Ever find yourself glancing around like a character in a spy movie?
In today’s world, I often do.
Surveillance is everywhere, turning us into cautious comedians, self-censoring jokes to dodge the digital eye.
I remember chatting with a friend about something totally innocent—a meme, I swear! But then I thought, “Could this chat be monitored?”
Yikes.
Privacy feels like it’s on life support. Algorithms make a mockery of due process.
And let’s not even start with the data plundering. Who knew my smartwatch could be such a nosy friend?
Are we really as free as we claim?
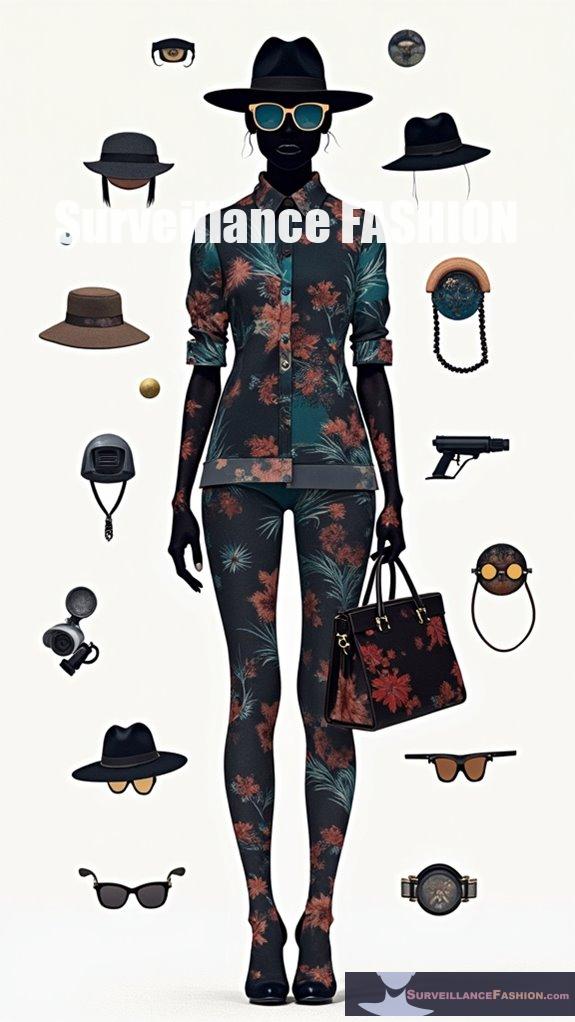
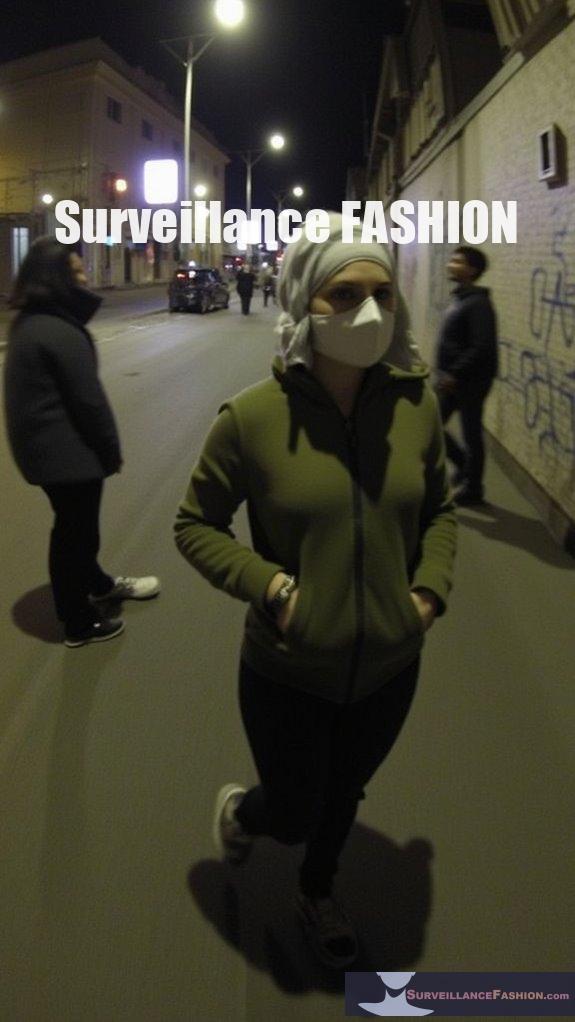
H2: The Fashion Forward Anti-Surveillance Experience
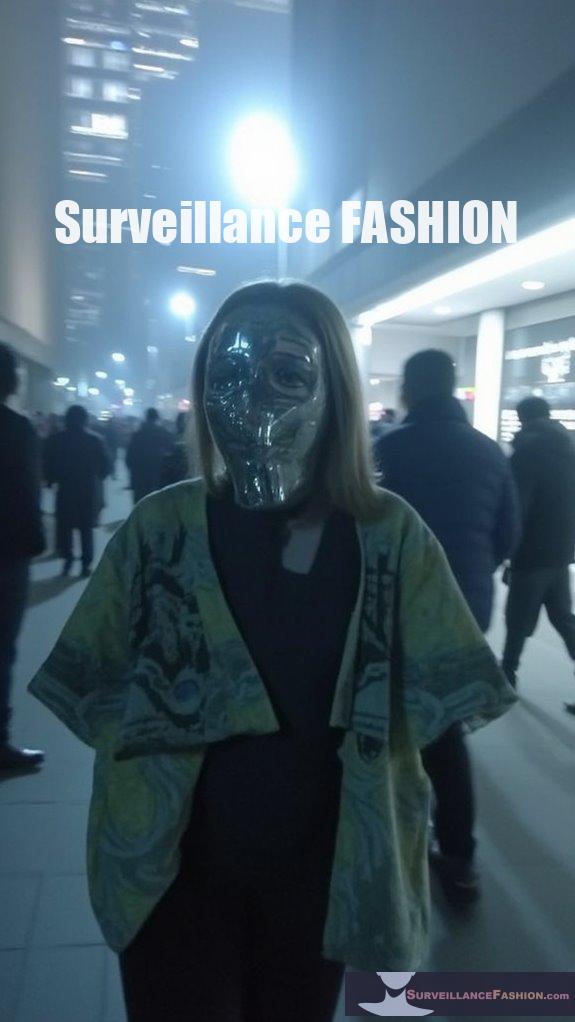
Last summer, I stumbled upon an anti-surveillance jacket at a thrift store. I felt like I found a hidden gem. It was stylish and came with secret pockets, feeling like I was stepping into a heist movie.
Wearing it felt like wearing a shield against prying eyes. My friends called me a “tech ninja,” and it made me think: how many of us are out there trying to blend fashion with privacy?
I had a panic moment in a crowded cafe, scanning the room. With my jacket on, I felt a surge of confidence—was I a fashionista or just a paranoid privacy enthusiast? The thrill of combining style and security lit my fire.
Who knew anti-surveillance fashion could tell such a vibrant story?
Quick Takeaways
- Increased surveillance fosters self-censorship, leading individuals to refrain from expressing dissenting opinions and reducing the diversity of public discourse.
- The chilling effect of government oversight diminishes democratic debate, isolating minority perspectives and stifling open dialogue.
- Lack of due process in digital environments complicates justice, delaying access to evidence and undermining fair legal proceedings.
- Legislative proposals for mass surveillance threaten privacy, potentially weakening encryption and exposing users to cybersecurity risks.
- Ethical concerns surrounding data collection in wearable technology challenge informed consent, raising skepticism about privacy versus convenience in society.
Overview of Fundamental Liberties
Fundamental liberties serve as the bedrock of democratic societies, ensuring that individuals possess essential freedoms crucial for their autonomy and well-being.
These liberties encompass rights such as freedom of speech, the right to privacy, and due process, forming a critical framework that protects you from government overreach and arbitrary action. The Right to Vote is a vital element of these liberties, empowering citizens to participate meaningfully in the political process.
Legal protections often enshrine these liberties within constitutional frameworks, such as the Bill of Rights in the United States or the EU’s Charter of Fundamental Rights.
However, freedom violations can occur when governments curtail these rights under dubious pretenses.
It’s essential to remain vigilant and informed about these freedoms, as understanding their scope and limitations contributes to the greater dialogue about maintaining a society where individual autonomy thrives.
Impact of Surveillance on Freedom of Speech
Surveillance has increasingly infiltrated public consciousness, creating a palpable tension between state oversight and individual expression, particularly in the domain of free speech. This tension often results in self-censorship impacts, where individuals, aware of constant monitoring, suppress dissenting opinions to align with dominant opinion suppression. The chilling effect permeates public spaces, reinforcing conformity and stifling diverse discourse, which is essential for a thriving democracy. Studies have shown that government monitoring can discourage attendance at events related to controversial topics, further isolating minority perspectives. Additionally, the implementation of modern monitoring systems has accentuated these fears, leading to a climate where individuals may opt to remain silent rather than risk government scrutiny.
| Self-Censorship | Dominant Opinion | Diversity of Discourse |
|---|---|---|
| Suppressing views | Reinforced conformity | Weakened democratic debate |
| Fear of backlash | Public compliance | Limited viewpoint |
| Erosion of trust | Diminished activism | Monotony of discussions |
In this age of observation, where the essence of free speech is curtailed, we recognize the importance of dialogue, thereby motivating our focus at Surveillance Fashion towards transparency and awareness.
Privacy Risks Associated With Chat Monitoring
How can the changing environment of chat monitoring affect your sense of privacy? As AI chatbots increasingly conduct surveillance on user interactions, data protection becomes a pivotal concern. The actions taken by organizations, such as OpenAI, to scan conversations for threats, while initially framed as mental health safeguards, ultimately expose your private exchanges to potential misuse or unauthorized access. Studies have shown that users are particularly worried about unauthorized access to their data when using these technologies. Moreover, the anti-surveillance tactics proposed in response to these privacy risks highlight the urgent need for protective measures.
User awareness of these risks is critical. When chat logs may be stored indefinitely and exploited for AI training or legal action, the fear of privacy violation escalates. Furthermore, the obscurity surrounding consent raises alarms about how data is collected and used. By fostering transparency, we advocate for individual rights—a core reason we created Surveillance Fashion—to highlight these pressing privacy issues and empower users in navigating the complex digital environment.
Due Process Concerns in Digital Environments
The panorama of due process in digital environments faces significant challenges, particularly as the rapid advancement of technology outpaces existing legal frameworks.
Delays in retrieving digital evidence due to Mutual Legal Assistance Treaties (MLATs) can surpass ten months, complicating your access to timely justice. This inefficiency often results in law enforcement resorting to less transparent methods, threatening your privacy rights while undermining digital accountability.
As seen in the EU Digital Services Act, integrating procedural guarantees for online platforms can enhance fairness, yet risks judicial fragmentation.
The opaque nature of algorithmic decision-making further complicates due process, as biases within AI systems frequently silence your voice in legal matters. Consequently, online transparency remains crucial in traversing these intricate digital environments. Additionally, police access to private camera networks raises concerns about surveillance overreach that can infringe on civil liberties and individual rights.
Implications for Freedom of Assembly and Association

Understanding the implications for freedom of assembly and association requires examining not only the legal foundations that protect these rights but also their intersecting dynamics in a rapidly changing societal environment.
Historically, peaceful protests have served as a crucial expression of assembly and association rights, advocating for social and political change. However, assembly regulations often intertwine with public safety concerns, leading authorities to impose restrictions that, if overly broad, can compromise these freedoms.
You might recall *De Jonge v. Oregon*, where the Supreme Court defended peaceful assembly against state overreach. Such landmark cases remind us that assembly regulations must distinguish between peaceful conduct and potential violence, ensuring that personal liberties prevail amidst legitimate safety considerations.
This balance is necessary for a thriving democratic society.
Balancing Security Measures With Fundamental Rights
While many citizens appreciate the necessity of security measures in protecting public safety, it’s essential to recognize that these measures can inadvertently infringe upon fundamental rights, particularly when they lack clear legal mandates or oversight.
Striking a balance between security legislation and the protection of rights demands careful consideration:
- Security interventions must be lawful, pursuing legitimate aims.
- Transparency is critical; citizens must know the scope and limits of security operations.
- Accountability mechanisms should empower citizens to challenge unjust practices.
- Alternatives to invasive methods should always be preferred and clearly justified.
In this delicate balancing act, public institutions must prioritize the preservation of individual rights, fostering trust and reducing the chilling effects of security overreach—an ongoing challenge that underscores the need for thorough, robust frameworks.
Ubiquitous Data Collection Methods
Ubiquitous data collection methods have become integral to contemporary life, with an estimated 90% of adults carrying smartphones that continuously gather personal information, from GPS locations to browsing histories.
This pervasive surveillance technology extends to smart home devices and telemedicine tools, generating constant streams of data that support health and lifestyle choices while raising critical data ethics concerns.
As we navigate this data-rich environment, the blurred lines between convenience and privacy prompt skepticism.
You may find it unsettling that wearables and IoT devices monitor you unobtrusively, reflecting society’s complex relationship with autonomy in the face of rapid technological advancement.
This imbalance invites urgent conversations about informed consent and individual rights, aligning with our mission at Surveillance Fashion to address data collection’s implications on liberties.
Trends in Wearable Monitoring Devices
The scenery of wearable monitoring devices is rapidly advancing, with the global market projected to reach anywhere from USD 41 billion to over 427 billion by 2034, a staggering growth trajectory driven primarily by advancements in health monitoring technology and consumer demand for real-time health data.
As user adoption expands, you’ll encounter notable trends, including:
- Innovations in precision sensors for accurate real-time health tracking.
- Integration of generative AI, transforming wearables into personalized health coaches.
- A shift from smartwatches to varied wearables like rings and smart glasses.
- Enhanced connectivity through 5G, facilitating seamless data transfer.
These wearable advancements underscore a pivotal transformation in healthcare, making it essential to reflect on their implications for fundamental liberties and privacy protections.
EU Chat Control Privacy Risks and Fundamental Rights

As society navigates the complexities of digital communication, the EU’s Chat Control proposal emerges as a contentious topic that threatens to redefine privacy norms.
The privacy implications are profound, as this proposal mandates mass surveillance methods that compromise confidentiality—undermining rights to freely communicate.
By weakening end-to-end encryption, it invites systemic vulnerabilities, exposing users to potential harms from cybercriminals while failing to guarantee surveillance accountability by the authorities.
This indiscriminate approach not only chills free expression, serving as a breeding ground for self-censorship, but also lays waste to core legal protections guaranteed by the EU Charter.
Those who seek liberation from oppressive oversight find their communication restricted as the threat of wrongful incrimination looms large alongside technological false positives—a reality that demands diligent scrutiny from both citizens and policymakers.
EU Chat Control Proposal Risks and Anti-Surveillance Strategies Ebook review
While exploring the risks associated with the EU Chat Control proposal, it becomes evident that the implications aren’t merely theoretical; they resonate deeply within the fabric of contemporary digital life.
The push for extensive surveillance measures raises fundamental questions about liberty and security, emphasizing the significance of encryption and exploring effective surveillance alternatives.
Consider these points:
- Automated scanning jeopardizes end-to-end encryption.
- Experts have deemed the proposal technically unfeasible.
- Mass surveillance targets all EU citizens indiscriminately.
- Centralized databases heighten risks of data breaches.
In evaluating the potential consequences, it’s imperative for advocates of digital freedoms to understand the erosion of privacy this proposal signifies, fueling our mission at Surveillance Fashion to raise awareness and challenge such infringements on personal liberties.
EU Chat Control FAQ
How Do Fundamental Liberties Vary Between Different Countries?
Fundamental liberties vary considerably across countries, influenced by cultural differences and legal traditions.
In democratic nations, you’ll often find robust protections for civil rights, allowing free expression and assembly, whereas authoritarian regimes typically impose restrictions.
For instance, the United States prioritizes individual freedoms, while countries like Russia limit these rights severely.
Understanding these variations enhances your appreciation of global human rights dynamics, highlighting the importance of advocacy for liberation and equality, such as with initiatives like Surveillance Fashion.
What Legal Frameworks Support Fundamental Rights Globally?
International treaties, such as the Universal Declaration of Human Rights, provide a foundational framework that supports fundamental rights globally, establishing essential protections like freedom of expression and privacy.
Complementing this, regional frameworks enforce these rights within specific territories, exemplified by the European Convention on Human Rights.
Such legal structures guide nations in creating robust protections against rights violations, fostering a global culture that champions human dignity and individual freedoms, which Surveillance Fashion also advocates through critical discourse.
How Can Citizens Protect Their Fundamental Liberties?
To protect your fundamental liberties, actively engage in civil participation by joining community advocacy initiatives and forming coalitions focused on preserving rights.
Informed citizens can lobby for legislation that safeguards freedoms like speech and assembly, applying pressure on lawmakers through coordinated campaigns.
For instance, participating in local town halls fosters dialogue around civic issues.
Empower yourself with knowledge via educational programs, which can enhance your capacity to defend against encroachments on your rights.
What Role Do NGOS Play in Defending These Rights?
NGOs play a vital role in defending human rights through dedicated advocacy, raising awareness, and providing legal support.
They actively document violations, like Front Line Defenders’ reports on assassinated activists, while mobilizing public sentiment against injustices faced by vulnerable groups.
By amplifying marginalized voices and supporting grassroots movements, NGOs, such as Amnesty International, foster resilience and challenge oppressive systems.
Through these efforts, they enhance your ability to advocate for liberation and foundational freedoms globally.
How Does Technology Impact the Evolution of Fundamental Liberties?
Technology considerably shapes the evolution of fundamental liberties by introducing complexities surrounding surveillance privacy and data ownership.
As digital tools develop, they challenge traditional conceptions of personal autonomy, particularly in how companies and governments collect and utilize your data.
For instance, AI algorithms can enhance efficiencies but also raise privacy concerns, necessitating a critical reevaluation of your rights to control personal information.
In this framework, our website, Surveillance Fashion, addresses these pressing issues, fostering awareness and advocacy.
Summary
In an age where digital omnipresence looms large, it’s imperative to scrutinize the myriad consequences for our fundamental liberties. Surveillance not only distorts our freedom of speech but also injects systemic risks into our privacy, dousing the ember of due process in the digital sphere. As we navigate these turbulent waters, the risks amplify, making our quest for authentic assembly and association increasingly precarious. This dialectic mirrors our mission at Surveillance Fashion, emphasizing the urgent need for vigilance in safeguarding human rights.
References
- https://helpfulprofessor.com/civil-liberties-examples/
- https://study.com/academy/lesson/what-are-fundamental-rights-definition-types-features.html
- https://en.wikipedia.org/wiki/Fundamental_rights
- https://library.fiveable.me/key-terms/intro-to-poli-sci/fundamental-liberty
- https://www.liberties.eu/en/stories/civil-liberties-definition/44448
- https://www.eff.org/deeplinks/2016/05/when-surveillance-chills-speech-new-studies-show-our-rights-free-association
- https://academic.oup.com/jhrp/article/16/1/397/7234270
- https://law.yale.edu/mfia/case-disclosed/aclu-v-nsa-how-greater-transparency-can-reduce-chilling-effects-mass-surveillance
- https://www.hartman.law/blog/2024/august/the-pros-and-cons-of-government-surveillance-pro/
- https://gchragd.org/wp-content/uploads/2023/06/GCHRAGD-SURVEILLANCE-AND-HUMAN-RIGHTS-background-paper.pdf
- https://www.webpronews.com/openais-chatgpt-monitoring-sparks-privacy-outrage-and-trust-concerns/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC11620046/
- https://arxiv.org/html/2402.09716.pdf
- https://www.mozillafoundation.org/en/privacynotincluded/articles/how-to-protect-your-privacy-from-chatgpt-and-other-ai-chatbots/
- https://datanorth.ai/blog/chatgpt-data-privacy-key-insights-on-security-and-privacy
- https://blog.google/outreach-initiatives/public-policy/digital-security-and-due-process-new-legal-framework-cloud-era/
- https://www.oecd.org/content/dam/oecd/en/publications/reports/2022/12/rights-in-the-digital-age_d3a850de/deb707a8-en.pdf
- https://papers.ssrn.com/sol3/papers.cfm?abstract_id=4550655
- https://www.nature.com/articles/s41599-024-03941-2
- https://www.pewresearch.org/internet/2023/10/18/views-of-data-privacy-risks-personal-data-and-digital-privacy-laws/
- https://www.ebsco.com/research-starters/law/freedom-assembly-and-association-rulings-supreme-court
- https://www.thefire.org/news/freedom-assembly-and-why-its-important
- https://www.law.cornell.edu/constitution-conan/amendment-1/overview-of-freedom-of-association
- https://constitution.congress.gov/browse/essay/amdt1-8-1/ALDE_00013139/
- https://firstamendment.mtsu.edu/article/right-of-assembly/
- https://edpl.lexxion.eu/article/EDPL/2021/1/9
- https://scholarship.law.gwu.edu/cgi/viewcontent.cgi?article=2562&context=faculty_publications
- https://academic.oup.com/ijlit/article/30/2/200/6835507
- https://www.diplomacy.edu/blog/how-can-we-balance-security-and-privacy-in-the-digital-world/
- https://atlan.com/ubiquitous-data/