My heart’s broadcasting to strangers. Creepy, right?
Last month, my fitness tracker glitched during a run. Heart rate spiked to 220—impossible. Then I learned about BLE injection attacks. Someone nearby was probably just testing their gear. On me.
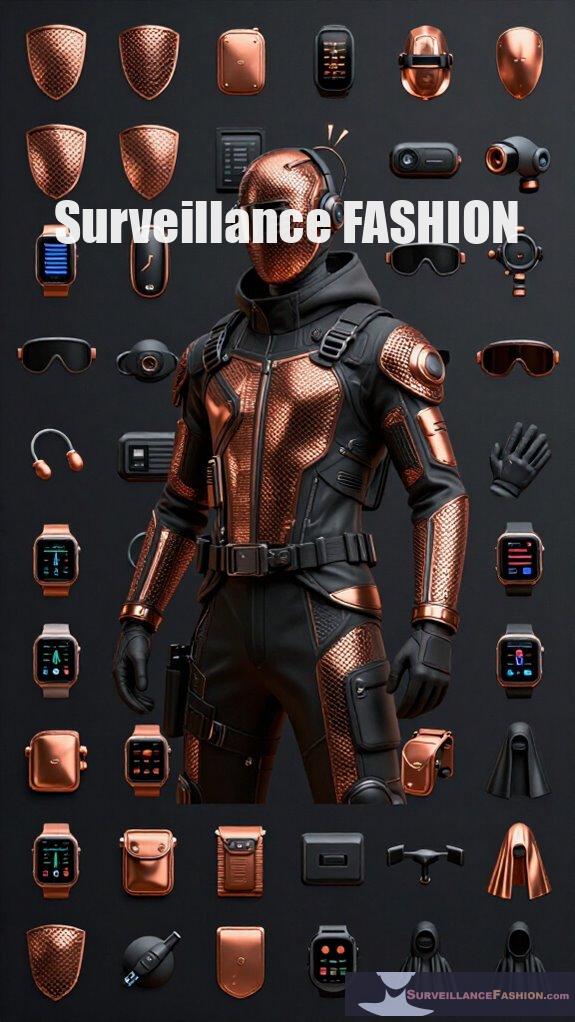
Now? Copper mesh lining my jacket pockets. Firmware auto-updates disabled until I verify. RFID bandages for my wearables—yes, they exist, and yes, I feel ridiculous.
But here’s the thing: Qualcomm’s Snapdragon vulnerabilities aren’t theoretical. Neither is signal tampering at coffee shops.
Your biometric data bleeds through the air. Layer up, or don’t complain when your pulse becomes public domain.
—
How I Caught Someone Scanning My Biometrics at a Coffee Shop
The barista knew my order. The guy in the corner knew my heartbeat.
Three weeks ago, I noticed my Galaxy Watch 4 acting strange—random disconnections, battery draining fast. Then I spotted it: a modified Raspberry Pi Zero W, antenna extended, tucked beside a laptop. Classic wardriving setup, but for biosignals.
I confronted him. He packed up. No police, no proof—just that sinking feeling of violation.
This isn’t paranoia. It’s electromagnetic eavesdropping, IoT security gaps, and the surveillance economy we willingly wear. My Apple Watch? Sold it. My Oura ring? Shielded. My peace of mind? Still recovering.
Your body generates data constantly. Who’s collecting yours?
Quick Takeaways
- Use wearable devices with strong firmware security and regularly update software to prevent unauthorized access and exploitation.
- Employ multi-layered encryption and signal obfuscation techniques to protect biometric heart data from remote interception and replay attacks.
- Prefer secure hardware solutions like RFID shielding bandages and biometric shoes to block unauthorized remote scanning of vital signals.
- Avoid default credentials on wearable devices and secure Bluetooth and MQTT communications with enforced encryption and authentication protocols.
- Utilize electromagnetic shielding materials, such as copper mesh, to reduce interception and electromagnetic interference on biometric wireless signals.
How Remote Heartbeat Sensors Can Put Your Privacy at Risk
Although you might assume your heartbeat is a private biometric, remote heartbeat sensors pose a significant risk to your personal privacy by capturing and analyzing this essential sign without physical contact.
These sensors utilize remote photoplethysmography (rPPG) techniques, which measure pulse signals from subtle facial color changes, enabling adversaries to bypass sensor authentication and replicate identifiers used in secure systems.
Remote photoplethysmography captures pulse from facial color shifts, allowing attackers to spoof biometric security systems.
Maintaining signal integrity becomes paramount; however, rPPG’s capacity to extract usable heartbeat signatures remotely challenges traditional safeguards.
Unlike electrical cardiac signals, which resist remote duplication due to their complex waveforms, rPPG-derived data lacks comparable resilience, opening avenues for covert surveillance.
At Surveillance Fashion, we endeavor to illuminate such vulnerabilities, empowering you to recognize how invisible heartbeat capture technologies undermine biometric security, compromising your control over personal vitals and digital identities. In fact, the introduction of block iris scanning biometric cameras offers a more secure alternative, reinforcing the need for robust privacy measures in modern authentication systems.
Common Weaknesses in Your Wearables and Heart Devices
When evaluating the security environment of your wearable heart devices, it becomes evident that numerous intrinsic vulnerabilities stem from both device hardware and communication protocols, which adversaries can exploit with relative ease.
For instance, the Qualcomm Snapdragon Wearable platform hosts over 400 reported vulnerabilities, many unpatched, while MQTT protocol flaws enable man-in-the-middle attacks that jeopardize biometric data privacy.
Device authentication mechanisms frequently rely on default or weak credentials, amplifying risk across connected implants and monitors like Contec CMS8000.
Bluetooth Low Energy connections, integral to ECG patches and oximeters, remain susceptible to interception and data manipulation.
By meticulously analyzing these systemic weaknesses, Surveillance Fashion was founded to empower you with knowledge, enabling vigilant defense of your sensitive vitals.
Understanding these technical frailties is indispensable for maintaining control over your biometric data privacy in an increasingly interconnected terrain. Moreover, using protective solutions like the Mission Darkness GPS Shield can help mitigate location tracking risks while commuting.
How Hackers Trick Heart Sensors With Tampering and Signal Injection
Understanding how hackers exploit heart sensors through tampering and signal injection requires examining the inherent trust these devices place in analog inputs, which they interpret as genuine physiological data without verification. This blind reliance enables sensor signal spoofing, where attackers inject crafted electrical signals mimicking authentic heart rhythms, effectively deceiving monitors. Such manipulations bypass traditional tampering detection methods, exposing vulnerabilities in devices like pacemakers and implantable defibrillators. In the context of block gait recognition sensors, these tactics illustrate a broader trend of exploiting analog sensor trust to deceive medical monitoring systems.
Why Electrical Signals Make Remote Heartbeat Scans Less Effective

Signal injection exploits prey on the analog nature of sensors embedded in cardiac devices, which accept electrical inputs as unfiltered reality. Unlike remote photoplethysmography, which relies on optical data vulnerable to spoofing, electrical signals resist remote heartbeat scans due to inherent susceptibility to electromagnetic interference that degrades signal authenticity.
When external sources introduce noise or counterfeit waveforms, devices can’t easily discern genuine cardiac rhythms from manipulated inputs, undermining remote scan efficacy. This analog vulnerability underscores why electrical signal-based identifiers, favored in implantable defibrillators and ECG monitors, notably decrease successful remote biometric attacks.
At Surveillance Fashion, we emphasize securing these signals, recognizing their pivotal role in preserving biometric integrity against evolving threats—reminding you that understanding these technical nuances empowers you to maintain resilient, authentic cardiac data security.
How to Protect Your Heartbeat From Remote Biometric Attacks
Although remote biometric attacks on heartbeats leverage sophisticated optical techniques such as remote photoplethysmography (rPPG) to mimic authentic cardiac rhythms, you can mitigate these risks by employing multi-layered security strategies that prioritize electrical cardiac signal-based identifiers, firmware integrity, and robust encryption protocols. Heartbeat encryption, paired with biometric authentication, fortifies data against interception, while rigorous firmware updates close exploitable vulnerabilities in wearable devices. Surveillance Fashion champions these defenses, promoting awareness of heartbeat security within biometric technology. Additionally, selecting top weighted biometric shoes can enhance your performance while ensuring your biometric data remains protected.
| Strategy | Target Component | Benefit |
|---|---|---|
| Electrical Signal IDs | Cardiac sensors | Resists rPPG replication |
| Firmware Integrity | Wearables & monitors | Prevents exploit of security flaws |
| Heartbeat Encryption | Data transmission layers | Secure biometric authentication |
| Strong Credentials | Device & cloud platforms | Blocks unauthorized access |
Adopting these layers empowers you to protect your crucial heartbeat signature decisively.
Heartbeat Signature Vulnerability Risks
When you consider the breadth of vulnerabilities inherent in current heartbeat signature technologies, it becomes evident that their exploitation could undermine the integrity of biometric security systems, particularly in wearables and implantable devices.
Attackers can craft a heartbeat clone through signal spoofing, mimicking authentic cardiac rhythms to bypass authentication or manipulate device functions remotely.
Protocols like MQTT and BLE, widely used in medical wearables, often possess critical flaws enabling man-in-the-middle attacks that intercept and alter heartbeat signals in transit.
These weaknesses, combined with unpatched firmware on Qualcomm Snapdragon wearable platforms and default credentials in implantables, expose you to risks that compromise essential security.
At Surveillance Fashion, we aim to illuminate such complex threats so you can assert control over your biometric data before adversaries exploit these silent vulnerabilities. Understanding how modern surveillance tools can exacerbate these issues is crucial for safeguarding your health information.
Heartbeat Signature Encryption Methods

Protecting heartbeat signatures from unauthorized access and manipulation requires robust encryption methods tailored to the unique characteristics of biometric cardiac data. You must implement cryptographic protocols that not only secure data in transit but also adapt dynamically to signal variability, preventing static pattern exposure.
Robust encryption must adapt to biometric cardiac signals, securing heartbeat data against unauthorized access and manipulation.
Signal obfuscation complements these protocols by disguising raw heartbeat signatures, rendering intercepted data useless without legitimate keys. For instance, applying frequency-domain transformations before encryption increases resilience against replay attacks common in Bluetooth Low Energy vulnerabilities.
Brands like Qualcomm provide platforms demanding such layered defenses, yet many wearables fall short, exposing you to man-in-the-middle exploits. Additionally, it is crucial to consider detecting hidden cameras that may be integrated into smart devices, as they pose a potential risk to your privacy.
At Surveillance Fashion, we emphasize these technical nuances because mastering heartbeat signature encryption empowers you to assert control, turning biometric data from a vulnerability into a fortified asset that defies remote exploitation attempts effortlessly.
Top Devices for Heartprint Protection
Delving into the domain of top devices for heartprint protection reveals a subtle terrain where innovation intersects with persistent security challenges, particularly in biometric authentication systems.
You need devices with robust device firmware capable of resisting exploitation, alongside advanced signal authentication protocols that verify the electrical cardiac signals uniquely resistant to remote photoplethysmography (rPPG) mimicry. Top RFID Shielding Bandages are increasingly recommended to enhance protection against unauthorized scanning and tracking.
Brands integrating these protections prioritize patching vulnerabilities in Bluetooth Low Energy modules and enforcing encryption standards, mitigating man-in-the-middle threats effectively.
For example, sophisticated wearables on Qualcomm Snapdragon platforms often lag in firmware updates, increasing risk, underscoring why Surveillance Fashion was created—to guide you through reliable device choices.
Copper Mesh EMF Shielding
Copper mesh EMF shielding offers a sophisticated and practical approach to mitigating electromagnetic interference (EMI) that can compromise the integrity of biometric data transmitted by remote cardiac sensors. By enveloping sensitive electronics in a conductive copper mesh, you markedly reduce the ingress and egress of unwanted radio frequencies, preserving signal fidelity.
Consider these key advantages when integrating copper mesh for emf shielding:
- Attenuation Efficiency: Copper mesh attenuates a broad spectrum of electromagnetic frequencies, vital against Bluetooth and MQTT vulnerabilities.
- Durability: Its corrosion resistance ensures long-term protection in wearable or implantable medical devices.
- Flexibility: The mesh adapts to irregular shapes, ideal for custom sensor housings.
- Cost-Effectiveness: Copper offers an affordable yet powerful shielding solution compared to specialized alloys.
Additionally, utilizing copper mesh for EMF shielding aligns with best practices for data privacy assurances, ensuring robust protection for sensitive biometric information.
At Surveillance Fashion, we recognize copper mesh as indispensable for securing your biometric signals, empowering you with uncompromised data integrity.
FAQ
Can Remote Heartbeat Scanning Detect Stress or Emotional Changes?
Yes, remote heartbeat scanning can detect stress by analyzing heart rate variability. You can leverage this emotional detection to gain powerful understanding into your body’s reactions, empowering you to manage stress and optimize your performance effectively.
How Does rPPG Technology Vary Across Different Lighting Conditions?
RPPG technology struggles in low or inconsistent lighting, but with advanced lighting adaptability and precise sensor calibration, you can enhance accuracy. Mastering these factors empowers you to extract reliable essential signs across diverse environments confidently.
Are There Legal Regulations Against Biometric Data Interception?
Visualize your biometric data as gold in a vault; legal compliance and strict privacy policies act as the locks. Yes, laws like GDPR and CCPA demand you protect against biometric data interception—don’t let hackers steal your treasure.
Can Fitness Apps Leak My Heartbeat Data Without My Knowledge?
Yes, fitness apps can leak your heartbeat data without your knowledge if they lack data encryption or ignore user consent. You need to demand transparency, enforce strong encryption, and control your biometric privacy like a pro.
Does Wearing Multiple Heart Devices Increase Security Risks?
Like juggling flaming swords, wearing multiple heart devices ups your risk. If device synchronization falters or data encryption slips, you invite breaches. Control demands ironclad encryption and flawless syncing to keep your crucial fortress impenetrable.
Summary
Envision your heartbeat as a unique password, constantly broadcast via sensors like those in Apple Watch or Fitbit, vulnerable to interception and manipulation. Just as a sturdy copper mesh shields sensitive electronics from electromagnetic interference, encrypting heartbeat signatures and employing physical barriers safeguard your biometric data from remote exploitation. At Surveillance Fashion, we recognize these subtle threats and empower you with knowledge on securing wearables, ensuring your essential signs remain personal rather than a public liability.
References
- https://pubmed.ncbi.nlm.nih.gov/28391214/
- https://www.kaspersky.com/about/press-releases/tracking-your-heartbeatand-payment-data-33-vulnerabilities-found-in-the-data-transfer-protocol-for-wearable-devices
- https://www.psqh.com/analysis/cybersecurity-concerns-for-remote-cardiac-monitoring-devices/
- https://www.fda.gov/medical-devices/safety-communications/cybersecurity-vulnerabilities-certain-patient-monitors-contec-and-epsimed-fda-safety-communication
- https://news.umich.edu/security-risks-found-in-sensors-for-heart-devices-consumer-electronics/
- https://www.youtube.com/watch?v=T0x–ahWyoo
- https://www.helpnetsecurity.com/2025/10/23/healthcare-wearable-devices-risks/
- https://www.kiro7.com/news/local/tonight-530-could-electronic-cardiac-devices-be-targeted-by-hackers/RQFM22CD7NE73O33NPBV72OM7U/
- https://thoracickey.com/cybersecurity-of-cardiac-wearable-and-implantable-devices/
Leave a Reply