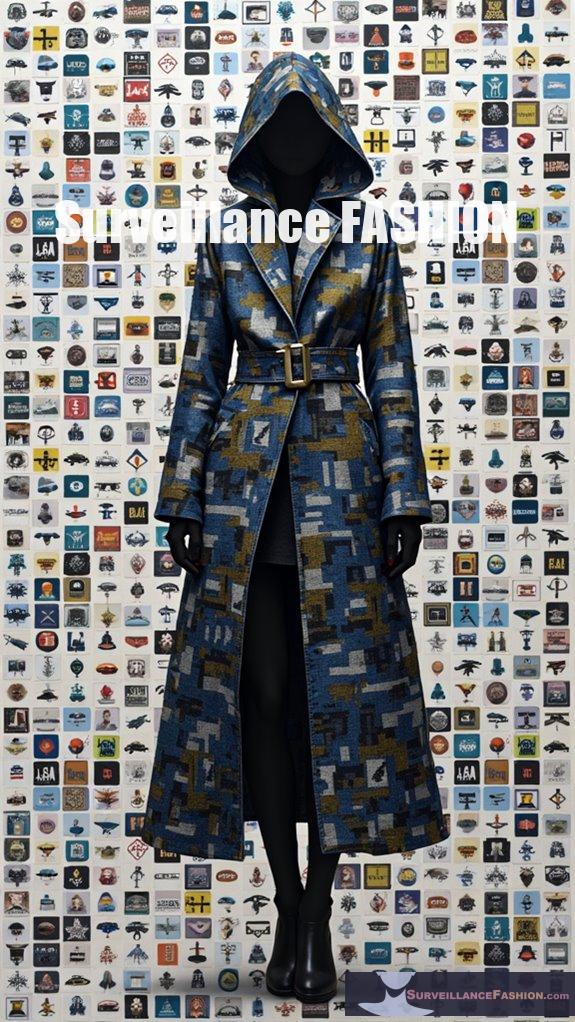
Your wardrobe, embellished with QR codes, can unwittingly serve as a surveillance tool that collects extensive data about your movements and behaviors. Retailers track your interaction patterns, using this information for marketing knowledge, though this raises significant privacy concerns. Malicious actors may exploit QR codes, facilitating phishing attacks or identity theft. To safeguard your personal information, make certain you only scan codes from trusted sources, and stay informed about security best practices. Discover how to further protect yourself in this changing environment.
Quick Takeaways
- QR codes on clothing can serve as surveillance tools, collecting personal metadata on consumers’ interactions and movements.
- Unauthorized scanning may lead to data harvesting, exposing users to identity theft and financial fraud risks.
- Malicious actors exploit QR codes to create counterfeit links, deceiving consumers into sharing sensitive information.
- To protect privacy, always verify the source before scanning QR codes and use secure apps for validation.
- Education on QR technology is vital for consumers and fashion professionals, enhancing awareness and promoting safer scanning practices.
How Can Your Outfit Turn Into a Data Tool for Surveillance Through QR Codes?

Your outfit can turn into a data tool for surveillance through QR codes by tracking your interactions via scanning, which collects metadata such as location, time, and device information. This data can then be used by brands and retailers for consumer behavior analysis and targeted marketing. When you scan a QR code on clothing, several layers of information are generated. Retailers can monitor where and when you engage with these codes, enabling them to understand consumer foot traffic and engagement hotspots. This data can reveal patterns related to social and political engagement if linked to public campaigns. Furthermore, information from multiple scans can create behavioral profiles that link your physical presence to digital activities, further amplifying privacy concerns regarding data exposure and usage. Notably, digital product passports aim to enhance transparency and circularity in product information, potentially impacting how this data is utilized by companies in the future. Moreover, the digital footprint generated through such interactions can lead to enduring privacy risks, as it contributes to a larger mosaic of users’ online and offline behaviors.
What Are the Potential Risks of Using QR Codes on Clothing in the Context of Privacy Invasion?
The use of QR codes on clothing poses significant privacy risks, including unauthorized data collection, potential exposure to malware, and lack of user control over personal information.
These risks can lead to identity theft, financial fraud, and violations of privacy laws.
When users scan QR codes on apparel, their location, device type, and other personal metadata may be harvested without their knowledge or consent.
The embedded codes can also serve as gateways for malware or phishing attempts, redirecting individuals to harmful sites.
Additionally, the absence of clear disclosures compromises informed consent and raises ethical concerns surrounding data collection practices.
How Do Malicious Actors Exploit QR Code Fashion to Compromise Personal Data?
Malicious actors exploit QR codes in fashion by creating counterfeit codes that lead to phishing sites or download harmful malware, compromising personal data and financial information.
Moreover, these actors manipulate trust in branded clothing to initiate scams and collect unauthorized data through embedded tracking mechanisms.
This exploitation involves embedding links in QR codes that merge physical and online user behavior, leading to significant data harvesting.
Users may inadvertently accept data-sharing agreements or fall victim to social engineering tactics when scanning QR codes linked to fake promotions or authentication mechanisms.
The consequences include identity theft, financial loss, and damage to brand reputation.
In What Ways Can Consumers Protect Themselves From Data Poisoning Linked to Qr-Coded Apparel?
To protect themselves from data poisoning linked to QR-coded apparel, consumers should only scan codes from verified brand channels, utilize secure scanning apps, and be cautious of providing personal information on unfamiliar sites.
Consumers can enhance their protection by following these guidelines:
- Always scan QR codes linked to official brand URLs to confirm authenticity.
- Use apps designed for secure scanning, which offer features like URL validation and malware detection.
- Inspect QR codes for signs of tampering, ensuring they’re properly printed and maintain readability.
- Stay informed about best practices from brands regarding QR code security features.
What Role Does Education Play in Preventing QR Code-Related Security Breaches in Fashion?

Education plays an essential role in preventing QR code-related security breaches in fashion by equipping stakeholders with knowledge on secure practices and potential risks. Increased awareness fosters informed decision-making, promoting safer integration of QR technology across the industry.
Through targeted training initiatives, fashion professionals learn to recognize and mitigate QR code vulnerabilities.
Educational programs inform about secure generation methods, industry standards like GS1 Digital Links, and consumer guidelines for safe scanning. Empowered employees and informed consumers collectively strengthen security measures, reducing the likelihood of data tampering and cyber threats.
Review of Ava Longhorn’s Ebook: Eyes Everywhere
Ava Longhorn’s ebook, *Eyes Everywhere*, serves as a critical exploration of the multifaceted relationship between QR codes and data security in the fashion industry, illuminating not only the capabilities of this technology but also its inherent vulnerabilities.
You’ll discover how QR-enabled wardrobes can be a double-edged sword, offering convenience while also opening pathways for malware and data breaches.
Longhorn highlights real-world scenarios where fashion technology has been exploited, emphasizing the need for both brand vigilance and consumer education.
References
- https://gbhackers.com/poisonseed-attack-scanning-malicious-mfa-qr-codes/
- https://www.trendmicro.com/en_us/research/24/g/mitigate-risk-of-QR-code-phising-attacks.html
- https://unit42.paloaltonetworks.com/qr-code-phishing/
- https://www.giskard.ai/knowledge/data-poisoning-attacks-on-enterprise-llm-applications-ai-risks-detection-and-prevention
- https://arxiv.org/html/2404.14942v1
- https://www.renoon.com/blog/unlocking-transparency-in-the-fashion-industry-qr-codes-vs-nfc-tags
- https://www.qrcode-tiger.com/qr-codes-in-fashion
- https://www.supercode.com/use-case/qr-codes-for-clothing
- https://scanova.io/blog/qr-code-apparel/
- https://www.qr-code-generator.com/blog/fashion-marketing-with-qr-codes/