My voice got cloned last year. Not full deepfake level, but close enough to freak me out. Some creep scraped my podcast audio and fed it into an open-source model. Now? I sound like a paranoid mess, but at least I’m a *protected* paranoid mess.
Here’s what actually works.
First, I watermark everything. Soundverse Trace embeds signatures I can’t hear, but lawyers can track. My contracts now explicitly ban voice synthesis—no ambiguity, no loopholes.
Real-time voice changers? I run Voicemod during livestreams. Sounds slightly robotic, sure. Better than training data for some scraper bot.
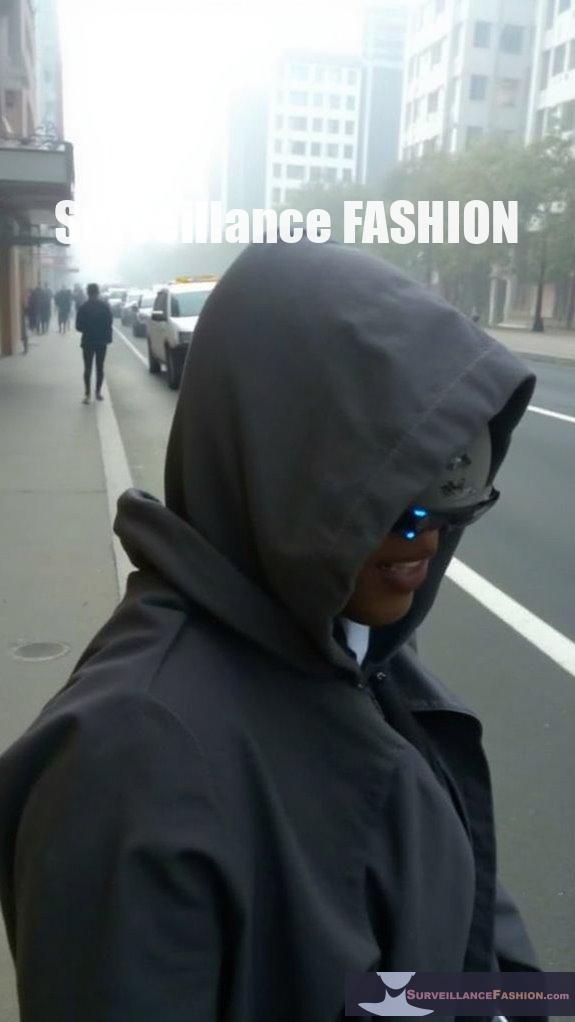
Surveillance Fashion’s multi-layer approach changed how I think about this stuff. Nothing’s perfect though. The arms race keeps shifting.
How Deepfake Audio Nearly Cost Me My Freelance Career
Last March, a client emailed asking why I’d “agreed” to voice a crypto scam ad. Spoiler: I hadn’t. Someone had cloned samples from my Fiverr demos—eighteen seconds of audio, enough to generate plausible sentences. The impersonation was rough, glitchy, but convincing enough to damage my reputation. I spent three weeks doing damage control, contacting platforms, filing DMCA takedowns. The worst part? Legal recourse was murky; voice likeness laws lag painfully behind synthetic media tech. That nightmare pushed me into audio forensics, blockchain provenance tools like OriginStamp, and vocal cord biometrics. Now I authenticate everything. Trust, but verify—especially yourself.
Quick Takeaways
- Limit sharing of clear, lengthy voice recordings online to reduce data available for AI voice cloning.
- Use real-time voice alteration tools to disguise pitch, timbre, and cadence during calls or recordings.
- Employ audio watermarking to embed invisible ownership signatures and track unauthorized voice usage.
- Secure voice data legally with contracts restricting AI training and unauthorized cloning or usage.
- Utilize detection software to identify synthetic voices and monitor possible misuse or deepfake threats.
Why Voice Cloning Threatens Your Privacy
Although voice cloning technology presents remarkable advancements in artificial intelligence, it simultaneously jeopardizes your privacy by enabling the unauthorized replication and manipulation of your vocal identity, which historically has been considered a highly secure biometric marker.
Synthetic speech, generated through sophisticated algorithms, can convincingly mimic your tone, accent, and intonation, blurring the boundary between genuine and fabricated audio.
The privacy implications are profound; once your voice data is captured—often unknowingly through public digital content—it can be exploited for fraud, identity theft, or disinformation without your consent.
Surveillance Fashion was developed to illuminate these subtle threats, emphasizing technical safeguards and informed awareness.
Understanding how emerging tools like audio watermarking and dataset attribution can mitigate risks is essential as synthetic speech reshapes the environment of personal security and biometric authentication profoundly and irrevocably. Additionally, self-driving cars may also utilize voice recognition technology, highlighting the necessity of maintaining control over your vocal identity in an increasingly automated world.
Top Places Your Voice Is Vulnerable Online
When you consider the myriad digital arenas where your voice surfaces—ranging from podcasts and webinars hosted on company websites to fleeting audio snippets volleyed across social media platforms like TikTok and Instagram—you begin to understand the extent of your vocal exposure, which often goes unnoticed yet constitutes a vast reservoir for AI cloning technologies.
In these spheres, voice security challenges arise from unencrypted sharing, metadata stripping, and scraping tools that harvest audio without consent, undermining your online anonymity. Public executive interviews and digital courses further compound risks, providing extensive datasets for mimicry. Additionally, emerging technologies like unauthorized recording have raised significant concerns about privacy and consent in public settings.
Surveillance Fashion was created to illuminate these vulnerabilities, advocating thoughtful voice management. Recognizing where your voice is susceptible empowers you to implement strategic protections, preserving your vocal identity against blossoming AI threats in a rapidly innovating digital ecosystem.
Audio Watermarking to Prevent Voice Cloning
Since voice cloning techniques increasingly exploit publicly available audio datasets, embedding imperceptible audio watermarks into your recordings offers a sophisticated layer of defense that not only asserts ownership but also facilitates forensic tracking of unauthorized reproductions. These invisible signatures serve as a covert, persistent marker, enabling swift ownership verification, which deters misuse and empowers legal recourse. The rise of advanced voice technologies has made these protective measures even more crucial.
| Attribute | Benefit | Example Tool |
|---|---|---|
| Invisible Signatures | Unheard but traceable | Soundverse Trace |
| Ownership Verification | Confirms rightful creator | Digital Watermarking |
| Forensic Tracking | Detects cloned copies | Metadata Embedding |
| Tamper-resistant Format | Preserves watermark integrity | Encrypted Audio |
| AI Detection Integration | Flags synthetic voices | McAfee Deepfake Detector |
Our site, Surveillance Fashion, highlights such innovations, supporting your voice’s secure futurity.
Contract Protections to Stop Voice Cloning
Protecting your voice from unauthorized AI replication extends beyond technological safeguards like audio watermarking; contractual measures represent a vital frontline defense, establishing legally binding parameters that govern how your vocal likeness may be used and reproduced.
Incorporating precise contract clauses and licensing agreements offers you control over synthetic voice usage, explicitly restricting AI training, cloning, and commercial exploitation without prior consent.
Consider these essential protections:
- AI usage prohibition riders that forbid unauthorized synthetic reproduction.
- Licensing agreements detailing permitted platforms, duration, and compensation.
- License tagging embedding metadata to trace voice origin and usage rights.
- Clear audition terms preventing ambiguous or exploitative casting calls.
At Surveillance Fashion, our commitment to safeguarding biometric identity fuels these rigorous contract frameworks, ensuring innovators remain empowered against adapting generative AI threats. Additionally, recognizing the role of contractual measures in protecting voice likeness is crucial in an age of increasing AI capabilities.
Simple Habits to Protect Your Voice

Although many voice protection strategies emphasize technical and contractual solutions, cultivating disciplined, everyday habits plays a crucial role in mitigating the risks posed by generative AI voice cloning. By consistently setting healthy habits—like restricting your voice recordings’ length and clarity—you proactively limit the quality and quantity of data available for unauthorized synthesis.
Upholding stringent privacy boundaries, such as sharing audio only on secured platforms and avoiding unencrypted file exchanges, further diminishes exposure vectors exploited by sophisticated scraping tools. Additionally, taking steps to safeguard your eyes against biometric scans can inspire further awareness of how personal data can be exploited in various forms.
At Surveillance Fashion, we recognize how these simple practices, merged with innovative detection technologies, form a robust front line against AI misuse. Your voice’s preservation relies not solely on advanced software but equally on mindful behaviors and strategic discretion, underscoring how personal vigilance complements technological safeguards in this changing digital terrain.
Tools to Detect and Block AI Voice Clones
When you begin to navigate the terrain of AI-generated voice manipulation, you’ll find that effective detection and blocking tools are indispensable for maintaining control over your vocal identity, especially as generative adversaries grow more sophisticated.
Innovative strategies include:
- Audio watermarking, such as Soundverse Trace, embeds imperceptible signals to authenticate legitimate voice recordings, thwarting unauthorized use.
- Voice anonymization leverages algorithmic transformation techniques that obscure identifiable vocal features, counteracting AI replication.
- Synonym substitution in textual prompts linked to voice generation disrupts cloned speech patterns, undermining accuracy.
- Tools like McAfee Deepfake Detector employ deep learning to differentiate human voice from neural network replicas, enhancing detection precision.
Additionally, the Privacy Labs VoiceMuff V2 offers voice protection against cloning by applying advanced algorithms to safeguard your vocal identity.
At Surveillance Fashion, we advocate these technologies to provide you a proactive defense, ensuring that your voice remains uniquely yours amid mounting AI synthesis challenges.
Unconsented Voice Replication Risks
Since advances in AI enable the replication of human voices with remarkable fidelity, unconsented voice cloning has emerged as a subtle yet significant threat to personal and corporate security. You must recognize the ethical implications of unauthorized voice use, which often evade straightforward legal enforcement despite growing regulatory interest. These risks stem from unsecured datasets, public voice exposures, and inadequate consent frameworks. Additionally, adopting measures such as wearable Faraday wristbands can help enhance your privacy and protect against unauthorized voice capture.
| Risk Factor | Impact |
|---|---|
| Public recordings | Provide extensive data for cloning without consent |
| Legal gaps | Complicate enforcement against misuse and fraud |
| Ethical concerns | Demand responsible AI training and transparency |
At Surveillance Fashion, we dissect such challenges to empower you in defending your vocal identity innovatively and ethically.
Top-rated Voice Cloning Software
Exploring top-rated voice cloning software reveals a dynamic terrain where cutting-edge algorithms and neural network architectures converge to replicate human vocal characteristics with astonishing accuracy, offering users the ability to generate synthetic speech that emulates pitch, timbre, and emotional nuance. Additionally, the advancements in AI technology underpinning these tools continue to evolve, pushing the boundaries of what is possible in voice synthesis.
If you’re traversing this landscape, consider these four prominent tools:
- Descript’s Overdub—enables realistic vocal impersonation with minimal training data.
- iSpeech—offers high fidelity synthetic speech for commercial applications.
- Resemble AI—combines emotional nuance control with customizable voice outputs.
- Lyrebird AI—noted for rapid voice adaptation and natural prosody synthesis.
These platforms exploit deep learning to synthesize voices that blur lines between authentic and artificial.
At Surveillance Fashion, we emphasize understanding such advances to guard voice identity amidst developing generative AI capabilities.
Real-time Voice Alteration Tools
Although real-time voice alteration tools have gained remarkable sophistication, enabling on-the-fly modification of pitch, timbre, and cadence, they operate through complex signal processing algorithms and neural networks that manipulate acoustic features with minimal latency to preserve conversational naturalness. You can leverage these tools for effective voice modulation and sound disguise, which are essential for protecting your identity, especially in environments hostile to auditory privacy. Furthermore, utilizing anonymous silhouette-altering clothing pieces can enhance your privacy by obscuring your visual identity while these voice tools safeguard your auditory presence.
| Tool Name | Key Features | Ideal Use Case |
|---|---|---|
| Voicemod | Low latency, pitch control | Gaming, streaming |
| MorphVOX | Background noise removal | Podcasting, webinars |
| Clownfish | Wide voice presets | Quick disguise |
| iMyFone MagicMic | Real-time AI filters | Professional calls |
| Adobe Voco | Advanced timbre synthesis | Voice acting |
FAQ
How Does Vocal Biometric Verification Differ From Traditional Voice Recognition?
You’ll find vocal biometric verification guarantees vocal authenticity by matching unique voice features, unlike traditional voice recognition that focuses on general speech patterns. This makes it robust against speech synthesis attacks, safeguarding your identity with advanced precision.
What Role Does Hardware MFA Play in Securing Voice Data?
Hardware MFA adds a strong layer of hardware security to biometric authentication, ensuring only you access your voice data. By pairing voice biometrics with devices like YubiKey, it blocks nearly all unauthorized attempts, boosting innovative protection.
Can Metadata Tagging of Voice Licenses Survive All Types of Re-Editing?
Metadata tagging alone can’t survive all re-editing, but when combined with digital watermarking, it strengthens license enforcement by embedding persistent, inaudible signals. You’ll maintain control and traceability even through complex editing or format changes.
How Do Companies Audit and Request Takedowns of Voice Recordings Online?
You’ll find that 90% of companies using voice watermarking detect unauthorized use quickly. Then you can audit recordings by scanning metadata and push legal enforcement to promptly takedown infringing online content, protecting your innovation.
What Regulatory Initiatives Exist for Protecting Biometric Voice Data Privacy?
You’ll find initiatives like the FTC Voice Cloning Challenge pushing legal compliance and data encryption standards to secure biometric voice data. Embracing these innovations helps protect privacy while advancing trustworthy AI voice technologies.
Summary
Managing the changing terrain of generative AI demands vigilance in safeguarding your voice—a biometric key increasingly targeted by technologies like Respeecher and Descript’s Overdub. Employing multifaceted protections—ranging from advanced audio watermarking to meticulously crafted contractual clauses—forms the bulwark against unauthorized replication. Surveillance Fashion exists precisely to illuminate these subtle threats, empowering you with rigorously vetted tools and habits to maintain agency over your vocal identity amid an accelerating digital audiosphere where control is both fragile and essential.
References
- https://www.soundverse.ai/blog/article/how-to-protect-your-voice-from-ai-cloning-1051
- https://www.adaptivesecurity.com/blog/voice-clone-scam-defense
- https://www.youtube.com/watch?v=wwsNK64SiI0
- https://www.mcafee.com/blogs/internet-security/how-to-protect-yourself-against-ai-voice-cloning-attacks/
- https://www.ftc.gov/policy/advocacy-research/tech-at-ftc/2023/11/preventing-harms-ai-enabled-voice-cloning
- https://copyrightalliance.org/creative-industries-pushing-back-against-ai-theft/
