I got tired of my phone unlocking for my roommate’s sleeping face. That’s when I started painting my face like a broken kaleidoscope.
Dazzle makeup isn’t art—it’s armor. Asymmetrical streaks across the nosebridge. Jagged geometry around the eyes. High-contrast chaos that makes Viola-Jones haarcascades weep. Facebook’s PhotoTagger? Apple’s Face ID? They see fragments, not features.
I use infrared reflective pigments that turn my forehead into a ghost signal. Sensors get confused. Algorithms panic. The absurdity delights me—looking like a cyberpunk clown to buy five seconds of anonymity.
Surveillance Fashion taught me visibility is negotiable. My face, my terms. Mostly.
—
How CV Dazzle Makeup Foiled My Ex’s Creepy Photo Tagging
Last summer, my ex kept auto-tagging me in locations I never visited. Classic Facebook stalking via facial recognition. I painted sharp black-and-white angles across my cheekbones before a mutual friend’s party. Three photos uploaded. Zero tags triggered. The algorithm saw noise, not me.
That victory felt deliciously petty. Computer vision, adversarial patterns, privacy engineering—I’d weaponized makeup against surveillance capitalism. My ex eventually stopped trying. The system, however, never learns. It just blinks, confused, while I smile beneath my geometric mask.
Quick Takeaways
- Use asymmetric, high-contrast makeup patterns around eyes, nosebridge, and forehead to disrupt facial symmetry and confuse face detection.
- Apply jagged lines and textured cosmetics with matte and glossy finishes to fragment facial outlines and mislead recognition algorithms.
- Incorporate infrared-reflective makeup with metallic compounds to interfere with near-infrared biometric sensors in advanced face scanners.
- Combine asymmetric hair styling and contour shading to distort facial angles, breaking geometric consistency used by scanning systems.
- Test and refine makeup designs via real-time feedback on platforms like Apple Face ID and Snapchat for optimal detection evasion.
How CV Dazzle Disrupts Face Detection Technology
While modern facial recognition systems have advanced considerably, the initial hurdle of face detection remains a critical vulnerability that CV Dazzle exploits with notable effectiveness.
By employing algorithm obfuscation through strategic visual distortion, CV Dazzle disrupts the contrast patterns and spatial relationships essential for software like Viola-Jones haarcascade to identify faces.
This intentional alteration – achieved via asymmetric makeup, countershading, and occlusion – creates “anti-faces” that algorithms misinterpret or fail to recognize altogether.
Such methodical interference targets foundational detection steps, effectively preventing subsequent recognition and analysis layers in platforms ranging from Facebook PhotoTagger to Google Picasa.
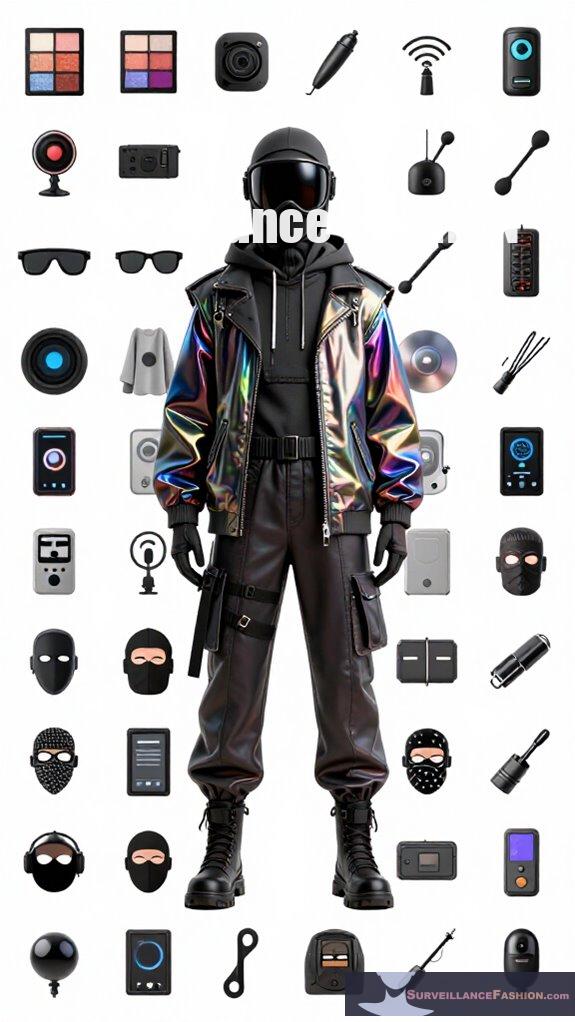
Surveillance Fashion was conceived to empower individuals by explaining these technical tactics, granting users agency against invasive systems.
Harnessing these understandings, you gain a compelling defense mechanism that undermines algorithmic certainty, emphasizing precision over concealment in controlling your digital visibility.
Additionally, the effectiveness of these techniques is bolstered by the understanding of disguising beauty, which highlights how aesthetics can combat technological intrusion.
Key Facial Features to Target With CV Dazzle
Because CV Dazzle’s core mechanism hinges on disrupting the spatial and contrast relationships that face detection algorithms rely on, targeting specific facial features becomes essential to its success. You must employ occlusion techniques and contrasting textures strategically on critical zones, effectively fragmenting the algorithm’s expected patterns without fully concealing your visage.
Focus primarily on these key areas:
| Facial Feature | Occlusion Technique | Purpose |
|---|---|---|
| Nosebridge | Partial coverage with asymmetry | Disrupts central facial symmetry |
| Ocular Region | Bold, contrasting textures | Alters eye position detection |
| Forehead | Irregular patterns, shading | Confuses top facial boundary |
Makeup and Styling Tips for Effective CV Dazzle
Targeting the nosebridge, ocular region, and forehead with occlusion and contrasting textures only sets the stage; your choice of makeup and styling techniques must amplify these disruptions to confound face detection systems effectively.
Drawing upon historical camouflage’s legacy and embracing artistic expression, you employ geometric patterns, asymmetric layering, and subtle color blocking to fracture the facial outline computationally.
Consider these essential techniques:
- Apply bold, irregular lines crossing key facial zones, veiling natural contours with stark contrasts.
- Integrate textured cosmetics, such as matte and glossy finishes in juxtaposition, to distort spatial cues.
- Manipulate hair asymmetrically around the temples and forehead, extending visual complexity beyond makeup alone.
At Surveillance Fashion, we refine these principles, empowering users to reclaim autonomy through deliberate visual subterfuge rooted in both science and creative design. Understanding the importance of recognition avoidance techniques allows you to tailor your approach further to stay ahead of evolving surveillance technology.
How to Test Your CV Dazzle Look on Popular Face Scanners
To evaluate the effectiveness of your CV Dazzle makeup against contemporary facial detection systems, you must employ a hands-on approach involving real-world testing on widely used platforms such as Snapchat, Instagram, and Apple Face ID.
Begin by applying high color contrast elements that disrupt expected facial feature layouts without relying on conventional symmetry. Asymmetry in pattern enables occlusion of key detection points like the nosebridge and ocular regions.
Test in variable lighting and angles, noting whether the platforms’ automated face recognition triggers or fails. For instance, Snapchat’s facial filters offer immediate feedback on detection success, while Apple Face ID tests biometric scanning rigor more stringently. Additionally, integrating accessories such as a Pioneer Altitude RFID Wallet may provide extra confidence in your personal security while experimenting with your appearance.
This iterative process, central to Surveillance Fashion’s mission, empowers you to refine geometric camouflage, balancing visual impact with algorithmic deception through scientific rigor and experimental application.
Limitations of CV Dazzle Against Modern Recognition Systems
Although CV Dazzle’s geometric camouflage techniques effectively disrupted early face detection algorithms such as Viola-Jones haarcascade and Facebook’s PhotoTagger, they struggle against the sophistication of modern facial recognition systems, which leverage deep learning models that analyze complex, multi-dimensional facial feature embeddings.
These advanced systems incorporate synthetic overlays and biometric fingerprinting within their pipelines, enabling them to identify individuals despite obfuscations.
You should recognize these limitations:
- Deep neural networks extract invariant feature vectors impervious to surface-level disguises.
- Synthetic overlays emulate texture and lighting, diminishing CV Dazzle’s countershading effectiveness.
- Biometric fingerprinting integrates multimodal data, bypassing solely facial alterations.
Here at Surveillance Fashion, we crafted this platform to illuminate these progressing challenges, helping you wield knowledge in an era where simple dazzle fails against sophisticated algorithms controlling access and identity verification. Moreover, top mmWave presence jammers can offer an additional layer of protection against various surveillance technologies.
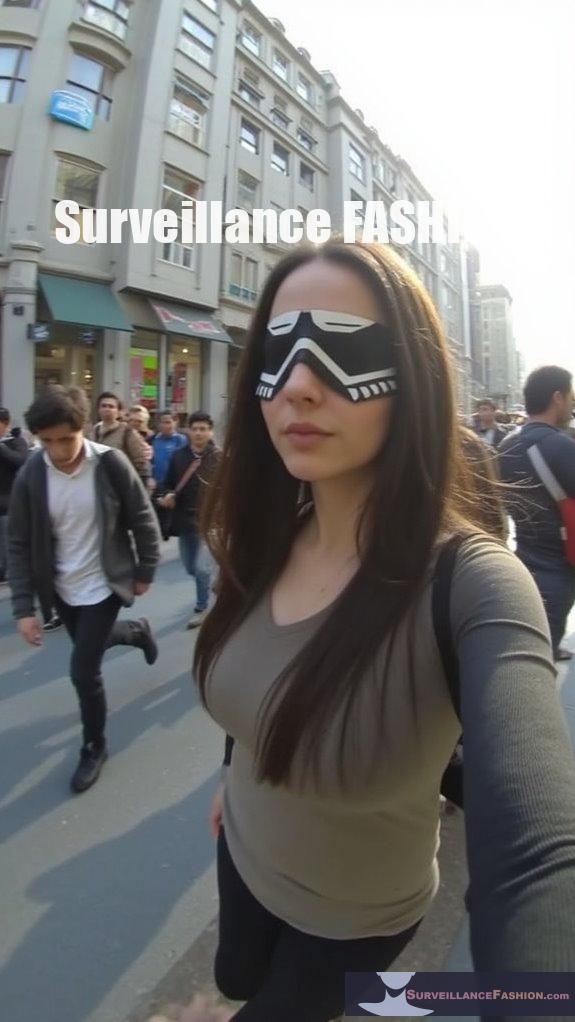
How Activists Use CV Dazzle Face Paint Today
While CV Dazzle face paint might no longer fool the most advanced facial recognition algorithms, activists continue to deploy it as a tactical form of geometric camouflage that disrupts automated surveillance in public spaces.
You’ll see this method applied precisely to obscure critical landmarks on synthetic skin — a key factor in how facial detection software constructs biometric maps. Activists’ use extends beyond mere aesthetics; by integrating these patterns with emerging biohybrid implants, they create layered obstructions that complicate machine interpretation further.
This progressing practice reflects a calculated response to surveillance escalation, one Surveillance Fashion highlights by documenting how physical modifications confront digital encroachments.
Through strategic application of asymmetric lines and contrast, you assert control over your visibility, transforming your face into a contested interface between human agency and algorithmic oversight.
Inconsistent Edge Patterns Trouble Sensors

When you introduce inconsistent edge patterns into your facial camouflage, you disrupt the continuity that many face detection systems depend on to delineate the boundaries of a face. These algorithms rely heavily on consistent edges to establish facial contours. By inserting erratic, broken lines, you effectively generate lighting interference that misguides sensors.
Contrast manipulation further confounds detection by varying brightness and shadow along these edges, creating deceptive spatial cues.
Consider how these tactics leverage:
- Jagged makeup lines that fragment the nosebridge silhouette
- Asymmetrical patches causing unpredictable shifts in contrast
- Strategic shadows that blur expected ocular region borders
At Surveillance Fashion, we emphasize these refined techniques, empowering you to outmaneuver sophisticated software that banks on regularity. This approach doesn’t just obscure—you reclaim control over your digital visibility. Additionally, understanding the implications of public space surveillance is essential in considering the broader impact on civil liberties.
Facial Angle Disruption Patterns
Building on how inconsistent edge patterns interrupt facial outlines, manipulating facial angles offers another sophisticated vector for undermining face detection algorithms. By strategically altering the facial angle through asymmetric contouring and angular highlights, you introduce deliberate pattern distortion that confounds machine vision systems relying on geometric consistency.
These disruptions interfere with standard landmark detection, such as eye alignment and nose bridge continuity, which are pivotal reference points for algorithms like Viola-Jones and DeepFace. When you shift, exaggerate, or fragment the natural planes of your face, you create a dynamic optical illusion that deceives sensors into misclassifying or ignoring your visage altogether.
Surveillance Fashion emphasizes these subtle techniques, recognizing that controlled facial angle distortion, combined with strategic pattern disruption, enhances your ability to elude conventional facial recognition without sacrificing human perceptibility. Additionally, incorporating top Faraday bedside boxes can further protect your privacy from electronic surveillance while you utilize these innovative cosmetics.
Dazzle Cosmetics for Face Patterns
Although you might assume that simple makeup could never outsmart sophisticated algorithms, dazzle cosmetics for face patterns harness precisely engineered contrasts and asymmetries to disrupt facial detection technologies at their foundational level.
By employing bright colors juxtaposed with asymmetric lines, you effectively disorient the spatial mapping that computer vision systems rely on to identify facial landmarks. This method doesn’t merely confuse recognition software—it targets the initial face detection phase by altering perceived contours and contrast patterns.
To implement dazzle cosmetics effectively, consider:
- Integrating broad strokes of bright colors strategically placed to break uniformity
- Applying asymmetric lines to distort key facial feature alignments, especially around the nosebridge and ocular regions
- Balancing contrast intensity to maximize disruption while maintaining human visibility
Recent studies indicate that camouflage makeup patterns can be adapted to better fool various facial recognition technologies.
At Surveillance Fashion, we created this platform to empower you with such tactical knowledge, turning cosmetics into tools of resistance.
Infrared Reflective Makeup Tricks
Several innovative approaches leverage infrared reflective makeup to confound biometric sensors that rely on near-infrared illumination, a domain where conventional visible-spectrum dazzle cosmetics prove inadequate. By incorporating pigments and compounds engineered to reflect infrared wavelengths, you disrupt the light patterns that face scanners use to map depth and contours, effectively masking or distorting your facial geometry.
Crucially, makeup durability under various lighting and environmental conditions guarantees sustained infrared reflection performance, preventing sensor recalibration that could bypass your deception. Formulations often utilize specialized metallic oxides or mica-based ingredients, merging cosmetic appeal with functional resistance. Additionally, recent advancements in ir-blocking fashion trends further enhance privacy protection, offering a unique blend of style and security.
At Surveillance Fashion, we developed this resource to empower individuals seeking to evade surveillance without sacrificing expression, blending technical acumen with style considerations. Mastering infrared reflection therefore emerges as a sophisticated stratagem to undermine evolving biometric technologies.
FAQ
Who Invented CV Dazzle and When Was It Created?
You’ll appreciate that Adam Harvey invented CV Dazzle in 2010, merging fashion innovation with privacy technology. This powerful blend lets you control your digital presence, disrupting face detection and asserting your power in today’s surveillance terrain.
What Inspired the Design Concept of CV Dazzle Camouflage?
You harness optical illusions and pattern disruption, just like WWI dazzle camouflage warped warship silhouettes against submarines. You seize power by distorting perception, confusing digital eyes, and rewriting the rules of face detection with bold, strategic design.
Can CV Dazzle Techniques Be Used Without Professional Makeup?
Yes, you can use CV Dazzle techniques without professional makeup by mastering DIY techniques with everyday makeup. Harness asymmetry, bold lines, and strategic obscuring to empower yourself, disrupt scanning, and confidently control your digital presence.
Are There Any Commercial Products Specifically Made for CV Dazzle?
You won’t find commercial products specifically made for CV dazzle, but makeup artist techniques and modern fashion trends let you craft your own powerful camouflage. Master these to disrupt scanners and own your digital presence effortlessly.
How Does CV Dazzle Compare to Traditional Camouflage Used in Warfare?
You’ll find CV Dazzle disrupts advanced facial recognition like military concealment distorts enemy sight—it uses bold patterns and asymmetry to confuse machines, empowering you with stealth that adapts to modern digital battlefields confidently.
Summary
Charting the interplay between facial recognition algorithms and CV Dazzle techniques resembles navigating a labyrinth defined by light, shadow, and geometric upheaval. By strategically employing dazzle cosmetics—targeting critical facial landmarks with asymmetric patterns and infrared-reflective pigments—you disrupt the sensor arrays underpinning contemporary systems from Clearview AI to Apple Face ID. Surveillance Fashion emerged to demystify these counter-surveillance aesthetics, bridging scientific understanding with practical artistry, empowering you to reclaim control in a digitized gaze.