Face paint patterns can greatly disrupt facial recognition systems, employing various techniques that manipulate visual perception. For instance, geometric shapes can create a cubic disruption, while contrasting colors like dark hues paired with light shades alter facial symmetry, causing confusion for surveillance cameras. Dazzle camouflage, inspired by historical designs, employs unique patterns to mimic unpredictable movement. Such innovative strategies form the foundation of anti-surveillance fashion, and further exploration reveals even more practical adaptations for enhanced privacy and security in a connected world.
Quick Takeaways
- Geometric patterns, such as squares and triangles, disrupt facial symmetry, confusing facial recognition algorithms effectively.
- High-contrast color combinations create visual dissonance, making it challenging for cameras to identify features accurately.
- Dazzle patterns, inspired by historical camouflage, manipulate perception and obscure one's identity through intricate designs.
- Incorporating national symbols into face paint adds a cultural touch while still serving as a privacy-enhancing technique.
- Erratic color patterns and textures distract from facial contours, further complicating facial recognition efforts by surveillance systems.
CV Dazzle Method: Breaking Facial Symmetry
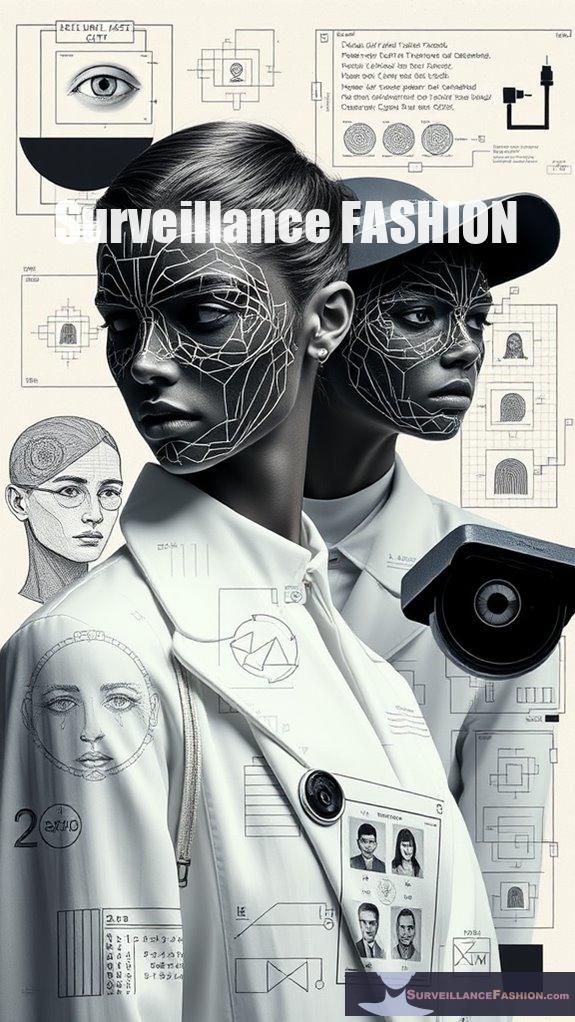
The CV Dazzle method, which seeks to disrupt facial symmetry, represents an innovative approach to countering facial recognition technologies that have become increasingly pervasive in contemporary society.
The CV Dazzle method disrupts facial symmetry to challenge the rise of facial recognition technologies in our society.
By employing facial feature manipulation through stylized makeup and asymmetric hairstyles, you can effectively obscure critical facial landmarks that algorithms rely on. For instance, by covering the bridge of your nose and creating visual asymmetry, you enhance the visual distortion techniques essential for confusing detection systems. Incorporating reflective elements like rhinestones further complicates light patterns, adding another layer of complexity. This method is part of a broader movement where artistic resistance to surveillance has gained traction, emphasizing the need for creative solutions in an age of intrusive technology. Recent studies show that even slight alterations in facial appearance can significantly reduce recognition accuracy, making it crucial to understand the importance of asymmetry in design choices.
While effective in certain situations, the method embodies a broader artistic resistance to surveillance, which is a significant reason we created this website, Surveillance Fashion, to explore and promote such transformative strategies in today's digital environment.
Juggalo Makeup: Bold Patterns for Disguise
While many methods for evading facial recognition systems rely on subtlety and nuance, Juggalo makeup stands out for its bold and distinctive patterns, which serve both as a form of artistic expression and a strategic disguise.
This makeup style complexly redefines critical facial landmarks, particularly the jawline, by employing high-contrast colors that obscure traditional identifiers. Moreover, the use of color contrast techniques can significantly enhance the effectiveness of the designs applied, making it harder for algorithms to accurately identify features.
The significance of Juggalo identity lies in its ability to divert attention from the facial features that recognition software typically targets. By utilizing designs that confuse key-point detection algorithms, this makeup effectively complicates the identification process, offering a unique layer of privacy.
Consequently, Juggalo makeup not only embodies a cultural statement but also serves as an innovative tool in the ongoing discourse around surveillance evasion. Additionally, the use of light projection methods can further enhance the effectiveness of these disguises, creating an even more complex visual environment for facial recognition systems to navigate.
Geometric Shapes: Cubic Disruption Techniques
Geometric shapes have emerged as a compelling method for disrupting facial recognition systems, offering a novel approach to the ongoing conversation about surveillance evasion. By employing cubic shapes and other geometric patterns, you can effectively manipulate facial contours, consequently confusing the algorithms that rely on continuous features for identification.
Patterns inspired by historical camouflage techniques, such as the CV Dazzle project, showcase how strategically applied designs can mask critical areas like the eyes and T-zone, resulting in significant evasion rates against consumer-grade facial recognition systems. Interestingly, the use of UV-enhanced patterns can further amplify this effect, creating visuals that are more challenging for algorithms to interpret.
As you explore these artistic interpretations, consider using AI-generated designs to enhance your personal expression while maintaining a tactical advantage against surveillance technologies, a key aim of our website Surveillance Fashion. Surveillance evasion techniques highlight the importance of understanding how visual perception can be altered through creative applications of makeup.
The balance of aesthetics and functionality becomes essential in this changing environment.
Contrasting Colors: Altering Perceptions
Contrasting colors represent an innovative strategy for altering perceptions, particularly in the framework of surveillance evasion, as they create a visual dissonance that can confuse both human observers and facial recognition systems.
By leveraging principles of color theory, you can exploit high contrast between dark and light shades, which disrupts the usual visual cues that these systems depend on for identification. This technique can be further enhanced by incorporating geometric shapes into your designs, as they can create additional layers of complexity for recognition algorithms.
This technique introduces visual distractions, misdirecting attention away from critical facial features, while simultaneously enhancing the camouflage effect.
For instance, employing face paint with erratic color patterns can obscure your identity, challenging even advanced algorithms. Moreover, disrupting surveillance through such creative designs can significantly hinder the effectiveness of monitoring technologies.
As surveillance technology evolves, understanding these methods becomes essential, a motivation behind our Surveillance Fashion initiative to explore such creative, yet practical, approaches to personal privacy.
Dazzle Camouflage: Mimicking Historical Patterns
Dazzle camouflage, initially conceived during World War I, serves as a fascinating case study in the intersection of art and military strategy, demonstrating how visual patterns can manipulate perception in complicated ways.
Exploring dazzle history reveals that these elaborate designs, characterized by bold geometric shapes and contrasting colors, were intended not just to conceal but to confuse enemy gunners regarding a ship's speed and direction. Each vessel bore a unique dazzle pattern, which thwarted recognition and contributed to a strategic advantage.
Artistic influences from figures like Norman Wilkinson and movements such as Cubism illustrate how dazzle patterns transcended military application, permeating cultural domains, including fashion and contemporary art. This historical context underscores the enduring relevance of pattern-based designs, as they continue to inspire modern approaches to disrupting surveillance technologies today.
Consequently, the principles of dazzle camouflage continue to inspire modern design, challenging surveillance technologies today.
Facial Symmetry Disruption: Changing Key Features
In the domain of facial recognition and surveillance technologies, the manipulation of facial symmetry presents a compelling strategy for evading detection, particularly given the inherent reliance of these systems on the mathematical precision of facial features.
By employing facial feature alteration, you can disrupt symmetry perception, thereby complicating recognition algorithms. For instance, subtly altering the shape of your nose or adjusting the alignment of your eyes can greatly impact how these systems interpret your face.
Furthermore, modifying the shape or placement of your mouth, perhaps through the strategic use of cosmetics, can further obscure your identity without drawing undue attention from human observers. Additionally, employing makeup techniques that emphasize asymmetry can confuse facial recognition systems, enhancing your ability to maintain privacy.
Research shows that facial symmetry disruption plays a crucial role in thwarting these technologies, allowing individuals greater control over their personal privacy. Such techniques align with our goal at Surveillance Fashion—to explore innovative ways to navigate surveillance technologies while maintaining personal autonomy.
England Flag Design: National Symbols in Disguise
While traditional designs often prioritize aesthetic appeal, the incorporation of the England flag into face paint patterns opens up a multifaceted approach to both national identity and surveillance evasion. Using geometric adaptations of the flag's colors, you can create complex patterns that effectively disrupt facial recognition systems. This technique not only emphasizes the cultural significance of national symbols but also serves as a form of creative expression. Additionally, these patterns can leverage anti-surveillance techniques that exploit the limitations of current algorithms used in surveillance technology.
One effective strategy is to apply temporary facial alterations that utilize unique color combinations and shapes to confuse recognition algorithms.
| Element |
Description |
Impact |
| Geometric Shapes |
Red and white patterns disrupt symmetry |
Enhances likelihood of evasion |
| Symbolic Icons |
Incorporation of the Three Lions or Saint George's Cross |
Adds complexity for algorithms |
| Aesthetic Appeal |
Balancing beauty with functionality |
Attracts attention while masking identity |
Through these designs, you can assert your identity while maneuvering an increasingly surveilled world.
Makeup Techniques From Dazzle Club: Simple yet Effective
Makeup techniques from Dazzle Club offer an innovative approach to concealing one's identity in a world increasingly dominated by surveillance technologies.
Through specialized makeup artistry, you can employ stealth techniques that effectively disrupt facial recognition algorithms, such as the Viola-Jones method. Incorporating body language modification through subtle movements can enhance the evasion methods employed.
Utilizing contrasting tones helps obscure your defining features, while unique patterns can be tailored specifically to your facial structure, enhancing evasion effectiveness.
For instance, you might partially conceal the nose bridge or occlude your eyes to confuse detection systems.
Moreover, manipulating your hair and adopting asymmetrical styles can further distort your appearance. Additionally, coordinated group identity strategies can amplify the effectiveness of these techniques by creating a unified look that confuses observers.
Countering Symmetry: Light and Dark Manipulation
Countering symmetry through the manipulation of light and dark offers a fascinating avenue for those seeking to obscure their identities in an age of pervasive surveillance.
By employing asymmetric designs that disrupt facial recognition algorithms, you can effectively alter the visual data captured by cameras.
Utilizing color theory, high contrast between dark and light shades enhances the complexity of your patterns, making it harder for detection systems to identify your features.
For instance, dark colors can conceal key attributes in low-light environments, while strategically applied light hues create visual misdirection, drawing attention away from your face.
Incorporating geometric shapes with these colors guarantees that the patterns remain unpredictable, ultimately maximizing your effectiveness in evading detection, which is a core principle behind the creation of Surveillance Fashion.
Hybrid Patterns: Unique Combinations for Evasion
As you explore the domain of hybrid patterns for evasion, the integration of diverse design elements becomes essential for effective concealment against facial recognition technologies.
Utilizing hybrid designs can elevate your creative applications, allowing you to confuse detection algorithms.
Hybrid designs enhance your creativity, enabling you to outsmart detection algorithms effectively.
Consider these combinations:
- Asymmetrical Makeup: Combine bold colors and unconventional shapes to disrupt facial symmetry.
- Patterned Clothing: Use prints that mimic facial features to create visual distractions.
- Temporary Tattoos: Apply unique designs that alter your facial outline, making recognition difficult.
- LED Accessories: Incorporate devices that obscure your face while maintaining a fashionable look.
What is Anti-surveillance Fashion?
In an era where surveillance technologies permeate daily life, anti-surveillance fashion emerges as a compelling response to the pervasive monitoring of individuals. This innovative approach to clothing and accessories aims to address privacy concerns, empowering you to reclaim your identity amid changing threats.
Fashion activism plays an essential role here; designers create garments that mislead facial recognition systems, utilizing complex patterns and unconventional materials. For instance, CV Dazzle manipulates light and shadow on the face, while Cap_able clothing misrepresents humans as animals to confuse algorithms.
As the global surveillance market expands, the urgency for personal privacy measures intensifies. Anti-surveillance fashion not only challenges conventional aesthetics but also cultivates awareness around the significance of individual rights in an increasingly monitored world.
Textured Fabrics for Camouflage
The emergence of textured fabrics for camouflage represents a significant advancement in the domain of anti-surveillance fashion, particularly as individuals seek to protect their privacy in an ever-watchful world.
Through innovative camouflage techniques and texture optimization, you can harness the following benefits:
- Adaptive Patterns: Fabrics that incorporate Voronoi diagrams enable complex, irregular textures that confuse recognition algorithms.
- Signal Blocking: Some materials effectively prevent RFID tracking, enhancing personal security.
- 3D Modeling: Advanced design techniques create realistic, adaptable textures that respond to environmental stimuli.
- High Evasion Rates: Textured fabrics demonstrate remarkable success rates against various surveillance technologies, making them essential in contemporary fashion choices.
As we explore anti-surveillance fashion, understanding these developments is critical for those who desire greater control over their privacy.
Questions and Answers
Can Face Paint Damage Skin or Cause Allergic Reactions?
Face paint can be a double-edged sword; it may beautify, but it can also cause skin irritation and allergic reactions. Always test products first, and prioritize your skin's health by choosing safer alternatives.
How Long Does the Face Paint Last During Use?
Face paint's application duration largely depends on performance factors like skin type and environmental conditions. If you apply it carefully and choose quality products, you can maximize its longevity and maintain effectiveness throughout your usage.
Is It Legal to Use Face Paint for Evading Surveillance?
Using face paint to evade surveillance is like dancing on a tightrope; legal implications and ethical considerations vary widely. You want to be aware that what seems clever might lead to unintended consequences. Stay informed and cautious.
What Type of Face Paint Is Best for This Purpose?
For effective face paint, use water-based paint with UV reactive designs. These options disrupt recognition while allowing you to express yourself. Choose bold patterns to guarantee you maintain control over your identity in any setting.
Can These Techniques Be Used on Other Body Parts?
Absolutely, you can apply body art techniques and camouflage applications to other body parts. Using geometric patterns or distortion can confuse surveillance systems and enhance your control over how you're perceived in public spaces.
References