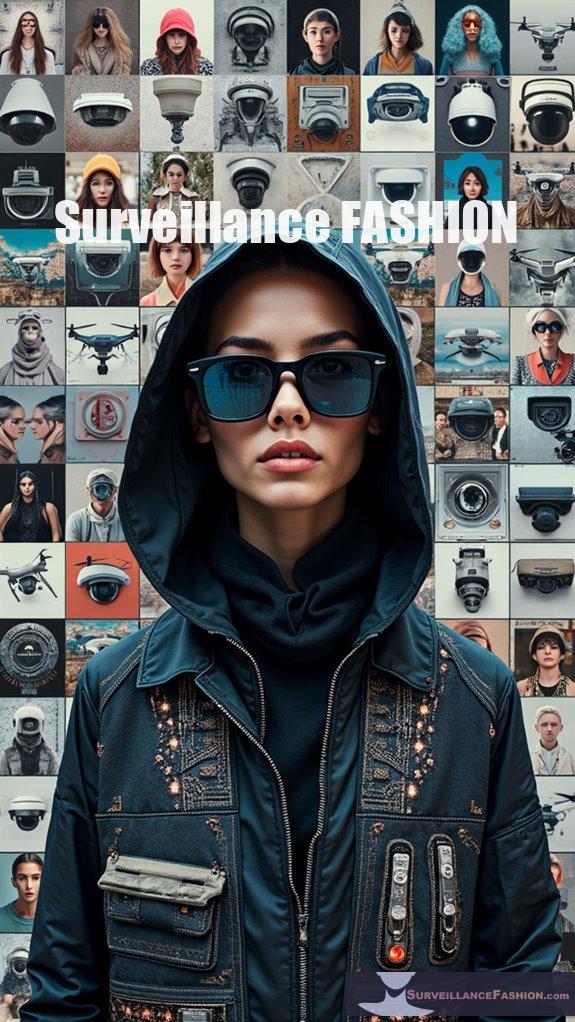
To keep my privacy intact in a surveillance-heavy world, I’ve turned to a quirky tool: anti-surveillance fashion.
Seriously, who knew a stylish hoodie could be my secret weapon?
I remember one day, strutting down the street, feeling like a secret agent. My friends laughed at my getup, but little did they know I was armed with an extra layer of anonymity.
With end-to-end encryption and client-side keys at play, I felt like I had more control over my digital life than ever.
And yeah, it’s a bit of a cloak-and-dagger routine, but hey, realism is my aesthetic.
Do you ever wonder how secure you truly are in this tech jungle?
—
The Time I Wore My Privacy Like a Cloak: Embracing Anti-Surveillance Fashion
One afternoon, in a busy café, I noticed a guy with one of those flashy tracking devices, and it made me cringe.
I suddenly felt trapped, as if my every move was being monitored. That’s when I decided to wear my oversized jacket – complete with reflective fabric.
It wasn’t just a fashion choice that day; it was a statement. It shielded me, making me feel less visible in a sea of prying eyes.
Those moments remind me why anti-surveillance fashion is vital. It blends style with a touch of rebellion. Retro technology, like fabric with privacy features, and even designs that disrupt facial recognition are no longer just fantasies. They’ve become essential in navigating today’s digital maze.
Have you ever considered how your style might shield you from unwanted scrutiny?
Quick Takeaways
- Implement end-to-end encryption (E2EE) to ensure only intended recipients can access sensitive messages and maintain privacy during communication.
- Practice metadata minimization by collecting only essential data and implementing role-based access controls to limit unnecessary exposure.
- Utilize automated lifecycle management to adapt encryption policies and ensure compliance with evolving data protection standards.
- Advocate for user consent by requiring clear, informed consent before data collection and providing easy opt-out options.
- Employ traffic obfuscation methods, such as SSL/TLS and data masking, to disguise data transmission and protect against external monitoring.
End-to-End Encryption Implementation

End-to-End Encryption (E2EE) implementation is fundamental in safeguarding communication, especially considering the increasing threats to privacy in our digital environment. By meticulously selecting protocols like AES-256, RSA, or PGP, you guarantee robust security against potential cyber threats. The rise of client-side scanning emphasizes the necessity of stringent encryption methods to ensure privacy.
In E2EE, each device generates a unique public/private key pair; this means your public key is shared, while your private key remains securely with you. This dynamic enables encrypted messages, confirming only the intended recipients can decipher them.
Using secure channels such as HTTPS enhances transmission integrity, shielding against outside interference. Furthermore, E2EE eliminates the central point of failure, significantly reducing vulnerability to data breaches.
For instance, automating key management—seen in platforms like PreVeil—can simplify processes, enhancing adoption. Given our purpose at Surveillance Fashion, understanding these intricacies is vital in traversing the complex domain of digital privacy.
Client-Side Encryption Strategies
As digital communication evolves, the significance of safeguarding information at the client level becomes increasingly evident.
Implementing client-side encryption strategies can enhance your data protection considerably. Here are several key considerations:
- Encrypt data before transmission to secure sensitive information.
- Maintain ownership of encryption keys, ensuring only you can access your data.
- Keep data encrypted throughout transit and storage, reducing interception risks.
- Integrate seamlessly into existing workflows to protect personal and organizational data.
- Comply with regulations like GDPR and HIPAA effortlessly. In addition, leveraging client-side encryption helps to ensure that your sensitive data stays private and secure from unauthorized access.
These tactics position you to assert control over your confidential communications, ultimately reducing vulnerability against third-party breaches while promoting an environment that cherishes privacy.
At Surveillance Fashion, our goal is to empower users like you to regain authority over your digital interactions.
Zero-Knowledge Encryption Benefits
In an age where data privacy concerns loom large, understanding the five compelling benefits of zero-knowledge encryption becomes vital for individuals and organizations alike.
Firstly, zero-knowledge encryption guarantees user-controlled data access, meaning only you hold the encryption keys, shielding your data from even the most invasive legal inquiries.
Furthermore, data breaches at service providers expose only ciphertext, rendering stolen information useless without access to your keys, thereby minimizing risks like identity theft and reputational damage.
In addition, zero-knowledge systems simplify regulatory compliance with GDPR and HIPAA, demonstrating proactive privacy measures.
They also facilitate strong authentication without revealing sensitive user data, mitigated by cryptographic proofs.
Finally, across all states—at-rest, in-transit, and in-use—data remains protected, a principle we emphasize at Surveillance Fashion to empower user privacy.
Metadata Minimization Techniques

Effective metadata minimization techniques are essential for enhancing privacy and safeguarding sensitive information in today’s data-driven environment.
By adopting strategic methodologies, you can considerably reduce metadata exposure and its associated risks:
Adopting strategic methodologies significantly reduces metadata exposure and its related risks.
- Collect only critical metadata relevant to defined objectives.
- Map data flows to pinpoint sources and limit unnecessary details.
- Utilize data masking to obscure sensitive elements while retaining utility.
- Automate retention schedules for timely data deletion, ensuring compliance with regulations.
- Implement role-based controls to grant data access only to those with a legitimate need.
Embracing these practices not only streamlines data governance but also aligns with our commitment at Surveillance Fashion to empower users in protecting their digital identities while traversing complex privacy challenges. Furthermore, understanding the implications of modern surveillance tools is crucial for effective privacy management in this evolving landscape.
Traffic Obfuscation Methods
While modern digital communications are rife with vulnerabilities, traffic obfuscation methods serve as essential protective mechanisms designed to enhance user privacy and safeguard sensitive data.
These methods leverage advanced protocols, like SSL/TLS, to encrypt packet contents, effectively disguising data from prying eyes. Techniques such as Base64 encoding transform recognizable information, while packet padding randomizes sizes, thereby complicating traffic pattern detection.
Moreover, tunneling protocols encapsulate data within trusted structures, like HTTPS or DNS, rendering suspicious activities inconspicuous.
Tools like Stunnel and Shadowsocks play crucial roles in masking VPN usage, facilitating stealthy communication.
At Surveillance Fashion, we believe these innovative tactics are significant in countering intrusive surveillance, empowering users to reclaim their online experience through robust privacy solutions.
Open-Source Encrypted Communication
As the digital environment evolves, ensuring secure communication has transformed into a paramount concern for users traversing an increasingly surveillance-heavy world.
Open-source encrypted communication platforms harness decentralized infrastructure, prioritizing user anonymity and resilience against censorship. Here are some critical aspects of these systems:
- Utilize decentralized peer-to-peer networks, eliminating central servers
- Employ IP address masking to protect user locations
- Avoid personal information input during account creation
- Support private/public key pairs for anonymous identity management
- Facilitate self-destructing messages to limit data persistence
Innovative platforms like Utopia, Jami, and Session exemplify these features, empowering users with enhanced privacy and security.
At Surveillance Fashion, we emphasize understanding these technologies, equipping individuals for a future where secure communication is essential.
Strong Key Management Practices

In the domain of secure communication, where open-source encrypted platforms offer users various protective features, strong key management practices become equally essential in safeguarding sensitive data. By implementing thorough key management policies, you establish a framework outlining responsibilities throughout the key lifecycle, from creation to destruction. This includes specifying access controls to minimize unauthorized use and reinforcing compliance via rigorous staff training.
Moreover, limiting each key’s purpose to singular tasks reduces security risks and simplifies management. Storing keys within hardware security modules (HSMs) guarantees isolated environments, while automated lifecycle management mitigates human error.
It’s particularly significant to regularly audit and adapt your key policies against changing threats, including advancements in quantum computing, thereby maintaining robust defenses in your encrypted communication environment.
Decentralized Architecture Advantages
Decentralized architecture fundamentally transforms the terrain of data security and privacy, enhancing resilience and control in an increasingly interconnected world.
This innovative framework brings several key advantages:
- Eliminates single points of failure, making it difficult for attackers to compromise entire systems.
- Maintains immutable records, ensuring transparent and accountable transactions.
- Empowers users with control over their identities through decentralized identity mechanisms.
- Supports dynamic scalability, adapting security measures to specific needs.
- Fosters a company-wide understanding of information security, embedding responsibility across departments.
Compliance With GDPR and Data Protection Laws
Maneuvering the terrain of compliance with GDPR and data protection laws isn’t merely a regulatory obligation; it’s an imperative that guarantees the safeguarding of personal data amidst rising cyber threats.
To guarantee compliance and protection, consider the following critical measures:
| Measure | Description | Importance |
|---|---|---|
| Encryption | Utilize AES-256 for data security | Protects against unauthorized access |
| Key Management | Implement strong key controls | Guarantees data remains intelligible and secure |
| Documentation | Maintain clear records of data processing | Demonstrates accountability and enhances security |
| Staff Training | Educate employees on data protection policies | Builds an informed workforce aware of compliance responsibilities |
| Continuous Risk Assessments | Regularly evaluate encryption strategies | Adapts to changing threats, ensuring ongoing data protection standards |
Advocacy for User Consent and Privacy Protection
While the digital terrain continually evolves and reshapes privacy considerations, advocating for user consent remains a cornerstone of building trust between organizations and individuals.
To effectively advance this advocacy, consider these essential tactics:
- Guarantee consent is explicit, informed, and freely given before collecting personal data.
- Use plain language in notices to enhance user comprehension and transparency.
- Design unambiguous consent requests that are separate from other agreements.
- Offer granular options so users can choose specific data processing activities.
- Facilitate frictionless opt-out processes that allow users to manage their consent seamlessly.
Adopting these measures can help cultivate a culture of trust and transparency, reflecting the commitment that drove the creation of Surveillance Fashion, guaranteeing a user-centric approach in an increasingly monitored world.
Digital Monitoring Techniques
What happens when digital monitoring techniques intersect with our daily online lives?
In an age where social media posts geotag our movements and reveal connections, it’s vital to understand the implications. Investigators can track individuals through GPS devices or analyze online communications, recovering data that might reveal illicit activities.
In today’s interconnected world, social media and GPS tracking expose our movements, highlighting the critical need to consider privacy implications.
This monitoring extends to audio and video surveillance technologies, capturing evidence in real-time through sophisticated systems like AI-enhanced CCTV.
The integration of these techniques with advanced analytics offers unprecedented perspective into human behavior, yet it raises pressing concerns about privacy rights.
As we navigate this digital environment, fostering awareness about the fine line between safety and intrusion becomes essential, especially in a world driven by innovation, where our identities can easily become fodder for both scrutiny and protection.
Fashion Influenced by Surveillance Technology
In a terrain shaped by relentless digital monitoring, fashion isn’t merely an expression of personal identity but a canvas for the intersection of technology and data surveillance. As innovation intertwines with style, consider these trends:
- Smart fabrics that monitor biometric data, seamlessly blending health awareness into daily wear.
- Conductive threads enabling real-time data transmission, presenting both utility and privacy risk.
- Fashion brands experimenting with garments that prioritize aesthetics while incorporating surveillance tech.
- The rise of digital fashion using blockchain, fostering transparency yet posing data security dilemmas.
- Eye-catching designs inspired by surveillance aesthetics, critiquing monitoring culture while ensuring design relevance.
EU Chat Control Anti-Surveillance and Encryption Defense Tactics
As the EU navigates the contentious waters of digital communication regulation, the impending Chat Control proposal raises significant concerns regarding privacy rights and encryption integrity.
You must consider employing tactics that prioritize robust encryption methods while advocating for digital privacy. Utilizing end-to-end encryption prevents unauthorized access, mitigating the risks of backdoors in communication platforms, while adopting decentralized technologies fosters user autonomy.
Employ robust encryption and decentralized technologies to safeguard user privacy and prevent unauthorized access.
Engaging in grassroots movements alongside national and international advocacy groups can amplify your voices against invasive surveillance directives.
Moreover, consider utilizing Virtual Private Networks (VPNs) that emphasize user privacy, which can counteract mandated data logging.
EU Chat Control Proposal Risks and Anti-Surveillance Strategies Ebook review
The looming EU Chat Control proposal embodies a profound intersection of technology, law, and ethics, presenting existential risks to encryption and privacy inherent in digital communications.
Consider these critical aspects:
- Mandates mass scanning of private communications, weakening encryption.
- Implications for whistleblowers, journalists, and vulnerable groups.
- High false positive rates risking wrongful incrimination.
- Systemic vulnerabilities that cybercriminals could exploit.
- Legal concerns, including clashes with the EU Charter of Fundamental Rights.
With the potential for mass surveillance creeping beyond intended targets, it’s essential to comprehend the broader implications on civil liberties.
As the EU considers this proposal, the perspectives from our ebook can guide you in steering through these complexities, ensuring you’re well-equipped to defend your privacy and encryption amid increasing surveillance pressures.
EU Chat Control FAQ
What Is the Role of Encryption in Securing Iot Devices?
Encryption acts as the digital fortress safeguarding IoT devices, preventing unauthorized data access and ensuring integrity in communication.
By encrypting data at rest and in transit, you thwart potential breaches, enhancing user privacy.
This secure framework not only employs protocols like TLS to protect data transmission but also enables safe device authentication, maintaining a robust ecosystem.
As innovative technologies flourish, such as those reflected on Surveillance Fashion, encryption remains pivotal in preserving data sanctity amidst growing threats.
How Does Quantum Computing Threaten Current Encryption Methods?
Quantum computing threatens current encryption methods by efficiently breaking conventional systems like RSA and ECC through algorithms such as Shor’s and Grover’s.
By leveraging quantum bits, a sufficiently powerful quantum computer could decrypt sensitive data rapidly, compromising online security.
This impending capability, anticipated around 2028-2030, urges you to contemplate alternative strategies, such as post-quantum cryptography, to safeguard your information.
Hence our initiative at Surveillance Fashion to highlight innovative solutions for advancing digital privacy concerns.
Are There Legal Consequences for Failing to Implement Encryption?
Yes, there are significant legal consequences for failing to implement encryption. Organizations like healthcare providers and businesses under GDPR face hefty fines, which can soar into millions annually for non-compliance.
For instance, under HIPAA, penalties can reach $1.5 million per violation. Furthermore, willful neglect could incur criminal penalties, including imprisonment.
These repercussions not only strain fiscal resources but also damage organizational trust, emphasizing the critical need for robust encryption practices in today’s data-driven environment.
How Can Individuals Verify if a Service Uses End-To-End Encryption?
To determine if a service employs end-to-end encryption (E2EE), you’ll want to read their privacy policy carefully, looking for explicit statements regarding E2EE capabilities.
Verify that users—not intermediaries—hold the encryption keys.
Furthermore, utilize client-side encryption tools and validate key management protocols.
Pay attention to third-party audits and community feedback, as these can provide valuable perspectives into a service’s encryption efficacy, ensuring you’re not left in the dark about your data’s safety.
What Are the Costs Associated With Implementing Encryption Solutions?
Implementing encryption solutions involves various costs.
You’ll face significant performance costs, as encryption and decryption demand substantial CPU resources, especially with complex algorithms like AES-256.
Storage expenses also rise, stemming from additional volume due to metadata and padding.
In addition, key management necessitates secure infrastructure, with potential maintenance costs exceeding $372.5K.
Software licensing can vary, often requiring substantial investment, but these upfront costs pale compared to potential breaches’ financial repercussions.
Consider organizations like IBM or Microsoft for innovative solutions.
References
- https://randtronics.com/why-encryption-is-a-mandatory-privacy-tool-in-2025/
- https://www.encryptionconsulting.com/compliance-trends-of-2025/
- https://moldstud.com/articles/p-top-10-data-security-solutions-to-protect-sensitive-information-in-2025
- https://trainingcamp.com/articles/encryption-best-practices-2025-complete-guide-to-data-protection-standards-and-implementation/
- https://solutionsreview.com/backup-disaster-recovery/data-privacy-day-insights-from-industry-experts/
- https://www.kiteworks.com/secure-file-sharing/real-world-examples-of-end-to-end-encryption/
- https://www.preveil.com/blog/end-to-end-encryption/
- https://www.splashtop.com/blog/what-is-end-to-end-encryption
- https://innovativeii.com/10-steps-to-end-to-end-encryption/
- https://www.sidekickinteractive.com/uncategorized/5-steps-to-implement-end-to-end-encryption-in-apps/
- https://www.tigrisdata.com/blog/client-side-encryption/
- https://www.impossiblecloud.com/glossary/client-side-encryption
- https://utimaco.com/news/blog-posts/how-choose-client-side-encryption-cloud-security
- https://learn.microsoft.com/en-us/answers/questions/1723580/why-we-need-client-side-encryption-not-client-side
- https://www.virtru.com/blog/file-encryption/client-side
- https://www.hivenet.com/post/zero-knowledge-encryption-the-ultimate-guide-to-unbreakable-data-security
- https://blog.pcloud.com/5-reasons-zero-knowledge-encryption-should-matter-to-you/
- https://bitwarden.com/resources/zero-knowledge-encryption/
- https://www.keepersecurity.com/resources/zero-knowledge-for-ultimate-password-security.html
- https://blog.cubbit.io/what-is-zero-knowledge-encryption/
- https://www.piiano.com/blog/data-minimization
- https://holisticai.readthedocs.io/en/latest/getting_started/security/metrics/data_minimization.html
- https://www.kiteworks.com/risk-compliance-glossary/data-minimization/
- https://www.centraleyes.com/glossary/data-minimization/
- https://www.decube.io/post/metadata-management-concepts
- https://armur.ai/ethical-hacking/defense/inv-1/traffic-obfuscation/
- https://arxiv.org/html/2504.07543v1
- https://www.comparitech.com/blog/vpn-privacy/vpn-obfuscation/
- https://library.fiveable.me/network-security-and-forensics/unit-4/obfuscation-techniques/study-guide/DMrSqXat2Mz4SL1N
- https://www.talend.com/resources/data-obfuscation/
- https://trueconf.com/blog/reviews-comparisons/secure-messengers
- https://jami.net
- https://zapier.com/blog/best-secure-messaging-app/
- https://cyberinsider.com/secure-encrypted-messaging-apps/
- https://www.tomsguide.com/reference/best-encrypted-messaging-apps
- https://www.liquidweb.com/blog/encryption-key-management-best-practices/
- https://www.ssl.com/article/key-management-best-practices-a-practical-guide/
- https://www.crashplan.com/blog/encryption-key-management-what-you-need-to-know/
- https://media.defense.gov/2024/Mar/07/2003407858/-1/-1/0/CSI-CloudTop10-Key-Management.PDF
- https://www.thalestct.com/wp-content/uploads/2022/09/Best-Practices-for-Cryptographic-Key-Management.pdf