Wearable technology blocks your personal data signals primarily through advanced techniques such as signal jamming, encryption protocols, and software obfuscation. These measures create formidable barriers against unauthorized data interception, effectively addressing concerns like the staggering 96% re-identification risk associated with biometric signals. By disguising or disrupting these signals, wearables enhance your privacy and security in a data-driven world. As you explore further, you’ll uncover additional understandings into the developing terrain of personal data protection.
Quick Takeaways
- Wearable tech employs signal obfuscation techniques to prevent unauthorized access to personal data signals.
- Jamming technologies mask genuine signals, enhancing privacy during data transmission.
- Signal-blocking fabrics in accessories disrupt data interception by creating interference.
- Encryption protocols and software obfuscation secure data against potential threats and unauthorized access.
- Physical access controls are implemented to prevent data compromise and safeguard user information.
What Are Biometric Data Scrambling Fashion Accessories?
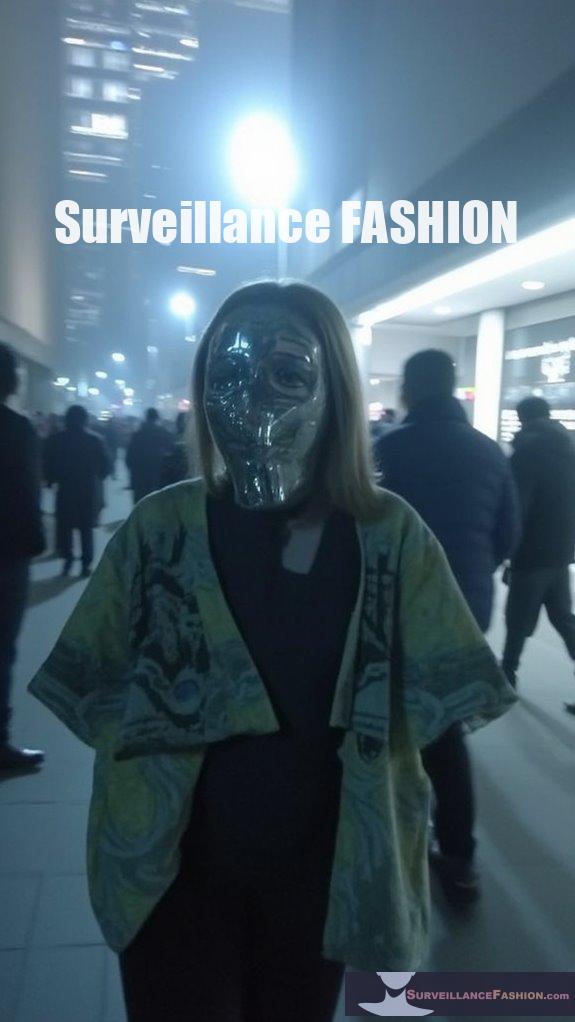
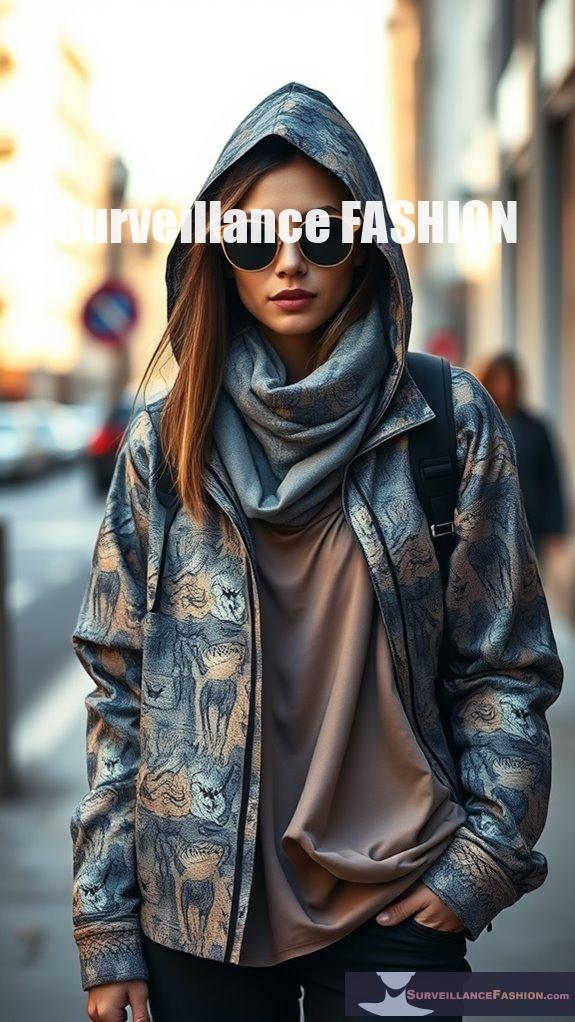
Biometric data scrambling fashion accessories combine fashion with technology to protect individuals’ biometric data from unauthorized capture by surveillance systems. These innovative designs not only enhance personal security but also promote stylish solutions that allow wearers to express their individuality. These items use adversarial designs and encryption methods to mislead facial recognition algorithms, enabling individuals to better control their personal data exposure. Biometric data encryption enhances security in wearable technology, making these accessories even more effective at safeguarding information. These accessories include garments and items like clothing with misleading patterns, reflective fabrics, and face masks.
They act as a proactive solution against surveillance by:
- Confusing AI algorithms with adversarial designs.
- Obscuring biometric signals with reflective materials.
- Protecting data with advanced encryption technology.
Ultimately, they empower wearers to maintain privacy in increasingly monitored environments.
How Do Wearable Technologies Block Personal Data Signals?
Wearable technologies block personal data signals through various methods such as signal obfuscation, jamming technologies, and on-device encryption.
These techniques protect against unauthorized access and data interception, ensuring user privacy. Wearables may actively block or scramble wireless signals like Bluetooth and Wi-Fi to prevent data sniffing. In light of the growing consumer engagement in health management through wearable tech, techniques include:
- Radio frequency (RF) jammers: These devices create interference to mask genuine signals.
- Signal-blocking fabrics: Fashion accessories can be embedded with materials that dampen or reflect radio waves.
- Software obfuscation: Random or fake data streams can be transmitted alongside genuine data to confuse potential interceptors.
Why Is Personal Biometric Data Vulnerable to Re-Identification?
Given the distinctiveness of biometric signals, such as those derived from wrist-worn accelerometers or ECG readings, re-identification risks can be astoundingly high. Machine learning algorithms can effectively detect subtle patterns, facilitating the re-linking of anonymized data to individual identities. Additionally, simply removing personal identifiers from biometric datasets is insufficient, especially when additional data or identifiers are accessible, allowing for correlations. Key contributing factors include:
- High uniqueness of biometric signals across individuals.
- The advanced capability of machine learning to discern patterns.
- Insufficient traditional methods of de-identification failing to protect sensitive information.
- Regulatory frameworks struggling to keep pace with technological advancements and risks. Moreover, studies have indicated that sharing a full day’s worth of wrist-worn accelerometer data results in an astonishing average re-identification risk of 96%.
What Types of Biometric Data Do Wearables Typically Collect?
Wearable technology typically collects various types of biometric data, including physiological measurements like heart rate and blood oxygen levels, physical activity metrics such as step counts, and behavioral indicators encompassing motion patterns and sleep quality.
These measurements enable users to monitor their health and fitness levels effectively. Key data types include:
- Heart rate and respiratory rate for essential sign tracking.
- Blood pressure and glucose levels for chronic condition management.
- Sleep patterns for evaluating rest and recovery.
- Movement and posture data to improve overall physical health.
Wearables also capture advanced biometric signals, like GPS for activity tracking and behavioral patterns for user customization.
This ongoing data collection supports personalized health feedback and decision-making in everyday life.
How Can Personal Data Collected by Wearables Be Misused?

Personal data collected by wearables can be misused for unauthorized data access, commercial exploitation, discrimination by insurers or employers, and violation of user privacy. These practices can lead to increased insurance premiums, employment bias, and unauthorized third-party data sharing.
Wearable devices often gather more data than necessary, including sensitive health information, location, and user behavior. This data is frequently shared without explicit user consent, making it vulnerable to cyber-attacks and exploitation in lucrative markets.
Key concerns include:
- Insurance companies evaluating risk based on wearables data.
- Employers using health data to influence hiring decisions.
- Third-party sharing that lacks transparency.
- Dense privacy policies leading to uninformed consent.
Such risks underscore the need for stricter regulations and clearer user protections in wearable tech data handling.
What Are the Legal Regulations Governing Wearable Tech and Personal Data?
Wearable tech and personal data are governed by a mix of federal and state laws in the U.S. and stringent regulations in the EU, focusing on privacy, consent, and data protection. Key frameworks include the FTC’s enforcement in the U.S., and the GDPR and EHDS in the EU.
In the U.S., federal laws like the FTC’s guarantee that data practices aren’t unfair or deceptive.
The Americans with Disabilities Act (ADA) further restricts the use of medical information derived from wearables in employment, emphasizing security in data storage. Recently, states like Colorado and California have enacted specific laws governing neural data privacy, with more states considering similar regulations.
In the EU, the General Data Protection Regulation (GDPR) sets strong standards for consent and user rights related to personal data, while the new European Health Data Space (EHDS) Regulation aims to harmonize health data usage, including data from wearables.
The Data Act complements these regulations by promoting secure, privacy-compliant data sharing within member states, addressing various privacy challenges associated with wearable tech.
How Does Informed Consent Play a Role in Wearable Data Collection?
Informed consent is essential in wearable data collection as it guarantees users understand what data is being collected, how it’s used, and their rights regarding that data. It supports user autonomy and privacy in a legal and ethical framework.
Effective informed consent in wearable technology requires transparent communication about several key areas. Users must be clearly informed about:
- Types of data collected, such as health metrics and personal information.
- The specific usage of this data, including potential sharing with third parties.
- Data security measures and the associated risks.
- Users’ rights, including how to withdraw consent or stop data collection.
Achieving meaningful informed consent is complicated by factors such as the technical complexity of devices, passive data collection practices, and potential power imbalances in workplace settings.
These challenges call for best practices that prioritize user understanding and control over their data.
What Features Do Surveillance Blocking Wearables Typically Include?
Surveillance blocking wearables typically include features such as encryption protocols, biometric authentication, and automatic logout functionalities to protect user data and privacy.
Furthermore, they may employ real-time threat detection systems and anonymization techniques to prevent unauthorized access and maintain compliance with data protection regulations.
These wearables often utilize advanced technology to mitigate risks associated with data breaches and surveillance.
Key features encompass:
- Multi-factor authentication to restrict access.
- Panic buttons or hidden alarms for rapid emergency alerts.
- Continuous monitoring of health metrics to guarantee user safety.
- Integration with geofencing and GPS for location privacy.
How Do Reflective Fabrics Work to Protect Biometric Data?

Reflective fabrics protect biometric data by utilizing metallic or coated fibers that reflect incoming light and thermal emissions, disrupting sensors and cameras.
These materials create misleading visual and heat patterns, effectively concealing facial and body biometrics from surveillance systems.
These multi-functional fabrics are engineered to scatter both visible and infrared light, confusing biometric recognition systems. They mask features necessary for facial identification and obscure temperature signatures valuable for thermal imaging.
Key benefits include:
- Disruption of light signals for iris and vein recognition.
- Reduction of signal clarity from environmental biometric scanners.
- Ability to prevent accurate facial landmark detection in AI systems.
While effective, challenges remain in balancing comfort, durability, and performance under various conditions, necessitating advanced manufacturing techniques.
What Are the Ethical Considerations Surrounding Biometric Scrambling Technologies?
Biometric scrambling technologies raise ethical concerns about informed consent, privacy violations, and equitable access.
It’s essential to develop transparent policies, empower users with control over their data, and guarantee inclusive design to prevent discrimination and mistrust.
The deployment of these technologies must consider various ethical dimensions.
Key considerations include:
- Guaranteeing users understand data collection and scrambling processes.
- Balancing privacy rights with security needs, particularly in law enforcement.
- Providing equitable access to vulnerable groups to avoid exacerbating existing inequalities.
- Maintaining transparency about how scrambling works and its limitations to foster accountability and user trust.
How Can Fashion Accessories Aid in Preventing Unauthorized Data Collection?
Fashion accessories equipped with RFID-blocking technology and EMF shielding materials can prevent unauthorized data collection by safeguarding sensitive information stored in devices like credit cards and passports.
These accessories use innovative materials such as conductive fibers and advanced coatings to create a protective barrier against electronic threats.
Here are key features:
- RFID-Blocking: Prevents scanning of embedded chips, protecting personal information.
- EMF Shielding: Reduces exposure to harmful electromagnetic radiation.
- Anti-Surveillance: Disrupts facial recognition, enhancing anonymity.
- Functionality and Style: Stylish designs meet contemporary privacy needs without sacrificing aesthetics.
This combination enhances safety while aligning with modern privacy concerns.
What Impact Do Surveillance Blocking Wearables Have on User Privacy?
Surveillance blocking wearables enhance user privacy by reducing the risk of unauthorized data collection and limiting third-party access to sensitive personal information.
These technologies empower users to regain control over their data and mitigate the pervasive surveillance inherent in many wearable devices.
As wearables capable of blocking surveillance emerge, they challenge established norms of data collection and sharing. Users can enjoy increased autonomy by:
- Preventing unauthorized tracking and monitoring.
- Ensuring data flows remain more private and secure.
- Encouraging a shift toward ethical data practices and transparency.
These devices contribute to a more equitable environment, where the balance of power shifts back to users, allowing for better protection against potential privacy infringements.
How Can Users Educate Themselves About Wearable Data Privacy?

To educate themselves about wearable data privacy, users should review privacy policies, stay informed on relevant legislation, and consult independent resources on data protection strategies.
Individuals can enhance their understanding of wearable data privacy through several avenues. First, carefully scrutinizing official privacy policies and terms of service can reveal critical information about data practices. Users should also keep current with laws like GDPR, HIPAA, and COPPA that impact data usage, ensuring they know their rights.
Additionally, engaging with resources from consumer advocacy groups or technology literacy programs can provide practical knowledge. These may include:
- Understanding ethical data practices.
- Recognizing red flags in consent agreements.
- Attending workshops focused on digital health ethics.
What Role Do Third-Party Apps Play in Wearable Data Access?
Third-party apps serve as essential facilitators for wearable data access by enabling synchronization of biometric, activity, and lifestyle data through API integrations. These integrations enhance functionality, allowing users to sync information with external platforms while streamlining app development.
Through these integrations, wearables communicate using protocols like HTTP and data formats such as JSON and XML. Key shared data includes:
- Biometric data (e.g., heart rate, oxygen levels)
- Location information (e.g., GPS tracking)
- Lifestyle metrics (e.g., step counts, diet logs)
- Health indicators (e.g., menstrual cycle tracking)
As a result, third-party apps considerably increase the utility and personalization options available to wearable users.
However, they also raise privacy and security concerns, as users may remain unaware of the extent of data sharing and the potential risks involved.
How Do Employers Ensure Compliance With Nondiscrimination Laws Regarding Wearable Data?
Employers guarantee compliance with nondiscrimination laws regarding wearable data by adhering to Equal Employment Opportunity (EEO) standards, maintaining confidentiality, and implementing reasonable accommodations for employees.
They must also validate the accuracy of wearable data to prevent biased employment decisions.
To achieve compliance, employers must:
- Avoid making employment decisions based on wearable data that infer protected characteristics.
- Keep medical data confidential and limit access to authorized personnel only.
- Consider individual accommodation requests for employees facing conflicts with wearable tech.
- Assess the accuracy of data across diverse populations to mitigate discriminatory outcomes.
Documentation and regular audits of wearable data practices are also essential for compliance.
What Innovations Are Emerging in Biometric Scrambling Technologies?
Innovations in biometric scrambling technologies involve hybrid systems that utilize multiple biometric identifiers, data fusion methods to obscure signals, and dynamic switching between modalities, greatly enhancing user privacy and security.
These technologies enhance security by combining biometric traits like facial recognition and fingerprints into composite authentication signals. They utilize data fusion techniques to scramble individual signals during transmission, making it difficult for adversaries to intercept identifiable traits.
Key features include:
- Dynamic switching between biometric modalities.
- Reduction of false acceptances through cross-verification.
- Adaptive algorithms that continuously learn and modify behavioral patterns.
- Wearables that can mask or jam biometric readings from sensors.
These advancements aim to establish more secure, user-friendly authentication solutions while addressing privacy concerns.
How Does Data Collection by Wearables Differ in Public vs. Private Spaces?

Data collection by wearables noticeably differs in public and private spaces, with private spaces focusing on intimate health metrics and public spaces collecting broader data like location and social interactions.
This divergence raises distinct privacy and ethical concerns, influenced by user consent, situational risks, and socioeconomic factors.
In private spaces, wearables track sensitive health information, such as heart rate and sleep patterns, where users may have greater control over their data.
However, in public spaces, data can be aggregated, shared, and used without explicit user understanding, leading to surveillance and profiling risks.
Key differences include:
- Data sensitivity: Private data is often health-related, while public data involves location and interactions.
- Consent mechanisms: Public and private data collection lacks differentiation, complicating user permissions.
- Transparency: Data sharing practices are often opaque, increasing risks in public environments.
These factors particularly affect marginalized communities, highlighting the urgent need for improved privacy frameworks.
What Are Common Misconceptions About Biometric Data Privacy?
Biometric data privacy is often misunderstood, with concerns about raw data storage, vulnerability to breaches, and invasive use. However, modern systems utilize encrypted templates, prioritize user consent, and implement robust security measures.
Current biometric technologies work with mathematically abstracted biometric templates rather than raw images, enhancing privacy by preventing the reconstruction of original data. These templates, when stored, are encrypted and anonymized to safeguard personal identity.
Key points include:
- Biometric systems don’t collect personal behavior data.
- Encryption and strong security protocols typically protect biometric data.
- Advances in technology have mitigated many concerns about accuracy and spoofing.
- Permanent storage of biometric data is discouraged and regulated for compliance.
How Does Interference With Data-Capturing Signals Protect Users?
Signal jamming and disruption techniques are vital in safeguarding wearable technologies. By preventing unauthorized access and ensuring that only legitimate connections are established, users can maintain privacy.
Key protection methods include:
- Denial of Service (DoS) attacks prevent unwanted device connections.
- Signal interference disrupts communication, minimizing risks of interception.
- Blocking device MAC addresses protects against tracking.
These techniques work in conjunction with encryption protocols, filtering practices, and physical access controls to create a multi-layered defense against data compromise.
What Is the Future of Wearable Tech and Personal Data Privacy?
The future of wearable tech and personal data privacy is increasingly focused on compliance, enhanced data protection technologies, and consumer-driven privacy demands.
As regulations evolve, manufacturers must adopt innovative privacy-enhancing technologies and robust security measures to guarantee user trust and data protection.
To thrive in this rapidly changing environment, companies will need to prioritize:
- Adherence to diverse regulations, such as GDPR and HIPAA.
- Implementation of privacy-enhancing technologies like homomorphic encryption and federated learning.
- Adoption of advanced data security methods, including blockchain and biometric authentication.
- Commitment to transparency and user control over personal data.
The intersection of compliance, technology, and consumer expectations will shape the wearable tech industry, ensuring that privacy remains paramount.
Biometric Data Scrambling Fashion Accessories
As consumers grow increasingly aware of their digital footprints, the fashion accessory market has responded by integrating innovative technologies designed to shield personal biometric data from prying eyes.
These biometric accessories impact how we navigate privacy in a digital age, showcasing the developing fashion trends.
Imagine wearing gloves with absorptive nano-coatings that disrupt iris scanners or rings embedded with low-power jammers that obstruct data harvesting. Each accessory serves as a barrier against unauthorized scans, reinforcing your data sovereignty.
In a world where tracking is rampant, incorporating these designs into your wardrobe isn’t just a style choice; it’s an assertion of control over your private information.
Anti Surveillance Ebook review: Eyes Everywhere
While exploring today’s elaborately crafted environment of personal data collection, you may find yourself reflecting on the pervasive nature of surveillance as detailed in the ebook “Eyes Everywhere.”
This thorough analysis illuminates the alarming integration of government and corporate networks that harvest a wide range of personal communications, including phone calls, emails, and even movements tracked by cameras positioned in public and private spaces.
Through its examination, the book encourages surveillance resistance practices, urging the adoption of privacy technologies to reclaim autonomy in an increasingly monitored world.
Ultimately, it invites deeper reflection on our personal data and the unseen forces at play.
References
- https://pmc.ncbi.nlm.nih.gov/articles/PMC10040444/
- https://sites.suffolk.edu/jhbl/2024/04/16/competitive-health-the-heart-data-wars-and-their-legal-implications-for-tomorrows-wearable-technology-and-health-data/
- https://www.aad.org/public/fad/digital-health/wearable-devices
- https://www.goldbergsegalla.com/news-and-knowledge/knowledge/eeoc-avoid-bias-with-wearable-tech-in-the-workplace/
- https://www.cyberpeace.org/resources/blogs/wearable-tech-navigating-privacy-compliance-and-misinformation
- https://www.venuez.dk/biometric-data-encryption-in-smart-clothing-for-security/
- https://www.lefashionpost.com/2025/07/15/how-biometric-fashion-is-revolutionizing-your-style-experience/
- https://vtechworks.lib.vt.edu/items/5db7be2c-9042-4b04-9c56-d49b35502110
- https://www.stratecta.exchange/fashion-that-can-beat-facial-recognition-systems/
- https://blog.richardvanhooijdonk.com/en/the-fashion-industry-is-leading-the-fight-against-facial-recognition-technology/
- https://news.mobar.org/every-breath-you-take-data-privacy-and-your-wearable-fitness-device/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC7884134/
- https://www.bitdefender.com/en-gb/blog/hotforsecurity/five-steps-to-protect-your-privacy-on-wearable-devices
- https://www.halllawgroup.com/love-your-wearable-technology-know-what-youre-sharing/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC9988376/
- https://arxiv.org/html/2408.10228v1
- https://www.ftc.gov/news-events/news/press-releases/2023/05/ftc-warns-about-misuses-biometric-information-harm-consumers
- https://www.nature.com/articles/s41598-022-19045-3
- https://pmc.ncbi.nlm.nih.gov/articles/PMC11165804/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC12167361/