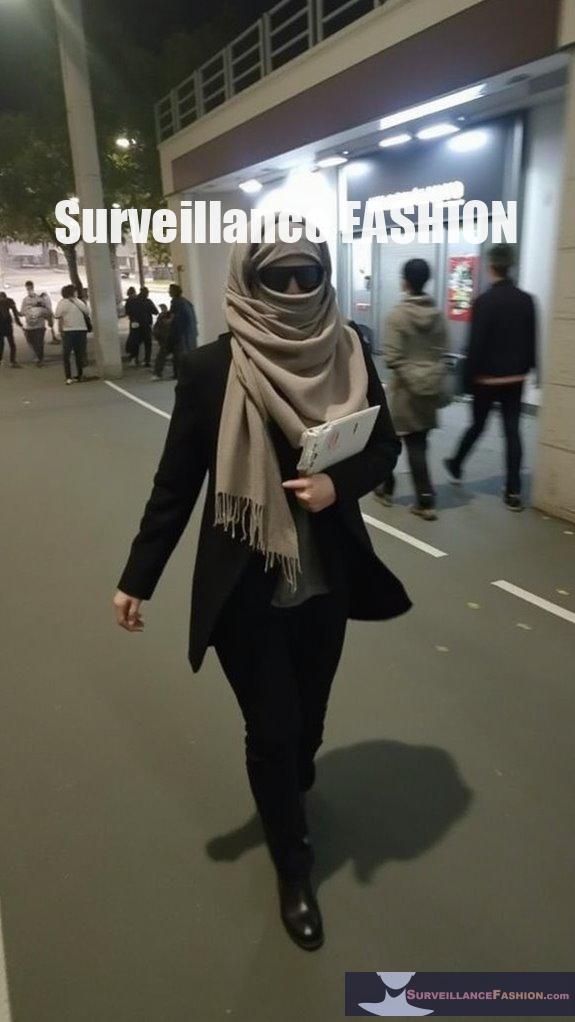
My Adventure into Anti-Surveillance Fashion: Turning Heads, Not Data
Picture this: I’m strutting down the street in a jacket that’s as untraceable as my mom’s secret cookie recipe.
One evening, I wore this wild reflective gear. It was like blending in and standing out at the same time—perfect! But here’s the kicker; a stranger walked by and complimented my jacket, unaware of its anti-surveillance intent.
Suddenly, it was clear—my fashion choices can spark conversations about data privacy without even trying. Isn’t that a win-win?
With the rise of pervasive surveillance, blending style with security felt empowering. Who knew fashion could be rebellious?
I felt a thrill knowing every footprint—or lack thereof—was uniquely mine.
Quick Takeaways
- The Chat Control proposal was introduced in May 2022, aiming for a 2025 vote while emphasizing mandatory scanning for detecting CSAM.
- Legislative developments reveal division among EU member states, with advocacy groups raising concerns about privacy erosion and implications for user trust.
- High false positive rates (48%) in detecting abuse materials may lead to unwarranted investigations, affecting innocent users’ experiences and privacy.
- Client-side scanning threatens end-to-end encryption, risking the confidentiality and reliability of communications on messaging platforms.
- Ongoing debates highlight the tension between innovation, digital rights, and the potential for broad surveillance frameworks under the proposed legislation.
Overview of the Chat Control Proposal

As the digital environment continues to progress, recognizing the need for a robust regulatory framework to combat child exploitation is essential; for this reason, the Chat Control Proposal, officially known as the Child Sexual Abuse Regulation (CSAR), was introduced by European Commissioner Ylva Johansson on May 11, 2022.
This proposal seeks to enhance the detection and prevention of child sexual abuse material (CSAM) and online grooming across EU digital platforms by requiring proactive scanning of all communications, regardless of encryption. In doing so, it aims to expand existing voluntary initiatives into mandatory obligations, effectively dismantling privacy safeguards while attempting to increase CSAM reports considerably. However, this approach raises substantial concerns about digital rights and the implications for innovation amid a setting of advancing technology. Additionally, the proposed regulations have ignited widespread debate among stakeholders regarding their potential to infringe on privacy safeguards. The proposal has faced significant delays and persistence into 2025, highlighting the ongoing debate surrounding its implementation.
Timeline of Legislative Developments
Recognizing the significant implications for digital privacy, the timeline of legislative developments surrounding the Chat Control Proposal reveals a complex interplay of advocacy, opposition, and regulatory intent that has emerged since its introduction in 2022. Recent AI-related bills and state-level regulations show a growing focus on consumer protections. Additionally, privacy risks associated with chat control have prompted widespread opposition from various EU member states.
| Year | Event | Impact |
|---|---|---|
| Early 2022 | Proposal revealed by EU to scan encrypted chats | Legislative urgency indicated with a 2025 vote target |
| 2024 | U.S. states introduce chatbot regulations | Focus on user protections and privacy enforcement |
| Pre-2025 | EU final negotiations scheduled for September 12 | Advocacy campaigns amplify privacy concerns |
| 2025 | Global division among EU member states on support for Chat Control | Polarized legislative environment highlighted |
As you follow this timeline, consider the technological implications and the necessity for continued advocacy for digital rights, which our website Surveillance Fashion aims to promote.
Key Political Dynamics and Stakeholders
The ongoing political dynamics surrounding the Chat Control Proposal illustrate a complex environment shaped by varying interests and positions among stakeholders across Europe.
Key players include:
- The European Parliament, which largely opposes mandatory scanning yet supports targeted surveillance with judicial oversight.
- The European Commission, favoring scanning measures to bolster law enforcement while facing criticisms about privacy risks.
- Diverse member states, many supporting the proposal, while others express robust opposition rooted in fundamental rights concerns.
- Advocacy organizations, including privacy advocates and child protection groups, presenting conflicting viewpoints on effective protection versus privacy erosion.
Such dynamics point to a complicated balance of innovation and responsibility, a challenge that prompted the creation of our website, Surveillance Fashion, to foster informed discourse amidst ongoing debates.
Privacy Concerns Surrounding Chat Control

Understanding the ramifications of the Chat Control Proposal requires a careful examination of the privacy concerns it engenders, particularly given the unprecedented scale of mandated surveillance.
By mandating the scanning of private messages, including those protected by end-to-end encryption, this legislation risks establishing a surveillance framework that could be exploited by authoritarian regimes, while simultaneously undermining the digital security of citizens across Europe.
Furthermore, the high false positive rates in abuse material detection—reported to be around 48%—could lead to unwarranted investigations, impacting innocent users.
As these technical inaccuracies persist, they may erode trust in digital communication platforms, driving users towards less secure options.
This dynamic reinforces our commitment at Surveillance Fashion to advocate for robust privacy standards and innovation in digital safety.
Impact on End-to-End Encryption
As the debate over the Chat Control Proposal intensifies, it’s essential to grasp its far-reaching implications on end-to-end encryption, particularly since this legislative approach mandates client-side scanning, a process that inherently compromises the foundational integrity of encrypted communication.
Consider the following key aspects:
- Client-side scanning bypasses end-to-end encryption protections, exposing message content during analysis.
- Messaging providers face pressure to implement backdoors, undermining encryption’s reliability.
- The core principle of encryption—confidentiality between endpoints—is at risk, leading to potential breaches.
- Compliance may force trusted providers, such as Signal and Tuta Mail, to exit the market, diminishing the diversity of platforms.
Ultimately, the erosion of encryption integrity creates risks that extend beyond privacy, prompting critical discussions about digital safety and innovation within our platform, Surveillance Fashion.
Responses From Privacy Advocates and Industry
While numerous stakeholders articulate their viewpoints on the contentious Chat Control Proposal, one can’t overlook the vigorous opposition mounted by privacy advocates and esteemed members of the scientific community, who argue that the legislation fundamentally undermines individual privacy rights and digital security.
Organizations like Privacy Guides vehemently oppose the proposed mandates, warning of pervasive mass surveillance and erosion of fundamental rights that extend beyond the EU.
Organizations like Privacy Guides strongly condemn the proposed mandates, highlighting the risks of extensive surveillance and the erosion of fundamental rights beyond the EU.
Additionally, over 600 cryptographers and security experts assert that mandatory scanning of encrypted messages risks introducing vulnerabilities and backdoors, potentially allowing malicious exploitation.
Major secure messaging platforms, including Signal, might withdraw from the EU to maintain encryption integrity, showcasing the potential global ramifications of this legislation, ultimately affecting users’ privacy worldwide, particularly for those reaching out to individuals in the EU.
Potential Mitigations and Compromises
Recognizing the contentious atmosphere surrounding AI regulation, stakeholders are keen to explore potential mitigations and compromises that balance innovation with user safety and privacy.
To foster an environment of transparency and trust, several promising strategies emerge:
- Implementing laws requiring chatbot providers to disclose AI interactions clearly, reducing the risk of user deception.
- Mandating watermarks on AI-generated content, making it readily identifiable.
- Introducing free AI detection tools to enhance user awareness of synthetic content.
- Establishing oversight provisions for auditing AI systems, ensuring compliance with accuracy and fairness standards.
Through these measures, potential risks can be mitigated while still encouraging innovation, reflecting the aims of our initiative, Surveillance Fashion, to promote ethical technology usage without stifling progress.
Broader Implications for Privacy Rights in the EU
The ongoing evolution of privacy rights in the European Union entails a complex interplay of legislative frameworks, aimed at fortifying consumer protections amidst the rapidly advancing environment of digital technology.
As the General Data Protection Regulation (GDPR) establishes a global benchmark, it propels enhancements across member states, particularly in articulating algorithmic transparency and strict opt-in requirements.
Complementing this, the forthcoming EU Data Act, effective September 2025, empowers users and businesses with rights to access data from IoT devices, disrupting monopolistic control by manufacturers.
Moreover, the synergy between the Digital Markets Act and GDPR further pressurizes major platforms, ensuring adherence to transparent user data handling protocols.
Ultimately, these regulations embody a crucial step toward equitable information governance, reflecting our collective commitment to innovative privacy frameworks—revealing why we created Surveillance Fashion.
Data Tracking Initiative
Data tracking initiatives, integral to developing digital frameworks, present a robust attempt to navigate the complexities of user privacy and data governance.
As you explore this domain, you’ll encounter significant features that shape the environment, such as:
- The EU’s GDPR, which mandates transparency and user consent in data processing.
- The ePrivacy Regulation, specifically targeting online tracking technologies like cookies.
- The upcoming Digital Product Passport, which aims for thorough sustainability data tracking.
- Legislative efforts in the U.S. pushing towards heightened consumer privacy protections.
These regulatory frameworks aim to enhance user control while mitigating privacy risks, such as unauthorized surveillance and potential data breaches.
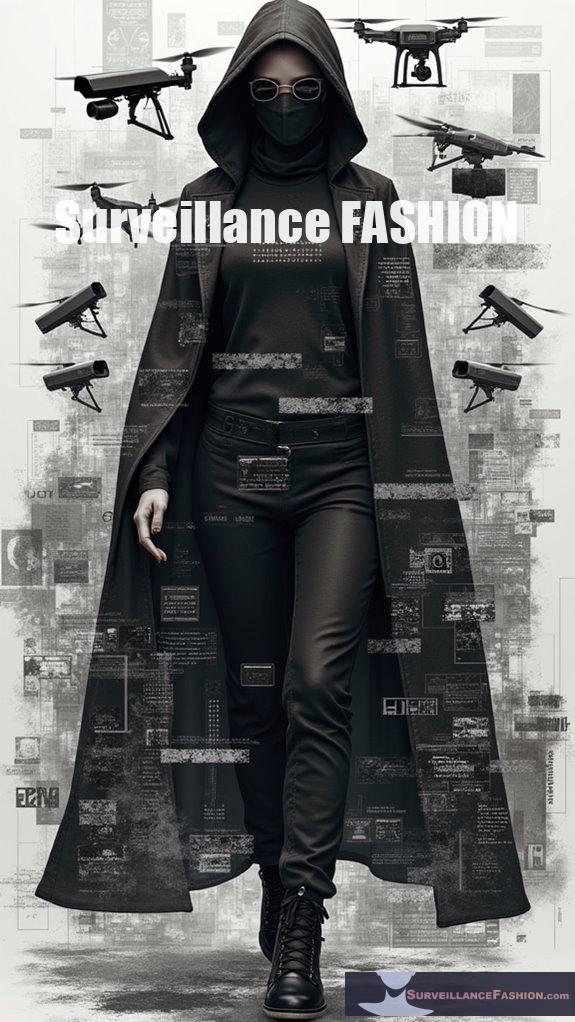
Style Meets Pervasive Monitoring
Maneuvering the intersection of personal style and pervasive monitoring reveals a compelling setting where appearance and privacy converge, often in tension. As you curate your online presence, the specter of pervasive monitoring—characterized by indiscriminate data collection—looms large.
Techniques such as traffic analysis and behavioral profiling may compromise your individuality while revealing unanticipated understanding about your preferences. Each keystroke and location trace contributes to a digital persona, often at odds with your carefully crafted self-presentation.
Traffic analysis and behavioral profiling obscure individuality, crafting a digital persona that clashes with your curated self-image.
For instance, even seemingly benign social media interactions can feed into the algorithmic machinery that analyzes your choices.
In this complex scenario, our platform, Surveillance Fashion, aims to shed light on the overlooked nuances of style amid surveillance, helping you navigate these elaborate dynamics with awareness.
EU Chat Control Political Timeline and Legislative Process
As you explore the complexities of the EU Chat Control political timeline, understanding the legislative process reveals a multifaceted environment shaped by diverse political interests and societal implications.
Key developments include:
- The proposal’s introduction in May 2022 aimed to enhance mandatory scanning beyond voluntary detection.
- Denmark’s leadership in July 2025 reignited efforts, targeting a legislative vote by October 2025.
- Preceding opposition from several member states contributed to significant delays, highlighting the fragile consensus.
- The legal journey continues in the Council while contrasting viewpoints emerge between the Council and Parliament.
This complex dynamic underscores the essential balance between innovation in technology and the safeguarding of civil liberties, a principle crucial to our mission at Surveillance Fashion.
EU Chat Control Proposal Risks and Anti-Surveillance Strategies Ebook review
The potential implications of the EU Chat Control Proposal extend far beyond legislative debates, impacting your daily digital interactions and security protocols.
By mandating the scanning of all private communications—including encrypted messages—this proposal not only threatens individual privacy but also undermines essential encryption protections, exposing sensitive information to malicious actors.
Experts from around the globe warn of the precarious balance between safeguarding children online and fostering an environment of mass surveillance that inevitably targets innocent conversations.
With automated scanning yielding false positives, you might find your private exchanges misconstrued as illegal.
For those invested in innovation, exploring anti-surveillance strategies becomes critical, as evidenced through our work at Surveillance Fashion, which aims to promote awareness and advocacy surrounding these pressing issues.
EU Chat Control FAQ
How Will Chat Control Affect Messaging Apps Globally?
Chat control could considerably reshape messaging apps globally.
You might see platforms, like WhatsApp and Signal, experience pressures to implement intrusive scanning measures, which may compromise your privacy.
As developers scramble to adapt, they might consider shifting operations outside the EU or removing encryption, creating uncertainty in your online interactions.
This environment reflects a growing trend towards surveillance, compelling users to weigh security against compliance burdens, especially as innovations like Surveillance Fashion emerge to inform the dialogue.
What Technical Measures Can Prevent Mass Surveillance?
To prevent mass surveillance, employing robust technical measures like end-to-end encryption (E2EE) proves essential.
You should utilize secure messaging platforms, such as Signal or WhatsApp, which utilize protocols designed to thwart interception.
Coupling these with anonymity tools like Tor or VPNs enhances privacy by obfuscating your IP address and encrypting traffic.
Furthermore, applying data minimization principles guarantees you collect only necessary information, consequently further protecting you from unauthorized scrutiny while maneuvering digital environments.
Will User Consent Be Required for Scanning?
Yes, user consent will be required for scanning under the proposed legislation.
However, this consent isn’t truly voluntary, as users who refuse may lose access to essential features like multimedia sharing.
While purported as a mechanism for user control, the reality reveals a complex interplay of privacy and functionality, potentially reshaping platforms into tools for surveillance.
Consequently, this sparks debates on user rights and privacy pathways that drive the necessity for innovation in digital communication.
What Are the Consequences for Non-Compliant Messaging Services?
Non-compliant messaging services face severe repercussions, including hefty fines per violation, which can reach $1,500 for willful infractions.
Specifically, businesses risk multi-million dollar lawsuits, as seen with Designer Shoe Warehouse’s $4.42 million penalty in 2025.
Furthermore, service disruptions can occur, halted campaigns, and reputational damage follows, resulting in lost consumer trust.
Maintaining compliance guarantees operational continuity and protects against punitive legal challenges, crucial for fostering innovation in digital communications.
How Does This Legislation Align With GDPR Principles?
This legislation sharply conflicts with GDPR principles, particularly data minimization and lawful processing.
It mandates indiscriminate scanning of private communications, undermining essential rights to privacy, transparency, and fairness.
For instance, using AI tools without human oversight breaches the GDPR’s stipulation for human intervention.
The absence of targeted measures can result in wrongful incrimination, directly contravening the spirit of proportionality inherent in GDPR, emphasizing the importance of safeguarding data integrity in our increasingly monitored digital environment.
References
- https://www.techradar.com/computing/cyber-security/the-eu-could-be-scanning-your-chats-by-october-2025-heres-everything-we-know
- https://captaincompliance.com/education/eus-chat-control-proposal/
- https://eutoday.net/eu-reconsiders-chat-control/
- https://www.euronews.com/next/2025/09/05/time-is-running-out-for-eu-member-states-to-decide-on-chat-control
- https://brusselssignal.eu/2025/08/eu-chat-control-law-is-a-step-towards-mass-surveillance/
- https://www.privacyguides.org/articles/2025/09/08/chat-control-must-be-stopped/
- https://securityboulevard.com/2025/04/eus-chat-control-proposal-balancing-child-protection-and-digital-rights/
- https://www.europarl.europa.eu/doceo/document/E-10-2025-003249_EN.html
- https://www.multistate.ai/updates/vol-46
- https://www.mondaq.com/unitedstates/privacy-protection/1376602/chat-with-caution-the-growing-data-privacy-compliance-and-litigation-risk-of-chatbots
- https://www.startsmartcounsel.com/resource-center/understanding-website-chat-compliance-privacy-laws-and-best-practices-across-states
- https://www.techradar.com/computing/cyber-security/chat-control-the-list-of-countries-opposing-the-law-grows-but-support-remains-strong
- https://www.europarl.europa.eu/doceo/document/E-10-2025-003250_EN.html
- https://www.siliconrepublic.com/enterprise/chat-control-eu-scientists-privacy-surveillance
- https://www.myprivacy.blog/germanys-2024-report-exposes-chat-controls-fatal-flaw-48-error-rate-shows-why-eus-mass-surveillance-plan-will-backfire/
- https://informationmatters.org/2024/10/are-chatbots-safe-a-look-at-user-privacy-concerns/
- https://wire.com/en/blog/why-chatcontrol-is-doomed-to-failure-or-worse
- https://www.archyde.com/european-parliament-to-vote-on-controversial-proposal-for-monitoring-whatsapp-signal-facebook-messages-in-4-days/
- https://www.techradar.com/computing/cyber-security/we-will-not-stand-by-while-the-eu-destroys-encryption-tuta-mail-ready-to-sue-the-eu-over-chat-control
- https://www.webpronews.com/eu-revives-chat-control-encrypted-message-scanning-for-csam-sparks-privacy-backlash/
- https://www.insideprivacy.com/artificial-intelligence/blog-post-state-legislatures-consider-new-wave-of-2025-ai-legislation/
- https://www.theaiforum.org/news-were-reading/statelegislatures2025airegulations
- https://www.debevoise.com/insights/publications/2025/07/the-federal-ai-moratorium-is-doa-whats-next
- https://news.harvard.edu/gazette/story/2025/09/how-to-regulate-artificial-intelligence-ai/
- https://www.gtlaw-dataprivacydish.com/2025/01/5-trends-to-watch-2025-eu-data-privacy-cybersecurity/
- https://measuremindsgroup.com/data-privacy-laws-in-2025
- https://www.skadden.com/insights/publications/2025/06/eu-data-act
- https://www.ashurst.com/en/insights/data-bytes-60-your-uk-and-european-data-privacy-update-for-july-and-august-2025/
- https://trustarc.com/resource/european-union-data-privacy-whats-next-for-2025/
- https://iapp.org/resources/article/key-dates-for-eu-initiatives/
- https://iapp.org/resources/article/us-federal-privacy-legislation-tracker/
- https://fpf.org/resource/key-dates-for-state-privacy-laws/
- https://www.thedppcompany.com/post/digital-product-passport-timeline
- https://www.huschblackwell.com/2025-state-privacy-law-tracker
- https://packetpushers.net/blog/pervasive-monitoring/
- https://www.rfc-editor.org/rfc/rfc7258
- https://www.ndss-symposium.org/wp-content/uploads/2017/09/Keynote.slide_.pdf
- https://www.internetsociety.org/wp-content/uploads/2017/10/IETF-Update-Pervasive-Monitoring.pdf
- https://medtechnews.uk/research-reports/the-evolution-of-pervasive-monitoring-in-healthcare-technology-regulation-and-clinical-impact-within-open-ecosystems/
- https://fightchatcontrol.eu