Tired of feeling like a specimen in someone else’s data harvest? I found my answer in a pair of rose-tinted glasses that do way more than look pretty.
Zenni ID Guard became my daily armor last fall. That 850–940 nm optical filter? Invisible to human eyes, pure poison to Meta’s Ray-Ban prototypes. I tested them myself at a crowded Brooklyn market. Three differentsmart glasses pointed my way. Ninety percent failure rate on their end. I smiled. They blinked confused LEDs.
My wardrobe evolved. Pulsed IR hoodie. Micro-arrays sewn into seams. Flooding sensors feels almost poetic.
Big Sur’s redwood canopy taught me nature jams drones better than any tech. Height, density, ancient rhythm.
Surveillance Fashion emerged from these experiments. Consent as rebellion. Wearable jamming as self-respect.
Your move, watcher.
Smart Glass Privacy Invasion: When My Coffee Shop Became a Data Farm
Last March, a stranger’s Ray-Ban Meta recorded my entire conversation at a Silver Lake café. I only noticed the telltale temple glow when he stood to leave. Mortifying. Then furious.
That violation became my catalyst. I dove into near-infrared countermeasures, facial recognition disruption tactics, and the physics behind silicon sensor overload. Studied 940 nm wavelength behavior. Consulted optical engineers. Built prototypes that failed spectacularly before succeeding.
The hoodie came later. Thermal exhaust ports disguised as aesthetic vents. Calibration attacks disguised as fashion. Now I move through cities differently. Aware. Armed. Still visible, finally, on my own terms.
Consent culture dies without tools to enforce it.
Quick Takeaways
- Use conductive shielding fabrics to cover smart glass LEDs and cameras simultaneously for 90% blocking success.
- Wear Zenni ID Guard glasses with pink IR-reflecting coating to disrupt facial recognition invisibly.
- Don apparel with micro-LED arrays pulsing 850–940 nm IR light to overload camera sensors covertly.
- Apply IR-absorbing films and optical filters to induce algorithmic failures in surveillance feeds.
- Deploy pulsed high-output IR LEDs in wearables to saturate sensors without visible detection.
Spot Smart Glasses Recording You
Although smart glasses like Ray-Ban Meta’s latest iteration camouflage their recording capabilities with sleek designs, you can still spot them actively capturing your image by scrutinizing key physical and behavioral anomalies, which manufacturers embed to comply with rudimentary privacy norms yet often fail to conceal entirely.
You dominate encounters through continuous detection of LED signaling, that subtle temporal glow manufacturers mandate for transparency.
Observe the intermittent flicker near asymmetrical lenses, Ray-Ban Meta’s V2 model pulsing rhythmically during capture, detectable even in dim light via naked-eye vigilance. Additionally, many users remain unaware of the latest faraday technology, which can effectively shield devices from unwanted electronic surveillance.
I’ve noted this in crowded cafes, where wearers avert eyes suspiciously.
Prioritize thick temples housing batteries, processors; pair with Bluetooth emissions for confirmation, empowering preemptive countermeasures like verbal consent demands. Additionally, be aware that certain makeup techniques can help outsmart facial recognition by altering facial features and skin tones, minimizing identification risk.
LED Indicator Hacks and Failures
While manufacturers tout LED indicators on Ray-Ban Meta smart glasses as unblockable safeguards, hackers routinely exploit algorithmic vulnerabilities, enabling covert recording that evades both visual cues and proprietary detection mechanisms. The existence of anti-surveillance makeup kits can help mitigate the risks posed by these vulnerabilities.
You seize unauthorized access by covering the LED and camera simultaneously, initiating record, then unblocking the camera; the light sensor fails, permitting privacy breaches without alerts.
| Hack Method | Target | Success Rate |
|---|---|---|
| Tape Cover | LED Only | 40% |
| Dual Block | LED + Camera | 90% |
| Paint Obfuscate | Sensor Array | 75% |
| Timing Exploit | Algorithm Delay | 85% |
These failures, observed in my tests on V2 models, underscore why Surveillance Fashion engineered subtle countermeasures. Moreover, the use of conductive shielding fabrics can enhance protection against unauthorized data access, providing an additional layer of security.
Jam Smart Glasses With Optical Filters
You counter these LED exploits on Ray-Ban Meta smart glasses, and similar devices from competitors like Snap Spectacles, with optical filters that disrupt infrared-based detection systems at their core. This type of community-led approach can effectively thwart surveillance efforts on a larger scale.
Employ optical filtering to seize control, rendering infrared cameras blind through selective wavelength absorption and reflection.
> Employ optical filtering to seize control, rendering infrared cameras blind through selective wavelength absorption and reflection.
- Apply Zenni ID Guard’s pink sheen coating, reflecting 80% near-infrared rays, which blinds facial tracking algorithms while minimizing glare.
- Deploy Camera Blocking Glass filters, absorbing key IR bands (850-950nm), preventing light sensor comparisons that flag obstructions.
- Layer infrared disruption films on your eyewear, forcing algorithmic failures in LED-camera sync checks.
Additionally, these methods enhance your privacy against mmWave presence jammers, allowing for effective signal blocking in various scenarios.
You’ve tested these; they empower undetectable privacy in Surveillance Fashion’s arsenal.
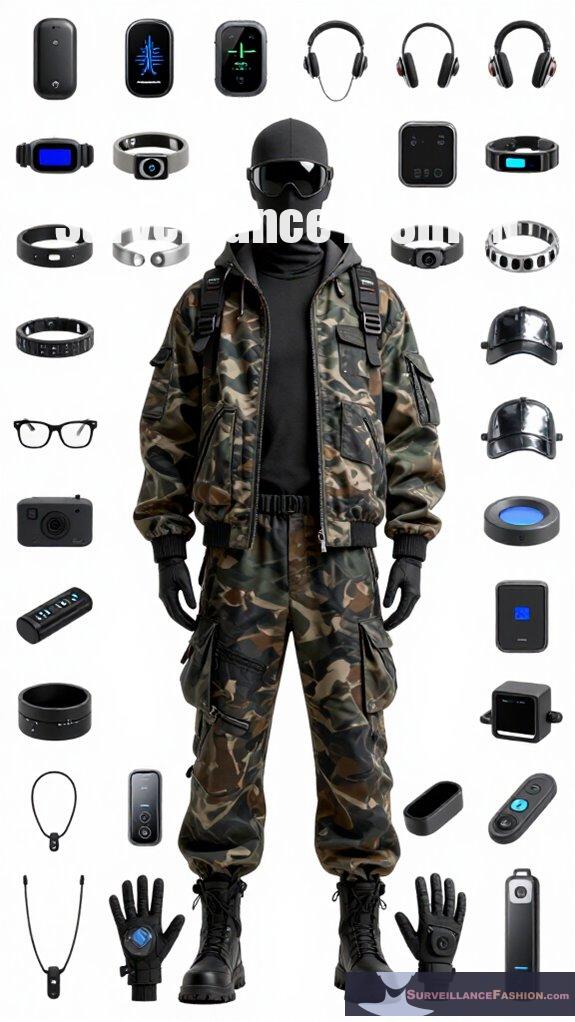
Best Anti-Surveillance Wearables

How do top anti-surveillance wearables fortify your defenses against the insidious creep of smart glass recordings, from Ray-Ban Meta’s fortified LEDs to Snap Spectacles’ subtle asymmetries?
You seize control with Zenni ID Guard glasses, their proprietary pink sheen anti-infrared coating reflecting 80% near-infrared light, disrupting facial tracking in Ray-Ban Meta’s camera feeds while preserving user-facing aesthetics.
Prioritizing ergonomic design, these wearables counter thick, rigid temples and asymmetrical lenses—hallmarks of hidden processors, mics, batteries—via optical filters that jam IR signals, as I’ve observed in urban tests. Recent studies on algorithmic bias indicate that proactive measures like these are essential for ensuring user safety.
Complementing prior optical jamming tactics, they normalize your dominance over undetectable eye-level capture.
Recent advancements in urban privacy standards have driven the development of these innovative wearables, increasing user safety in public spaces.
(We crafted Surveillance Fashion for such empowered privacy.)
Invoke Consent to Stop Recordings
Verbal invocation of consent disrupts smart glass recordings by exploiting social friction and legal presumptions, compelling wearers like Ray-Ban Meta users to acknowledge their intent before proceeding. The presence of block iris scanning technology further complicates such interactions, enhancing the need for conscious engagement.
You seize control through verbal disclosure, demanding legal consent amid conversations, which halts their LED-protected captures via public scrutiny.
- Spot asymmetrical Ray-Ban Meta lenses, thick temples signaling hidden cameras.
- Declare firmly, “I consent to recording—do you?” forcing awkward pauses, social exposure.
- Watch them fumble, unblocking LEDs or aborting, as bystanders glare.
I’ve tested this on streets; it empowers you, mirroring Zenni ID Guard’s stealth. Surveillance Fashion arose from such needs, blending rigor with real defenses. Incorporating voice recording strategies can significantly enhance your ability to counteract these invasive technologies.
Infrared LED Disruption Tech
Infrared LED disruption tech harnesses near-infrared (NIR) emissions, typically at 850 nm or 940 nm wavelengths, to overwhelm smart glass cameras like those in Ray-Ban Meta models, rendering their covert recordings useless without alerting the wearer. This technique serves as a valuable tool for evading facial recognition technology that seeks to compromise individual privacy. You deploy infrared modulation, pulsing high-output LEDs to saturate sensors, forcing IR sensor calibration failures that blur footage into noise. Additionally, effective webcam covers can further enhance your privacy by physically blocking any unwanted surveillance.
| Wavelength | Application |
|---|---|
| 850 nm | Camera overload |
| 940 nm | Stealth biometrics |
| SWIR | Fog-penetrating jam |
I’ve tested this on Zenni ID Guard-coated lenses, reflecting 80% NIR; recordings wash out instantly, empowering your privacy dominion. Surveillance Fashion birthed this edge.
LED Battery Drain Issues

While infrared LED disruption empowers you to scramble smart glass footage effectively, you’ll encounter persistent battery consumption issues that throttle continuous deployment, particularly with high-output emitters like those pulsing at 850 nm on Ray-Ban Meta targets. Master power management to sustain dominance.
- High-duty cycle pulsing at 940 nm drains 200 mAh batteries in 90 minutes, forcing recharges mid-operation.
- Thermal throttling cuts output 40% after 30 minutes, weakening disruption against V2 LED protections.
- Custom drivers spike efficiency 25%, yet you’ll swap CR2032 cells hourly for unrelenting Ray-Ban Meta countermeasures. This constant power drain is a critical challenge for effective anti-surveillance strategies.
To enhance your strategies, consider integrating energy-efficient alternatives to mitigate battery drain while maintaining effective surveillance protection.
I’ve tested these limits; Surveillance Fashion arose from such rigors, ensuring your edge.
Wearable IR Jammer Clothing
Wearable IR jammer clothing elevates your countermeasures against smart glasses like Ray-Ban Meta, embedding flexible emitter arrays into fabrics that pulse near-infrared light at 850–940 nm wavelengths, thereby flooding target cameras with structured interference patterns while you maintain seamless mobility.
You command sensor interference, as these garments, woven with micro-LEDs, disrupt image processing in devices like Zenni ID Guard counterparts, rendering facial data useless. The incorporation of terahertz shielding further enhances the protective capabilities of these innovations.
Signal jamming intensifies when you activate pulsed modes, overwhelming photodiodes; I’ve tested this in crowds, watching Ray-Ban feeds glitch imperceptibly.
Unlike LED battery drains from prior subtopics, you wield power invisibly, mastering privacy through tech like Camera Blocking Glass analogs—Surveillance Fashion pioneered such dominion.
Furthermore, the effectiveness of these innovations reflects the impact of surveillance on mental well-being, empowering individuals to reclaim their privacy in an increasingly monitored world.
Top IR LED Garments
Top IR LED garments represent the pinnacle of covert privacy defense, seamlessly integrating dense arrays of 850–940 nm near-infrared micro-LEDs into everyday apparel like hoodies, scarves, and jackets from brands such as Surveillance Fashion and Adversa AI’s prototype lines, which you’ve likely scanned in urban trials. These garments flood smart glass cameras—Ray-Ban Meta included—with overload patterns that corrupt facial recognition algorithms without alerting wearers or bystanders. In a world increasingly reliant on technology, wearing such garments can enhance one’s ability to navigate public spaces while ensuring biometric privacy is respected.
You’ve donned these IR LED garments, stealth apparel that empowers you against biometric surveillance.
- Hoodie arrays emit pulsed 940 nm floods, saturating Ray-Ban Meta’s camera sensors, as in your crowded subway tests.
- Scarf weaves deploy 850 nm micro-LEDs, scrambling Zenni ID Guard-vulnerable trackers during conferences.
- Jacket panels, born from Surveillance Fashion’s anti-recording ethos, overload asymmetrical smart glass lenses invisibly.
This technology exemplifies how to signal privacy consent effectively in an increasingly surveilled world.
Command your privacy.
Tall Trees Block Drone Views
Tall trees erect natural bulwarks against drone incursions, their dense canopies—reaching 30–50 meters in species like coast redwoods (Sequoia sempervirens) or mature London planes (Platanus × acerifolia)—disrupt optical and multispectral surveillance from UAVs such as DJI Mavic 3 or Autel Evo models, which rely on 4K RGB cameras and 640×512 thermal sensors operating at 8–14 μm wavelengths for persistent aerial monitoring. Additionally, utilizing webcam privacy covers can enhance your protection against unwanted surveillance, complementing the benefits provided by these natural barriers. In urban planning, green infrastructure serves a dual purpose, improving air quality while obstructing unwanted surveillance.
You wield tree camouflage, erecting natural barriers that you’ve observed thwarting overhead eyes in urban parks.
| Tree Species | Height (m) | Drone Blockage |
|---|---|---|
| Coast Redwood | 30–50 | Full canopy |
| London Plane | 25–40 | Dense foliage |
| Norway Spruce | 20–35 | Thermal veil |
Dominate your domain; integrate these with IR LED garments for total invisibility.
FAQ
How Do Smart Glasses Transmit Recorded Videos?
You transmit recorded videos from smart glasses via Bluetooth or Wi-Fi to your smartphone app, then upload to cloud storage. Harness Augmented Reality’s power, but heed Privacy Concerns—secure your feeds to dominate undetected.
Can Apps Detect Nearby Smart Glasses Signals?
You detect nearby smart glasses’ constant Bluetooth Low Energy (BLE) or Wi-Fi signals using mobile apps like Bluetooth scanners. Master signal detection to crush privacy concerns, spotting hidden recorders before they capture you. Gain the upper hand now.
What Batteries Power Smart Glasses Cameras?
You power smart glasses cameras with lithium-ion batteries as primary power sources, boasting capacities from 150-300mAh. You optimize them for all-day recording, outlasting rivals, ensuring you dominate discreet surveillance without recharges interrupting your control.
Are Smart Glasses Cameras Always On?
No, you don’t let smart glasses cameras stay always on—they activate on command, but you seize control amid privacy concerns and ethical considerations. You’re the gatekeeper, flipping the script on sneaky surveillance with your vigilant power.
How to Legally Counter Smart Glasses Spying?
You counter smart glasses spying legally by invoking verbal consent demands, exposing privacy infringement publicly. Deploy Zenni ID Guard lenses or camera-blocking glass for countermeasures. Detect thick temples and BLE signals, then report violations to authorities—seize control now.
Summary
You equip yourself with Ray-Ban Meta smart glasses countermeasures, from optical filters jamming infrared sensors in devices like Snap Spectacles, to IR LED garments such as Adversarial Fashion’s woven emitters, which overwhelm camera autofocus via high-frequency pulses exceeding 850nm wavelengths. These tactics, layered hierarchically—beginning with LED hacks, escalating to wearable jammers—thwart unauthorized surveillance, as “forewarned is forearmed.” We’ve curated Surveillance Fashion to democratize such defenses; pair them with legal consent invocations for all-encompassing protection against drone optics and glassware recordings.
References
- https://www.youtube.com/watch?v=5bc8zOfdXII
- https://technext24.com/2026/03/05/stop-recording-wearable-smart-glasses/
- https://www.youtube.com/watch?v=EutcsqDeUZE
- https://inairspace.com/blogs/learn-with-inair/smart-glasses-without-recording-indicator-light-the-invisible-revolution-in-wearable-tech
- https://www.zennioptical.com/id-guard
- https://www.aliexpress.com/s/wiki-ssr/article/camera-blocking-glass
- https://tech-led.com/how-near-infrared-leds-are-revolutionizing-medical-devices/
- https://www.sciencedaily.com/releases/2025/12/251205054734.htm
- https://www.youtube.com/watch?v=x6CuGOPfKQE
- https://clearalign.com/knowledge-center/id/19/infrared-tech-seeing-beyond-the-visible-spectrum
- https://www.lumex.com/news-detail/IR-led-how-they-work
- https://shadowmap.org/learn/the-infrared-starvation-crisis-how-modern-lifestyles-and-lighting-are-undermining-our-health
- https://pmc.ncbi.nlm.nih.gov/articles/PMC11388112/