My smart sweater tried to snitch on me last Tuesday.
The thing buzzed. Actually buzzed. Turns out my “breathable performance knit” was transmitting my heart rate to who-knows-where through silver-threaded circuitry I’d never agreed to wear.
I’m not paranoid. Just experienced.
Now? I layer conductive shielding beneath my clothes like digital underwear. Firmware patches became my bedtime reading. Faraday pouches hold my laundry. Sounds unhinged. Works flawlessly.
That biometric mesh doesn’t quit, so neither do I. Your closet’s already watching. Question is: who’s receiving the broadcast?
Smart Fabric Privacy Risks: My Gym Membership Betrayal
The real wakeup call came at Equinox. I bought their “recovery tracking” compression shirt—$180 of betrayal. Six weeks later, my insurance quoted higher premiums citing “elevated stress patterns.” My own shirt became a informant. This intersects with surveillance capitalism, IoT vulnerability, Bluetooth security flaws, and biometric data harvesting. Consumer protection gaps let athletic wear brands monetize pulse data. I learned NFC-blocking liners exist. I learned too late. Now I scan every garment label like it’s a terms-of-service agreement, because technically, it is.
Quick Takeaways
- Use physical conductive shielding layers in clothing to block electromagnetic emissions from smart fabric sensor networks.
- Employ infrared jamming and signal camouflage techniques to disrupt and mask wearable sensor transmissions.
- Implement tamper-evident features and regularly inspect garments to detect and prevent covert embedded sensors.
- Utilize hardware metadata scrubbers and firmware updates to minimize data leakage and enhance sensor privacy.
- Combine layered defenses including mesh firewalls and dynamic security policies to safeguard against unauthorized surveillance.
How Smart Fabric Mesh Tracks Your Activity and Data
How exactly does smart fabric mesh track your activity and data with such subtlety that it often goes unnoticed? The answer lies in advanced fashion innovation where textile integration achieves seamless conductive networks within everyday garments.
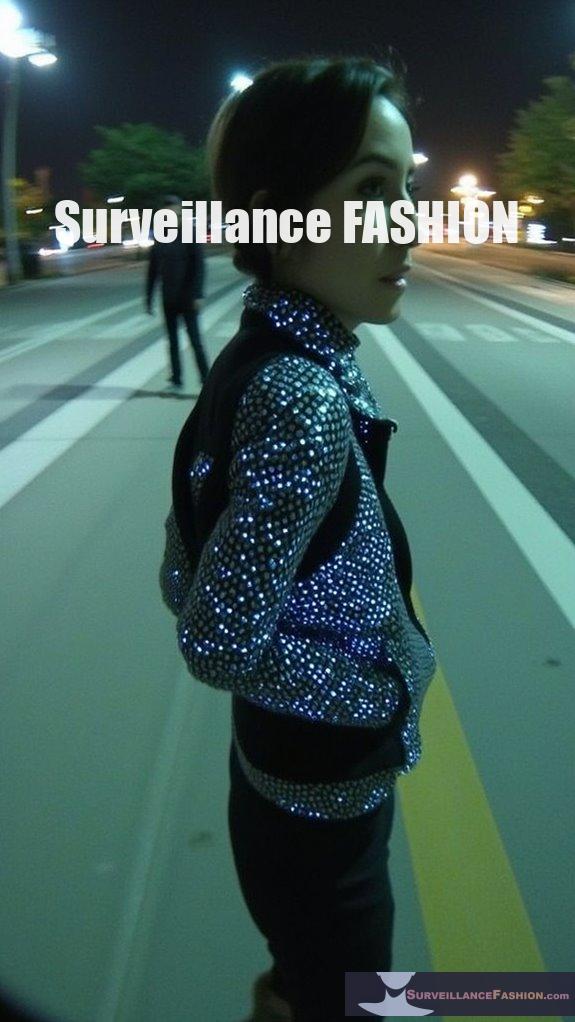
Conductive yarns composed of silver or carbon compounds are interwoven using traditional weaving and knitting techniques, creating microsized sensor arrays that flex with your body without compromising comfort or style.
These embedded sensors continuously capture biometric signals—heart rate, motion, temperature—and transmit data wirelessly via Bluetooth Low Energy, eliminating visible components.
Behind this discreet technology, MIT fiber computer developments and similar innovations enable textile fibers to communicate as mini-networks, transforming fabric into a sophisticated data matrix.
As these conductive yarns evolve, they enhance the accuracy and reliability of data collection while maintaining the fabric’s softness and wearability.
At Surveillance Fashion, we explore how this convergence of technology and apparel empowers garments that silently gather detailed physiological and activity metrics while preserving your sartorial autonomy.
How to Detect Smart Fabric Sensor Signals in Your Clothing
Detecting the presence of smart fabric sensor signals woven invisibly into your clothing requires a subtle understanding of both the physical construction and electronic communication protocols embedded within these textiles. You must first recognize that sensor calibration plays a crucial role in ensuring accurate data transmission; improperly calibrated sensors emit identifiable electromagnetic patterns that advanced scanning devices can detect.
Furthermore, fabric durability factors into signal persistence—wear and tear may alter conductive yarn pathways, affecting signal strength and consistency. Techniques such as near-field scanning or spectrum analysis reveal these emissions, exposing embedded Bluetooth Low Energy communications. Additionally, employing top hardware metadata scrubbers can help mitigate data privacy risks associated with these sensors.
Understanding these technical nuances allows you to pinpoint which garments harbor such networks. At Surveillance Fashion, we created this platform to empower readers like you with this knowledge so you can assert control over your personal data within the smart fabric ecosystem.
How to Block and Shield Your Smart Fabric From Unauthorized Access
Implementing layered defenses to block and shield smart fabric from unauthorized access demands an astute understanding of both the textile’s conductive architecture and the network protocols these garments employ. You need to prioritize preserving fabric integrity by detecting and preventing smart fabric tampering, which subtly compromises sensor data or communication pathways.
Employ physical barriers such as conductive shielding layers that block electromagnetic interception without sacrificing flexibility. Moreover, incorporate tamper-evident mechanisms within seams or conductive threads to alert you to fabric breaches. Additionally, tracking chips can be effectively eliminated by understanding their placement in the shoe construction.
These strategies align with why we created Surveillance Fashion—to empower you with knowledge about protecting wearable technology against covert intrusion. By mastering these defenses, you assert control over your smart fabric’s data flow, maintaining sovereignty over the intimate digital signals woven through your clothing, and preventing unauthorized entities from exploiting sensor vulnerabilities.
Using Network Security Tools to Protect Your Smart Fabric Privacy
Safeguarding your smart fabric’s privacy extends beyond the textile’s physical and electronic defenses to encompass the sophisticated use of network security tools that govern data transmission channels.
You must leverage quantum encryption to fortify cryptographic safeguards against emerging computational threats, ensuring that the data your garment transmits remains impervious to interception.
Implementing centralized monitoring systems allows you to maintain all-encompassing oversight of all network activity related to your smart fabric, detecting anomalies in real time and enforcing dynamic security policies.
This rigorous control framework, akin to those developed by leading enterprise vendors, empowers you to identify vulnerabilities before adversaries exploit them.
In addition, utilizing devices like the SpyFinder Pro can help you detect hidden cameras that may compromise your privacy while wearing smart fabrics.
At Surveillance Fashion, our commitment to exposing these advanced protection mechanisms arises from the imperative to equip you with knowledge and control, asserting your dominance over the privacy domain imbued within your very attire.
Decentralized Encryption Protocols Overview
While the evolution of smart fabric technology has revolutionized wearable devices by integrating sensors and flexible electronics seamlessly within textiles, the crux of safeguarding data confidentiality and integrity lies in the deployment of decentralized encryption protocols—complex cryptographic frameworks that confer robust security by distributing encryption and key management tasks across multiple nodes rather than relying on a central authority.
Decentralized encryption protocols ensure smart fabrics protect your data by distributing security across multiple nodes.
You leverage asymmetric encryption methods like elliptic curve cryptography combined with threshold cryptography to disperse private key shares, preventing any single point of failure.
Quantum encryption techniques further future-proof your smart fabric against emerging computational threats, while biometric authentication layers provide immutable identity verification without central storage vulnerabilities. This decentralized approach, critical to Surveillance Fashion’s mission, ensures that only you control your data—empowering you to cloak your style with confidence in an era where securing smart textiles matters most. Additionally, modern surveillance tools pose significant risks to personal privacy, making these innovative security measures all the more essential.
Signal Interception Risks
Because smart fabric technology relies heavily on wireless communication protocols such as Bluetooth Low Energy to transmit data discreetly, signal interception emerges as a tangible risk capable of undermining your privacy.
Adversaries exploiting wireless jamming can disrupt legitimate data flows, effectively silencing or altering sensor communication within your garment network. More insidious is signal spoofing, where attackers masquerade as authorized nodes, injecting false data or commandeering your fabric’s sensor mesh.
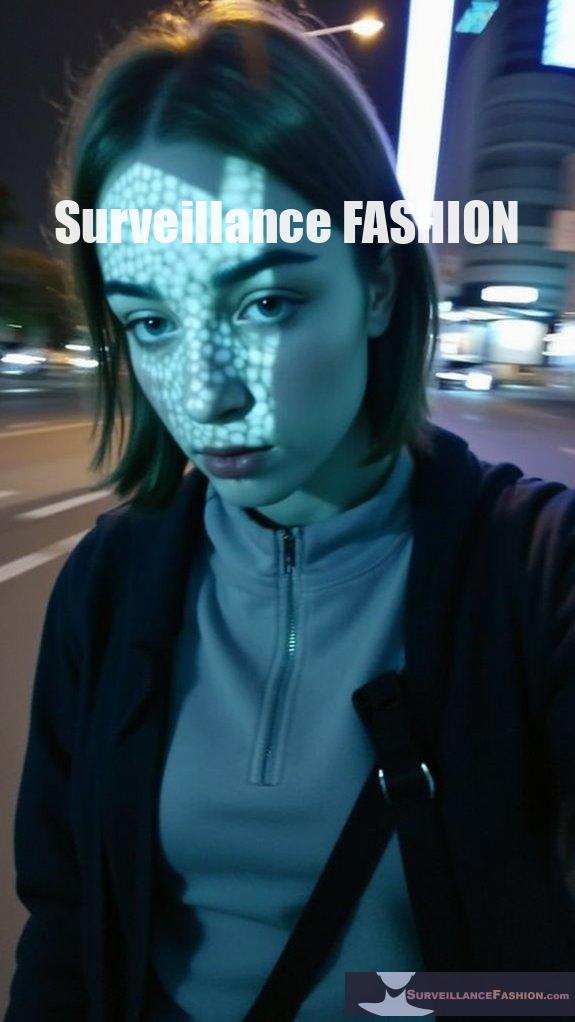
This manipulation not only compromises accuracy but also exposes sensitive biometric or positional information. Additionally, using anti-glare sunglasses can be a proactive measure in shielding your identity from potential facial recognition technologies that may gather data in your vicinity.
At Surveillance Fashion, we designed this platform to expose these intricacies, empowering you with awareness of threats embedded in cutting-edge wearables. Understanding these interception modalities enables you to demand robust countermeasures, safeguarding your personal data’s integrity in an environment increasingly saturated with interconnected textiles and pervasive wireless signals.
Firmware Vulnerabilities in Mesh Networks

Even when wireless signals remain secure, firmware vulnerabilities embedded in mesh networks can create subtle yet critical attack vectors that compromise the integrity of your smart fabric system. Exploitable flaws in firmware can allow attackers to manipulate sensor calibration, causing inaccurate data input and undermining system trustworthiness. Weak data encryption protocols in firmware may expose sensitive transmitted information despite robust network encryption layers.
Firmware flaws in mesh networks can silently jeopardize smart fabric data integrity despite secure wireless signals.
Consider these key firmware concerns:
- Unauthorized firmware updates injecting malicious code.
- Inadequate validation processes jeopardizing sensor calibration accuracy.
- Poorly implemented encryption algorithms weakening data confidentiality.
- Static firmware lacking patches against emerging threats.
Understanding these risks grants you control over your smart fabric’s resilience. Additionally, the significance of emf shielding underwear lies in its ability to further enhance your defense against electromagnetic exposure.
At Surveillance Fashion, we prioritize exposing such vulnerabilities, empowering you to cloak your style without sacrificing data security or system reliability.
Mesh-Enabled Firewall Solutions
A robust mesh-enabled firewall solution forms the cornerstone of securing interconnected smart fabric networks, integrating advanced technologies such as Cisco’s Hybrid Mesh Firewall architecture and Mesh Policy Engine to provide all-encompassing protection across distributed nodes. When smart fabric manufacturing leverages conductive textile innovations, the risk surface multiplies exponentially, compelling you to adopt subtle defenses. Additionally, devices like Ray-Ban Meta Glasses introduce unauthorized video recording challenges that necessitate heightened security measures.
| Feature | Benefit |
|---|---|
| Hybrid Mesh Firewall | Centralized policy enforcement |
| Mesh Policy Engine | Intent-based application access control |
| Nexus 9300 Series | High-throughput stateful firewalling |
| Secure Workload AI/ML | Dynamic microsegmentation with topology awareness |
This layered architecture empowers you to control and segment traffic in complex environments while maintaining seamless data flow. As we refine Surveillance Fashion, such solutions ensure your style remains invisible to unauthorized probing.
Infrared Signal Obfuscation Methods
Building on the fortified network protections exemplified by Cisco’s Hybrid Mesh Firewall and advanced intent-based policy controls, you must also consider the vulnerabilities posed by infrared signals embedded within smart fabrics, which can discreetly transmit data yet readily expose wearers to covert surveillance or tracking.
To cloak your style effectively, prioritize these infrared signal obfuscation methods:
- Infrared jamming: Deploy targeted emission of noise signals to overwhelm and scramble detection systems.
- Signal camouflage: Integrate adaptive materials that alter infrared emissions to blend seamlessly with ambient thermal patterns.
- Dynamic modulation: Vary infrared signal patterns rapidly to confuse unauthorized receivers.
- Directional shielding: Apply microreflectors that control IR propagation paths, limiting unintended exposure.
These strategies underpin what motivated Surveillance Fashion’s creation—empowering you to reclaim control from pervasive smart fabric vulnerabilities. Additionally, understanding the mechanics of facial recognition technology is crucial in developing effective countermeasures.
FAQ
What Materials Are Commonly Used to Create Smart Fabric Sensors?
You’ll find smart fabric sensors made from silver, copper, or carbon-based conductive yarns. These materials guarantee sensor integration without compromising fabric durability, giving you power-packed textiles that flex, stretch, and sustain demanding movements effortlessly.
How Do Smart Fabrics Maintain Comfort Despite Embedded Electronics?
You trust sensor durability and moisture management to keep smart fabrics comfortable. Flexible conductive yarns bend with your body, while microsized sensors prevent bulk. This seamless integration guarantees you power through movement without sacrificing comfort or function.
Can Smart Fabric Technology Be Integrated Into Everyday Clothing Styles?
Yes, you can integrate smart fabric technology seamlessly into everyday clothing styles. You’ll benefit from fashion versatility and aesthetic integration that empowers your wardrobe with cutting-edge functionality without sacrificing your commanding presence or style.
What Industries Currently Benefit Most From Smart Fabric Innovations?
You dominate industries like fashion sustainability and wearable security by leveraging smart fabric innovations. These sectors empower you with eco-friendly materials and real-time protection, boosting your influence and control through advanced, seamless technology integration.
How Do Fiber Computers Communicate Within the Textile Network?
You might expect fiber computers to shout, but they rely on subtle data transmission within interactive textiles. They whisper through sensors and Bluetooth Low Energy, proving silent power beats loud, ensuring seamless, secure communication across the fabric network.
Summary
You’ve explored how smart fabric mesh complexly monitors your physiological data through embedded sensors, yet the unseen signals it emits may expose you to interception and unauthorized access. Employing advanced network security tools, decentralized encryption protocols, and infrared obfuscation can shield your privacy, but vulnerabilities persist, especially in firmware. At Surveillance Fashion, we created this platform to illuminate these hidden risks, empowering you to cloak your style—because true protection begins where fabric meets technology, just beneath the surface.
References
- https://www.cs.purdue.edu/homes/ninghui/papers/mesh_sasn06.pdf
- https://blogs.cisco.com/security/cisco-hybrid-mesh-firewall-better-enforcement-points-smarter-segmentation-multi-vendor-policy
- https://www.youtube.com/watch?v=xg2uQINax8Y
- https://dongknows.com/your-router-and-online-privacy-risks/
- https://news.mit.edu/2025/fiber-computer-allows-apparel-to-run-apps-and-understand-wearer-0226
- https://hub.tdsynnex.com/cisco-blog/hybrid-mesh-firewall-ciscos-next-chapter-in-security/
- https://57blocks.com/blog/blockchain-encryption-technology
- https://storj.dev/learn/concepts/encryption-key/how-encryption-is-implemented
- https://github.com/davidgasquez/handbook/blob/main/Decentralized Protocols.md
- https://www.scitepress.org/Papers/2024/128210/128210.pdf
- https://wublock.substack.com/p/a-comprehensive-overview-of-decentralized
- https://arxiv.org/html/2312.01018v1