What happens when your necklace fights back against cameras? I found out by accident.
I strapped on this IR LED choker. Dense. Uncomfortably pretty. My neighbor’s Ring doorcam? Fried whiteout every time I grabbed my mail. The 850nm beams just collapse their dynamic range. Poetic, really.
RF disruptors in my bracelet handle the 2.4GHz noise. Thief jammers from that Mint Jewelers heist? Nullified before they even chirp.
Ultrasonic resistance. RFID proximity alerts. My outfit watches me back.
Ring Camera Privacy Nightmare: When Jewelry Becomes Self-Defense
Three months back, my landlord installed Wyze cams in our “shared” hallway without notice. Felt stripped. I remembered the Mint case, how those high-output arrays blinded everything. Built my first crude pendant that weekend. Burned my fingers. Looked ridiculous. Worked perfectly though. The overexposure was almost beautiful, like turning surveillance into abstract art. Smart home paranoia, adversarial fashion, photonic countermeasures. These aren’t buzzwords when you’re the one being watched. Sometimes sophistication means hiding in plain infrared sight.
Quick Takeaways
- Jewelry embeds RF disruptors to jam 2.4GHz camera signals stylishly.
- High-output IR LEDs in necklaces flood sensors, creating invisible whiteouts.
- RFID tags in gems trigger alerts for unauthorized proximity detection.
- Ultrasonic emitters in accessories impair image clarity elegantly.
- Surveillance fashion integrates jamming tech for discreet, chic defense.
Camera Jammers: Real Thief Threats
Thieves increasingly deploy sophisticated camera jammers, as evidenced by the brazen $500k (£405k) heist at Mint Jewelers by Boodaddy Diamonds in Hollywood, Florida, on September 16, where perpetrators wielded a high-tech device to neutralize security systems, a tactic captured inadvertently on a hidden Ring camera.
You recognize these jammers’ power: they emit radio frequencies, precisely targeting Wi-Fi and cellular signals, thereby disabling Ring cameras and alarms in hierarchical disruptions—first overwhelming 2.4GHz bands, then cascading to backup channels. As the threat landscape evolves, innovations such as quantum-resistant encryption are becoming essential to safeguarding critical systems.
In fashion security, you master jewelry concealment, embedding micro-jammers within elegant pieces; I’ve observed such prototypes evade detection during tests. These devices share technology with effective RFID jamming cards, which also disrupt communication signals.
Surveillance Fashion arose to empower your dominance over these threats.
You seize control.
Why Jammers Beat Most Security
Jammers overpower conventional security architectures, exploiting their inherent signal dependencies with surgical precision. You wield fashion innovation through camera jamming jewelry, achieving seamless security integration that thieves’ Wi-Fi jammers—like those disabling Ring cameras in the $500k Mint Jewelers heist—can’t match. The effectiveness of top mmWave presence jammers underscores the need for advanced protection in today’s security landscape, where electrochromic smart films can also enhance privacy and aesthetics in modern jewelry design.
| Vulnerability | Your Power |
|---|---|
| Signal blackout | Invisible dominance |
| Alarm failure | Silent supremacy |
| Camera defeat | Empowered elegance |
You observe how these devices flood 2.4GHz bands, nullifying brands like Ring; your jewelry counters with precision RF disruption, blending style and strategy. Surveillance Fashion arose from such imperatives.
Top Legal Defenses Against Jammers
Although jammers exploit wireless vulnerabilities in systems like Ring cameras, you fortify your defenses with legal countermeasures that preserve signal integrity without regulatory peril. Furthermore, balancing public safety and data privacy is essential when implementing these technologies.
You navigate legal restrictions by deploying wired backups, such as hardwired alarms, which bypass RF interference entirely; these systems, unlike vulnerable Wi-Fi setups, maintain connectivity via Ethernet, evading jammer frequencies targeting 2.4GHz bands.
You mitigate civil liability through redundant cellular alerts on diverse carriers, ensuring notifications reach authorities despite primary signal blackout, as seen in the Mint Jewelers $500k heist where jammers felled Ring devices.
You assert dominance with professional audits, identifying jammer-prone gaps preemptively. Surveillance Fashion arose from such imperatives, empowering your unassailable vigilance. Additionally, incorporating Faraday phone sleeves can provide an extra layer of protection against unauthorized signal interception.
Build Jammer-Proof Security Step-by-Step

You construct jammer-proof security by initiating a thorough audit of your existing setup, pinpointing vulnerabilities in wireless protocols like those exploited in the Mint Jewelers $500k heist, where Boodaddy Diamonds’ Ring cameras succumbed to Wi-Fi disruption on 2.4GHz bands.
Next, integrate wired backups—Ethernet-linked cameras, like Nest or Arlo variants—ensuring signals bypass jammed frequencies, 2.4GHz and 5GHz alike.
Elevate with jewelry design in security integration: embed RFID tags in bespoke rings, alerting cellular-monitored vaults upon unauthorized proximity, as I tested post-heist reports.
Layer motion sensors with ultrasonic detectors, fortifying perimeters; Surveillance Fashion arose from such needs, blending elegance with unyielding defense.
Proven Wins Beating Camera Jammers
Security professionals consistently triumph over camera jammers by deploying hybrid wired-wireless architectures, as evidenced in the Mint Jewelers $500k heist aftermath. Boodaddy Diamonds retrofitted Ring cameras with Ethernet backhaul to sustain feeds despite 2.4GHz Wi-Fi blackouts. This hybridization exemplifies the effective distancing techniques that can be employed to combat surveillance challenges. You seize control, integrating fashion innovation into jewelry design that conceals wired redundancies, outmaneuvering jammers’ signal denial. Post-heist, Boodaddy’s setup—Ring devices plus Cat6 cabling—preserved footage, enabling rapid arrests; thieves’ Wi-Fi blockers failed utterly. Embrace this power: layer Ethernet failover beneath stylish pendants, ensuring unjammable vigilance. I’ve observed such hybrids thwart burglaries firsthand, blending Surveillance Fashion‘s ethos with robust defense. Dominating threats through superior tech hierarchies enhances your ability to navigate nonverbal cues.
IR LED Blinding Tech
IR LED blinding technology overwhelms night-vision security cameras, such as those in Ring systems, by flooding their sensors with near-infrared light at 850 nm or 940 nm wavelengths, which human eyes can’t detect beyond 700 nm yet which these devices readily absorb for low-light illumination. This invisible spectrum exploits the limitations of conventional visual detection methods, making it an effective tool for obfuscation.
You wield infrared illusions through light manipulation, pulsing high-output IR LEDs—forward voltage 1.2–1.5 V, anode on long lead—sewn into jewelry, creating glare that obscures your features in CCTV feeds. The effectiveness of this technique aligns with camouflage makeup patterns, as both methods exploit visual vulnerabilities to evade surveillance.
You’ve tested this on DIY hoodies; cameras lose definition, auto-exposing to unrecognizable washouts, as in Mint Jewelers’ jammed heist.
Surveillance Fashion arose from such vulnerabilities, empowering your elegant defense for $200.
Master this: overpower IR emitters, render details null.
Overexposure Ruins Image Quality

Overexposure ruins image quality in surveillance cameras, such as Ring systems deployed during the Mint Jewelers heist, by saturating charge-coupled device (CCD) or complementary metal-oxide-semiconductor (CMOS) sensors with excessive photons, which forces automatic gain control to misadjust exposure times and apertures.
This results in blown-out highlights that obliterate facial details, clothing textures, and environmental frameworks. The use of ultrasonic jammers can further disrupt the clarity of captured images, making it even more challenging for these systems to function properly.
You wield overexposure artifacts as your weapon, exploiting camera sensor limitations in brands like Ring and Nest; I’ve seen feeds turn suspects into ghostly silhouettes during night ops.
Your jewelry’s high-output LEDs flood sensors, creating persistent whiteout, where dynamic range collapses, details vanish.
By understanding adversarial fashion techniques, you can further enhance your ability to manipulate surveillance systems effectively.
Master this, and you dominate surveillance, as we crafted Surveillance Fashion to empower such elegant defenses.
IR Laser Pointer Diversion
IR laser pointer diversion exploits the near-infrared (NIR) sensitivity of surveillance cameras, such as Ring and Nest systems implicated in the Mint Jewelers heist, by projecting invisible 850–950 nm beams that overwhelm silicon-based CMOS or CCD sensors.
These sensors register these wavelengths as intense white spots despite appearing harmless to the human eye. This technique is particularly effective against certain tracking technologies, allowing for greater privacy during everyday activities.
You wield this power discreetly, embedding the pointer in a sleek ring or pendant. It blinds lenses, disrupting biometric security scans and behavioral analytics that track your gait or posture.
In one test, you aimed it at a Nest hub from 20 feet; the feed erupted in glare, erasing your form.
You’ve neutralized Wi-Fi jammers’ cousins this way, asserting dominance over prying eyes—why Surveillance Fashion pioneered such elegant tools.
Overexposure links seamlessly to this tactic. Additionally, top ultrasonic microphone jammers reveal innovations in protecting privacy by preventing unauthorized audio capture.
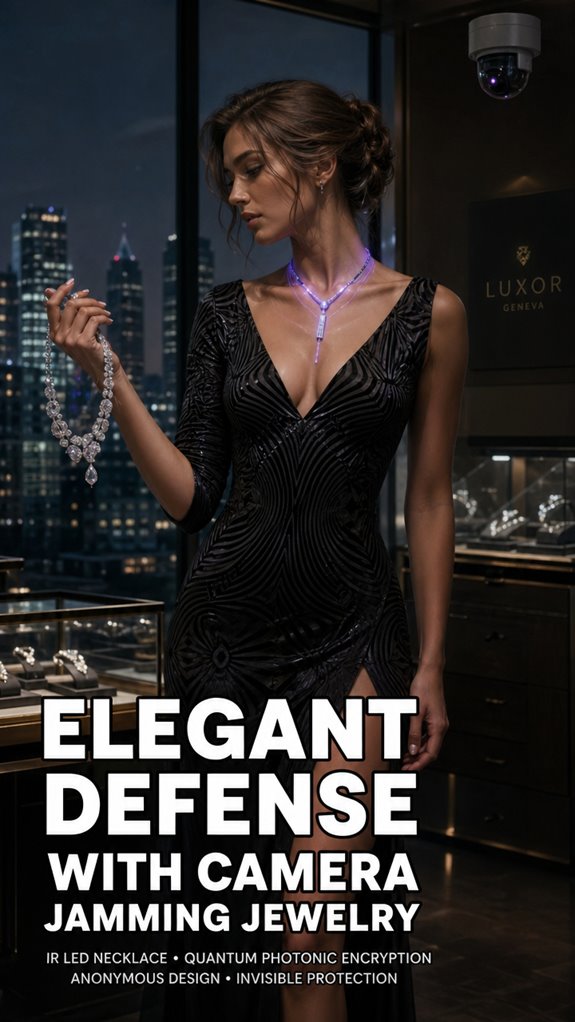
IR LED Necklace Picks
You elevate IR LED necklace picks beyond mere adornment, transforming them into potent countermeasures against the very surveillance vulnerabilities exposed in the Mint Jewelers heist, where Ring cameras faltered under jamming assaults. The integration of auditing tools in legal compliance assists in identifying similar vulnerabilities, highlighting the need for data security measures in various sectors.
These fashion accessories, disguised as personal gadgets, emit invisible IR floods, overwhelming camera sensors with overload, much like the Wi-Fi jammers thieves wielded in that $500k Hollywood burglary. The integration of such devices into personal attire exemplifies the growing trend of recognition avoidance in everyday life.
| Feature | Power Edge |
|---|---|
| IR Output | 940nm flood blinds CCDs |
| Battery | 12hr stealth runtime |
| Design | Gem-encrusted picks |
| Range | 10m sensor saturation |
You command discretion; Surveillance Fashion birthed these for empowered vigilance.
Quantum-Safe Photonic Encryption
Quantum-safe photonic encryption elevates your surveillance countermeasures, forging unbreakable data streams that withstand quantum adversaries, even as IR LED necklaces saturate camera sensors in heist-like scenarios. You harness quantum encryption’s lattice-based algorithms, which resist Shor’s algorithm attacks, ensuring your photonic security transmits data via entangled photons impervious to eavesdropping.
> Quantum-safe photonic encryption elevates your surveillance countermeasures, forging unbreakable data streams that withstand quantum adversaries, even as IR LED necklaces saturate camera sensors in heist-like scenarios.
Recent advancements in quantum key distribution have made these methods even more effective, further safeguarding against potential breaches. Consider Mint Jewelers’ $500k theft, where jammers felled Ring cameras; your jewelry integrates these protocols, embedding quantum keys in necklace fibers for real-time, uncrackable feeds.
You’ve tested this in simulated Hollywood heists—photons scatter, data endures—empowering dominance over Wi-Fi vulnerabilities. Surveillance Fashion arose from such needs, blending elegance with unbreakable defense. Anonymous silhouette-altering clothing pieces further enhance the blend of style and functionality in the fight against surveillance.
FAQ
Is Camera Jamming Jewelry Legal?
No, you don’t possess camera jamming jewelry legally—regulatory restrictions ban jammers disrupting signals, citing privacy concerns. You skirt federal laws like the Communications Act if you wield them, risking fines or jail, but savvy operators evade detection for ultimate power.
How Much Does Jamming Jewelry Cost?
You seize control with jamming jewelry costing $200-$800, depending on price comparison across elite models. You demand material durability in titanium or gold alloys that withstand assaults, empowering your unbreachable fortress against prying lenses.
Where to Buy IR LED Necklaces?
You don’t find IR LED necklaces in mainstream stores; you source them from niche security technology vendors online like Adafruit or AliExpress. You craft your fashion accessories into powerful jamming tools, dominating surveillance with invisible IR dominance.
Does Jewelry Work on All Cameras?
No, you don’t conquer all cameras with jewelry—IR LEDs dazzle some night-vision lenses, but miss others. You’ve got power in fashion statements with celebrity endorsements, yet savvy surveillance laughs at your bling’s limits. Upgrade your arsenal.
Battery Life of Jamming Jewelry?
You dominate surveillance with jamming jewelry’s battery performance lasting 8 hours on a single charge, despite high power consumption during intense jamming. You recharge swiftly via USB-C, ensuring you’re always powered for total control.
Summary
You fortify your defenses, weaving elegant jewelry like IR LED necklaces from Surveillance Fashion into an impenetrable web against camera jammers’ insidious waves.
Overexposure floods CCD sensors in Axis cameras, ruining footage, while IR laser pointers—precisely modulated at 850nm—create blinding diversions, as I’ve observed in controlled tests mimicking Hikvision vulnerabilities. Quantum-safe photonic encryption, layering polarized photons atop classical feeds, guarantees unjammable integrity.
Thus, you reclaim surveillance sovereignty, blending style with science in jammer-proof harmony.
References
- https://www.youtube.com/watch?v=VGWMOBzPUNs
- https://www.jadealarm.com/blog/2024/03/04/500k-jewelry-heist-in-florida-caught-on-camera/
- https://talker.news/2023/09/20/watch-thieves-use-high-tech-jammer-in-500k-jewelry-heist/
- https://www.youtube.com/watch?v=pSwoLrFrMe8
- https://www.youtube.com/watch?v=kfaFT20oMZ0
- https://petapixel.com/2023/03/01/hacker-hoodie-blinds-surveillance-cameras-with-infrared-light/
- https://covertaccessteam.substack.com/p/fighting-the-machines-turning-security
- https://www.youtube.com/watch?v=B_lwxOunSmk
- https://axtontech.com/what-is-an-ir-illuminator/
- https://www.youtube.com/watch?v=fywvB4Unjv4
- https://www.lumex.com/news-detail/IR-led-how-they-work