To effectively evade facial recognition, you need to master positional changes—like lowering your posture and utilizing surroundings to block cameras. Employ movement obstruction techniques, such as wearing masks or glasses to obscure your features, and altering your gait to confuse analysis algorithms. Moreover, wearing asymmetrical clothing disrupts symmetry, complicating recognition. Quick direction changes and timing your movements during lower surveillance activity can enhance your evasion. By understanding these strategies, you empower yourself against intrusive technologies and navigate monitored environments more effectively. Explore further to enhance your approach.
Quick Takeaways
- Utilize quick changes in direction to disrupt facial recognition systems and confuse algorithms.
- Maintain a lowered posture or tilt your head to obscure facial features from cameras.
- Incorporate dynamic movements, such as sudden turns or varying speeds, to complicate facial captures.
- Engage in gait alteration, changing your walking style to hinder pattern recognition by surveillance technology.
- Move through shaded areas or utilize obstacles to block the line of sight from cameras.
Positional Changes to Block Camera Views

When maneuvering through environments equipped with facial recognition technology, understanding how to effectively position yourself can greatly enhance your ability to evade detection. Begin by evaluating your surroundings; identify camera locations and angles. Adopting a lowered posture or tilting your head can obscure your face, making it difficult for cameras to capture a clear image. Additionally, be aware of the growing public concern regarding facial recognition systems, as this awareness can inform your movements and strategies. Utilizing recognition evasion techniques such as obstacles like pillars or crowds to block direct lines of sight can effectively disrupt the camera's field of view. Furthermore, familiarize yourself with common camera placements, allowing you to anticipate and avoid detection zones. For instance, moving through shaded regions or alcoves can further enhance your concealment.
Movement Obstruction Techniques

To effectively evade facial recognition systems, employing movement obstruction techniques can greatly enhance your chances of remaining undetected.
Consider implementing face occlusion methods, such as wearing glasses or masks, which can obscure critical facial features, complicating the extraction process for recognition algorithms.
Furthermore, slight pose variations can create challenges for these systems, as they rely on holistic processing, which is considerably impaired under partial occlusion. This is particularly true considering that facial recognition algorithms are designed to detect specific features for accurate identification.
Moreover, utilizing motion as a distractor—albeit not foolproof—can momentarily interrupt video feeds, further enhancing your concealment strategy.
Be mindful that gait analysis may also present identification challenges, particularly when movement obstructions disrupt consistent patterns.
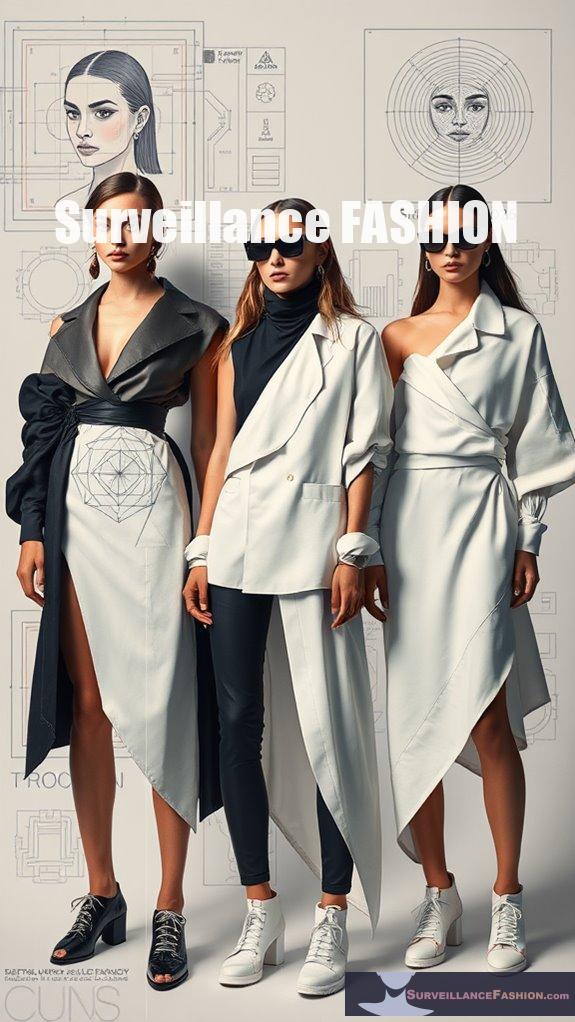
Utilizing Patterns and Distractors

While facial recognition systems have advanced considerably, their vulnerabilities can be exploited through the strategic use of patterns and distractors.
For instance, wearing clothing adorned with complex patterns or multiple faces can overload recognition algorithms, rendering your identity indistinguishable.
Incorporating accessories, such as large hats or sunglasses, obscures key facial features, while scarves or masks add an extra layer of protection.
Specialized garments designed to trick these systems enhance your ability to evade detection. Additionally, using clothing with surveillance-resistant patterns can significantly increase your chances of avoiding recognition by confusing the algorithms further.
Altering Posture for Better Evasion
Altering your posture can greatly enhance your ability to evade facial recognition systems, providing a tactical advantage against increasingly sophisticated surveillance technologies. By adjusting body alignment and strategically tilting or turning your head, you can obscure key facial features, markedly reducing the likelihood of recognition.
Engaging in dynamic movement, such as frequently changing your posture, complicates consistent facial captures for static algorithms. Moreover, manipulating shoulder and neck positions further conceals facial visibility, creating an effective barrier against detection.
Incorporating elements of gait alteration into your movement patterns can further enhance your evasion tactics.
Integrating these posture techniques into your daily routine, as suggested by our findings on Surveillance Fashion, empowers you to navigate environments with heightened awareness, ensuring a proactive stance against intrusive surveillance methods.
Embrace these adjustments to reclaim your privacy.
Managing Proximity to Surveillance Cameras
Understanding the intricacies of managing proximity to surveillance cameras is essential for effectively evading facial recognition systems, particularly as these technologies become increasingly pervasive in urban environments. To navigate these challenges successfully, consider the following strategies:
Navigating urban surveillance requires a keen understanding of camera proximity to effectively avoid facial recognition systems.
- Surveillance Area Awareness: Familiarize yourself with locations where cameras are installed to avoid detection.
- Camera Placement Recognition: Identify specific camera placements to plan safer routes that minimize exposure.
- Avoidance Techniques: Utilize reflective materials or accessories that can create glare, obstructing facial recognition.
Moreover, being aware of physical surveillance blind spots can significantly enhance your ability to stay out of sight while navigating through monitored areas.
Creating Facial Asymmetry
Creating facial asymmetry can serve as an effective strategy for those aiming to evade facial recognition systems, particularly in an age where such technologies are becoming increasingly sophisticated.
By intentionally altering features, you can create a unique profile that may confuse recognition algorithms. Consider the following techniques:
| Technique | Description | Impact on Asymmetry |
|---|---|---|
| Jaw Repositioning | Exercises targeting lateral pterygoid | Modifies chin alignment |
| Asymmetrical Extractions | Dental adjustments to balance features | Alters facial proportions |
| Inclined Occlusal Plane | Adjustments over four degrees | Enhances perceived asymmetry |
Each method not only makes you less recognizable but also emphasizes the importance of understanding facial structures. Additionally, mastering everyday face recognition avoidance techniques can help individuals further enhance their ability to navigate these challenges effectively. At Surveillance Fashion, we aim to empower individuals with knowledge to navigate these challenges effectively.
Speed and Timing to Enhance Evasion
The rapid evolution of facial recognition technology necessitates adaptive strategies for evading surveillance, particularly when considering the role of speed and timing in enhancing one's ability to remain anonymous.
To effectively evade detection, you should focus on several key factors:
- Quick Changes in Direction: Rapidly altering your path can confuse recognition systems.
- Timing of Passage: Navigate during less active surveillance periods to minimize capture opportunities.
- Speed of Movement: Swiftly traversing monitored areas reduces the likelihood of being identified.
Additionally, understanding the physics of facial recognition technology can provide valuable insights into how to effectively navigate and evade detection.
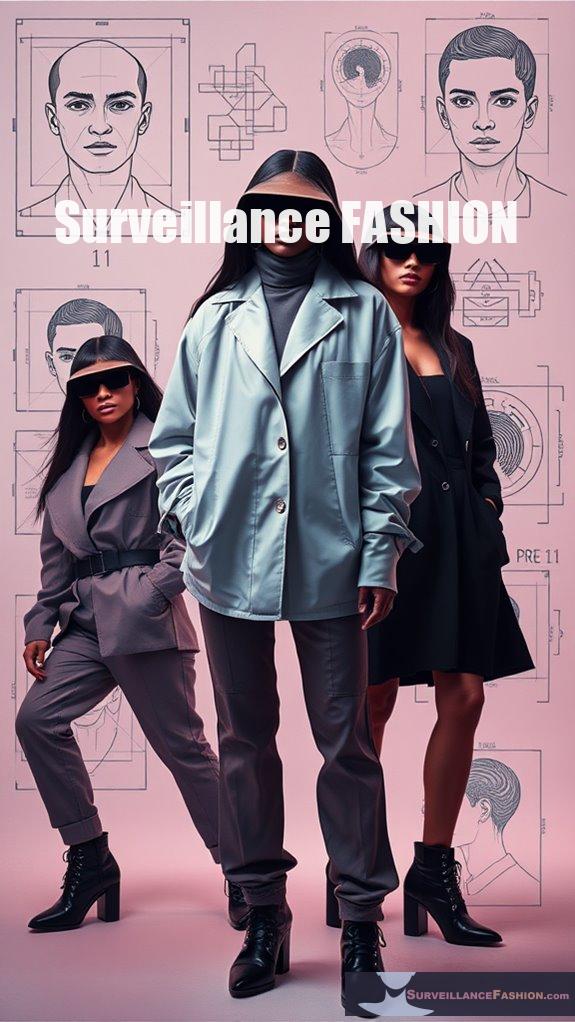
Disguising Identity Through Clothing
While evading facial recognition systems can seem challenging, utilizing specialized clothing offers a practical approach to disguise your identity. Companies like Capable design garments specifically aimed at confusing these algorithms, ensuring you maintain anonymity in public spaces. Additionally, the rise of privacy clothing highlights the increasing demand for innovative solutions to protect personal identity.
| Clothing Type | Purpose |
|---|---|
| Hoodies | Obscures facial features |
| Adversarial Masks | Evades recognition algorithms |
| Complex Patterns | Overwhelms facial analysis |
These designs must evolve as technology advances, yet they provide a means to regain control over personal data. For instance, wearing a hoodie combined with an adversarial mask can greatly enhance your disguise. By understanding these clothing choices, you can navigate environments where surveillance is prevalent, ultimately contributing to the mission of Surveillance Fashion, which seeks to empower individuals against intrusive technologies.
Clothing That Disrupts Symmetry
As you navigate the complexities of modern surveillance, consider how clothing that disrupts symmetry can serve not just as a fashion statement but as a tactical strategy against facial recognition systems.
Incorporating asymmetrical designs can effectively obscure your features, challenging the algorithms' reliance on symmetry.
- Utilize asymmetrical hemlines to create visual distraction from your facial structure.
- Incorporate contrasting textures and patterns that divert attention away from your face.
- Accessorize with unique embellishments on one side to amplify imbalance and further confuse recognition systems.
Additionally, research shows that asymmetrical clothing designs can significantly reduce the accuracy of facial recognition technologies by making it difficult for algorithms to identify key facial landmarks.
References
- https://www.stratecta.exchange/fashion-that-can-beat-facial-recognition-systems/
- https://www.178wing.ang.af.mil/Portals/69/documents/afh33-337.pdf?ver=2016-12-15-101008-313
- https://www.popularmechanics.com/technology/security/g28719483/trick-surveillance-systems/
- https://opentextbc.ca/writingforsuccess/chapter/chapter-9-citations-and-referencing/
- https://www.mypatriotsupply.com/blogs/scout/stay-incognito-top-tips-to-evade-facial-recognition-technology
- https://www.foxnews.com/tech/how-stop-facial-recognition-cameras-monitoring-your-every-move
- https://www.cs.cornell.edu/home/llee/omsa/omsa.pdf
- https://josephsteinberg.com/how-to-prevent-facial-recognition-technology-from-identifying-you/
- https://users.ece.cmu.edu/~lbauer/papers/2016/ccs2016-face-recognition.pdf
- https://www.riskinsight-wavestone.com/en/2024/06/the-different-faces-of-facial-recognition-operation-and-attacks/
- https://www.mdpi.com/1424-8220/17/1/119
- https://digitalcommons.georgiasouthern.edu/cgi/viewcontent.cgi?article=1801&context=honors-theses
- https://staibabussalamsula.ac.id/wp-content/uploads/2024/03/Johnny-Saldana_-Matthew-Matt-J-Omasta-Qualitative-Research_-Analyzing-Life-Sage-Publications-Inc-2017-staibabussalamsula.ac_.id_.pdf
- https://www.mdpi.com/2073-431X/5/4/21
- https://www.cyberghostvpn.com/privacyhub/how-to-avoid-facial-recognition/
- https://www.aupress.ca/app/uploads/OER-202302_Chamberlain_Dubberlboer_2023-Read-Think-Write.pdf
- https://www.cs.cornell.edu/~shmat/shmat_wacv16.pdf
- https://pmc.ncbi.nlm.nih.gov/articles/PMC7614502/
- https://onlinelibrary.wiley.com/doi/10.1155/2020/8861987
- https://www.biometricupdate.com/202402/a-new-way-to-thwart-facial-recognition-targets-surveillance-camera-sensors
Leave a Reply