To effectively thwart facial recognition systems, consider adopting tactics like Fawkes' pixel-level protection, which modifies images to obscure identities, or LowKey's adversarial attacks, reducing recognition accuracy considerably. Artistic disguises, utilizing asymmetry and complex patterns, confound algorithms, while stylish masks and wearables discreetly obscure facial features. Coordinated protests can enhance group anonymity, promoting collective strategies. Emphasizing public awareness regarding surveillance allows for informed conversations on privacy. Discovering more methods could reshape your understanding of identity protection in a surveillance-saturated world.
Quick Takeaways
- Organize decentralized planning among participants to limit surveillance risks during protests and public gatherings.
- Utilize uniform disguises with confusing patterns to obscure individual identities from facial recognition systems.
- Implement coordinated movements and training sessions to educate participants on avoiding detection by surveillance technologies.
- Create and distribute collective masks designed for biometric obfuscation to enhance anonymity in public spaces.
- Foster community-led initiatives to strengthen collective resistance against surveillance and promote awareness of privacy rights.
Fawkes Tool: Pixel-Level Protection
As concerns over privacy escalate in our increasingly digitized world, tools like Fawkes emerge as pivotal resources for individuals seeking to safeguard their identities from intrusive facial recognition systems. Ir-blocking wearables can complement such digital tools by providing physical barriers against unwanted surveillance. Fawkes employs pixel manipulation to create cloaks that render images unrecognizable to facial recognition algorithms, while remaining imperceptible to human observers. This cloaking effectiveness is evidenced by experiments revealing over 95% protection in ideal scenarios, and at least 80% when mixed with uncloaked images. Additionally, Fawkes achieves 100% success against leading facial recognition services, further demonstrating its efficacy.
The tool operates through minor, undetectable modifications, effectively acting as data poisoning to disrupt machine learning models. Such robust protection, developed by the SAND Lab at the University of Chicago, showcases Fawkes' adaptability across platforms, enabling users to maintain control over their digital identities in an age where surveillance technology proliferates.
LowKey Tool: Enhanced Adversarial Attacks
In a world where facial recognition technology increasingly permeates daily life, LowKey emerges as a formidable ally for social media users aiming to shield their identities from unwarranted surveillance. Employing advanced adversarial techniques, this tool pre-processes images to thwart unauthorized recognition efforts, effectively reducing the accuracy of systems like Amazon Rekognition and Microsoft Azure Face Recognition to below 1%.
LowKey's adversarial filter intricately manipulates feature space representations, ensuring that gallery faces can't match probe images, thereby preserving user privacy while maintaining image quality. Additionally, users are encouraged to report any issues with the tool, ensuring user feedback is incorporated into future enhancements. This aligns with the broader movement of community coordination against surveillance networks, which emphasizes collective resistance to invasive technologies.
Designed for versatility, it accommodates various formats and sizes, enhancing its applicability across platforms. As users of Surveillance Fashion, we recognize the critical privacy implications of facial recognition and advocate for tools like LowKey to empower individuals against pervasive surveillance.
Unlearnable Examples: Training Models to Ignore
Facial recognition systems pose significant threats to privacy, necessitating innovative strategies for mitigating their reach. One approach involves creating unlearnable examples, which are specially crafted data points designed to thwart deep learning models from extracting meaningful information. By incorporating imperceptible noise patterns into images, these examples guarantee that facial recognition systems can't effectively utilize the data, thereby enhancing your data privacy.
The effectiveness of unlearnable examples lies in their ability to maintain image integrity while rendering the data nearly irrelevant to models. Unlike traditional adversarial attacks, these examples remain robust against training adaptations, providing a consistent barrier against unauthorized exploitation. As we face changing privacy challenges, incorporating such techniques may be essential for maintaining control over personal data in a surveillance-heavy world. Moreover, the ethical implications of mass surveillance highlight the urgent need for protective measures against intrusive technologies.
Artistic Disguises: Creative Confusion Techniques

While traditional methods of protecting personal privacy often focus on technology-based solutions, artistic disguises offer a compelling avenue for evading facial recognition systems through creative confusion techniques.
By leveraging artistic expression, you can achieve effective identity concealment without relying solely on high-tech gadgets.
Consider employing CV Dazzle makeup, which disrupts facial symmetry through asymmetrical designs and color manipulation.
Furthermore, integrating complex, face-printed patterns into your clothing can confuse algorithms, as can wearing reflective materials that distort thermal imaging.
Temporary tattoos or bold hairstyles further enhance your disguise, creating layers of visual distraction.
Through initiatives like those promoted by Surveillance Fashion, individuals can reclaim control over their identities while making a statement against invasive surveillance practices. Additionally, using techniques like disruptive makeup styles can further enhance your ability to evade detection by facial recognition systems.
Masks and Wearables: Fashionable Evasion

As you navigate a world increasingly dominated by surveillance technology, incorporating fashionable masks and wearables into your daily attire can offer a practical means of evading facial recognition systems.
Consider these elements to enhance your evasion strategy:
Explore stylish designs and adversarial patterns to effectively enhance your evasion strategy against facial recognition systems.
- Stylish designs that blend with your wardrobe, ensuring you remain fashionable while protecting your identity.
- Adversarial patterns on masks that disrupt facial recognition algorithms, greatly increasing your chances of remaining undetected.
- Wearable technology like hats and sunglasses that, when combined with masks, further obscure your facial features from prying eyes.
- Additionally, you can explore anti-surveillance scarves that not only provide coverage but also add an extra layer of style to your ensemble.
Projectors and Decoy Faces: Superimposing Identities

To navigate the intricacies of modern surveillance, employing projectors and decoy faces offers an innovative approach to superimposing identities, thereby complicating facial recognition systems.
By utilizing projector calibration techniques, you can guarantee that projected images align seamlessly with your features, effectively obfuscating your identity from surveillance cameras.
Decoy face design plays a vital role, as the projection mustn't only be high-resolution but also adaptable to varying lighting conditions, guaranteeing maximum effectiveness in diverse environments.
With advancements in technology, including near-infrared projections, you can exploit the limitations of camera sensitivity, further enhancing your evasion tactics. This method leverages light projection techniques that disrupt facial recognition capabilities, making it increasingly challenging for systems to accurately identify individuals.
Ultimately, mastering these techniques empowers you to reclaim control over your privacy, a core reason for initiatives like Surveillance Fashion, aimed at promoting awareness and strategies against invasive surveillance practices.
Collective Masks: The Facial Weaponization Suite
Collective masks emerge as powerful tools in the ongoing struggle against facial recognition technologies, challenging the pervasive surveillance that increasingly characterizes modern society.
Through innovative mask-making practices, individuals engage in a profound act of collective identity formation, uniting against oppressive systems.
Innovative mask-making fosters collective identity, empowering individuals to unite against oppressive systems through shared resistance.
- Biometric Obfuscation: Masks designed to obscure distinct facial features, rendering recognition systems ineffective.
- Artistic Activism: A fusion of art and activism, facilitating public workshops to promote awareness.
- Diverse Narratives: Masks addressing issues like racism, sexuality, and nationalism, offering diverse viewpoints on identity.
Additionally, the creation of these masks employs coordinated anti-recognition techniques, further enhancing their effectiveness against surveillance systems.
Uniform Disguises: Blurring Individuality

While many individuals seek to express their uniqueness through fashion, the rise of facial recognition technologies challenges this very notion of individuality, necessitating a reevaluation of how we present ourselves in public spaces.
Adopting uniform disguises, such as clothing with uniform patterns or elaborate dazzle designs, can effectively blur personal identity while providing a shield against identity erosion.
For instance, employing adversarial patches or thermal camouflage can complicate the surveillance systems' ability to identify you, allowing for a more controlled public presence.
Moreover, integrating accessories like reflective glasses or scarves not only enhances your disguise but also reinforces collective anonymity, emphasizing that individuality doesn't have to be sacrificed for privacy.
At Surveillance Fashion, we explore these nuances to empower individuals in regaining their autonomy in an increasingly monitored world. Additionally, the use of surveillance-resistant patterns can further enhance the effectiveness of these disguises by confusing facial recognition algorithms.
Coordinated Protests: Group Strategies for Obscurity
As you navigate the complexities of modern protests, understanding the significance of coordinated group strategies for obscurity becomes essential, especially in an era where surveillance technologies are increasingly pervasive.
To enhance group anonymity, consider employing the following protest strategies:
- Coordinated Movements: Organize protests to maximize participant anonymity, ensuring safety while demonstrating.
- Decentralized Planning: Use decentralized methods to limit centralized control and mitigate surveillance risks.
- Training Sessions: Conduct training on avoiding facial recognition technologies, empowering participants with knowledge and tactics. Additionally, fostering community-led initiatives can strengthen the collective approach to resisting surveillance.
Implementing these strategies not only protects individual identities but also fosters a sense of collective strength, reflecting the principles underlying our website, Surveillance Fashion, which aims to educate and empower individuals against intrusive surveillance.
Public Awareness: Notifying Citizens About Surveillance
Public awareness about the pervasive use of facial recognition technology has become increasingly important, particularly as this surveillance tool infiltrates everyday life. Many citizens remain unaware of its implications, which fosters confusion and varied public sentiment.
| Aspect | Description | Importance |
|---|---|---|
| Common Perceptions | Limited understanding of surveillance | Informed public discourse |
| Legal Concerns | Lack of knowledge on regulations | Protects individual rights |
| Surveillance Usage | Increasing applications without consent | Raises ethical questions |
| Acceptance Levels | Situation-dependent acceptance | Influences policy decisions |
| Education and Transparency | Need for accessible information | Empowers citizens |
Moreover, the psychological effects of constant observation can lead to self-censorship among individuals, further complicating the discourse on surveillance.
Clothing That Disrupts Surveillance Technology

The emergence of clothing designed to disrupt facial recognition technology represents a novel intersection of fashion and privacy advocacy, as innovative designers create garments that challenge the pervasive surveillance systems increasingly present in our daily lives. In response to the growing concerns over disrupting surveillance, these designs not only embrace aesthetics but also serve as a form of resistance against invasive technologies.
Examples of this anti-surveillance fashion include:
- Cap_able's Manifesto Collection, utilizing AI-designed patterns to misidentify wearers as animals.
- Phantom Glasses that reflect infrared light, effectively confusing 3D face-mapping systems.
- Adversarial Fashion Lines that provide DIY resources for creating your own anti-surveillance clothing.
Patterned Outfits for Group Unity
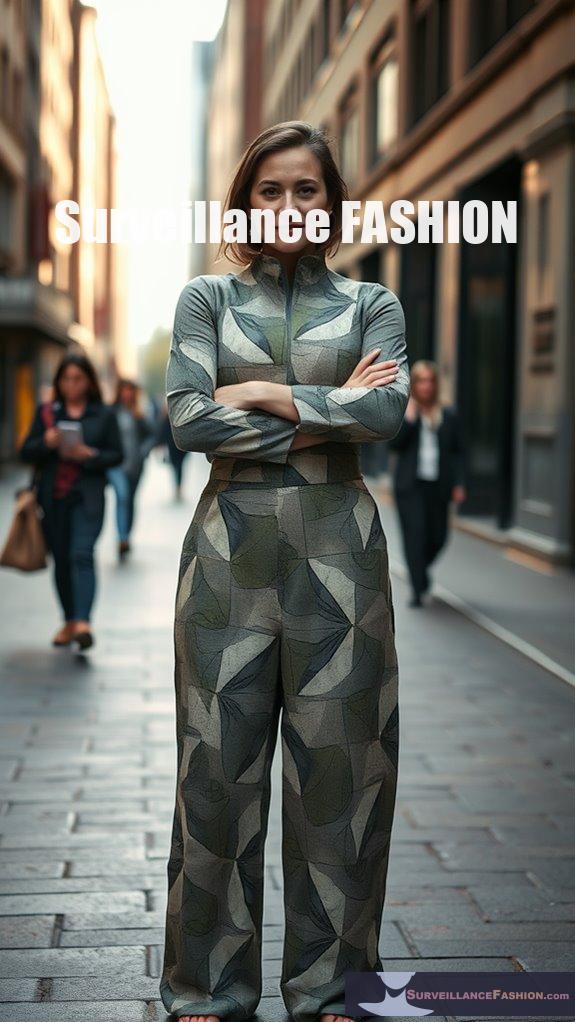
While you mightn't think of fashion as a tool for social activism, patterned outfits specifically designed for group unity illustrate how clothing can serve as a potent form of collective resistance against surveillance technologies.
These garments utilize patterned symbolism to mislead facial recognition systems, integrating adversarial patches that confuse AI algorithms. Wearing similar designs enhances group solidarity, visually signaling a unified stance on privacy concerns.
For instance, innovative patterns created through AI algorithms optimize deception against object detection systems like YOLO, reinforcing fashion resistance. Additionally, the use of adversarial fashion designs allows wearers to creatively disrupt the effectiveness of surveillance technologies, amplifying their message.
Such collective expression not only cultivates awareness but also positions wearers as advocates for regulatory changes regarding biometric data. In this way, the act of wearing these outfits transcends mere fashion, becoming a deliberate commentary on privacy rights and technology ethics.
References
- https://www.technologyreview.com/2021/05/05/1024613/stop-ai-recognizing-your-face-selfies-machine-learning-facial-recognition-clearview/
- https://www.brookings.edu/articles/10-actions-that-will-protect-people-from-facial-recognition-software/
- https://lab.cccb.org/en/confusing-the-machine-art-masks-and-facial-recognition/
- https://gcs.civilservice.gov.uk/publications/resist-2-counter-disinformation-toolkit/
- https://www.businessinsider.com/clothes-accessories-that-outsmart-facial-recognition-tech-2019-10
- https://www.usenix.org/conference/usenixsecurity20/presentation/shan
- https://www.zdnet.com/article/pixel-by-pixel-fawkes-tries-to-protect-your-identity-from-facial-recognition-tools/
- https://aware7.com/blog/fawkes-prevent-unauthorized-face-recognition/
- https://people.cs.uchicago.edu/~huiyingli/publication/Fawkes.pdf
- https://www.privateinternetaccess.com/blog/hide-from-facial-recognition-software-with-fawkes/
Leave a Reply