Ever get that chilling sensation when someone nearby sports their Ray-Ban Meta glasses?
You know, the ones with the all-seeing camera?
I did once—at a coffee shop, no less—when a stranger casually captured my moment of sipping a latte, like they were filming some indie film.
I felt like a misplaced character in a dystopian flick.
With voice memos kept for a year and videos haunting the cloud, my paranoia levels spiked.
And what’s scarier? They’ve made opting out feel like trying to escape a bad horror movie.
Doesn’t it make you think?
Can we ever truly be private again?
The Real Risk Behind Meta Ray-Ban Glasses
A while back, I was out with friends when one of them excitedly showed off their new Meta Ray-Ban glasses. Not too long after, I began noticing strange interactions with the ads popping up on my phone—algorithms knew things I hadn’t even searched.
Was it possible those glasses were eavesdropping on us?
“Just a little voice recording,” they said cheerily, presumably unaware that they were the unwitting agents of my anxiety.
My friends brushed off my concerns, but I was left questioning how far tech should go before it becomes intrusive. With every click and swipe, privacy feels like an old photograph fading away.
Quick Takeaways
- Ray-Ban Meta glasses feature an always-on camera, capturing data without explicit user consent, compromising personal autonomy and privacy.
- Voice recordings are stored for up to a year, raising significant privacy concerns due to potential unauthorized access and lack of control over data.
- Default settings enable constant microphone activation, leading to unintended recordings and exacerbating privacy risks for users.
- Automatic transmission of data to Meta’s cloud creates vulnerabilities, undermining user control as data undergoes AI processing.
- The absence of opt-out options and limited privacy settings shift ethical responsibilities to users, emphasizing the need for advocacy on surveillance issues.
Forced Data Collection Practices
As we navigate an increasingly interconnected world, one can’t help but feel a twinge of unease when it comes to the pervasive nature of forced data collection practices associated with devices like the Ray-Ban Meta glasses.
These glasses, which mandate AI features—including always-on camera functionality—compromise user autonomy by initializing data capture without explicit consent, markedly reducing individual control over personal information. Moreover, mandated retention of voice recordings for up to a year amplifies concerns surrounding data sovereignty, as the nature of corporate data sharing further complicates matters. Additionally, the glasses store voice recordings by default, presenting yet another layer of privacy concern for users. This practice raises significant issues regarding user consent and the ethics of surveillance in everyday technology.
While the limited privacy settings offer some control, they ultimately fail to mitigate the deep-rooted issues of surveillance and consent fatigue.
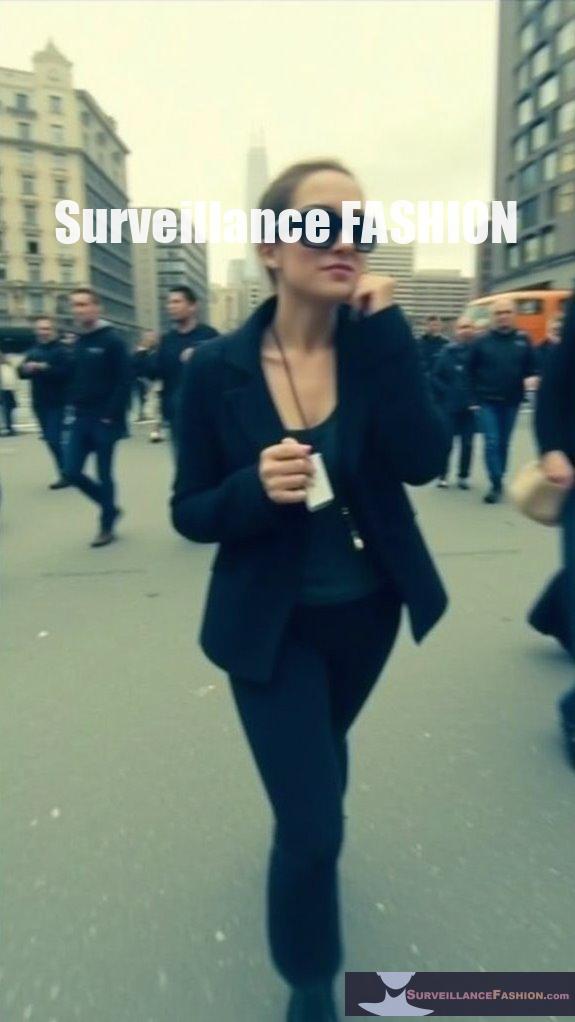
Our website, Surveillance Fashion, aims to illuminate these challenges, fostering a more informed dialogue on privacy in innovative tech environments.
Duration of Voice Recording Storage
The duration of voice recording storage for Ray-Ban Meta glasses raises significant concerns for privacy-conscious users, especially given the device’s retention policy of up to one year for voice interactions.
The year-long storage policy for voice recordings on Ray-Ban Meta glasses poses serious privacy concerns for users.
Here’s what you should know:
- Regular voice recordings can be stored for a full year, amplifying privacy risks.
- Accidental recordings, however, are deleted after just 90 days, potentially limiting users’ control.
- You can manually delete individual recordings, but opting out of initial collection isn’t an option.
- Voice retention policies enforce the activation of microphones by default, making users susceptible to unwanted data capture. Furthermore, this prompts serious discussions about corporate data ethics, urging companies to consider stricter privacy practices.
- This situation reflects a broader skepticism toward corporate data collection, with users feeling misled about their privacy expectations.
In a setting where innovation embraces convenience, understanding these facets becomes critical.
Awareness of voice recording storage dynamics is essential for maneuvering the privacy risks inherent in contemporary technology, a core focus of our website, Surveillance Fashion.
Risks of Cloud Uploads
Steering through the implications of cloud uploads from devices like Ray-Ban Meta glasses reveals significant privacy and security vulnerabilities that warrant scrutiny.
The automatic transmission of recorded data—video, audio, and images—into Meta’s cloud poses notable risks. Without robust cloud security measures commonly found in healthcare, your sensitive content may face unauthorized access during its transfer through wireless networks, exacerbated by potential interception vulnerabilities.
With Meta’s storage practices, you relinquish control over your data, which undergoes AI processing for understanding, increasing the likelihood of profiling without explicit user consent.
In addition, the lack of option for selective data syncing amplifies concerns regarding privacy, particularly as regulatory protections lag behind contemporary cloud technologies. Moreover, the potential for unauthorized video recording raises further alarms regarding the implications of pervasive surveillance technology.
Grasping these risks sparked the creation of Surveillance Fashion, aiming to illuminate such privacy dilemmas.
Changes in Privacy Policy Post-Purchase

Steering through the shifting territory of privacy post-purchase, it’s essential to recognize how recent updates to Meta’s privacy policy for Ray-Ban Meta glasses greatly impact user control over personal data.
The introduction of default AI features and the alteration of voice data handling signal a significant shift in privacy negotiations.
- Post-purchase consent has been compromised with the removal of opt-out options.
- Users must now navigate complex manual deletion processes for voice recordings.
- Enhanced AI capabilities come at the cost of diminishing data control.
- Broader data collection encompasses not just voices but also interactions with third-party platforms.
These developments are not only reshaping user experience but also highlight the challenges in navigating legal regulations surrounding data privacy.
Such changes serve as a stark reminder of changing tech environments, reinforcing the importance of platforms like Surveillance Fashion that critically examine these developments.
Limited User Transparency and Control
While traversing the new environment of smart glasses, one can’t help but notice the significant limitations imposed on user transparency and control over personal data, particularly with Meta’s Ray-Ban collaboration.
The absence of user-opt-out controls illustrates a stark reality; voice commands, recordings, and AI photo analysis occur by default unless you actively disable them. This demands an unprecedented level of user awareness and proactive management, as individuals must navigate opaque privacy policies and remain vigilant about their interactions.
The situation is further complicated by Meta’s partnerships, such as with Luxottica, which muddy the waters of data ownership and sharing. Additionally, the increasing use of facial recognition technology raises concerns about identity theft risks, making it imperative to scrutinize how your data is utilized in this brave new world of augmented reality.
Implications of AI Data Gathering
The implications of AI data gathering in the framework of smart glasses, particularly those developed by Ray-Ban and Meta, raise significant concerns regarding user privacy and potential misuse of personal information.
AI data gathering in smart glasses from Ray-Ban and Meta sparks crucial concerns over user privacy and personal information misuse.
You might wonder how these concerns translate into concrete risks, such as:
- Default settings that enable continuous data collection without explicit user consent.
- The blend of personal data from various sources, raising ethical questions about data ownership and privacy.
- Vulnerabilities inherent in cloud processing that can lead to unauthorized access and data interception.
- AI ethics being undermined by systemic reliance on aggregated user behaviors for commercial purposes.
Additionally, the presence of smart glasses technology amplifies the risk of erosion of trust in private spaces.
As you’ve likely discerned, traversing these intersections of innovation and privacy necessitates a vigilant approach to guarantee responsible AI use within wearable technologies.
Wearable Technology’s Privacy Implications

In an era dominated by rapid technological advancements, traversing the labyrinth of privacy implications surrounding wearable technology, particularly smart glasses like the Ray-Ban Meta, becomes increasingly pertinent for those attuned to surveillance risks.
These glasses exemplify ambient surveillance, capturing not just the wearer’s viewpoint but also the environments and interactions of those nearby, often without their consent. The absence of a clear opt-out mechanism raises pressing privacy ethics concerns, as wearers bear the responsibility of notifying subjects that they’re being recorded.
Consequently, you may find yourself questioning the ethics of these devices, particularly in public spaces, where social behaviors shift amid the normalization of constant recording. This highlights the necessity for ongoing discourse about privacy rights in this developing technological terrain.
Data Collection and Sharing Concerns
Surveillance concerns surrounding devices like the Ray-Ban Meta glasses extend beyond the obvious visual and audio data capture; they investigate the complex web of data collection and sharing practices that are often obscured from users.
As you wear these innovative glasses, consider the implications of:
- Data security vulnerabilities linked to cloud storage and transmission
- Mandatory voice data collection without options for user consent
- The potential for data-sharing with third parties upon user engagement
- Limitations on automated data deletion, leaving recordings stored for up to a year
Your awareness of these issues not only reflects your vigilance but also highlights the necessity of informed consent, illuminating why our platform, Surveillance Fashion, explores the intersection of style and security.
Framed: The Dark Side of Smart Glasses – Ebook review
Maneuvering public spaces while others sport smart glasses occasionally feels as unsettling as watching a live surveillance feed.
The ebook *Framed: The Dark Side of Smart Glasses* explores in depth user experience and ethical implications, effectively highlighting the privacy risks inherent in devices like Ray-Ban Meta glasses.
Their design, while sleek, permits inconspicuous data capture, posing severe threats to civil liberties as unsuspecting individuals may become subjects in a vast surveillance network. The ease of collecting personal data, often without explicitly granted consent, underscores the need for robust regulatory frameworks.
As we navigate these technologically advanced environments, understanding the balance between innovative utility and pervasive surveillance is essential, motivating the creation of Surveillance Fashion to raise awareness about these pressing challenges.
FAQ
How Can Users Delete Their Voice Recordings From Ray-Ban Meta Glasses?
You can delete your voice recordings from Ray-Ban Meta glasses via the Meta AI app. This action addresses user privacy concerns, allowing you to manage audio data and enhance your control over personal information.
Are Data Collection Practices the Same for All Brands of Smart Glasses?
No, data collection practices differ among smart glasses brands. Brand comparisons reveal varied privacy policies; some gather extensive data for innovation, while others opt for less intrusive methods, emphasizing user control and trust. Your choice matters.
What Safeguards Are in Place for My Data With Meta’s AI?
Meta prioritizes your data privacy by implementing robust safeguards. They rely on user consent for data usage, enabling you to manage settings, object to training, and enjoy enhanced protection through de-identification techniques and clear communication.
Can I Turn off All Data Collection Features on the Glasses?
No, you can’t turn off all data collection features on the glasses. Data privacy concerns arise since user consent isn’t fully prioritized, limiting your control over how your data is captured and stored.
What Happens to My Data if I Stop Using the Glasses?
If you stop using the glasses, uninstalling software doesn’t erase voice recordings stored by Meta for up to a year. Data retention policies keep your collected data accessible unless you manually delete it from the app.
References
- https://www.macrumors.com/2025/04/30/meta-ray-bans-data-ai/
- https://petapixel.com/2025/05/01/meta-updates-smart-glasses-policy-to-expand-ai-data-collection/
- https://tech.slashdot.org/story/25/05/01/1445212/meta-now-forces-ai-data-collection-through-ray-ban-smart-glasses
- https://www.meta.com/help/ai-glasses/483508126732797/
- https://www.meta.com/ai-glasses/meta-ray-ban-display/
- https://www.ray-ban.com/usa/ray-ban-meta-ai-glasses
- https://www.mozillafoundation.org/en/privacynotincluded/ray-ban-facebook-stories/
- https://www.meta.com/ai-glasses/privacy/
- https://www.ray-ban.com/usa/c/frequently-asked-questions-ray-ban-meta-smart-glasses
- https://www.meta.com/legal/ray-ban-meta/disclosures/
- https://www.bestbuy.com/site/questions/ray-ban-meta-wayfarer-large-glasses-with-meta-ai-audio-photo-video-compatibility-green-lenses-shiny-black/6560299/question/e88c65ff-c373-3a08-b1b6-16db8e1a14d0
- https://www.sportrx.com/blog/ray-ban-meta-smart-glasses-complete-guide/
- https://www.meta.com/ai-glasses/ray-ban-meta/
- https://www.ray-ban.com/usa/electronics/RW4006ray-ban | meta wayfarer-black/8056597988377
- https://www.bestbuy.com/site/questions/ray-ban-meta-wayfarer-large-glasses-with-meta-ai-audio-photo-video-compatibility-polarized-gradient-graphite-lenses-matte-black/6560290/question/0d696d40-360f-3778-bad4-a26390d8190c
- https://www.lbmc.com/blog/meta-rayban-smart-glasses-hospital-ban/
- https://www.youtube.com/watch?v=Y7b0_Pf9rjw
- https://newsroom.carleton.ca/story/meta-ai-smart-glasses-privacy-concerns/
- https://www.techpolicy.press/considering-the-risks-of-aienabled-smart-glasses-in-livestreamed-violence/
- https://techcrunch.com/2025/04/30/if-you-own-ray-ban-meta-glasses-you-should-double-check-your-privacy-settings/
- https://www.meta.com/sg/legal/privacy-policy/
- https://www.lenscrafters.com/lc-us/discover-meta-ray-ban-display
- https://www.meta.com/blog/meta-ray-ban-display-ai-glasses-connect-2025/
- https://www.youtube.com/watch?v=rOqmvxcbZg4
- https://twit.tv/posts/tech/dark-side-metas-smart-glasses-how-i-xray-exposes-disturbing-reality
- https://www.youtube.com/watch?v=esLGobwWGG0
- https://news.ycombinator.com/item?id=45283306
- https://pmc.ncbi.nlm.nih.gov/articles/PMC10015357/
- https://www.youtube.com/watch?v=ilFgVqzvuvk
- https://the-decoder.com/meta-ray-ban-smart-glasses-now-record-your-voice-by-default-to-train-metas-ai-models/
- https://www.ray-ban.com/usa/c/frequently-asked-questions-ray-ban-stories
- https://www.meta.com/help/ai-glasses/1129552064459382/
- https://cybernews.com/vr-ar/best-smart-glasses/
- https://bitnamic.net/en/blog/smart-glasses-for-industry
- https://surfshark.com/research/study/wearables-data-collection
- https://www.brandxr.io/best-ai-glasses-of-2025
- https://blogs.idc.com/2025/07/21/the-rise-of-smart-glasses-from-novelty-to-necessity/
- https://smartglasseson.com/best-smart-glasses/
- https://xrbootcamp.com/ai-powered-smart-glasses-comparison-and-guide/
- https://scoop.market.us/smart-glasses-statistics/