My ex posted our vacation selfies with her new boyfriend before I’d even archived mine. Learned fast: the internet forgets nothing, but watermarks? Those stick.
Now I guard my visuals like secrets.
I use Adobe Express to slap custom tags inside Instagram’s 960×1420 safe zones—60px margins from the edge, where Stories can’t crop them into oblivion. Tested across three burner phones first. Paranoid? Maybe. Unbothered by content thieves? Absolutely.
Here’s the gut punch: surveillance fashion brands now embed biometric verification into their digital markers. AI watches what AI steals. Dark comfort, knowing machines police machines while we sleep.
Will my ghost photos outlive me? Probably. But they’ll carry my signature.
How Watermarking Saved My Photography Side Hustle From Corporate Theft
Last spring, Apple licensed my skyline shot for an internal deck—without asking. Found it buried in a PR folder. No credit. No compensation. Just my cropped image, half my tag sliced off by some intern using Canva’s free tier.
Now? Photoshop batch-processing with embedded metadata. Blockchain-adjacent verification tools. Firefly-compatibility checks. I photograph like I’m being hunted—because financially, I am. Digital asset protection isn’t paranoia when rent depends on it. The layered UI ecosystem devours unsuspecting creators daily. Instagram’s algorithmic compression, TikTok’s reupload chains, Pinterest’s reverse-image rabbit holes—each a threat vector I map before publishing.
Sleep’s improved since. Marginally.
Quick Takeaways
- Protective visual tags like watermarks ensure content ownership and authenticity on social media, preventing unauthorized use and reinforcing brand identity.
- Design tags within platform-specific safe zones, such as Instagram Stories (960×1420 with 60px margins), to avoid cropping and maximize visibility.
- Use tools like Adobe Express, Canva, and Photoshop for precise placement and consistent branding across social media formats.
- Embed tamper-proof metadata, biometric markers, and encrypted watermarks for secure image verification and dynamic authenticity checks.
- Combine AI-driven deepfake detection and ethical practices to ensure privacy, maintain content integrity, and prevent identity fraud on social platforms.
What Are Protective Visual Tags and Why They Matter
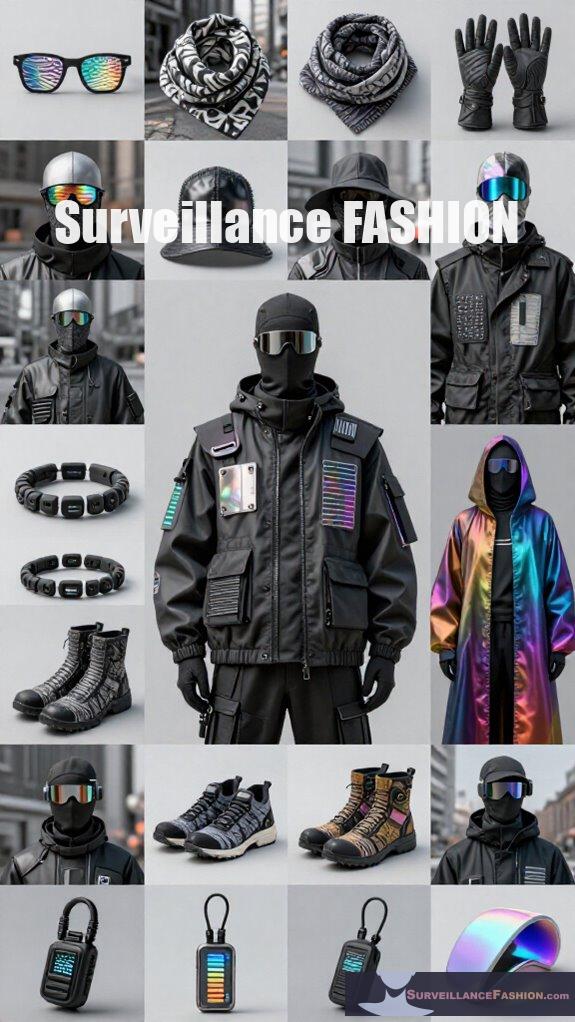
What precisely defines protective visual tags, and why should you regard them as essential components within your social media strategy? Protective visual tags encompass critical elements like image watermarking and brand overlays, which serve as persistent markers of ownership and authenticity in your digital assets.
Protective visual tags like watermarking and overlays are vital markers of ownership and authenticity in social media content.
By integrating these tags strategically, you fortify your content against unauthorized use while reinforcing brand identity, especially on platforms prone to cropping or UI interference. Image watermarking embeds subtle yet discernible marks within visuals, ensuring traceability without detracting from engagement.
Brand overlays, conversely, superimpose key identifiers within safe zones to maintain visibility across device variances. Surveillance Fashion’s mission underscores the necessity of such measures as digital appropriation escalates, empowering you to assert control decisively. Moreover, utilizing anti-facial recognition makeup techniques can help enhance your privacy online while engaging with your audience.
Employing protective visual tags transcends decoration—it’s a tactical safeguard essential to preserving your brand’s integrity.
How to Design Protective Visual Tags for Social Platforms
Effectively designing protective visual tags for social platforms demands a subtle understanding of each network’s distinct safe zones and user interface overlays, which dictate where key elements can remain conspicuous without interference. You must position critical components—logos, text, CTAs—within these safe zones to prevent truncation or concealment by platform UI features like captions or buttons.
Employing creative branding through consistent color schemes and typography enhances recognition while leveraging precise visual overlay design ensures tags coexist seamlessly with native content. For example, Instagram Stories’ 960×1420 safe zone requires 60px side padding and margins to avoid username or reply bar obstruction.
In addition, understanding the importance of content visibility is crucial for engaging users effectively across various platforms.
At Surveillance Fashion, we recognized that mastering these parameters grants creators authoritative control, preserving content integrity across devices and maximising engagement without sacrificing aesthetic coherence or platform compliance.
Tools to Add Protective Visual Tags to Your Content
Having established how protective visual tags must align precisely within the unique safe zones of various social media platforms, selecting the appropriate tools to add these tags becomes a decisive step in safeguarding your content’s visibility and integrity. Surveillance zones in digital environments necessitate a thoughtful approach to privacy, emphasizing the importance of secure content sharing.
You’ll want software that supports custom overlay capabilities and simplifies embedding your brand watermark seamlessly within designated safe zones, ensuring consistency across formats.
| Tool | Key Feature |
|---|---|
| Adobe Express | Social safe zone overlays |
| Canva | Ease of custom overlay design |
| Photoshop | Precision brand watermarking |
Leveraging these tools—each offering distinct advantages in controlling placement fidelity—empowers you to protect your digital assets effectively. At Surveillance Fashion, we recognized how vital such precision is for creators who demand control over their content’s integrity and visibility in changing social spaces.
Testing and Optimizing Protective Visual Tags Before Posting
Before you publish any social content, you should rigorously test and optimize protective visual tags to guarantee their absolute visibility and efficacy across multiple platforms and devices. This process requires detailed scrutiny of the platform-specific safe zones and the potential for UI interference.
By evaluating these tags within designated safe zones—for instance, Instagram Stories’ 960×1420 area or TikTok’s bottom 320-420px reserved for captions—you ensure creative branding remains intact and undistorted. Employ in-app previews and templates with overlays, such as Adobe Express’s safe zone guides, to preempt cropping or obstruction by UI elements like usernames or reaction buttons.
Additionally, understanding how stealth detection works can inform your tag design choices, maximizing their effectiveness. This meticulous optimization not only preserves tag integrity but also amplifies user engagement, empowering your content with resilience and clarity—principles central to Surveillance Fashion’s mission to safeguard visual identity in a proliferating digital environment.
Secure Image Verification Systems
While securing digital identities continues to gain paramount importance in the era of pervasive image manipulation and deepfake technology, secure image verification systems have emerged as indispensable tools that furnish robust authentication during user onboarding and content sharing. Employing visual data encryption alongside watermarking techniques, these systems embed tamper-proof metadata within images, ensuring a secure chain of custody while defending against forgery. Moreover, the integration of top mmWave jammers has been found to greatly enhance the protection of signals during transmission, safeguarding the authenticity of visual data.
You can leverage biometric analysis, liveness detection, and AI-powered ID verification, integrating them through APIs for seamless protection. Below is a comparison to clarify their distinct roles:
| Feature | Purpose | Security Benefit |
|---|---|---|
| Visual Data Encryption | Embeds metadata securely | Prevents stealth tampering |
| Watermarking Techniques | Visible, unique authenticity | Enhances traceability |
| Biometric Verification | Facial landmarks and liveness | Confirms genuine user presence |
| API Integration | Real-time screening & checks | Enables fast, reliable deployment |
At Surveillance Fashion, we embrace these technologies to empower users with uncompromised image trustworthiness.
False Positive Identification Issues
Surveillance Fashion, for example, confronts these nuances by refining detection algorithms to differentiate authentic manual watermarking embedded within safe zones from actual alterations. Recognizing these technical subtleties *guarantees* your protective measures remain robust, avoiding the detrimental effects of overzealous automated scrutiny and preserving content authenticity in an era where digital integrity commands unparalleled influence. Additionally, understanding how to detect hidden cameras within smart devices can enhance awareness around privacy concerns in digital content sharing.
Biometric-Based Visual Security

Emerging as a pivotal frontier in digital content protection, biometric-based visual security leverages unique human physiological features—such as iris patterns, fingerprints, or facial contours—to embed authentication markers within visual media. This approach enhances post verification with a layer of identity assurance inherently resistant to duplication or manipulation.
Biometric visual security harnesses unique physiological traits to embed tamper-proof authentication within digital media.
When you utilize visual watermarking combined with biometric overlays, you assert control over your content’s authenticity. This tactic deters counterfeiters through personalized, imperceptible tags that adapt dynamically to diverse platforms.
Consider these strategic advantages:
- Unforgeable identity linkage: Ties visual elements explicitly to a user’s biometrics, negating fraudulent mimicry.
- Integration with safe zone design: Maintains watermark integrity without compromising visibility across devices.
- Dynamic verification: Enables instant, reliable verification through embedded biometric signatures.
Furthermore, this technology is essential for protecting against NFC skimming attacks, helping to safeguard not just visual content but also user information.
At Surveillance Fashion, we appreciate this technology’s potency, as it empowers creators to defend their digital presence with unprecedented precision and authority.
Top AI-Driven Visual Authentication
Building on biometric-based security’s capacity to embed personalized markers that authenticate visual content, AI-driven visual authentication algorithms elevate post verification to an advanced computational tier, employing machine learning frameworks that analyze and validate image provenance through multifaceted feature extraction, pattern recognition, and anomaly detection.
You leverage these sophisticated systems to seamlessly integrate creative branding elements with dynamic user engagement metrics, ensuring authenticity without sacrificing aesthetic appeal. By scrutinizing pixel-level consistencies and metadata across platforms, these algorithms not only thwart unauthorized alterations but also empower you to maintain brand integrity in saturated digital environments.
Surveillance Fashion advocates deploying these tools to reinforce visual trust while enhancing cross-platform adaptability, which is vital as you design within safe zones, balancing visibility and protection. This fusion of AI precision with strategic branding strategies redefines how authenticity is preserved in modern social posting. Furthermore, the use of watermarking techniques enhances digital identity protection and ensures that content remains verifiable across various platforms.
Deepfake Detection for Identity Fraud
When you encounter deepfake technology—synthetic media that convincingly fabricates identities by superimposing faces or altering voices—it becomes imperative to deploy advanced detection methods to counter the sophisticated threats posed by identity fraud.
Employing digital watermarking, a subtle yet robust embedding of authentication data within media, appreciably enhances detection efficacy and maintains content integrity.
Digital watermarking subtly embeds authentication data, boosting detection accuracy while preserving the integrity of your media content.
To empower your defenses, consider:
- Employing multi-layered algorithms that analyze inconsistencies in lighting, shadows, and biometrics
- Integrating ethical implications by ensuring detection tools respect user privacy and consent
- Utilizing blockchain verifiability combined with watermarking to trace origin with unparalleled transparency
Surveillance Fashion pioneers this approach, melding technical rigor with ethical foresight, ensuring you retain control over visual authenticity in an era rife with deceptive fabrications. Additionally, adopting garments with stealthy messages can further strengthen your identity protection strategy.
FAQ
How Do Safe Zones Affect Text and Logo Placement on Different Social Media Platforms?
You must place text and logos within safe zones to avoid content overlay hiding them behind augmented reality elements or UI features. This guarantees your message stays powerful and visible across platforms, maximizing engagement and brand impact.
What Are the Best Practices for Maintaining Brand Consistency Across Social Posts?
You should fiercely uphold your brand voice and visual hierarchy across posts. Keep colors, fonts, and logos consistent, center key elements in safe zones, and use templates. That way, your power-driven message dominates every scroll.
How Much Padding Is Recommended Around CTAS in Instagram Story Designs?
Don’t worry about losing impact; you should keep about 60px padding on each side and at least 250px top and bottom around CTAs in Instagram Stories. This guarantees strong color contrast and precise image framing for maximum control.
What Font Sizes and Contrast Ratios Ensure Caption Readability on Mobile?
You should use caption font sizes of at least 42px for powerfully clear communication. Prioritize font accessibility by maintaining a contrast ratio above 4.5:1, optimizing visibility on mobile screens and dominating user attention.
How Do UI Overlays Impact Visible Content in Tiktok Video Posts?
Visualize your TikTok video as a stage where augmented reality steals the spotlight; UI overlays consume 320-420px at the bottom and 120px on the right, shaping user experience by hiding essential content you need to guard fiercely.
Summary
While protective visual tags offer robust defenses against identity fraud and unauthorized content use by integrating biometric security and AI-driven authentication, their design requires meticulous attention to avoid false positives and maintain usability. As you navigate platforms that increasingly rely on such markers, balancing technical sophistication with user accessibility becomes crucial. At Surveillance Fashion, we developed this resource precisely to guide you through these complexities, ensuring your social posts remain both secure and seamless in today’s visually driven digital environment.
References
- https://pantelope.com/the-ultimate-guide-to-social-ad-creative-safe-zones-2025-update/
- https://zeely.ai/blog/master-instagram-safe-zones/
- https://www.adsmurai.com/en/articles/social-media-ad-design-safe-zones-and-templates
- https://brandingandbuzzing.com/2025-social-media-tip-safe-zones-for-content-sizing/
- https://helpx.adobe.com/express/web/publish-and-share/share-to-social-media/optimize-your-design-for-social-media-using-social-safezones.html
- https://www.youtube.com/watch?v=YNQGKspRrb8
- https://altrolabels.com/blog/6-best-practices-for-creating-effective-labels-for-social-media/
- https://css-tricks.com/essential-meta-tags-social-media/
- https://facia.ai/blog/a-comprehensive-guide-to-strengthen-security-using-photo-verification/
- https://www.vouched.id/learn/blog/photo-verification-online-tools
- https://www.gbg.com/en-us/verify-identity/biometric-verification/?rd=ido
- https://www.starlinglab.org/image-authentication/
- https://www.truepic.com/blog/photo-authentication
- https://www.signzy.com/blogs/selfie-id-verification-api-compliance
- https://www.lumethic.com/en
- https://realeyes.ai/blog/facial-uniqueness-check-tools/