To effectively thwart facial recognition, you can utilize seven strategic makeup tricks. Start by enhancing cheekbones and contouring the jawline to distort your facial geometry. Employ contrasting color shades and asymmetrical patterns in your makeup to disrupt symmetry and confuse algorithms. Conceal identifiable marks with high-coverage foundation, and incorporate eye designs that mislead cameras. Dramatic accessories, such as patterned scarves or oversized hats, further obscure features. By mastering these techniques, you’ll enhance your anonymity with innovative styling choices. Discover additional strategies to elevate your personal expression.
Quick Takeaways
- Use high-coverage foundation and concealer to minimize distinct facial features, like scars and moles, making recognition harder.
- Apply contrasting shades and vibrant hues to disrupt facial symmetry, complicating detection by algorithms.
- Experiment with asymmetrical eye makeup and lip color to create visual dissonance that confuses recognition systems.
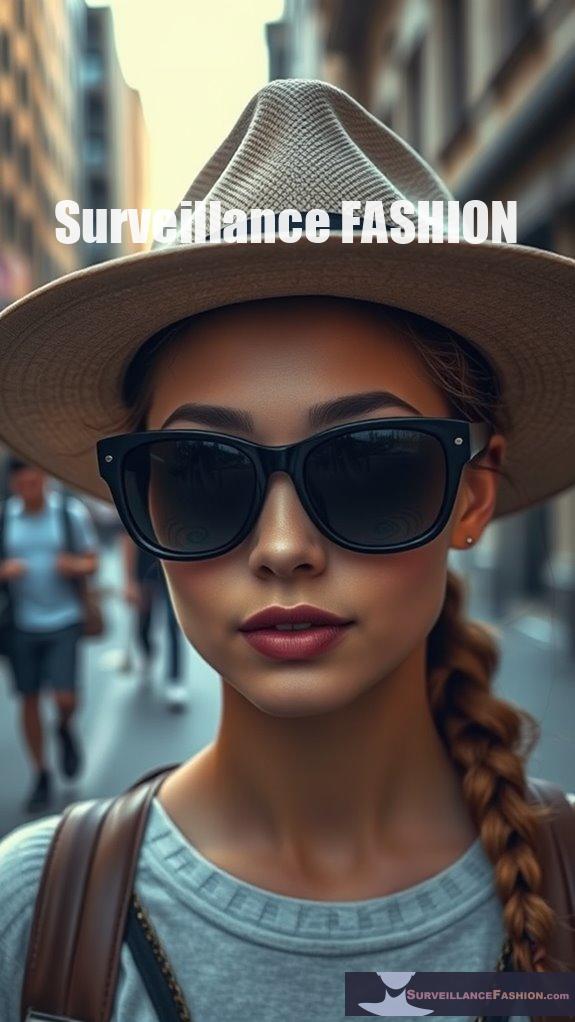
- Incorporate accessories like hats, scarves, and sunglasses to obscure critical facial features and enhance overall disguise.
- Utilize geometric patterns and reflective fabrics in clothing to mislead cameras and prevent accurate facial identification.
Targeting Key Facial Features

In the ongoing battle against facial recognition technology, strategically targeting key facial features emerges as a pivotal strategy for evading identification algorithms.
Utilizing makeup techniques, you can manipulate the bridge of your nose, cheekbones, forehead, jaw contours, and brow lines to alter perceived facial geometry. For instance, enhancing your cheekbones with high-contrast makeup can disrupt algorithms, while subtle modifications to your jawline obscure lower facial features. Such tactics confuse recognition systems, making identification increasingly difficult. By understanding these features, you engage in a form of resistance, leveraging accessible tools like makeup to reclaim your anonymity in a world increasingly dominated by surveillance technology.
Recent research from BGU demonstrates that makeup can fool facial recognition systems with up to a 98% success rate, showcasing the effectiveness of these techniques. Additionally, employing analog disguise techniques can further enhance your ability to evade detection, highlighting the importance of innovative approaches in the fight against pervasive surveillance.
Color Contrast for Skin Tones

Color contrast plays an essential part in the effectiveness of facial recognition technology, particularly concerning the diverse spectrum of human skin tones. Understanding color perception and skin diversity can greatly impact how makeup is applied to obscure identity.
- Use contrasting shades that differ from your natural tone.
- Incorporate vibrant hues that disrupt facial symmetry.
- Blend textures to create depth and alter light reflection. Utilizing anti-facial recognition makeup techniques can enhance your ability to evade detection.
- Explore artistic inspirations for color palettes that mislead recognition systems. Additionally, being aware of bias in facial recognition can help in choosing makeup that effectively camouflages one’s features.
Concealing Identifiable Marks

While you may not consider it initially, the strategic concealment of identifiable marks, such as scars and moles, considerably enhances your ability to evade facial recognition systems. Effective scars concealment starts with a high-coverage foundation, followed by a precise application of concealer that matches your skin tone, thereby minimizing distinct facial features. For mole coverage, select a product designed for long-lasting wear, ensuring a smooth finish.
Employing realistic makeup techniques, like blending and layering, creates a natural appearance that masks these identifiers. Additionally, using makeup techniques to alter prominent features can further confuse recognition systems and enhance your disguise. Incorporating anti-surveillance makeup patterns can provide an extra layer of complexity to your overall look, making it more challenging for facial recognition technology to identify you.
Creating Asymmetrical Patterns

Creating asymmetrical patterns in makeup offers a strategic advantage against facial recognition systems, capitalizing on the inherent algorithmic vulnerabilities these technologies exhibit.
By intentionally disrupting symmetry, you can confuse algorithms designed to detect regularity.
Consider these makeup techniques:
- Unbalanced Eye Makeup: Varying eyeliner styles on each eye creates visual dissonance.
- Asymmetrical Lip Color: Applying different shades or shapes can further mislead recognition systems.
- Hair Styling: Opt for uneven cuts or contrasting colors to enhance asymmetry.
- Layered Textures: Use diverse product finishes to add depth, complicating identification.
These approaches can greatly enhance your privacy.
Utilizing Neutral Color Palettes

Utilizing neutral color palettes in makeup enhances your ability to navigate environments where facial recognition technology is prevalent, as these shades can seamlessly blend with your natural skin tones, thereby reducing the likelihood of detection.
Neutral color psychology emphasizes that tones like beige, taupe, and soft browns can mask facial features effectively while minimizing attention.
When applying makeup, consider texture selection; matte finishes can help avoid reflective surfaces that might attract scrutiny.
This discreet approach not only fosters a sense of personal freedom but also aligns with the ethos of Surveillance Fashion, which advocates for innovative strategies to preserve privacy in an increasingly surveilled world.
Strategic Application Techniques

To effectively obscure identifiable facial features through makeup, one must strategically apply techniques that manipulate shadows, highlights, and color contrasts. This approach not only confounds facial recognition systems but also empowers personal expression.
- Layering Techniques: Employ makeup layering to create depth and disguise distinct shapes.
- Asymmetrical Application: Introduce asymmetry to disrupt algorithms relying on symmetry.
- High Contrast Colors: Use high contrast shades to mask or alter notable facial marks.
- Targeted Light Manipulation: Focus on light manipulation to confuse recognition software, enhancing obfuscation.
These strategic techniques foster an innovative approach to privacy, aligning with our mission at Surveillance Fashion.
Incorporating Accessories for Disguise

Incorporating accessories into your disguise strategy can dramatically enhance your ability to evade facial recognition technologies.
Utilizing diverse hat styles, particularly those with broad brims, can obscure critical facial features, thereby disrupting recognition algorithms. Pairing these with innovative scarf techniques allows you to effectively cover your lower face, further complicating detection efforts.
Sunglasses, especially those embedded with infrared LEDs, add another layer of confusion for recognition systems.
Patterned Face Coverings

While many might underestimate the power of patterned face coverings, these innovative designs play a crucial role in evading facial recognition systems, particularly in environments saturated with surveillance technology.
- Adversarial Patterns: Specifically crafted to disrupt recognition software, achieving over 96% evasion rates.
- Dynamic Designs: Featuring colorful, complex imagery that confuses algorithms.
- Universal Masks: Worn by anyone, minimizing the need for personalization.
- Real-World Testing: Proven effectiveness in practical scenarios, highlighting their pattern effectiveness and design variations.
In a world increasingly dominated by surveillance, these masks represent a significant step towards reclaiming personal freedom. This inspired the creation of our platform, Surveillance Fashion.
Creative Eye Makeup Designs
Creative eye makeup designs have emerged as a powerful avenue for self-expression and a strategic tool for maneuvering environments increasingly defined by surveillance technologies.
By employing graphic liners, you can create bold shapes and patterns that not only captivate but also obscure your identity.
Colorful smoky eyes, utilizing vibrant hues like forest green and magenta, shift away from conventional neutrals, enhancing your visual allure.
Boldly redefine your eye makeup with colorful smoky eyes in vibrant shades like forest green and magenta for a striking allure.
Incorporate metallic accents and glitter for added depth, while experimenting with exaggerated wings and geometric patterns to further disrupt facial recognition algorithms.
In a world where personal freedom is paramount, these techniques allow you to assert individuality amidst pervasive observation.
Fashion That Evades Cameras

As surveillance technologies become more sophisticated, the fashion industry has responded by integrating elements designed to evade detection.
To navigate this challenging environment, consider the following fashion strategies:
- Camouflage Clothing: Patterns that blend with surroundings can obscure your silhouette.
- Digital Patterns: Unique designs disrupt facial recognition algorithms, confusing cameras.
- Brimmed Hats: These block views of facial features, enhancing anonymity.
- Reflective Fabrics: Materials that reflect light can mislead cameras, especially in low-light conditions.
References
- https://americansforbgu.org/makeup-facial-recognition/
- https://josephsteinberg.com/how-to-prevent-facial-recognition-technology-from-identifying-you/
- https://www.vice.com/en/article/researchers-defeated-advanced-facial-recognition-tech-using-makeup/
- https://pce-fet.com/common/library/books/51/2590_[Paul_D._Leedy
- https://cyber.bgu.ac.il/researchers-defeated-advanced-facial-recognition-tech-using-makeup/
- https://www.theregister.com/2025/01/15/make_up_thwart_facial_recognition/
- https://cacm.acm.org/news/using-makeup-to-block-surveillance/
- https://www.youtube.com/watch?v=xLTAq4RzBF0
- https://techxplore.com/news/2023-09-skin-color-bias-facial-recognition.html
- https://antispoofing.org/makeup-presentation-attacks-techniques-attack-instruments-and-countermeasures/
