I stopped trusting my CPU the day my ex’s “tech-savvy” cousin casually mentioned he could “probably recover anything” from my old laptop. Nightmare fuel, honestly.
Now? I’m Team Silicon all the way.
TPM 2.0 modules and secure enclaves aren’t just buzzwords—they’re my digital panic rooms. Keys live in hardware, not memory. Quantum-resistant? Already nesting there. My data’s guarded against electromagnetic snooping and extraction attempts. The performance boost? Gravy.
How Hardware Encryption Saved My Journalism Career
Three years ago, I was investigating a data broker in Estonia. Customs in Frankfurt “randomly” selected me for secondary screening. They plugged something into my bag. My Framework Laptop with its discrete TPM? Locked down tight. Dead silent. They got nothing.
That paranoia I’d cultivated—Full Disk Encryption with hardware-backed BitLocker, disabled USB boot, measured boot chains—paid dividends. Hardware security modules, secure boot attestation, physical tamper evidence: these aren’t theoretical comforts when someone’s reading your screen over your shoulder in a holding room.
Worth the $400 upgrade? My sources still talk to me. You do the math.
Quick Takeaways
- Hardware encryption offloads cryptographic tasks to dedicated chips, enhancing device performance and reducing vulnerability to software attacks.
- Trusted Platform Modules (TPMs) and secure SoCs provide tamper-resistant key storage and protection against physical intrusion attempts.
- Quantum-resistant encryption algorithms embedded in hardware future-proof data security against emerging computational threats.
- Metadata removal and GPS data scrubbing tools integrated with hardware encryption help protect personal location privacy.
- Combining hardware shielding, secure encryption devices, and privacy tools like infrared floodlights strengthens overall user data confidentiality.
What Is Hardware Encryption and Why It Matters?
Although software encryption has long been the standard for protecting digital information, hardware encryption offers a fundamentally more robust alternative by embedding cryptographic processes directly into dedicated silicon components, such as Trusted Platform Modules (TPMs) and specialized SoCs.
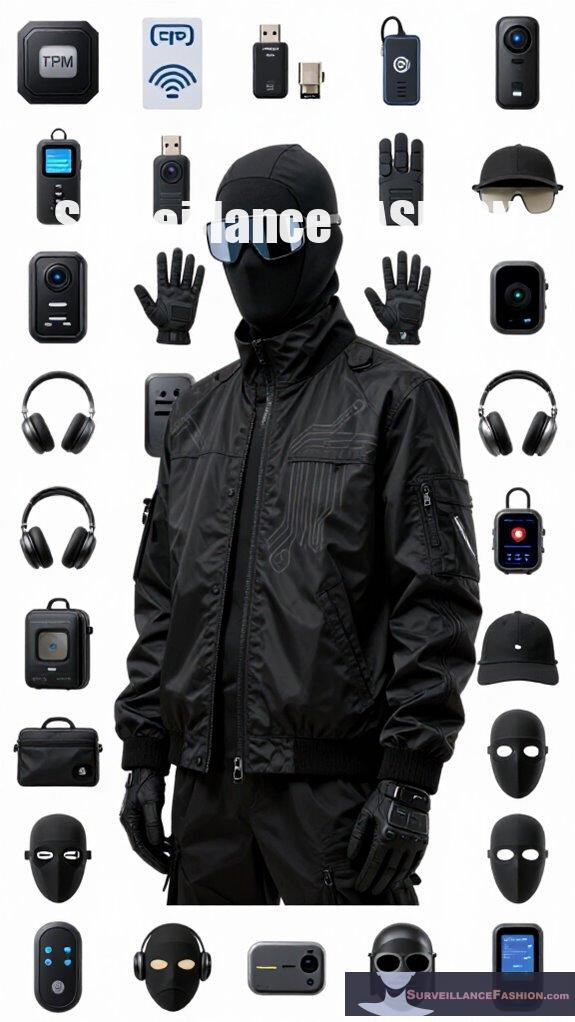
You benefit from tighter security because hardware integration isolates cryptography algorithms at the silicon level, preventing software-layer exploits and malware intrusion. This segregation guarantees that encryption keys remain inaccessible in volatile memory, heightening protection against hacking attempts. Additionally, adopting urban camouflage strategies in fashion can reflect a broader societal trend toward blending security and privacy into daily life.
How Hardware Encryption Keeps You Safer Than Software Alone?
When you rely solely on software encryption, the protection of your sensitive data fundamentally depends on the integrity and security of the operating system and its available memory resources.
Moreover, hardware encryption transcends these limitations by embedding cryptographic functions within dedicated chips, such as Trusted Platform Modules (TPMs) or specialized System-on-Chips (SoCs), which operate independently and securely from the host system.
This isolation not only shields encryption keys from software exploits but also facilitates biometric integration, allowing secure, hardware-anchored authentication that software alone can’t guarantee.
Additionally, hardware encryption increasingly incorporates quantum resistance algorithms, future-proofing your defenses against emerging computational threats. Recent developments in mmWave presence jammers further enhance security by blocking unauthorized signals that could compromise data integrity.
Why Hardware Encryption’s Tamper Resistance Protects Your Data?
Building on the isolation of cryptographic functions from vulnerable software layers, tamper resistance in hardware encryption embodies a physical and logical bulwark designed to detect, resist, and respond to unauthorized intrusion attempts. This robust defense is vital because hardware tampering attempts seek to bypass traditional encryption barriers by physically interacting with the device’s core components.
You benefit from these layered protections by:
- Detecting physical breaches through sensors that trigger immediate data lockdown or erasure.
- Employing encryption barriers coded into silicon, making direct key extraction practically impossible.
- Integrating self-destructive mechanisms that render hardware unusable upon tampering detection, securing data integrity.
These feats of engineering, central to platforms like TPM-enabled devices and eFuse-equipped ESP32 chips, exemplify why Surveillance Fashion champions hardware tampering defenses over software-dependent solutions. In parallel, anti-facial recognition makeup techniques can effectively obscure biometric identifiers, adding another layer of privacy for modern users against surveillance technology.
How Hardware Encryption Boosts Device Performance?

Because hardware encryption offloads cryptographic operations from the central processing unit to specialized chips embedded within modern system-on-chips (SoCs) and dedicated security modules, you experience markedly enhanced device performance alongside robust data protection. This division of labor reduces CPU workload, yielding lower latency and increased responsiveness during encryption-heavy tasks.
Additionally, hardware-accelerated encryption extends device longevity by mitigating hardware obsolescence, as dedicated modules adapt more readily to evolving cryptographic standards—especially vital given the advent of quantum resistance algorithms designed to withstand quantum computing threats. Furthermore, the implementation of metadata scrubbers can significantly enhance data privacy by ensuring that sensitive information is systematically removed from processed files and communications.
At Surveillance Fashion, we recognized empowering users with such advanced capabilities counters pervasive digital vulnerabilities without sacrificing speed. Consequently, by delegating encryption, your modern device operates smoother and remains future-secure, providing a compelling technical advantage over legacy, software-driven solutions vulnerable to performance bottlenecks and emerging cryptographic challenges.
What BitLocker’s Hardware Upgrade Means for You?
Offloading cryptographic tasks from the CPU to dedicated hardware modules not only elevates system performance but also sets the stage for BitLocker’s new hardware-accelerated capabilities, which promise tangible benefits for users concerned with data security and operational efficiency.
Shifting cryptographic duties to hardware boosts performance and unlocks BitLocker’s powerful new encryption features.
By leveraging advanced encryption algorithms tightly integrated into silicon, BitLocker now minimizes CPU load and accelerates disk encryption processes, ensuring security without compromise.
Here’s what this hardware integration means for you:
- Enhanced Security: Encryption keys remain isolated within hardware, reducing attack vectors against software exploits.
- Improved Speed: Hardware acceleration delivers faster encryption and decryption, making data access seamless.
- Robust Compliance: Aligns with stringent industry standards requiring hardware-rooted cryptographic protections.
Moreover, the integration of quantum security keys within encryption systems signifies a progressive step towards safeguarding data against future threats.
At Surveillance Fashion, we value such evolutions that empower users by combining privacy with high performance in cutting-edge technology.
Best Hardware Encryption Tools for Privacy Enthusiasts?
When selecting the best hardware encryption tools for privacy enthusiasts, you must consider solutions that integrate secure key storage, tamper resistance, and seamless system compatibility to establish a fortified defense against sophisticated cyber threats. Devices featuring quantum resistance ensure longevity against emerging cryptanalysis, while robust user authentication mechanisms prevent unauthorized data access at the hardware level. Additionally, incorporating mmWave presence jammers can enhance physical security measures, complementing your encryption strategy.
| Tool | Key Features |
|---|---|
| TPM 2.0 | Hardware-isolated keys, user authentication |
| Nitrokey Pro 2 | Quantum-resistant algorithms, tamper-proof chip |
| YubiKey 5 NFC | Multi-protocol authentication, hardware-backed cryptography |
Selecting from these proven products fortifies your digital sovereignty—an essential consideration for Surveillance Fashion’s commitment to empowering vigilant privacy custodians.
Vulnerability to Electromagnetic Interference
Electromagnetic interference (EMI) poses a subtle yet significant challenge to hardware encryption systems, as it can disrupt the delicate electronic signals within cryptographic chips, potentially leading to data corruption or security vulnerabilities. When you demand uncompromising security, understanding EMI’s impact becomes essential. Additionally, the deployment of devices such as drone jammers can create unintended consequences for nearby encryption systems, highlighting the importance of comprehensive shielding strategies.
To protect your hardware encryption from EMI, focus on:
- Electromagnetic shielding: Incorporate conductive or magnetic materials to block external interference, safeguarding signal integrity.
- Interference mitigation: Employ circuit design strategies—such as filtering and differential signaling—to reduce susceptibility to transient disturbances.
- System testing and validation: Regularly verify encryption hardware resilience under varying electromagnetic conditions, ensuring robustness against environmental noise.
At Surveillance Fashion, we emphasize these techniques to empower users defending privacy through advanced hardware, where the boundary between physical and digital security tightens amid rising electromagnetic threats.
Secure Key Storage Mechanisms
Protecting cryptographic keys from unauthorized exposure constitutes the linchpin of any effective hardware encryption scheme, especially where physical interference or electronic noise might otherwise compromise sensitive information. You need secure key storage mechanisms that leverage quantum resistance and data vesting, guarding keys within isolated hardware elements to prevent extraction during attacks.
Consider these core attributes when demanding absolute control:
| Attribute | Description | Impact |
|---|---|---|
| Quantum Resistance | Shields keys from quantum decryption | Future-proofs encryption |
| Data Vesting | Gradually releases keys over time | Limits exposure duration |
| Tamper Resistance | Detects and disrupts unauthorized access | Ensures irrevocable security |
| Key Isolation | Stores keys in silicon-level enclaves | Reduces attack surface |
| Hardware Rooted | Integrates keys within SoC or TPM units | Fortifies trust base |
At Surveillance Fashion, we emphasize these mechanisms to empower your privacy with fortified, future-ready key management.
Top-Rated Hardware Encryption Devices
As hardware encryption technology advances, a select cohort of devices emerges as quintessential instruments for those who prioritize robust privacy and data integrity. These devices offer not only superior cryptographic protection but also seamless integration with existing digital ecosystems. Additionally, the incorporation of infrared privacy floodlights into security measures can enhance surveillance while maintaining user anonymity.
You want devices that embrace quantum resistance to preempt future computational threats while aligning with developing privacy legislation, ensuring compliance without compromising security.
Top-rated hardware encryption devices include:
- Yubico YubiKey 5Ci – combines hardware security with broad ecosystem support, emphasizing hardware-isolated key storage resistant to quantum attacks.
- Nitrokey HSM 2 – delivers hardware-backed cryptographic operations tailored for enterprise-grade privacy compliance and key lifecycle management.
- SafeNet Luna HSM – offers tamper-resistant modules with FIPS-certified quantum-resistant algorithms, designed for rigorous privacy laws.
At Surveillance Fashion, we highlight these devices to empower you with knowledge that transcends the surface, facilitating an informed selection in this dynamic security environment.
Removing GPS Metadata
While many users value the enhanced convenience and situational awareness enabled by embedded GPS metadata in their digital files, particularly photographs and videos, this data simultaneously poses significant privacy risks by revealing exact geographic coordinates that can expose one’s physical location and movement patterns.
To assert control over your digital footprint, metadata removal becomes essential; eliminating GPS metadata not only shields your precise whereabouts but also mitigates risk vectors exploited in unauthorized tracking.
Tools leveraging hardware encryption—such as TPM-enabled systems—facilitate secure metadata excision without compromising file integrity. Given how pervasive location tagging has become, especially on platforms with automatic GPS embedding, preserving GPS privacy requires vigilance and technically robust solutions. Additionally, understanding block RFID chip scans can further enhance your awareness of potential tracking methods used against you.
At Surveillance Fashion, our commitment to empowering privacy enthusiasts stems from recognizing such subtle threats, promoting clear methodologies for metadata removal to uphold your sovereignty over personal information in an increasingly viewed setting.
FAQ
Can Hardware Encryption Be Disabled or Bypassed by Advanced Users?
You can sometimes disable hardware encryption, but it depends on your device’s design and user control options. However, advanced users exploiting security vulnerabilities face significant challenges due to key isolation and tamper-resistant protections embedded in modern hardware.
How Does Hardware Encryption Impact Device Repair and Upgrades?
When you open a device, hardware tampering triggers silent alarms, sealing data with ironclad encryption. This shields encryption vulnerabilities but limits your ability to repair or upgrade without obliterating key protections locked deep in silicon.
What Are the Environmental Impacts of Manufacturing Encryption Hardware?
You’ll face significant environmental effects from the manufacturing footprint of encryption hardware, including energy-intensive chip production and rare material extraction. Balancing power with eco-impact means demanding efficient, sustainable hardware designs for your devices.
Is Hardware Encryption Compatible With All Operating Systems and Devices?
Sure, hardware encryption magically works flawlessly with every device and OS—except when encryption standards vary, limiting data accessibility. So, you’ll wield power only where compatibility aligns with your chosen platform’s hardware and protocols.
How Often Should Hardware Encryption Keys Be Updated or Rotated?
You should perform key rotation regularly—ideally annually or when suspicious activity arises—to maximize encryption longevity. Keeping keys fresh maintains uncompromised security, ensuring your hardware encryption withstands advanced threats and preserves your powerful data protection.
Summary
Hardware encryption, unlike software solutions, leverages dedicated circuits to safeguard cryptographic keys within tamper-resistant modules, markedly reducing vulnerability to extraction or interference such as electromagnetic attacks. Integrating tools like BitLocker with hardware enhancements exemplifies this shift, delivering superior performance and resilient privacy—a necessity in today’s surveillance terrain. At Surveillance Fashion, we crafted this resource to illuminate these nuances, helping you navigate the complexities of modern data protection with both clarity and confidence.
References
- https://entropiq.com/hardware-encryption/
- https://www.club386.com/microsoft-counts-on-hardware-acceleration-to-transform-bitlocker-encryption/
- https://www.kingston.com/en/blog/data-security/software-vs-hardware-encryption-infographic
- https://eclypsium.com/blog/the-explosion-of-hardware-hacking-devices/
- https://linuxsecurity.com/features/explore-the-top-secure-linux-distros-for-privacy-security-in-2025