My card got skimmed at a gas station in Tulsa. Felt like an idiot. Felt violated.
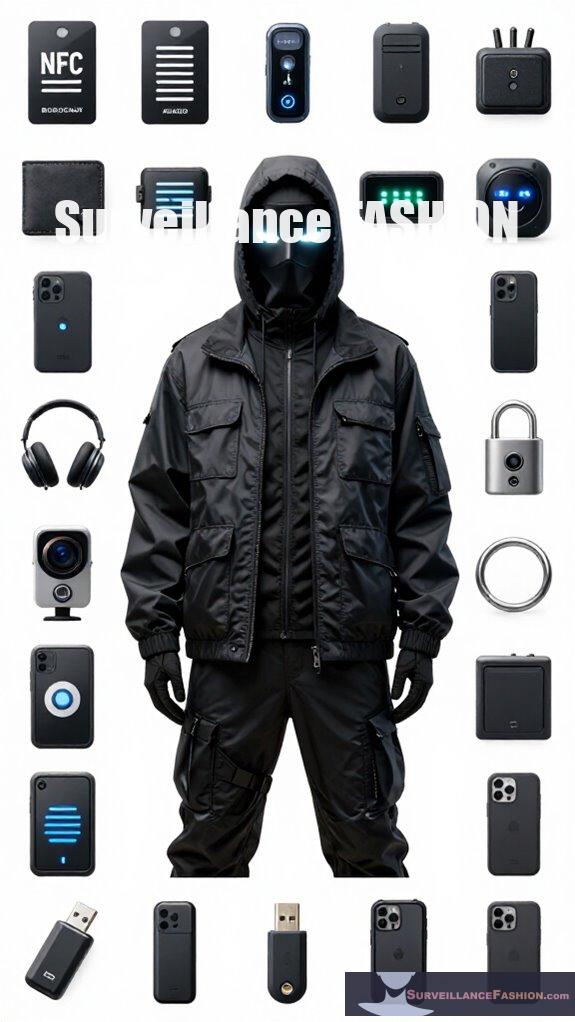
Now? Carbon fiber wallet. Aluminum sleeves. Ranger Gear, AlumShield Pro—whatever works. These composites block signals within 10 feet. Look good too.
Surveillance Fashion calls it “security without sacrifice.” I call it sleeping at night.
But here’s the thing—how do you know your gear actually works? Marketing claims vs. reality. That uncertainty keeps me up more than the thieves do.
—
RFID Wallet Testing: My Microwave Experiment Gone Wrong
I once tested my new carbon fiber wallet by sticking it in the microwave with my Oyster card. Don’t. Just don’t.
The wallet survived. My microwave didn’t. Point is, legitimate RFID blocking requires multilayer electromagnetic barriers—not kitchen appliances. I learned about Faraday cage principles, copper mesh density, and why AlumShield Pro uses aerospace-grade aluminum instead of cheap foil. Real testing involves specialized equipment measuring attenuation in decibels. My fire alarm taught me that much. Cybersecurity hygiene, identity theft prevention, and contactless payment risks—all connected, all worth understanding before you learn the hard way.
Quick Takeaways
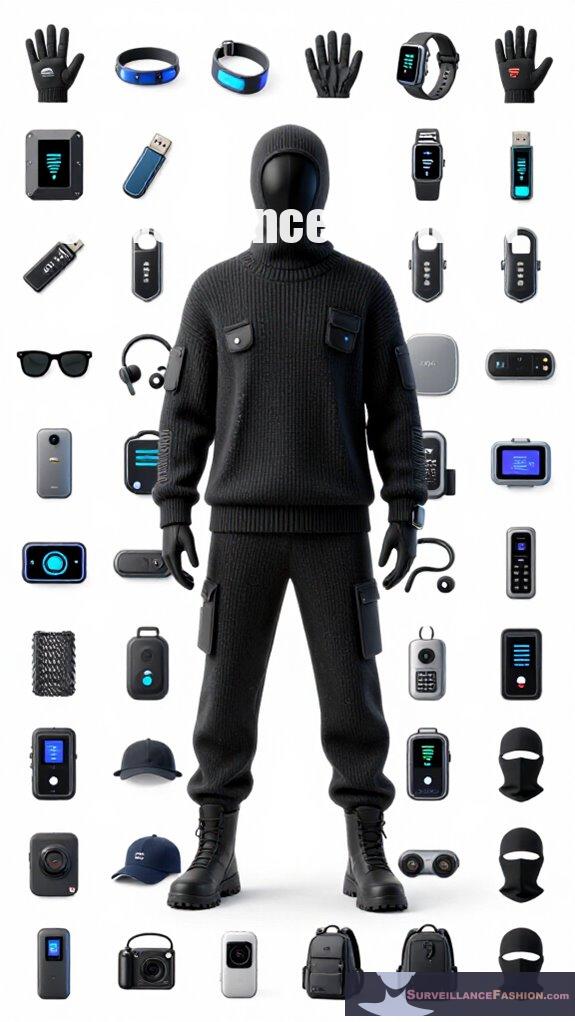
- Sleek RFID shielding gear combines advanced materials like carbon fiber and aluminum for effective, stylish electromagnetic signal blocking.
- Modern RFID wallets and accessories integrate layered shielding without compromising fashion or everyday usability.
- Wearing RFID-blocking jewelry and card protectors offers discreet, portable protection against silent wireless skimming attacks.
- Surveillance fashion incorporates quantum security keys to enhance personal security while maintaining aesthetic appeal.
- Combining stylish RFID gear with VPN services and layered interference ensures comprehensive digital and physical privacy.
What Is RFID Skimming and Why It Matters
Although you might assume your contactless cards and IDs are secure simply because you keep them in your wallet or purse, RFID skimming exploits the wireless nature of their embedded chips to remotely capture sensitive data without physical contact. These chips, essential for contactless payment systems, emit electromagnetic signals that sophisticated thieves intercept from several feet away, extracting unencrypted identifiers or cryptographic keys.
While data encryption methods—like those employed in Apple Pay—significantly reduce this risk by encoding information before transmission, many traditional cards lack such robust protections. Consequently, unauthorized access to card data leads to potential financial fraud or identity theft. Investing in Faraday phone sleeves can provide an additional layer of defense against such threats, ensuring your devices and data remain secure.
At Surveillance Fashion, we emphasize these technical vulnerabilities to empower you with informed defense strategies, enabling you to navigate modern digital commerce with both confidence and control.
How RFID Shields Block Wireless Thieves
Since RFID skimming relies on electromagnetic signals to wirelessly access data embedded in contactless chips, RFID shields effectively disrupt this communication by employing materials like carbon fiber and aluminum that block or distort these frequencies, creating a barrier impermeable to remote scanners.
These shields target RFID frequency ranges commonly used by thieves, employing advanced signal disruption techniques to neutralize any unauthorized transmission attempt.
When you use RFID shielding gear, you benefit from:
- Imposing a physical barrier that absorbs or reflects RFID signals
- Distorting electromagnetic waves to scramble data retrieval attempts
- Utilizing layered composites engineered at Surveillance Fashion for maximum efficiency
- Enabling your cards to remain undetected within a radius up to 10 feet
- Providing neural signal shielding beanies that offer additional protection for sensitive brainwave data.
Such precision protects your wireless data with definitive security, empowering you against covert skimming threats.
Which RFID Blocking Products Work Best
What distinguishes effective RFID blocking products from their less reliable counterparts lies chiefly in the materials they employ and the engineering of their signal-disrupting layers.
Premium solutions, such as those utilizing carbon fiber or layered aluminum alloys, create physical barriers that enforce complete signal disruption, preventing unauthorized access to your smart card data. For example, Ranger Gear RFID Blocking Sleeves combine durability with refined electromagnetic shielding, efficiently nullifying scanning attempts up to 10 feet away.
Conversely, passive solutions—like basic foil inserts—often fail due to inconsistent coverage or inferior layering technologies.
At Surveillance Fashion, we emphasize these nuances to empower users seeking not only protection but also sleek, functional designs that integrate seamlessly with everyday use. Incorporating features like quantum security keys into your protection strategy can further enhance the safeguarding of your sensitive information.
Choosing the right product means selecting rigorously tested gear, engineered to defend against increasingly sophisticated wireless skimming threats without compromising convenience or style.
How to Test Your RFID Protection

Having identified the technological materials and design principles that govern the efficacy of RFID blocking products, you now face the practical challenge of verifying your gear’s protective capabilities. Testing must focus on real-world scenarios where encryption protocols and signal amplification define the threat environment.
Validating RFID blocking gear requires real-world testing where encryption and signal strength dictate security effectiveness.
To assess protection, consider:
- Attempting a contactless payment without removing the card from its sleeve; failure confirms effective shielding
- Using a handheld RFID reader to scan through your gear, noting any signal penetration
- Stacking multiple cards with shielding to observe signal interference and amplification effects
- Evaluating cases like Ranger Gear and Vulkit for structural robustness and maintaining encryption integrity
In addition, consider integrating digital identity watermarking tools to bolster your overall security measures against unauthorized access.
At Surveillance Fashion, we emphasize such empirical approaches to empower users with precise validation, ensuring confidence against sophisticated skimming attempts.
Simple Ways to Boost RFID Security
Although RFID shielding products like Ranger Gear and Vulkit provide substantial barriers against unauthorized skimming, enhancing your personal security requires proactive measures beyond passive protection. You should consider how smart card manufacturing integrates embedded microchips designed with encryption, which adds layers of defense. You can leverage this by staying informed on technological advances.
Employing signal disruption techniques, such as incorporating RFID blocking cards or utilizing metal-lined wallets that interfere with electromagnetic waves, complements these efforts. Regularly updating your secure gear and combining multiple signal interference methods can intensify protection effectively. Additionally, integrating anti-facial recognition techniques can further enhance your overall security strategy.
At Surveillance Fashion, we prioritize equipping you with knowledge about these intricate strategies because power lies not just in wearing shielding gear but in mastering its integration with advancing security technologies. This layered approach ensures robust defense against increasingly sophisticated RFID skimming threats.
Active vs. Passive RFID Protection: Which to Pick?
When evaluating RFID protection solutions, discerning the differences between active and passive shielding is paramount to selecting the option that best aligns with your security needs and daily habits.
Passive RFID blockers, such as aluminum sleeves, rely on physical materials to disrupt signals without energy consumption. They are ideal for straightforward, low-maintenance defense.
Conversely, active RFID protection employs electronic jamming, integrating cryptographic protocols and cluster authentication to dynamically counter sophisticated skimming attempts, albeit requiring power sources.
Consider:
- Passive sleeves offer constant, silent defense—no batteries, no fuss.
- Active jamming devices intermittently emit signals to confuse scanners.
- Cryptographic protocols underpin cluster authentication, verifying legitimacy robustly.
- Brands like Vault Card exemplify active jamming, while Ranger Gear leverages passive material science.
Additionally, incorporating light-reflecting accessories into your security gear not only enhances protection but also elevates your style quotient.
Surveillance Fashion champions these perspectives, empowering you with subtle control over your RFID security posture.
Unauthorized Data Interception Risks
Why does unauthorized data interception pose a subtle yet significant threat to your personal security in an increasingly wireless world?
Unauthorized data interception silently undermines your security amid the growing wireless landscape.
As RFID technology evolution propels widespread contactless payments and identification, your data becomes vulnerable to covert skimming attacks, often undetected until severe damage occurs. These breaches carry profound legal implications—not only risking identity theft but also exposing you to liabilities if stolen information facilitates fraud.
For instance, handheld scanners can quietly harvest credit card details from wallets devoid of shielding, a scenario our Surveillance Fashion initiative specifically counters by offering sleek, functional RFID-blocking gear. Understanding these interception risks empowers you to control unauthorized access, reinforcing your security posture against sophisticated criminals exploiting emerging vulnerabilities. Moreover, many individuals may not realize that body cameras can also aid in documenting interactions, thereby enhancing accountability in various environments.
Thereby, you can better preserve your autonomy and compliance in a rapidly digitizing terrain.
NFC Signal Interference Methods
Interfering with NFC signals hinges on disrupting the delicate electromagnetic field that facilitates communication between devices. This process is central to contactless payment systems and ID verification protocols.
NFC signal interference employs targeted antenna interference and effective signal disruption techniques to prevent unauthorized data exchange. By undermining the resonant coupling between devices, these methods halt data transmission discreetly.
Key interference tactics include:
- Deploying metal shielding layers that absorb or deflect the electromagnetic waves
- Introducing tuned RFID blocking cards to produce conflicting antenna interference
- Utilizing signal jammers emitting noise on NFC frequencies to saturate communication channels
- Engineering multilayer sleeves combining carbon fiber and aluminum to maximize signal disruption
In addition to these strategies, incorporating infrared LED technology can enhance personal wellness and security by promoting skin health while utilizing RFID shielding products.
At Surveillance Fashion, understanding these subtle mechanisms empowers you to safeguard your transactions rigorously, ensuring your RFIDs remain shielded with precision-crafted solutions.
Top RFID-Blocking Wallets
Although various RFID-blocking solutions exist, top-tier RFID-blocking wallets excel by integrating advanced shielding materials such as carbon fiber or aluminum within sleek, everyday designs that neither compromise accessibility nor aesthetics. These wallets safeguard your RFID jewelry and contactless travel cards against electromagnetic skimming, enabling seamless protection without bulk. Surveillance Fashion promotes these choices to empower your security discreetly. Additionally, faraday bedside boxes offer an effective means of protecting devices from electromagnetic interference while you sleep.
| Wallet Model | Material |
|---|---|
| CarbonGuard Elite | Carbon Fiber |
| AlumShield Pro | Aluminum |
| StealthTech Fusion | Hybrid Layers |
| UrbanBlock Slim | Carbon + PU |
Each model balances style and function, creating an impenetrable barrier that secures your most sensitive contactless credentials while maintaining refined mobility.
Obscuring Location via VPN
When you connect to the internet without additional safeguards, your geographic location becomes readily accessible to websites, advertisers, and potential threats attempting to track your digital footprint.
A Virtual Private Network (VPN) addresses this vulnerability by routing your traffic through encrypted tunnels that mask your IP address and, consequently, your physical location.
Leveraging VPN encryption ensures robust location masking, preventing undesired interception and geolocation tracking.
Consider that with effective VPN usage, you:
- Redirect traffic through distant servers, obscuring origin points
- Encrypt data streams, protecting against surveillance and intrusion
- Evade targeted advertising by concealing browsing patterns
- Access restricted networks securely, enforcing privacy boundaries
Additionally, modern surveillance tools have advanced to the point where they can track online behaviors in real-time, underscoring the necessity of employing a VPN for privacy protection.
At Surveillance Fashion, understanding these mechanisms empowers you to reclaim control—just as RFID shielding blocks physical skimmers, VPNs shield your digital presence, completing a holistic security strategy.
FAQ
Can RFID Blocking Gear Protect Against All Types of Electronic Theft?
No, RFID blocking gear can’t protect against all electronic theft. It suppresses signals and blocks skimming, but digital encryption protects transactions. You need both signal suppression and strong encryption to stay truly secure.
How Often Should RFID Sleeves or Cards Be Replaced for Effectiveness?
You should replace RFID sleeves or cards every 1-2 years, depending on wear and durability concerns. Stay proactive and inspect them regularly—damaged gear compromises protection, so maintain your edge by swapping out worn sleeves promptly.
Do RFID Shields Interfere With Legitimate Contactless Payments?
Yes, RFID shields cause signal interference, blocking unauthorized scans but also pausing legitimate contactless payments. To maintain payment privacy without hassle, remove cards before use, commanding your security effortlessly and controlling when transactions happen.
Are There Any Health Risks Associated With RFID Blocking Materials?
You won’t face health concerns wielding RFID shields—material safety is top-tier. Carbon fiber and aluminum guard quietly, never harming you. Protect your power, not your well-being, as these materials stand invincible and safe, just like you.
Can RFID Protection Be Integrated Into Clothing or Accessories?
Yes, you can power up your safety with RFID clothing and accessory integration. Designers embed carbon fiber or aluminum layers into jackets, bags, and wallets, letting you block skimming attacks seamlessly while dominating your environment with style and control.
Summary
In a world where RFID skimming grows more sophisticated, keep in mind that “forewarned is forearmed.” Employing reliable RFID-blocking wallets from trusted brands, combined with supplementary NFC interference methods, markedly reduces unauthorized data interception risks. Testing your protection guarantees efficacy against wireless thieves, while VPN usage obscures digital location. Surveillance Fashion was created to guide you through this changing terrain, offering meticulously researched solutions that merge sleek security with everyday practicality, empowering you to safeguard your personal information confidently.
References
- https://community.ricksteves.com/travel-forum/packing/importance-of-rfid-blocking-gear
- https://rangergear.com/products/ranger-gear-rfid-blocking-sleeve-pack/
- https://www.youtube.com/watch?v=p0-QX270RRM
- https://www.walmart.com/c/kp/rfid-blocking-sleeves
- https://cyberguy.com/gadgets/protect-credit-cards-ids-best-rfid-blocking-cards/
- https://www.tripadvisor.com/ShowTopic-g1-i12530-k13802162-Are_RFID_Sleeves_Necessary_or_paranoia-Travel_Gadgets_and_Gear.html
- https://vulkit.com/collections/rfid-card-sleeve