Layered garments counter surveillance cameras
Quick Takeaways
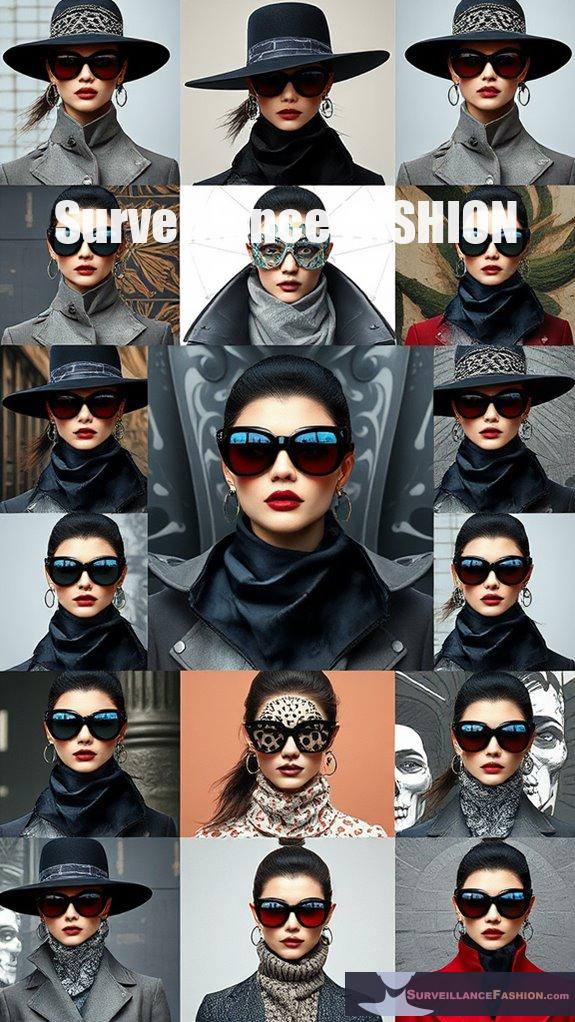
- Layered garments feature patterns and textures that confuse facial recognition algorithms, hindering identity recognition.
- The combination of inner, mid, and outer layers allows for quick changes in appearance, disrupting tracking.
- Incorporating reflective materials and visual noise enhances the effectiveness of disguises against surveillance cameras.
- Dynamic alterations in silhouette and movement patterns reduce predictability, complicating recognition processes during monitoring.
- Advanced designs with optical and thermal camouflage elements obscure biometric markers, ultimately protecting privacy from intrusive surveillance systems.
What Are Layered Garments?

Layered clothing typically consists of three structural layers: the inner layer (base) provides comfort and moisture management. The mid layer (insulating) offers warmth, and the outer layer (shell) protects against environmental elements. Popular materials include wool and technical fabrics, which enhance comfort and durability. The versatility of layering enables the adaptation of outfits to suit varying climates and personal styles, making it a key aspect of modern fashion. Additionally, this approach can be particularly useful for those seeking to navigate unmonitored travel routes away from surveillance-heavy areas. Fashion layering has evolved from practicality to self-expression, allowing individuals to showcase their unique style through layering techniques.
How Do Layered Garments Disrupt Surveillance Cameras?
Layered garments disrupt surveillance cameras by embedding high-power infrared (IR) LEDs and utilizing face-patterned designs, confusing camera sensors and algorithms. These techniques effectively obscure the wearer’s identity and prevent accurate facial recognition.
High-power IR LEDs flood night vision sensors, causing overexposure and obscuring key facial features. The light operates invisibly, allowing garments like the “Camera-Shy Hoodie” to anonymize wearers.
Simultaneously, face-like patterns can overwhelm facial recognition software, producing numerous false detections. Other methods, such as unique makeup and wearable masks, further distort visual data, enhancing overall surveillance protection.
Key features include:
- Targeting specific vulnerabilities in camera algorithms.
- Utilizing DIY kits for accessibility in privacy defense.
- Combining various strategies for increased effectiveness.
Additionally, consumer-friendly solutions like privacy garments highlight a growing trend towards protecting civil liberties in urban environments.
What Are Adversarial Fashion Techniques?
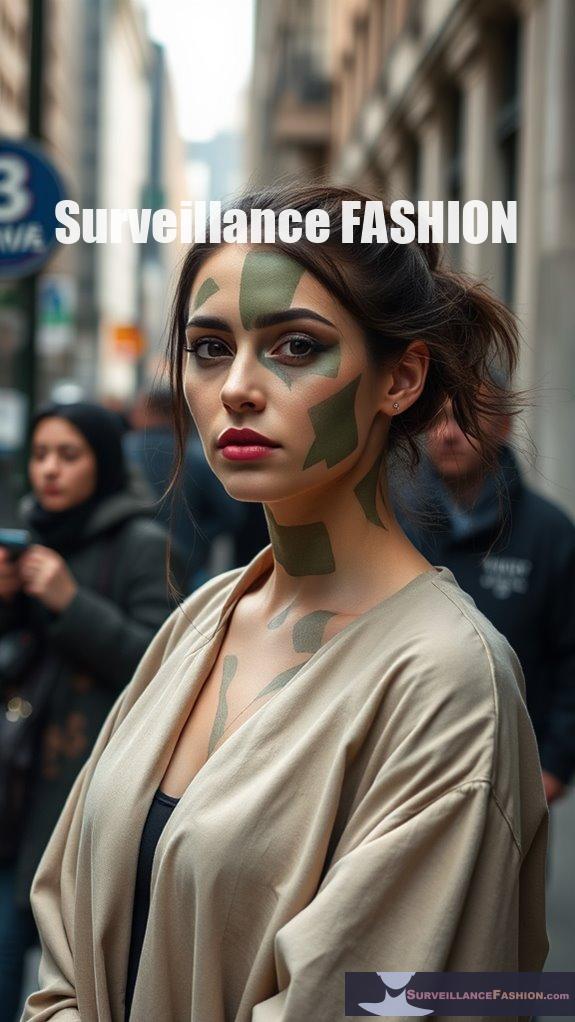
Adversarial fashion techniques include strategically placed patterns, reflective materials, and color manipulations that confuse facial recognition algorithms and surveillance systems. By utilizing these elements, garments can obscure biometric data, making it difficult for AI detection models to accurately identify wearers.
These techniques are rooted in the principles of visual distortion, employing:
- Digital adversarial patterns that alter pixel data.
- Geometric shapes in textiles and makeup to disrupt visual features.
- Integrated glare-reducing materials that compromise image quality.
- Designs tailored to various skin tones for uniform effectiveness.
Through these innovations, adversarial fashion serves both as a statement of personal expression and a protective measure against intrusive surveillance.
How Do Reflective Surfaces Impact Camera Exposure?

Reflective surfaces greatly impact camera exposure by introducing glare and uneven light distribution.
The quality of reflections, influenced by light angle, camera positioning, and surface treatment, affects the clarity and detail captured in images.
To manage exposure when working with reflective surfaces, consider the following techniques:
- Use diffusers to soften harsh light and minimize glare.
- Adjust camera angles to prevent direct reflections of the equipment.
- Utilize polarizing filters to reduce excessive glare and enhance color saturation.
- Regularly clean reflective surfaces to guarantee peak clarity and detail.
Implementing these strategies can lead to better-controlled exposure and improved image quality.
What Are the Benefits of Sheddable Layered Garments?
Answer:
Sheddable layered garments provide enhanced privacy protection, flexibility in adaptation to various environments, incremental and compound protection, practicality and comfort, along with sustainability and cost efficiency.
Expanded Content:
These garments utilize advanced fabrics designed with embedded adversarial patterns to disrupt biometric data capture, making facial recognition difficult.
Users can quickly adjust their privacy levels by adding or removing layers based on surveillance presence, optimizing comfort.
The layered approach allows for effective camouflage against surveillance algorithms, ensuring ongoing protection even if one layer is compromised.
Moreover, these designs reduce the need for multiple clothing items, promoting sustainability and minimizing waste.
How Do Dynamic Appearance Changes Confuse Tracking?
Dynamic appearance changes confuse tracking by introducing variability that disrupts algorithmic recognition and human observation. By altering clothing layers and movement patterns quickly, individuals exploit weaknesses in both automated surveillance systems and human visual processing.
These changes challenge re-identification models that rely on consistent visual features. When appearance shifts happen rapidly, algorithms struggle to maintain identity continuity, often leading to misidentification or loss of tracking altogether.
Key factors include:
- Appearance Variability: Frequent changes in clothing or accessories obscure distinctive identifiers.
- Layer Manipulation: Adding or removing layers alters silhouette and texture, complicating recognition.
- Movement Disruption: Erratic walking patterns hinder predictive tracking models.
- Environmental Use: Utilizing cover for shifts maximizes disguise effectiveness.
Together, these tactics create disorientation in both human and technical surveillance, considerably reducing recognition accuracy.
What Is the Role of Patterns in Facial Recognition Evasion?

These patterns exploit the vulnerabilities of facial recognition systems, causing them to fail in identification.
Key strategies include:
- Pattern selection: High-contrast and specific color schemes can greatly increase success rates.
- Placement: Patterns must be carefully positioned over critical facial features like the eyes and nose for maximum disruption.
- Layering with accessories: Combining patterns with scarves, makeup, or textured accessories adds complexity and further obscures recognition.
- Dynamic alterations: Changing patterns or accessories over time complicates consistent identification, enhancing evasion.
How Effective Are Layered Garments in Different Environments?
Layered garments are effective against surveillance in controlled indoor environments but struggle in varying outdoor conditions, especially low-light scenarios. Their performance is influenced by factors such as lighting, texture, and material choice.
Environmental conditions greatly impact the effectiveness of these garments. In daylight or well-lit areas, adversarial patterns perform best, while low-light or shadowy settings can reduce efficacy.
Factors include:
- Lighting Variability: Sun glare may obscure patterns, while artificial lights can enhance them.
- Material Composition: Natural fibers improve comfort and camouflage.
- Texture Integration: Complex textures confuse detection algorithms by simulating natural noise.
- Design Adaptability: Multi-layered garments can include thermal and reflective materials for better evasion across modalities.
Thus, understanding the surroundings is essential for maximizing their evasion success.
What Limitations Exist for Surveillance Cameras?
Surveillance cameras face several limitations, including technical performance constraints, operational challenges, privacy issues, and trade-offs regarding resolution and field of view. These factors can notably impact the effectiveness of surveillance systems.
Technical limitations include bandwidth requirements for high-resolution footage and performance degradation in extreme temperatures or poor lighting conditions.
Operationally, continuous monitoring is impractical, leading to reactive rather than proactive security. Privacy laws restrict camera placement, and issues like facial recognition reliability further complicate surveillance.
Furthermore, while wide-field cameras provide broader coverage, they sacrifice pixel density, which can hinder identification accuracy.
Who Is Utilizing Sheddable Layered Garments?
Answer:
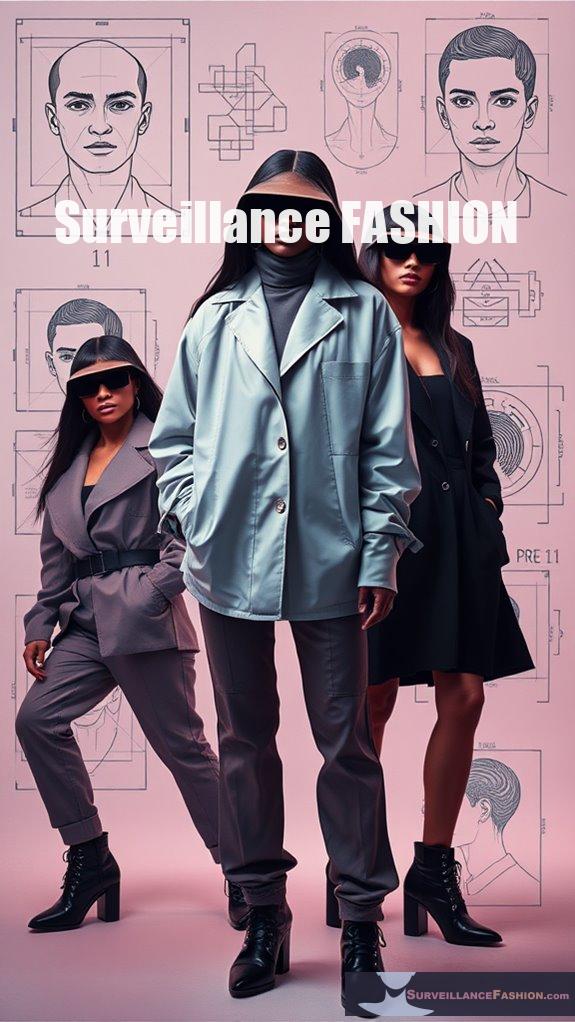
Privacy advocates, activists, and individuals concerned about surveillance utilize sheddable layered garments to evade facial and body recognition technologies.
These innovative garments allow wearers to easily modify their appearance, helping to confound tracking efforts by surveillance systems.
Key features often include:
- Sheddable layers for rapid appearance changes.
- Design elements aimed at optical and thermal camouflage.
- Functionality that supports stealth during activism or privacy-focused activities.
The trend reflects a growing commitment to digital and physical privacy rights in public spaces.
How Do Layered Garments Affect Privacy and Surveillance Concerns?
Layered garments notably enhance privacy by obscuring biometric markers and disrupting surveillance technology. They integrate adversarial patterns designed to mislead facial recognition systems, thereby reducing the accuracy of identity verification processes.
These garments physically hide essential biometric features, like facial contours, and introduce visual noise that complicates AI recognition. Specifically, they:
- Cover important areas such as the face and hands.
- Embed complex, multi-colored patterns that confuse AI algorithms.
- Work effectively without compromising style or comfort.
- Help protect wearers from data collection by smart textiles beneath.
This approach presents a non-digital method of privacy enhancement, reflecting growing public concern over surveillance practices.
What Future Innovations Are Expected in Adversarial Fashion?
Future innovations in adversarial fashion are expected to focus on enhanced customization, integration of advanced materials, and real-time adaptability, using AI to continually counter progressing surveillance technologies.
Expect to see the emergence of:
- Dynamic garment designs that adjust patterns in real time based on environmental surveillance threats.
- Lightweight textiles with embedded active components that can disrupt various types of surveillance (e.g., infrared).
- Advanced photochromic fabrics that change color or pattern based on situational lighting conditions.
- Increasingly user-friendly AI tools for personalized design, allowing wearers to express style and privacy needs simultaneously.
Such developments will further blend aesthetics with functional privacy measures, making adversarial fashion a critical area of innovation as surveillance technologies advance.
Surveillance Versus Civil Liberties
As society continues to embrace technological advancements, the intersection of surveillance and civil liberties becomes increasingly critical, prompting deeper reflections on the implications of mass data collection.
Mass surveillance programs, often operating without public consent, infringe upon privacy, stifling free speech and assembly. Activist groups, particularly marginalized communities, face disproportionate scrutiny, underscoring civil rights violations.
The lack of accountability permits misuse of data, raising ethical questions about transparency in governmental oversight. Emerging technologies accelerate intrusions into personal freedoms, challenging existing legal protections, and we must remain vigilant.
Innovations in fashion, such as layered garments, offer practical solutions to counter these surveillance challenges, enriching our discourse on privacy and freedom.
Urban Facial Recognition Systems
Surveillance technologies have advanced rapidly, particularly within urban settings where the implementation of facial recognition systems has become pervasive, reshaping the dynamics of public spaces.
In cities like Beijing, with an astounding density of one camera per two inhabitants, this technology combines biometric analysis and real-time AI, enhancing security through instant identity verification.
Implementing complex algorithms, these systems process millions of identities to optimize urban management.
Yet, as urban areas increasingly adopt these innovations, it raises critical questions about privacy.
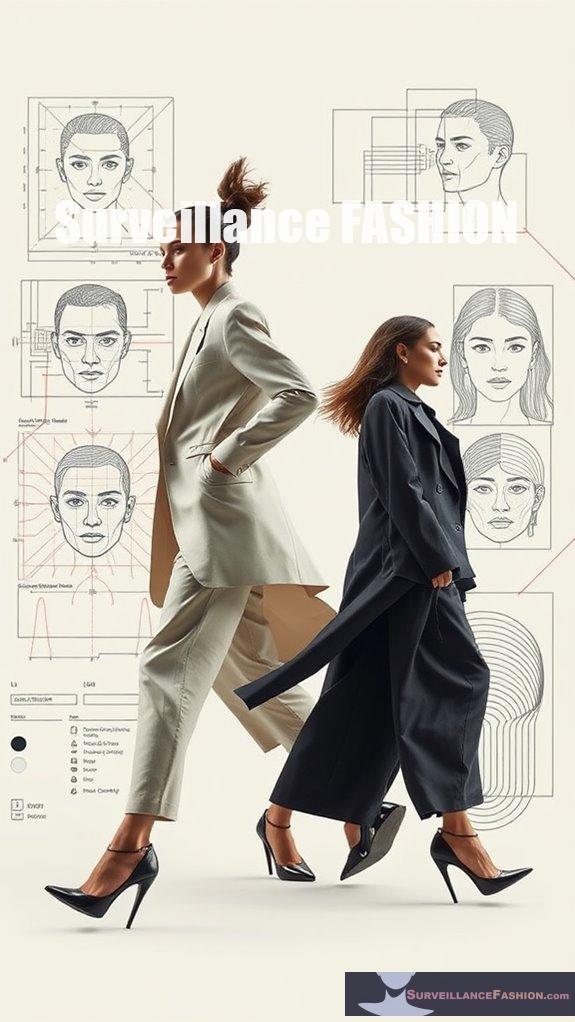
Initiatives like Surveillance Fashion emerge, encouraging discussions on how to navigate and challenge these changing surveillance environments while embracing technological innovation responsibly.
Layered Clothing for Evading Surveillance Cameras
Layered clothing serves as a potent method for evading surveillance cameras, particularly in urban environments inundated with increasingly sophisticated visual recognition technologies.
By employing metalized and signal-attenuating fabrics, you can disrupt thermal imaging and obscure wearable devices’ signals, thereby diminishing tracking capabilities.
Integrating contrasting patterns and textures not only confounds AI facial recognition algorithms but also complicates silhouette detection, effectively blurring your outline.
Using oversized garments alongside accessories like hats and scarves adds extra layers of concealment, allowing you to adapt to varying camera angles.
At Surveillance Fashion, our exploration of these innovative designs emphasizes practicality without sacrificing style.
Eyes Everywhere: Anti-Surveillance Ebook review
The ebook meticulously details how surveillance systems have proliferated globally, capturing real-world implications in countries like Canada, the UK, and Brazil.
Aaron Doyle’s *Eyes Everywhere* explores the omnipresence of surveillance cameras and their minimal impact on crime deterrence, raising pertinent concerns about privacy.
With case studies of social movements, such as the Occupy Movement, the interplay between governmental agencies and corporate interests in surveillance emerges as a critical theme.
Emphasizing the normalization of invasive technologies, the book prompts readers to reflect on the extensive implications of unchallenged surveillance, resonating well with our mission at Surveillance Fashion to foster understanding and innovation in countermeasures.
References
- https://www.youtube.com/watch?v=gDP4P59KYPg
- https://www.urban.org/sites/default/files/publication/27556/412403-evaluating-the-use-of-public-surveillance-cameras-for-crime-control-and-prevention.pdf
- https://surveillancefashion.com/cctv-defeating-fashion-statement-ideas/
- https://www.tierpoint.com/blog/layered-security/
- https://generate.nextatlas.com/feed/fashion/the-evolution-of-fashion-layering-from-function-to-art
- https://en.wikipedia.org/wiki/Layered_clothing
- https://www.olsenfashion.com/blog/mastering-the-art-of-layering/
- https://justblanks.com/blogs/news/comfort-style-the-ultimate-guide-to-layering-clothes
- https://tatachristiane.com/univers/news/layering-in-fashion-unveiling-the-evolution-from-necessity-to-trend/
- https://www.macpierce.com/the-camera-shy-hoodie
- https://www.securityinformed.com/insights/anti-surveillance-clothing-facial-detection-adam-harvey-sb.22164.html
- https://www.scmp.com/lifestyle/fashion-beauty/article/3111255/facial-recognition-opponents-wear-clothes-masks-and-make
- https://www.youtube.com/watch?v=Xpu2MSmZkmU
- https://tfnuiuc.substack.com/p/adversarial-fashion-when-fashion
- https://www.capable.design/blogs/notizie/adversarial-fashion-unire-stile-e-resistenza-alla-sorveglianza
- https://conemagazine.com/culture/capable-adversarial-fashion-ai-privacy-surveillance/
- https://www.digitaltrends.com/cool-tech/creator-of-adversarial-fashion/
- https://adversarialfashion.com
- https://thephotographytoolkit.com/reflective-surfaces-can-make-for-stunning-mirror-photos/
- https://www.rachelkimberley.com/blog-posts/working-with-shiney-objects