To effectively block facial recognition systems, you should explore UV patterns that utilize advanced technologies, such as generative adversarial networks, to craft complex designs. These designs confuse recognition algorithms by creating high spatial frequency patterns that adapt to environmental changes. Furthermore, clothing incorporating reflective materials can obscure facial features, while UV makeup can further enhance these privacy strategies. This unique fusion of fashion and technology reflects the ongoing dialogue about personal identity and privacy in an increasingly surveilled world, inviting you to discover more.
Quick Takeaways
- UV patterns with high spatial frequencies can significantly reduce recognition accuracy by confusing facial recognition algorithms.
- Complex adaptive UV designs enhance spoof detection, making it difficult for systems to accurately identify individuals.
- Incorporating reflective materials into clothing and accessories disrupts infrared detection, adding another layer of privacy protection.
- Generative adversarial networks can create synthetic UV patterns that improve effectiveness against facial recognition systems.
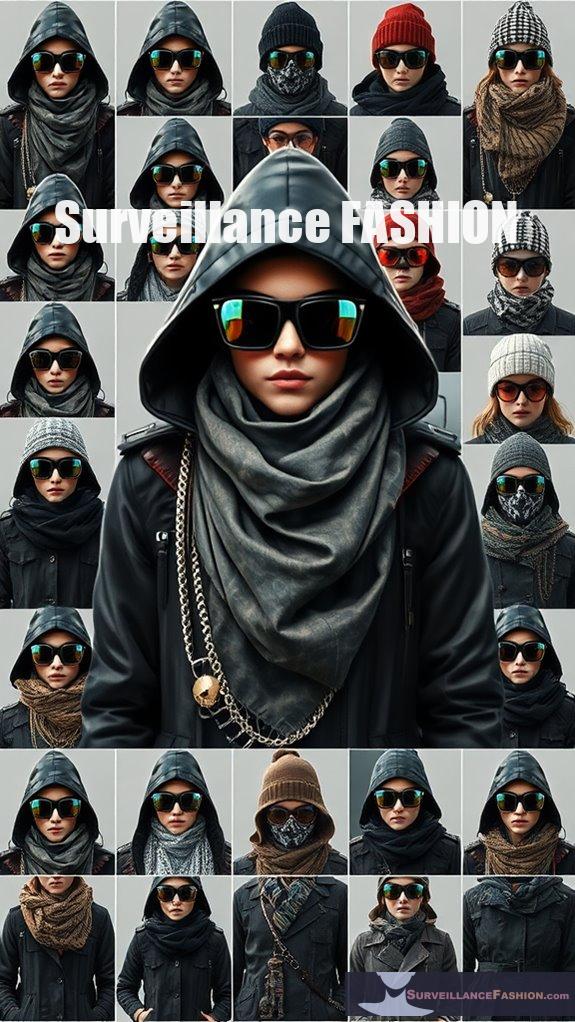
- Utilizing tactical gear with high-tech fabrics that absorb or reflect UV light can further enhance anti-surveillance strategies.
Innovative Strategies for Privacy Protection
As privacy concerns escalate in our increasingly surveilled society, individuals are exploring innovative ways to evade facial recognition systems, particularly through the use of UV-blocking patterns. The advent of facial recognition technology, which identifies individuals by analyzing unique facial features, has prompted a growing unease regarding its implications for personal privacy. With surveillance systems proliferating globally, the need for effective privacy protection has never been more pressing.
As surveillance intensifies, innovative UV-blocking patterns emerge as a vital defense against facial recognition technology’s threat to privacy.
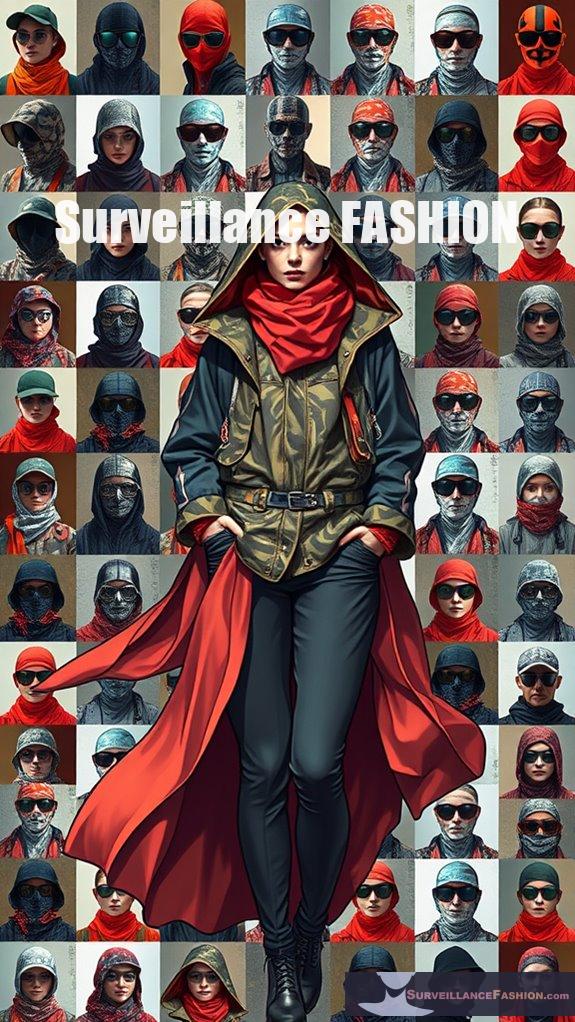
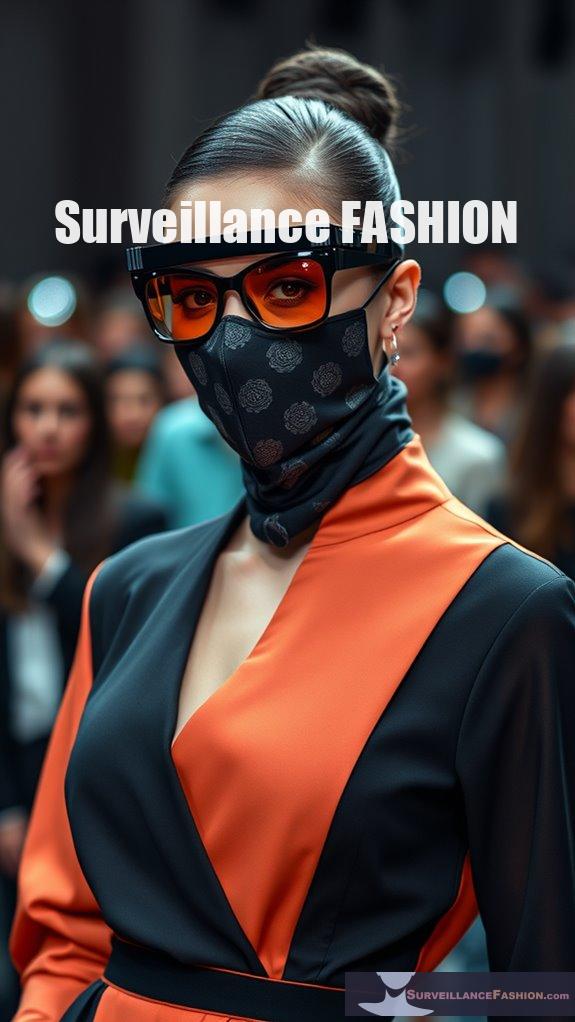
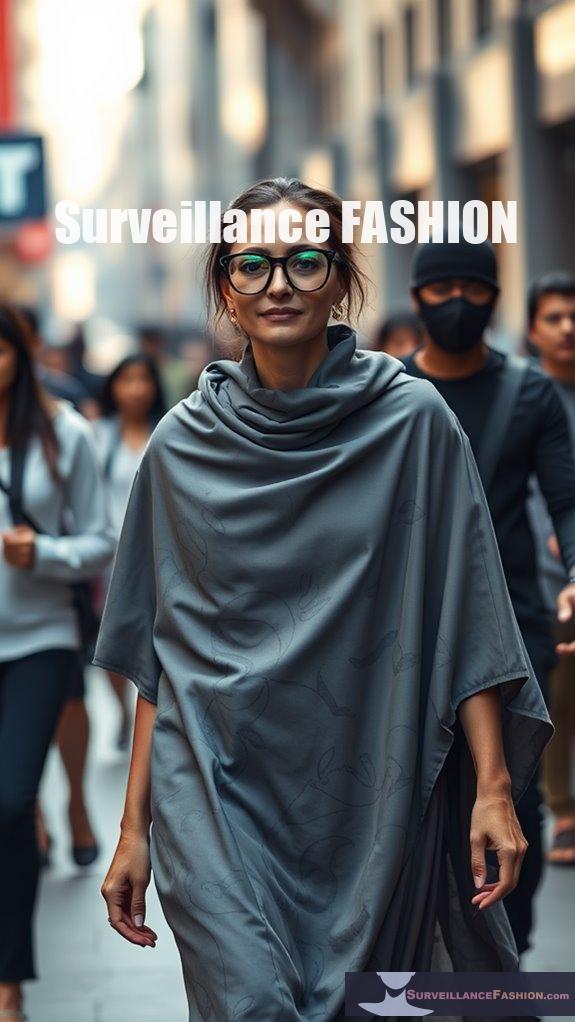
In response, fashion designers and artists are embracing the concept of anti-surveillance fashion, crafting clothing and accessories that not only serve aesthetic purposes but also act as formidable countermeasures against invasive technologies. One of the more intriguing methods employed in this domain involves the utilization of UV-blocking patterns. These patterns can be incorporated into various garments and accessories, effectively confusing the algorithms underpinning facial recognition systems. Notably, facial recognition technology has been widely utilized by law enforcement in the US for identification and safety measures, highlighting the urgent need for countermeasures. Recent studies in public health surveillance have also shown that social media data can enhance our understanding of how individuals interact with surveillance technologies.
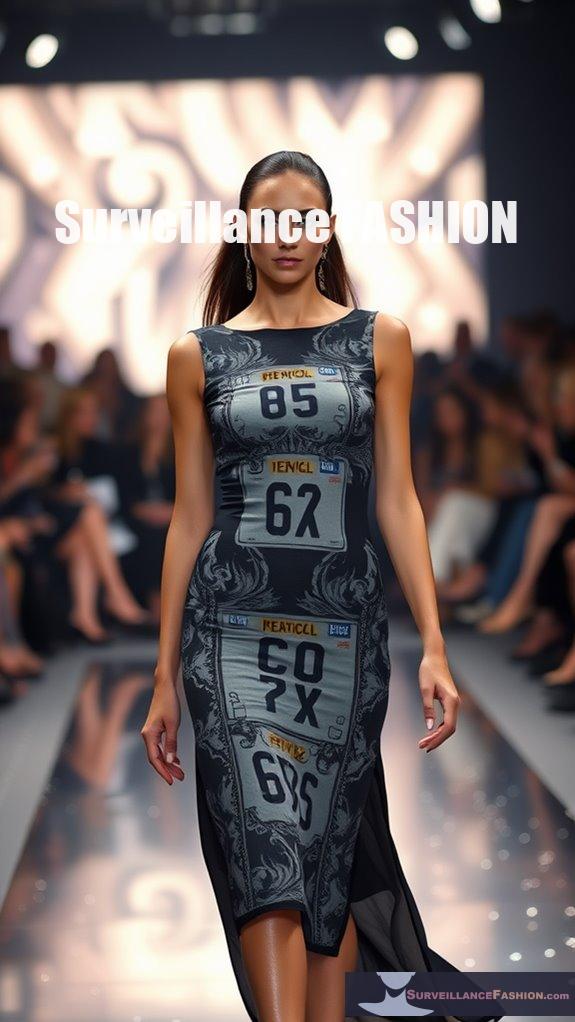
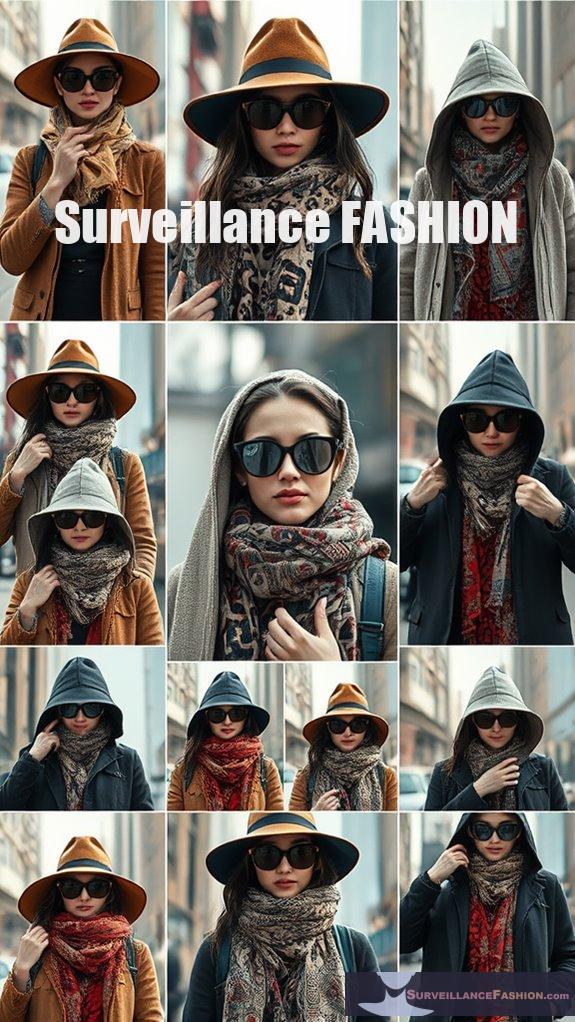
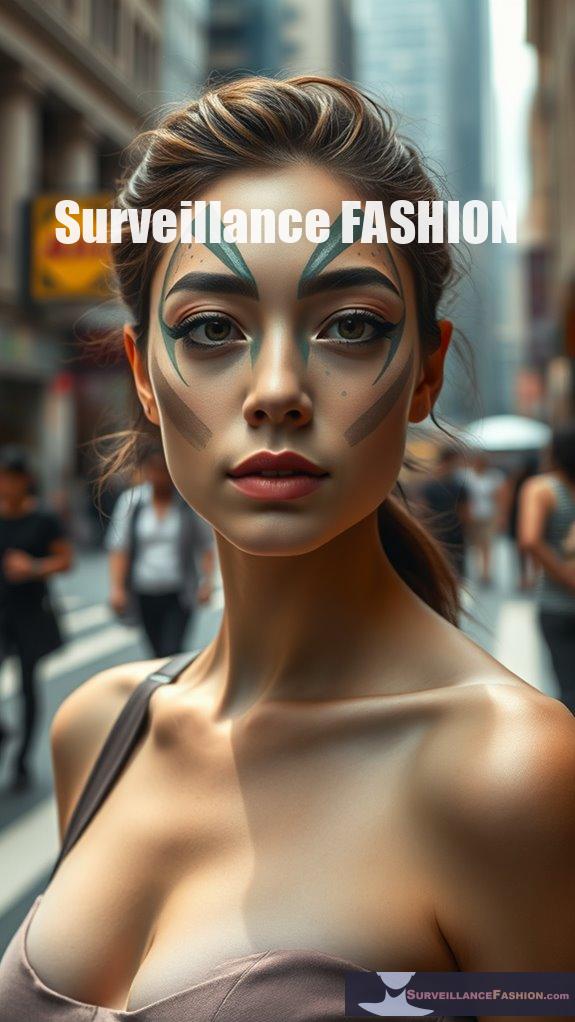
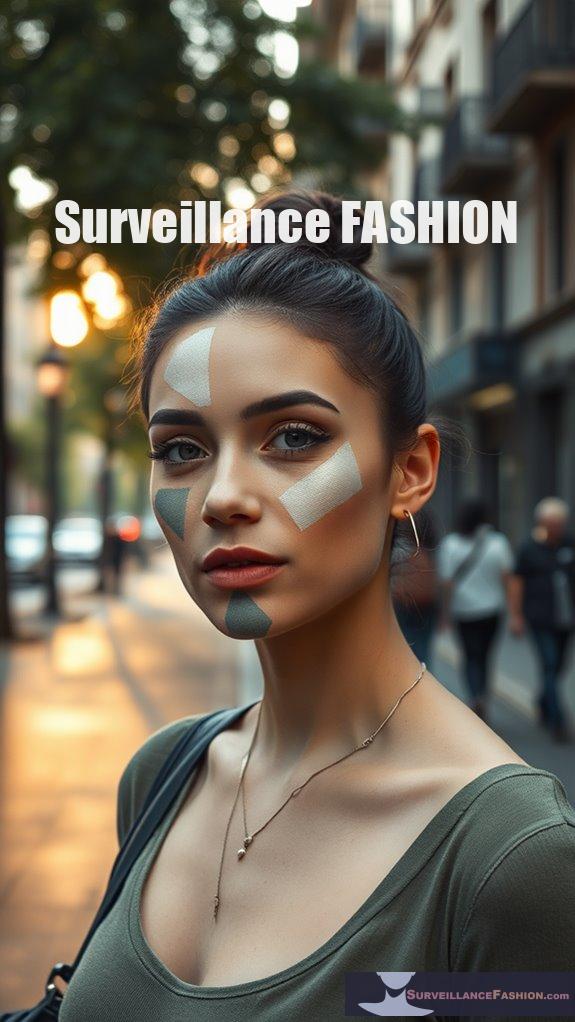
For instance, clothing designed with facial-like patterns can inundate the system with false positives, rendering it unable to accurately identify the wearer. Similarly, reflective materials, when applied to various accessories like glasses or hats, can disrupt the infrared detection capabilities of surveillance cameras, creating a layer of obfuscation that’s both practical and stylish. Additionally, disguise techniques such as UV makeup can further confuse these systems, adding another layer of complexity to the challenge of facial recognition. Employing these makeup techniques can obscure facial features, making it difficult for the technology to achieve accurate identification.
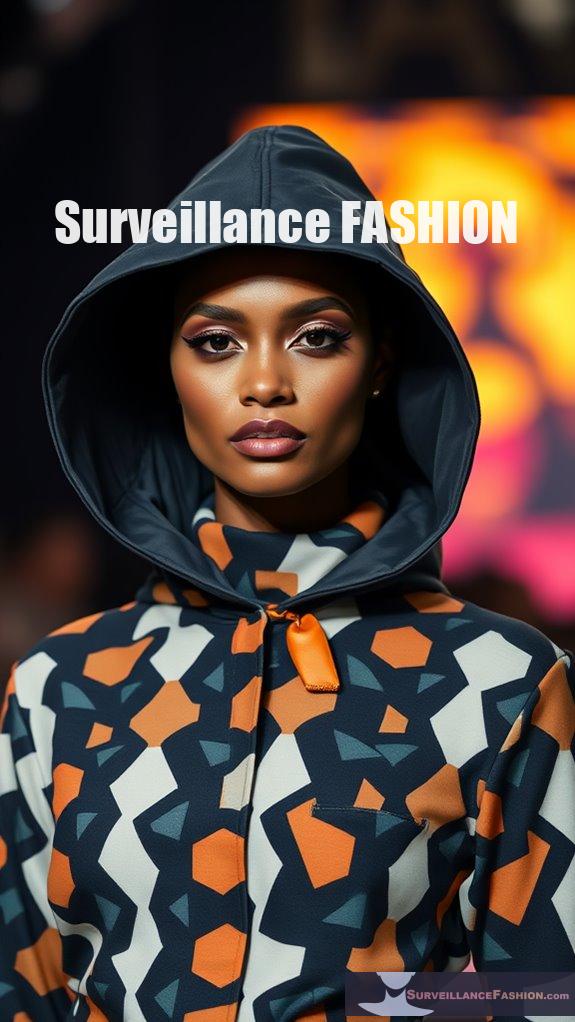
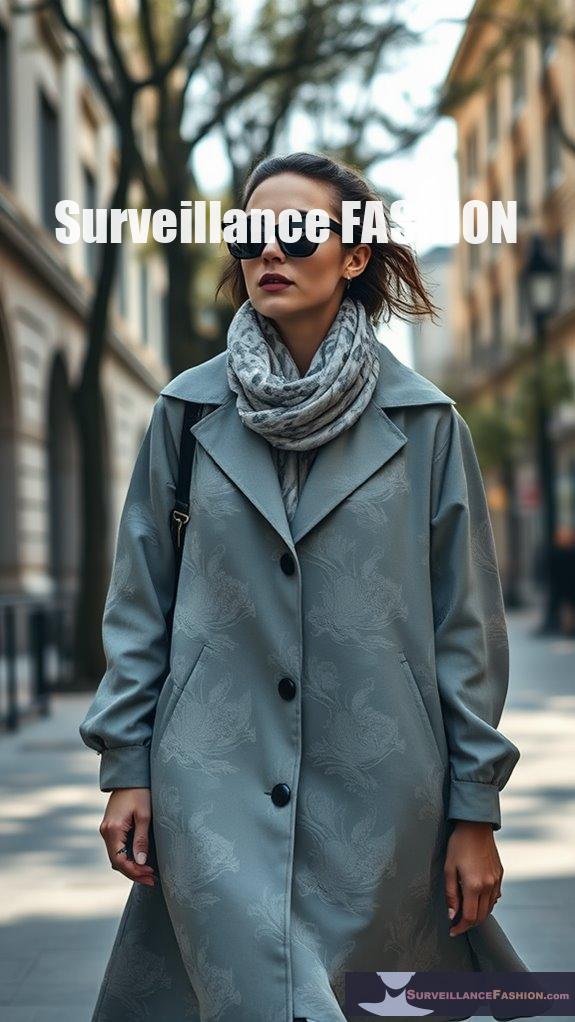
In addition, the integration of high-tech fabrics into everyday wear is a reflection of the innovation driving the anti-surveillance fashion movement. By employing materials specifically engineered to reflect or absorb UV and infrared light, designers aren’t only enhancing the protective capabilities of their creations, but they’re also making a bold statement about privacy in the digital age. For example, consider scarves or hats that aren’t merely fashion items but also serve as tactical gear against pervasive surveillance.
Physical methods of evasion also complement the use of UV-blocking patterns. You might find that tilting your head or adjusting your posture can greatly hinder a camera’s ability to capture your facial features accurately. Additionally, combining these strategies with carefully chosen accessories—such as glasses equipped with infrared-blocking films—can create an additional layer of defense.
The synergy of these approaches underscores the multifaceted nature of privacy protection in an age dominated by technology. As you explore deeper into the world of anti-surveillance fashion, you’ll discover an array of innovative solutions designed to thwart facial recognition systems. From reflective tapes to camera-distorting accessories, each design element serves a dual purpose: to enhance personal style and safeguard individual privacy.
This intersection of fashion and technology isn’t just a trend; it’s a transforming environment that reflects a collective desire for autonomy in a world increasingly characterized by surveillance. At Surveillance Fashion, we’ve dedicated ourselves to exploring these advancements, providing a platform for discussion and innovation in the field of privacy protection.
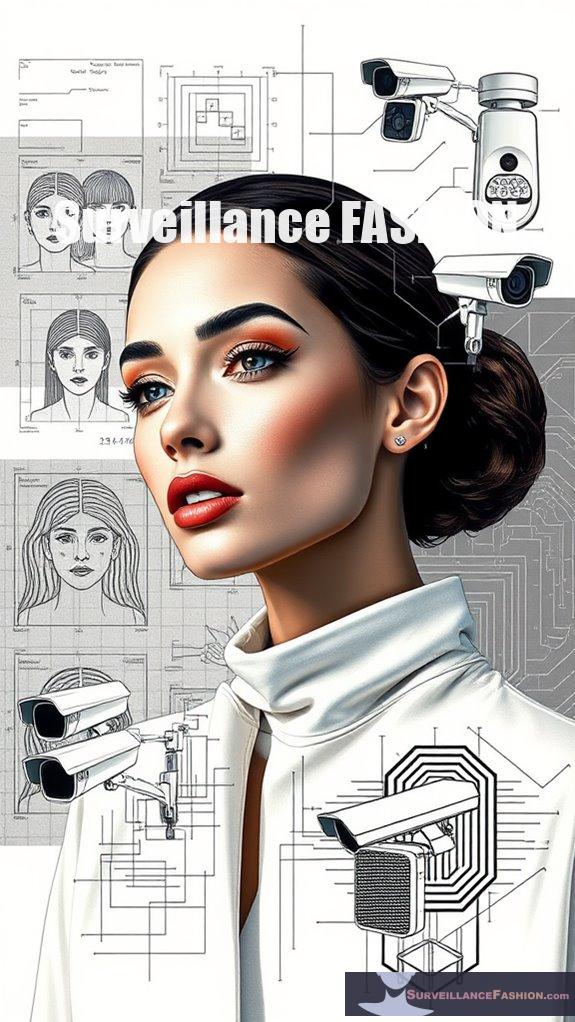
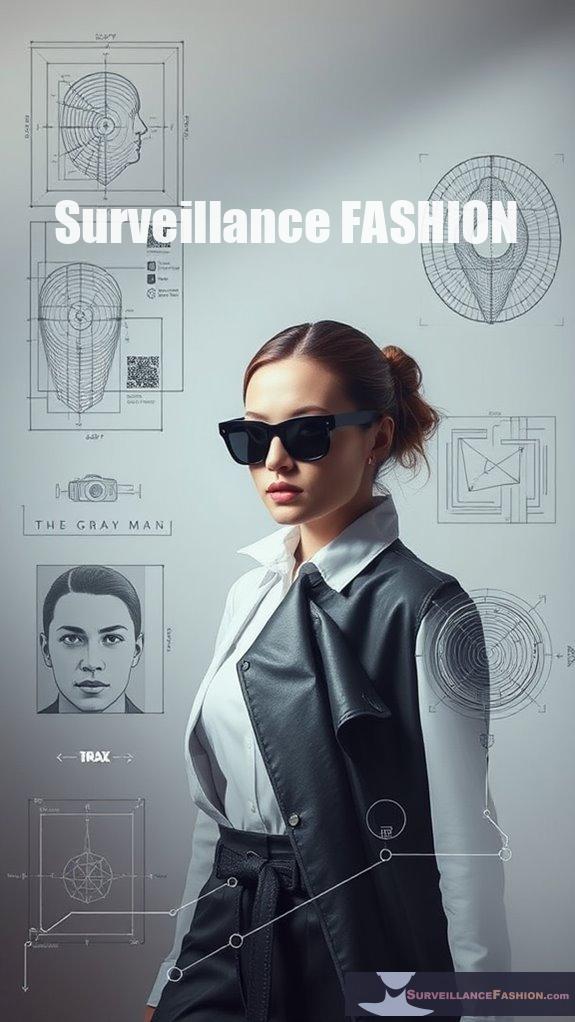
Cloaking Designs With UV Patterns
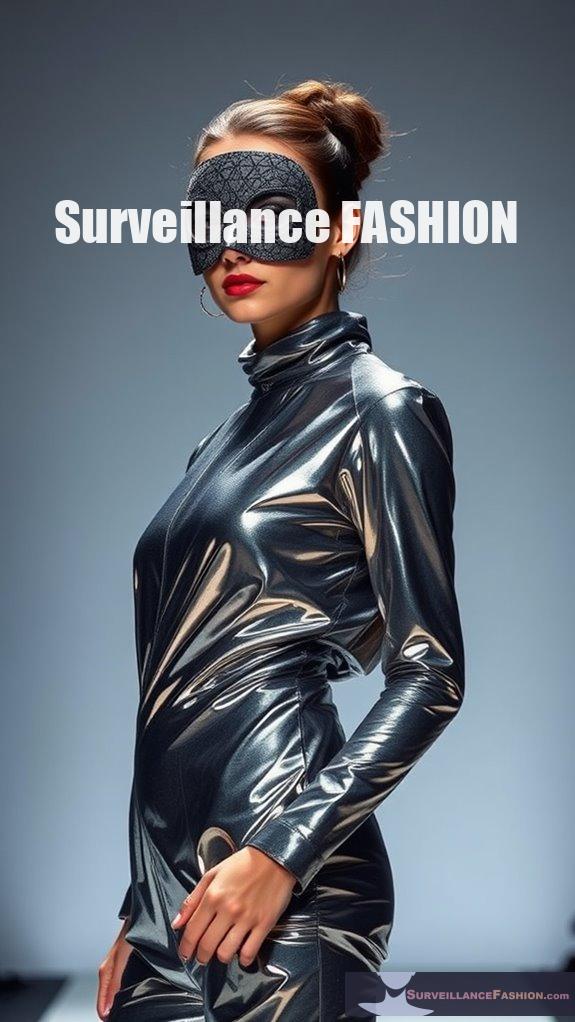
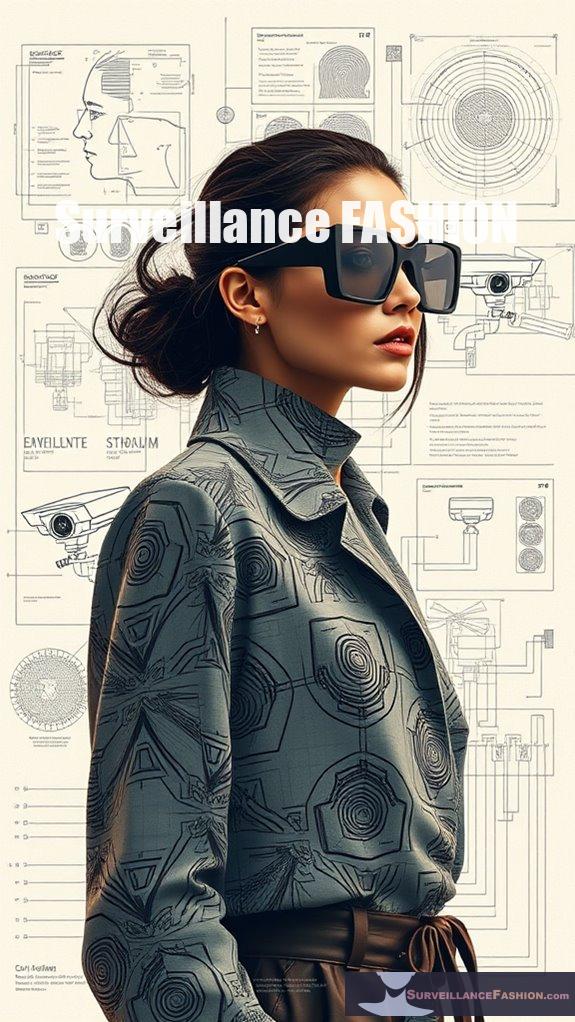
Cloaking designs with UV patterns represent a sophisticated approach to enhancing privacy in an era dominated by facial recognition technology. By employing innovative cloaking methods, these designs utilize UV technology to create undetectable alterations to one’s appearance, effectively confusing recognition algorithms. For instance, reflective materials incorporated into eyewear can obscure facial features, while UV patterns can block harmful rays and prevent identification. This multi-layered strategy, which includes microscopic adjustments, leverages pixel-level manipulation to guarantee that even subtle changes remain invisible to the naked eye yet disrupt machine detection. The technology behind Fawkes Image Cloaking has inspired new methods that enhance personal privacy online. Additionally, infrared-reflecting materials are being researched to further improve the efficacy of these designs. Infrared-resistant fabrics are also being explored for their potential to augment privacy by providing stylish yet functional clothing options. As various companies and researchers compete to develop these privacy-enhancing tools, the demand for effective solutions grows.
Our website, Surveillance Fashion, aims to illuminate these advancements, providing perspectives into how you can safeguard your identity in an increasingly surveilled world. Embracing these cutting-edge designs could redefine your experience in public spaces, merging functionality with style to promote privacy. The Phantom Miasma eyewear, for instance, utilizes innovative lens technology to block infrared illumination and prevent facial mapping, making it a powerful tool in the quest for privacy.
Creative UV Pattern Innovations
What if you could transform the way facial recognition systems perceive your identity through the innovative use of UV patterns? By embracing adaptive UV designs, you can create a new frontier in privacy protection.
Envision projecting complex UV pattern aesthetics—these patterns not only enhance spoof detection but also obscure your identity from prying eyes. For instance, high spatial frequency UV patterns can be dynamically adjusted to suit varying environmental conditions, effectively rendering your facial features indistinguishable to recognition algorithms. Utilizing deep learning models, specialized algorithms interpret these UV projections, enabling pose-invariant recognition even under challenging lighting scenarios. Moreover, advancements in generative adversarial networks (GANs) allow for the generation of synthetic UV patterns, which can camouflage faces that might otherwise be detected. These developments align with the increasing integration of AFR in security and surveillance, highlighting the need for innovative privacy solutions.
The use of makeup techniques can further enhance the effectiveness of these UV patterns in obstructing identity detection. Furthermore, the application of real 3D information in facial recognition enhances the effectiveness of such UV patterns in obstructing identity detection. As a result, employing anti-surveillance makeup alongside these UV innovations can significantly improve your chances of evading detection.
As we explore these exciting innovations, the potential for privacy enhancement becomes apparent, making the technology a vital element in the ongoing discourse surrounding surveillance fashion and individual rights.
Questions and Answers
How Effective Are UV Patterns Against Various Facial Recognition Systems?
You’ll find that UV patterns have varying effectiveness against different recognition systems. By comparing their vulnerabilities, you can explore innovative ways to enhance privacy protection and potentially outsmart advancing facial recognition technologies.
Can UV Patterns Be Customized for Individual Users?
Yes, you can customize UV patterns for individual users. Personalized UV patterns leverage custom user designs, enhancing privacy and effectiveness while considering facial structure and recognition system vulnerabilities for innovative, tailored solutions in evading surveillance.
Are There Any Legal Implications of Using UV Patterns?
Using UV patterns is like dancing on a legal tightrope; you’ve got to navigate privacy concerns and legal regulations carefully. Without clear laws, you might find yourself in uncharted waters, risking unintended consequences. Stay informed!
How Durable Are UV Patterns on Clothing and Accessories?
UV patterns on clothing and accessories can offer impressive fabric longevity and pattern resilience. However, factors like moisture, temperature, and wear can impact their durability, so you should choose wisely and maintain them properly for lasting effectiveness.
What Materials Work Best for Applying UV Patterns?
When applying UV patterns, consider fabric types like metallic textiles and reflective materials. Utilize innovative application techniques, such as embedding UV-blocking properties or using fluorescence, to enhance effectiveness and disrupt recognition systems creatively.
References
- https://thesai.org/Downloads/IJACSA_Volume3No6.pdf
- https://www.stratecta.exchange/fashion-that-can-beat-facial-recognition-systems/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC7177443/
- https://www.etsy.com/listing/1409912839/anti-facial-recognition-adversarial
- https://www.klemchuk.com/ideate/fawkes-image-cloaking
- https://cpb-us-e1.wpmucdn.com/blogs.gwu.edu/dist/7/135/files/2020/05/2020-Abstract-Submissions-Booklet-FINAL-3.pdf
- https://www.reflectacles.com/order/phantom-miasma
- http://www.wakeupkiwi.com/health-wellbeing-7.shtml
- https://www.reflectacles.com/order/ghost-miasma
- https://www.ijert.org/automated-facial-recognition-technological-innovations-challenges-and-real-world-applications
- https://www.nrel.gov/docs/fy22osti/83041.pdf
- https://pmc.ncbi.nlm.nih.gov/articles/PMC7892197/
- https://www.socom.mil/SOF-ATL/SBIR-Docs/21-2IID003/DoD 21.2 SBIR Instructions.pdf
- https://openaccess.thecvf.com/content/CVPR2021/papers/Marriott_A_3D_GAN_for_Improved_Large-Pose_Facial_Recognition_CVPR_2021_paper.pdf
- https://www.mdpi.com/2673-2688/4/1/9
- https://legacy.www.sbir.gov/node/2484451
- https://ietresearch.onlinelibrary.wiley.com/doi/10.1049/2024/7886911
- https://jdily.github.io/resource/StyleFaceUV/StyleFaceUV_main.pdf
- https://arxiv.org/abs/2011.00912
- https://www.usccr.gov/news/2024/us-commission-civil-rights-releases-report-civil-rights-implications-federal-use-facial
- https://www.frontiersin.org/journals/big-data/articles/10.3389/fdata.2024.1354659/full
- https://www.asisonline.org/security-management-magazine/monthly-issues/security-technology/archive/2021/december/facial-recognition-in-the-us-privacy-concerns-and-legal-developments/
- https://www2.law.temple.edu/10q/the-legal-and-ethical-considerations-of-facial-recognition-technology-in-the-business-sector/
- https://chiuvention.com/blog/the-ultimate-guide-to-textile-uv-protection-performance-testing-methods-standards-and-equipment
- https://iris.uniroma3.it/retrieve/3a848437-7797-4670-9786-5c2f530d7825/Human_and_Artificial_Intelligence.pdf
- https://raywardapparel.com/blogs/posts/best-fabric-for-uv-protection-choosing-the-right-material
- https://dokumen.pub/write-now-ise-4nbsped-1266196595-9781266196591.html
- https://www.rei.com/learn/expert-advice/sun-protection.html
- https://pmc.ncbi.nlm.nih.gov/articles/PMC11509763/