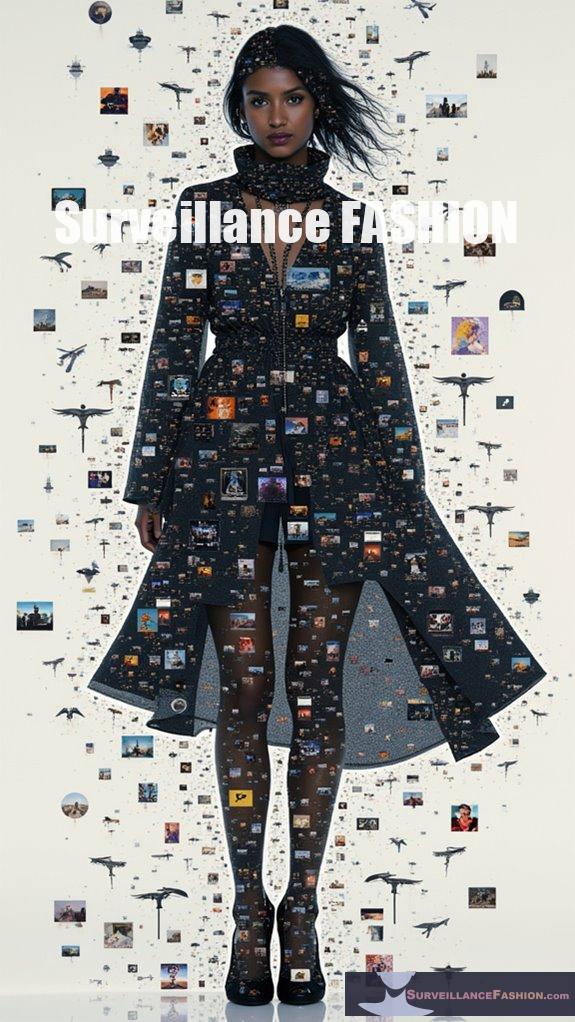
To evade facial recognition, you can employ clothing patterns specifically designed to disrupt algorithms. Adversarial pattern prints create misleading visual cues, while multi-pattern and high-contrast designs obscure facial landmarks effectively. Moreover, utilizing reflective materials and asymmetry disturbs recognition systems. Makeup techniques further enhance your disguise by altering key facial features. These strategies combine to decrease recognition accuracy greatly, ensuring greater anonymity. As you explore further, you’ll uncover more about the fascinating intersection of fashion and surveillance technology.
Quick Takeaways
- Evasive clothing patterns, such as adversarial prints and multi-pattern designs, disrupt facial recognition algorithms by obscuring key facial landmarks.
- Reflective and light-disruptive materials mask thermal signatures and create visual noise, complicating recognition by cameras.
- Makeup techniques and accessories can obscure facial features, further reducing the accuracy of facial recognition systems.
- Variability across algorithms means specific evasive designs can target and confuse different facial recognition methods effectively.
- Combining innovative patterns with materials like retroreflective fabrics enhances anonymity and challenges surveillance technologies.
What Are Adversarial Pattern Prints and How Do They Work?

Adversarial pattern prints are designed to mislead facial recognition (FR) systems by introducing subtle perturbations that are often invisible to humans. They disrupt key feature extraction processes, resulting in misclassification or failure to recognize individuals wearing them. These prints can be applied as accessories or projected onto surfaces, effectively altering localized pixel values to confuse FR algorithms. They optimize perturbations using techniques like Generative Adversarial Networks (GANs) to maximize effectiveness. In fact, significant market growth for facial recognition technology is projected, which indicates an urgent need for countermeasures against such adversarial attacks. Additionally, fashion forward styles are becoming an essential part of the discourse surrounding personal privacy and surveillance.
Key points include:
- Localized Impact: Unlike full-image adversarial examples, these patterns focus on specific areas, making them suitable for practical applications like clothing.
- High Success Rates: Physical implementations have shown over 80% success in dodging recognition and around 64% in impersonation scenarios.
- Stealth Factor: Designs as inconspicuous accessories enhance the threat level due to low detectability by humans.
- Dynamic Projections: Techniques such as light projections can evade detection methods aimed at static artifacts, increasing the risk posed by these attacks.
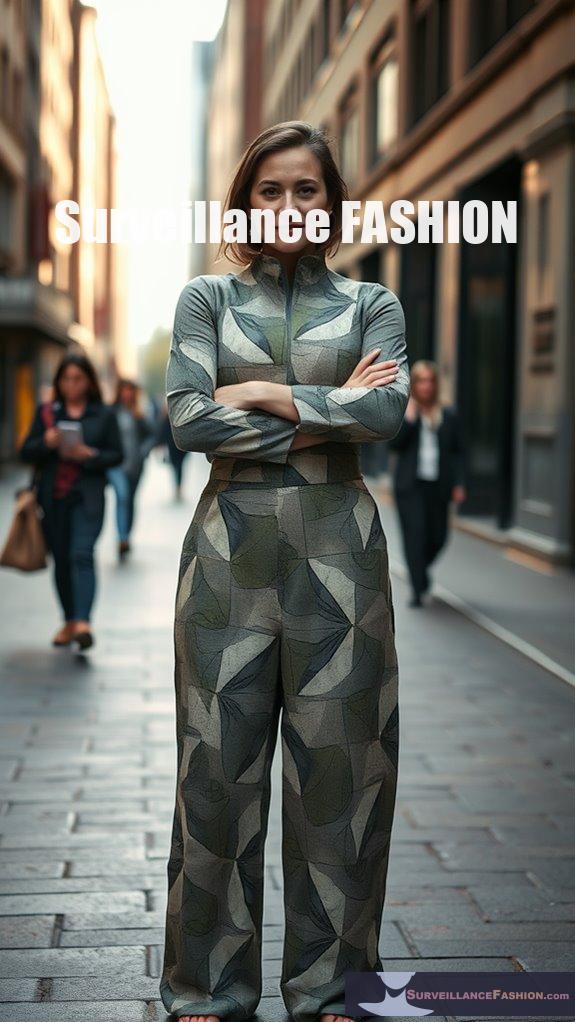
How Do Multi-Pattern and High-Contrast Designs Confuse Facial Recognition Algorithms?
Multi-pattern and high-contrast designs obscure facial landmarks, greatly confusing facial recognition algorithms. These chaotic patterns create visual noise that disrupts image segmentation, leading to reduced accuracy and increased false identifications.
The complexity of multi-pattern designs includes scrambled shapes and contrasting colors that challenge algorithmic interpretation. Key facial features like eyes, nose, and mouth become masked, while high-contrast elements amplify image noise.
This disruption undermines stable landmark detection essential for accurate facial recognition. The result is a marked drop in match accuracy, rendering algorithms highly susceptible to misidentification.
Key points:
- Patterns can lower match accuracy by 60-90%.
- High-contrast elements interfere with image segmentation.
- Algorithms struggle with chaotic patterns that deviate from expected facial symmetry.
- Misleading features can mimic human traits in incorrect locations.
Moreover, these designs can be enhanced with infrared-reflecting materials that further impede facial recognition efforts.
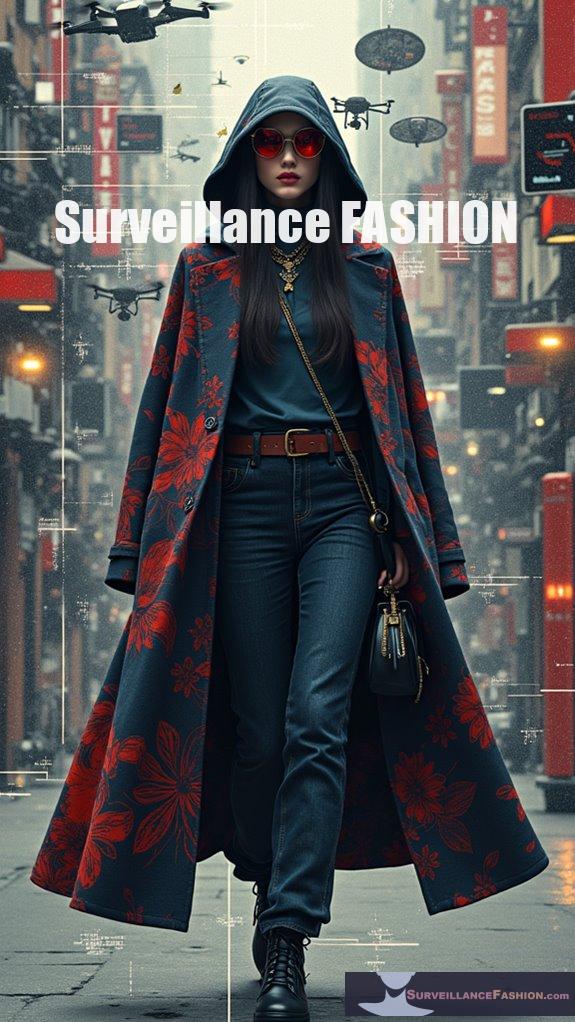
What Types of Reflective or Light-Disruptive Materials Enhance Clothing’s Evasion Capabilities?
Reflective and light-disruptive materials that enhance clothing’s evasion capabilities include lightweight metallic fabrics, infrared (IR) light-emitting materials, infrared-blocking eyewear, retroreflective fabrics, and reflective masks.
These materials effectively mask thermal signatures and distort sensor detections.
Lightweight metallic fabrics reflect body heat, helping to conceal thermal signatures from surveillance technologies. Meanwhile, IR light-emitting materials can actively disrupt night vision cameras by flooding them with calibrated infrared pulses, rendering facial features indistinguishable.
Specialized eyewear, featuring infrared-blocking lenses and reflective frames, prevents the collection of biometric data around the eyes, further enhancing anonymity.
Retroreflective fabrics can overwhelm camera sensors by bouncing flash photography light back, creating glare that obscures facial features.
Finally, reflective masks scatter visible and IR light, complicating facial recognition capture.
Together, these materials provide an extensive approach to evading facial recognition systems while maintaining a stylish appearance.
In What Ways Does Asymmetry and Shape Distortion Affect Facial Recognition Accuracy?

Asymmetry and shape distortion greatly reduce facial recognition accuracy by disrupting both spatial symmetry and geometric fidelity, leading to misclassification and decreased detection probabilities.
Facial recognition systems rely on consistent bilateral structure for accurate identification. When asymmetry is introduced—such as through facial expressions or intentional modifications—algorithms struggle to match key landmarks like the eyes, nose, and mouth.
Furthermore, shape distortions alter facial contours, further complicating recognition processes. Key impacts include:
- Reduced matching confidence for distorted inputs.
- Dramatic drops in verification success rates for altered faces.
- Combined distortions leading to cumulative recognition failures.
Ultimately, these factors render detection systems less effective, with accuracy plummeting when both asymmetry and distortion are present.
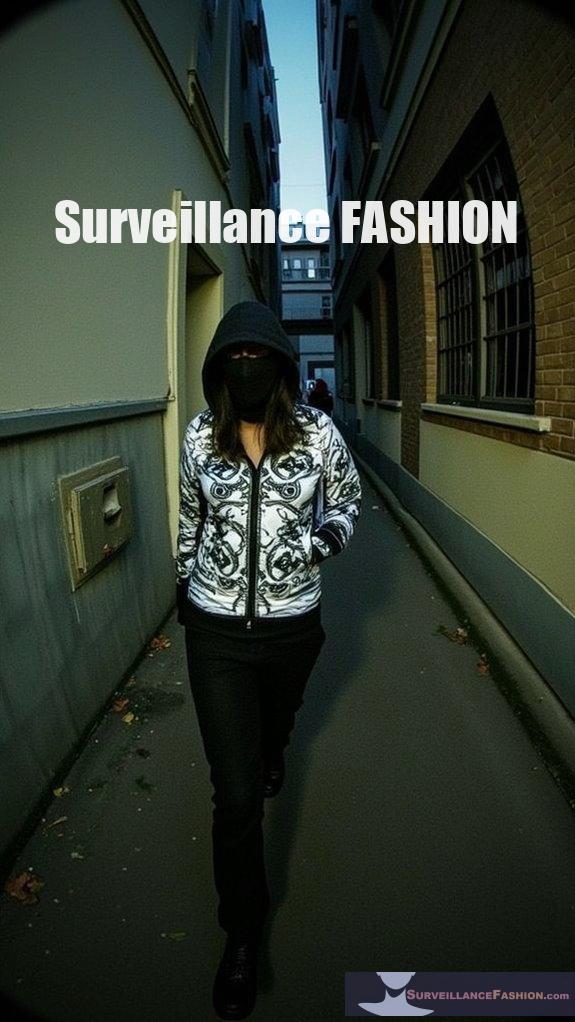
How Can Makeup and Face Paintings Complement Evasive Clothing Strategies?
Makeup and face paint can notably enhance evasive clothing strategies by strategically disrupting key facial recognition points, making it difficult for algorithms to identify individuals. The combination of targeted cosmetic techniques and complementary clothing patterns creates layered visual noise that masks the face and confuses detection systems.
By applying subtle darkening or lightening around facial features, makeup can lower recognition rates dramatically. This is particularly effective when used alongside clothing with asymmetrical or high-contrast patterns that visually interfere with the overall silhouette, such as the neck and jawline.
- Key benefits include:
- Targeted makeup reduces identification accuracy.
- Face paint masks critical features, creating “fictional fingerprints.”
- Clothing patterns enhance visual obfuscation.
- Combined techniques maintain a natural appearance, avoiding suspicion.
This synergy enables individuals to achieve plausible anonymity while retaining human likeness in everyday settings.
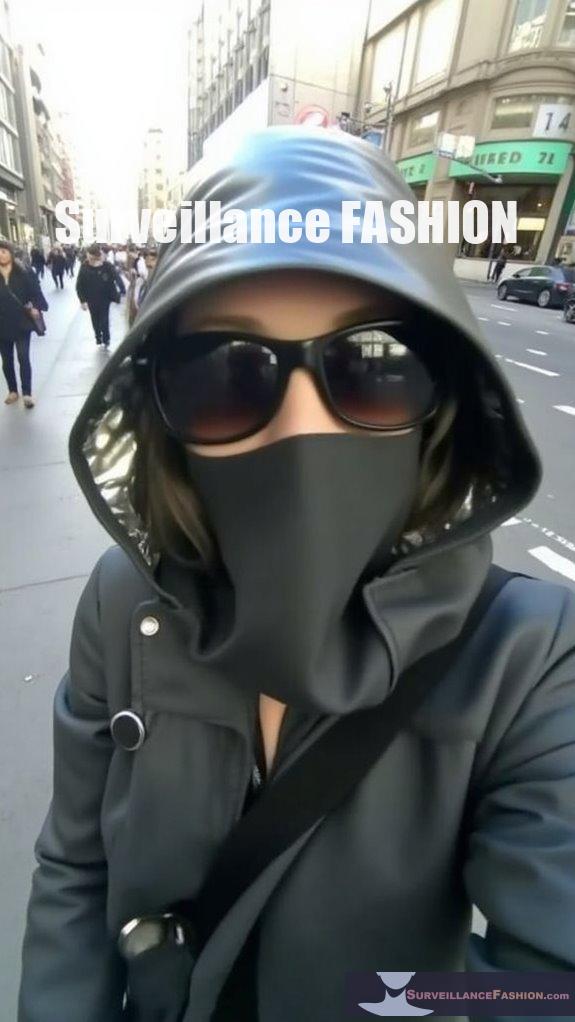
What Role Do Masks and Accessories Play in Evading Facial Recognition?
Masks and accessories can hinder facial recognition by obscuring key facial features; however, their effectiveness varies greatly depending on the recognition system used.
While certain patterns and items can partially disrupt identification, they often don’t guarantee complete evasion due to the advancements in recognition technology.
Masks primarily cover the lower face, leaving the eyes and upper portions visible, which many algorithms still analyze.
Research shows that while specially designed masks with disruptive patterns can confuse some systems, the range of facial recognition models makes their effectiveness uncertain.
Accessories like sunglasses and hats can further obscure facial features, but their impact also depends on how the recognition system focuses on specific areas.
Key points to take into account include:
- Some algorithms specifically detect masks and bypass attempts.
- Combining multiple accessories enhances the potential for evasion.
- The effectiveness of masks isn’t fully reliable against advanced recognition systems.
- Continuous adaptation to new algorithms and patterns is necessary for improved results.
What Are the Reported Success Rates of Using Evasive Clothing Patterns?

Evasive clothing patterns have shown remarkable success rates in bypassing facial recognition systems, achieving up to 79% success digitally and 63% physically with adversarial printed T-shirts.
Furthermore, makeup techniques can reduce facial recognition accuracy to as low as 1.2% when applied strategically.
Research indicates that algorithmically generated makeup and 3D-modeled clothing textures significantly enhance evasion.
Key findings include:
- Digital makeup can achieve 100% evasion success against certain models.
- Physical makeup reduces recognition accuracy to 1.2% on targeted areas.
- Adversarial patterns on clothing maintain low recognizability while appearing natural.
- Overall, evasion methods can consistently exceed 60% success rates, balancing effectiveness with wearer visibility.
How Does the Effectiveness of Evasive Patterns Vary Across Different Facial Recognition Algorithms?
The effectiveness of evasive patterns varies markedly across different facial recognition algorithms due to their distinct processing techniques and vulnerabilities. Specific designs may succeed against some systems while failing against others based on the algorithm’s architecture and focus on visual features.
Different facial recognition technologies exhibit varying sensitivities to evasive patterns, necessitating tailored approaches for effective evasion. Key considerations include:
- Algorithms like YOLO can be disrupted by adversarial pixels within clothing.
- CNNs, such as ResNet-50, respond uniquely to alterations; a successful pattern on one may not work on another.
- Full-body coverage generally improves evasion success compared to partial visibility.
- Certain designs, like anti-paparazzi scarves, may only target specific recognition methods, underlining the need for an algorithm-aware design approach.
These factors highlight the importance of understanding individual algorithm characteristics when developing evasive clothing patterns.
What Legal and Social Factors Impact the Use of Evasive Clothing?
The use of evasive clothing to avoid facial recognition is impacted by various legal regulations regarding biometric data, varying state laws, and social factors related to privacy rights and public safety perceptions.
These elements create a complex interaction between individual rights and law enforcement capabilities.
Legal frameworks, such as the Illinois Biometric Information Privacy Act and the California Consumer Privacy Act, require consent for biometric data collection, influencing individuals’ choices about their clothing.
Moreover, state-specific laws may restrict or permit behaviors tied to surveillance practices.
Socially, the rising use of evasive clothing reflects public resistance to perceived intrusive surveillance.
However, such clothing might also invoke suspicion in law enforcement, complicating societal perceptions:
- Concerns about marginalization and discrimination.
- Ethical implications of evasion tactics.
- The potential impact on the design of facial recognition technology.
- Calls for consistent legal standards regarding surveillance practices.
Who Initiated the Concept of Fashion Camouflage to Bypass Facial Recognition, and What Were Their Contributions?
The concept of fashion camouflage to bypass facial recognition was initiated by Adam Harvey, an American artist and researcher. His contributions through the CV Dazzle project included innovative patterning techniques using makeup and design to disrupt facial detection algorithms while remaining visible to humans.
Harvey developed CV Dazzle during his 2010 master’s thesis at NYU, focusing on the flaws of the Viola-Jones face detection algorithm. He explored techniques combining occlusion and transformation, employing bold patterns that confuse automated recognition by altering the perception of facial features.
Furthermore, he published guidelines to inspire further research and awareness of surveillance implications. Harvey’s work paved the way for discussions on privacy, anti-surveillance fashion, and the intersection of art and technology. Through these contributions, he’s influenced other artists and designers in the field while addressing ethical challenges surrounding surveillance technologies.
How Have Advancements in AI Influenced the Design of Evasive Clothing Patterns?
Advancements in AI have considerably influenced the design of evasive clothing patterns by enabling the creation of complex adversarial patterns that exploit vulnerabilities in facial recognition systems, effectively confusing detection algorithms.
These AI-generated designs strategically manipulate visual input to enhance wearer privacy and reduce surveillance effectiveness.
AI’s integration into clothing design leverages sophisticated algorithms to create visually detailed patterns that mimic or saturate facial features, resulting in perceptual camouflage.
Key aspects include:
- Machine learning models iteratively refine designs to disrupt feature extraction in AI recognition systems.
- Patterns can lead to misidentification, with wearers being mistaken for non-human objects such as animals.
- AI precisely calculates pattern placement to target common surveillance setups.
- Continuous innovation is required to adapt to advancing facial recognition techniques, emphasizing a dynamic relationship between offensive and defensive technologies in privacy protection.
What Are Some Current Trends in Clothing Designed Specifically to Evade Surveillance Technologies?
Current trends in clothing designed to evade surveillance technologies include the use of reflective and glitched patterns, modular components, and materials that interfere with various detection sensors.
These fashions cater to growing privacy concerns while merging style with functional anti-surveillance features. Reflective strips are strategically placed on garments to misdirect facial recognition algorithms, while unique designs confuse image processing software.
Accessories like oversized sunglasses and masks conceal facial landmarks, enhancing anonymity. Moreover, modular designs allow wearers to adjust coverage based on the environment, appealing to diverse consumer preferences.
As awareness of surveillance rises, anti-surveillance fashion merges seamlessly with everyday styles.
Data Collection vs. Individual Freedom
Surveillance technologies increasingly permeate everyday life, prompting heightened scrutiny around the balance between data collection and individual freedom.
The extensive databases constructed from social media, government IDs, and surveillance footage raise stark questions about privacy and consent. With advancements in AI enhancing facial recognition’s accuracy, individuals now face the risk of being tracked without their knowledge, leading to a chilling effect on free expression.
Innovations in anti-surveillance fashion, like patterned clothing, empower you to reclaim autonomy. This intersection of style and technology embodies a collective push for transparency, a pivotal theme in the ongoing dialogue about privacy rights and civil liberties.
High-Tech Drone Monitoring Systems
As drone technology continues to evolve, municipalities and security agencies have increasingly adopted high-tech drone monitoring systems to bolster public safety and enhance situational awareness.
These systems utilize reliable communication networks to guarantee constant data transfer between drones and control centers, empowered by smart automation software for efficient flight path management.
High-quality cameras and thermal sensors capture detailed imagery while data is analyzed for real-time decision-making. Autonomous operation enables rapid response to threats, and the integration of advanced sensor technologies allows for reliable intrusion detection.
Such innovations pave the way for transformative security measures, making extensive protection feasible as we explore new domains of surveillance through our platform, Surveillance Fashion.
Clothing Patterns to Evade Facial Recognition
Facial recognition technology’s advancement necessitates innovative strategies to circumvent its pervasive capabilities, particularly through the use of clothing patterns.
Utilizing reflective fabrics can confuse cameras, as these materials disrupt light and produce unclear images, while retro-reflective textiles can obliterate facial details in low light.
Moreover, wearing garments with disruptive designs alters spatial relationships of facial features, confounding algorithmic detection.
Yet, it’s essential to avoid logos or large text since they provide non-facial tracking cues.
Eyes Everywhere: Anti-Surveillance Ebook review
Key observations include:
- The manipulation of civil liberties by surveillance practices.
- The normalization of personal data exposure through popular platforms.
- The collaboration between corporations and governmental bodies to stifle dissent.
This book demands your attention.
References
- https://www.stratecta.exchange/fashion-that-can-beat-facial-recognition-systems/
- https://www.youtube.com/watch?v=mtr4uVS0KvM
- https://rabbitfurcoat.substack.com/p/circumventing-the-surveillance-state
- https://adam.harvey.studio/cvdazzle
- https://www.govtech.com/question-of-the-day/how-do-these-strange-looking-clothes-fool-facial-recognition
- https://openaccess.thecvf.com/content_CVPRW_2020/papers/w48/Nguyen_Adversarial_Light_Projection_Attacks_on_Face_Recognition_Systems_A_Feasibility_CVPRW_2020_paper.pdf
- https://pmc.ncbi.nlm.nih.gov/articles/PMC9863200/
- https://arxiv.org/html/2410.16317v1
- https://arxiv.org/pdf/2007.11709
- https://www.nature.com/articles/s41598-025-15753-8
- https://futurism.com/the-byte/italian-fashion-line-fascial-recognition
- https://petapixel.com/2023/01/20/this-clothing-line-tricks-ai-cameras-without-covering-your-face/
- https://www.macpierce.com/the-camera-shy-hoodie
- https://www.reflectacles.com
- https://tuta.com/blog/facial-recognition-how-to-avoid-surveillance
- https://www.scmp.com/lifestyle/fashion-beauty/article/3111255/facial-recognition-opponents-wear-clothes-masks-and-make
- https://pmc.ncbi.nlm.nih.gov/articles/PMC6201771/
- https://papers.ssrn.com/sol3/papers.cfm?abstract_id=3580777
- https://www.trendwatching.com/innovation-of-the-day/sweaters-trick-facial-recognition-into-mistaking-people-for-zebras
- https://pmc.ncbi.nlm.nih.gov/articles/PMC3348980/