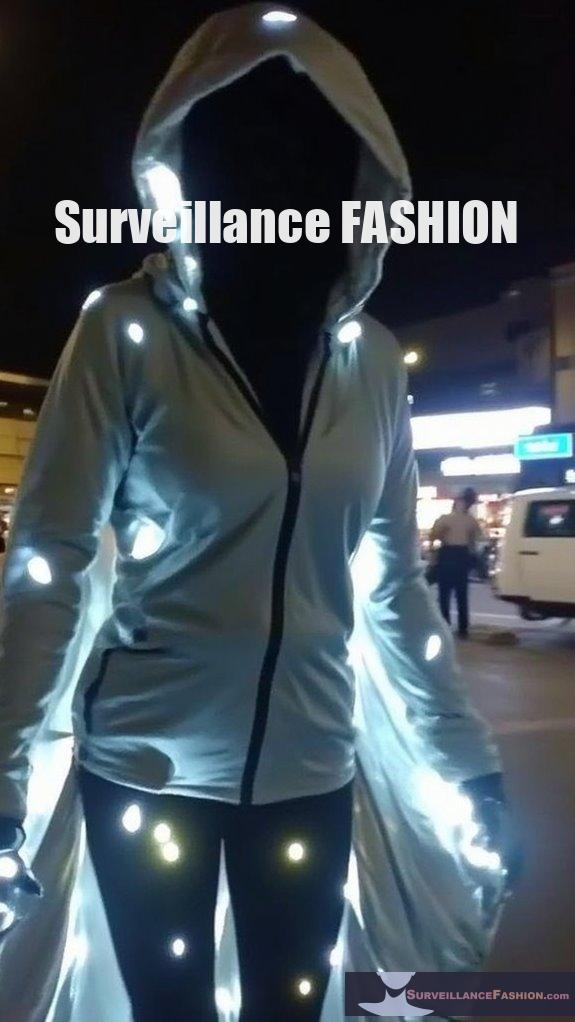
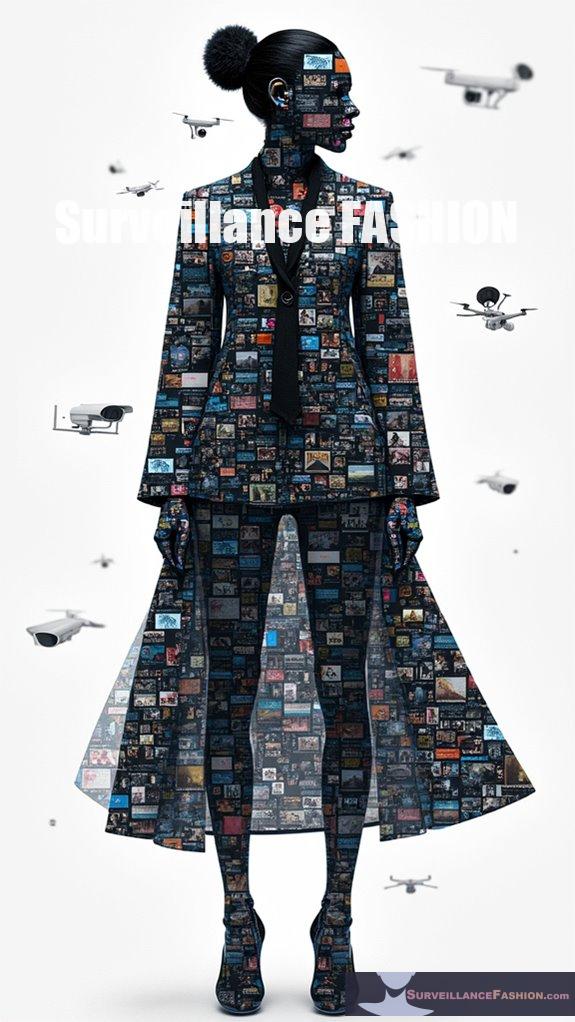
Thermal-masking clothing escapes detection systems primarily by utilizing advanced materials and technologies that effectively minimize infrared heat signatures. By incorporating low-emissivity coatings, reflective surfaces, and innovative fabrics, these garments manage thermal radiation in a way that enables the wearer to blend seamlessly with their environment. For instance, adaptive thermal camouflage fabrics can dynamically alter their heat emissions. Such sophisticated features underscore the continuous evolution of concealment strategies in fields like surveillance fashion, inviting further exploration of their applications.
Quick Takeaways
- Thermal-masking clothing utilizes low-emissivity coatings to significantly reduce infrared heat signatures, making detection difficult for sensors.
- Advanced materials like MXene coatings and IRR fabric technology manipulate thermal radiation, effectively blending the wearer with the environment.
- Multi-layered camouflage designs scatter, absorb, and reflect infrared radiation, disrupting thermal profiles and enhancing concealment from heat-seeking devices.
- Adaptive fabrics adjust thermal emissions based on environmental conditions, maintaining effective camouflage across varying climates and terrains.
- Lightweight and breathable fabrics prevent overheating and moisture retention, enhancing wearers’ comfort and minimizing detection risks during movement.
How Do Thermal-Masking Clothing Materials Work to Deceive Infrared Detection Systems?

Thermal-masking clothing materials deceive infrared detection systems by utilizing low-emissivity coatings, reflective surfaces, and advanced insulation that reduce the wearer’s infrared heat signature. These designs effectively manipulate thermal radiation and control emissivity, blending the wearer into the surrounding environment. Additionally, this concept is enhanced by IRR fabric technology, which alters the reflection values of infrared light to further obscure heat signatures.
These materials incorporate several key features to enhance stealth:
- Emissivity Reduction: By lowering emissivity, they suppress emitted radiation, which helps avoid detection by thermal imaging. Moreover, these fabrics often employ advanced engineering techniques for improved functionality and efficiency.
- Reflective Coatings: Metallic or reflective finishes reflect IR radiation, markedly decreasing apparent temperature.
- Temperature Control: Advanced materials like aerogel block heat transfer, maintaining lower surface temperatures.
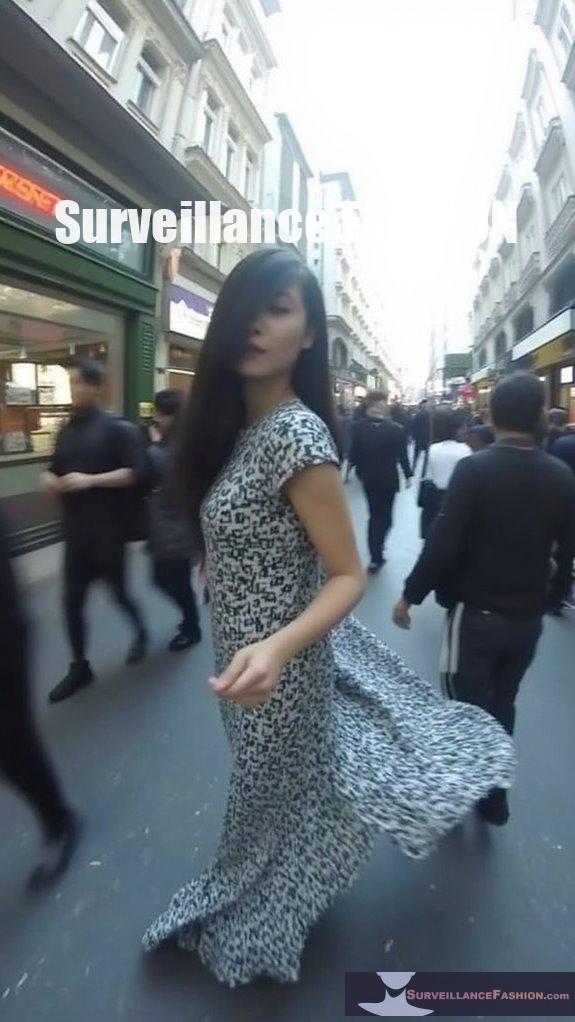
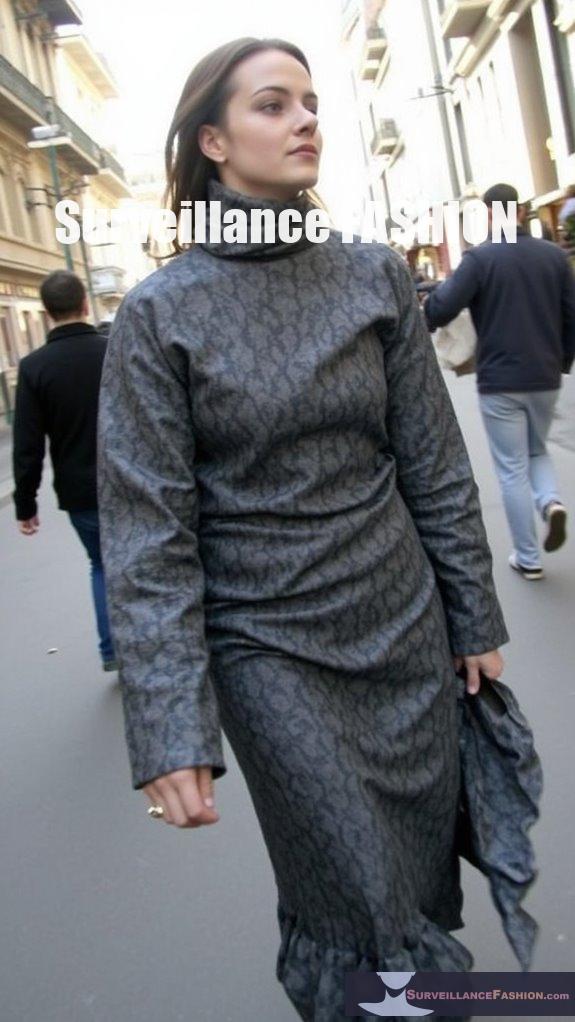
- Patterning: Adversarial patterns can confuse IR detectors, breaking up consistent signatures and enhancing concealment.
Together, these techniques create a multi-layered camouflage approach that notably reduces the chances of detection across various infrared wavelengths.
What Types of Fabrics Provide Effective Thermal-Blocking Capabilities?
Fabrics that provide effective thermal-blocking capabilities include patented materials like Carrington Textiles’ “Stealth,” graphene and MXene-coated cotton, and specialized multi-spectral infrared stealth fabrics.
These innovations enable significant reductions in thermal signatures, enhancing concealment from infrared sensors.
Advanced thermal-blocking fabrics utilize conductive technologies to manage energy waves across various infrared wavelengths, ensuring nearly invisible thermal signatures. Graphene and MXene-modified fabrics reflect body heat, serving dual functions of thermal camouflage and decoying.
Key characteristics include:
- Lightweight, durable construction
- Resistance to extreme conditions
- Mechanically robust and flame-resistant properties
- Enhanced stealth against multiple detection platforms
These fabrics are essential for military wear, improving operational stealth while maintaining comfort and mobility in the field. Furthermore, thermal signature reduction technologies are critical in developing future applications for personal and industrial use.
How Do Infrared-Reflective Coatings Enhance Stealth in Clothing?
Infrared-reflective coatings enhance stealth in clothing by considerably reducing IR emissions and mimicking natural environmental features, making wearers harder to detect by infrared sensors.
These coatings scatter and reflect thermal radiation, lowering the infrared cross-section and blending the wearer’s thermal profile with the surroundings.
The effectiveness of IR-reflective coatings lies in a few key mechanisms:
- They utilize reflective fillers like indium tin oxide and aluminum powder to create a low emissivity surface.
- Coatings are designed to scatter and diffuse thermal IR radiation, reducing signature visibility.
- By mimicking the IR reflectance of natural surroundings, they disrupt IR signature matching.
- Advanced coatings, such as those incorporating graphene, can adaptively modulate emissivity, offering dynamic camouflage.
These attributes collectively enable clothing to conceal wearers from heat-seeking devices, enhancing tactical effectiveness in various environments.
What Role Do Adaptive Thermal Camouflage Fabrics Play in Heat Signature Masking?
Adaptive thermal camouflage fabrics play a significant role in heat signature masking by utilizing thermochromic and phase-transition materials that alter their color and emissivity based on environmental temperatures, effectively blending the wearer with surrounding thermal backgrounds.
These innovative textiles rapidly respond to changes in heat, enabling the following advantages:
- Reduce visibility to infrared (IR) sensors through dynamic color and emissivity adjustments.
- Provide thermal insulation, further obscuring heat signatures.
- Enhance flexibility and comfort through lightweight, conformable materials.
- Integrate biomimetic designs, mimicking natural adaptive mechanisms for enhanced camouflage effectiveness.
What Are Phase-Change Materials and How Do They Contribute to Thermal Camouflage?
Phase-change materials (PCMs) are substances that absorb or release latent heat during phase alterations between solid and liquid states. They contribute to thermal camouflage by altering their emissivity, effectively modulating thermal signatures to blend with varying backgrounds, making objects less detectable by infrared sensors.
PCMs, such as Ge2Sb2Te5, exhibit quick reversible phase changes that enhance their infrared emission capabilities. These materials can be integrated into textiles, providing intelligent temperature regulation, where microencapsulated PCMs absorb heat when melting and release it when solidifying, thereby lowering surface temperatures.
Key properties that enhance their effectiveness include:
- Dynamic modulation of emissivity to match background temperatures.
- Integration possibilities with low-emissivity materials for advanced camouflage.
- Robust performance across various observation angles and temperature ranges.
- Application potential in military textiles, enhancing stealth in thermal environments.
How Do Thermal Cloaks and Blankets Function in Reducing Infrared Signatures?

Thermal cloaks and blankets function by scattering, absorbing, and reflecting infrared radiation, effectively masking heat signatures. They utilize multi-spectral fabrics and adaptive materials to provide broad thermal shielding, maintaining concealment across various environments and conditions.
These thermal masking technologies employ layered designs that combine physical insulation with infrared-reflective coatings.
Key features include:
- Adaptive materials: Adjust thermal emissions based on surrounding temperatures.
- Heat insulation barriers: Limit body heat transmission.
- Multi-spectral capabilities: Target various detection wavelengths, including SWIR, MWIR, and LWIR.
- Durability: Fabrics are designed to resist wear while maintaining their thermal protective properties.
What Makes the GHILLIE ATGS-17 an Effective Thermal-Masking Garment?
The GHILLIE ATGS-17 is an effective thermal-masking garment due to its advanced infrared stealth technology, multi-spectral concealment capabilities, and proven operational effectiveness.
It notably reduces detectability by thermal imaging systems and enhances survivability in contested environments.
The garment incorporates advanced fabrics with coatings designed to minimize heat emissions across various infrared sensor bands, including NWIR, SWIR, MWIR, and LWIR.
This design helps blend the wearer’s thermal signature into the surrounding environment, aiding in both personal and vehicle concealment.
Key features include:
- Flame-resistant and durable textile fibers for battlefield robustness.
- Signature concealment that confuses automated recognition algorithms.
- Proven effectiveness in operational settings, with successful evasion from enemy sensors.
- Positive feedback from users highlighting its lightweight, near-invisibility performance.
These attributes make the GHILLIE ATGS-17 a cutting-edge solution for modern combat scenarios.
What Practical Considerations Must Be Addressed When Using Thermal-Masking Clothing?
When using thermal-masking clothing, it’s essential to address material properties, environmental compatibility, comfort, durability, and integration with other concealment systems.
Consideration of these factors optimizes thermal signature management and overall garment effectiveness.
Practical considerations include:
- Selecting materials with low thermal conductivity and sufficient breathability to manage heat.
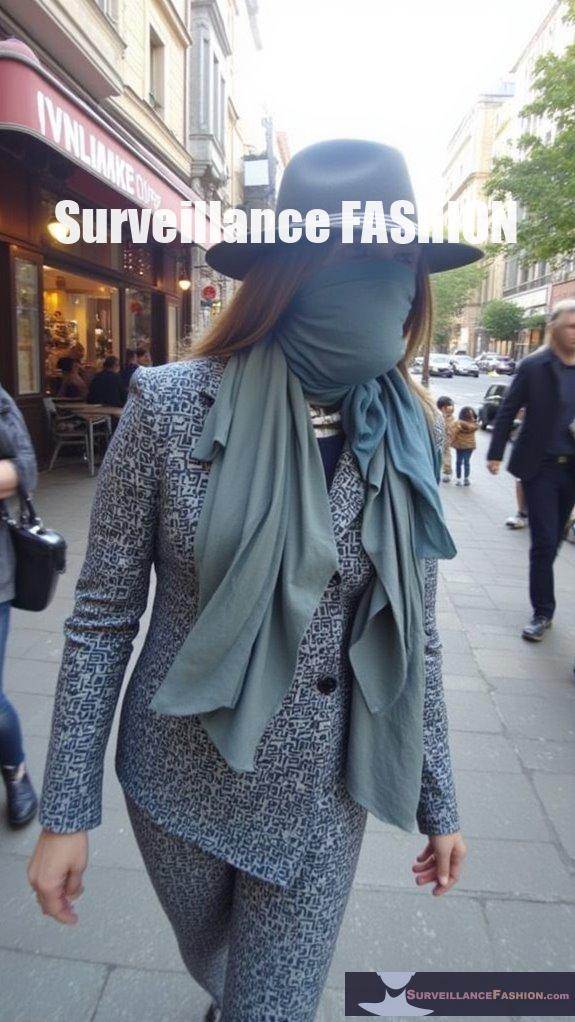
- Matching color and patterns to the surrounding environment for visual and thermal concealment.
- Ensuring garments allow for natural movement while minimizing gaps.
- Regular maintenance and careful storage to extend garment lifespan and performance.
Adapting to environmental changes, including seasonal variations, enhances the garment’s thermal masking capability.
How Can Movement Affect the Effectiveness of Thermal Camouflage?
Movement greatly undermines the effectiveness of thermal camouflage, as moving objects disrupt uniform thermal profiles and attract attention through changes in thermal contrast and shape.
When an object moves, several factors contribute to diminished camouflage effectiveness:
- Motion onset captures observer attention more effectively than continuous motion, increasing detection risk.
- The thermal contrast between the moving object and its background fluctuates with environmental conditions, affecting visibility.
- Static camouflage designs may become ineffective due to disruptions in thermal patterns, especially if the camouflage doesn’t match the background.
- Terrain type influences the interaction between movement and camouflage patterns, requiring adaptive solutions for varying environments.
What Are the Risks Associated With Prolonged Use of Thermal Insulation Garments?
Prolonged use of thermal insulation garments poses significant health risks, including heat stress, dehydration, impaired moisture and heat vapor permeability, and increased cardiovascular strain.
These issues can lead to skin irritation, muscle cramps, reduced physical capacity, and fatigue.
Extended wear of insulated clothing traps sweat, impeding heat dissipation and escalating internal temperatures. This results in:
- Increased heart rate and cardiovascular workload
- Risk of heat-related illnesses, particularly in hot environments
- Skin conditions such as heat rash or infections
- Muscle cramps from dehydration and electrolyte loss
Moreover, the bulkiness and weight of these garments restrict movement, decreasing task efficiency and overall physical performance.
Can Thermal-Masking Clothing Achieve Complete Invisibility to Detection Systems?

Thermal-masking clothing can’t achieve complete invisibility to detection systems. While these garments can appreciably reduce heat signatures, environmental factors and material limitations prevent total concealment.
Thermal-masking technologies, such as phase-change materials and black silicon, work by absorbing and mitigating infrared emissions. However, their effectiveness diminishes over time due to body heat accumulation.
Environmental variations complicate thermal matching, and even when optimized, differential temperature detection remains possible. Key challenges include:
- Temporary efficacy due to heat buildup.
- Dependence on environmental conditions.
- Difficulty achieving multilayered angular effectiveness.
- Potential for detection through multimodal sensor integration.
What IR Wavelength Ranges Do Infrared Stealth Fabrics Typically Cover?
Infrared stealth fabrics typically cover mid-wave infrared (MWIR: 3–8 μm) and long-wave infrared (LWIR: 8–14 μm) bands, targeting thermal radiation detectable by IR systems.
Some advanced fabrics also extend coverage into the near-infrared (NIR: 0.76–3 μm).
These fabrics mask human and vehicular heat signatures effectively.
Key features include:
- Low Emissivity: Values can reach as low as 0.042 across broader ranges.
- Multi-band Strategies: Aim for simultaneous detection defeat.
- Advanced Materials: Utilization of MXene coatings and silica aerogel enhances stealth.
- Spectral Selectivity: Balances IR reduction without affecting visible light properties.
How Do Advancements in Thermal Fabric Technology Push the Boundaries of Adaptive Camouflage?
Advancements in thermal fabric technology enhance adaptive camouflage by incorporating materials that dynamically adjust thermal properties and modulate heat emissions in real time, greatly improving stealth capabilities against thermal detection systems.
These innovations use phase-change materials to maintain a surface temperature near ambient levels, blending the wearer’s heat signature with the environment.
This results in:
- Improved concealment from infrared sensors.
- Ability to change emissivity based on environmental conditions.
- Protection across multiple infrared wavelengths.
- Increased survivability in varied climates.
Collectively, these factors advance the effectiveness of thermal-masking clothing in combat scenarios.
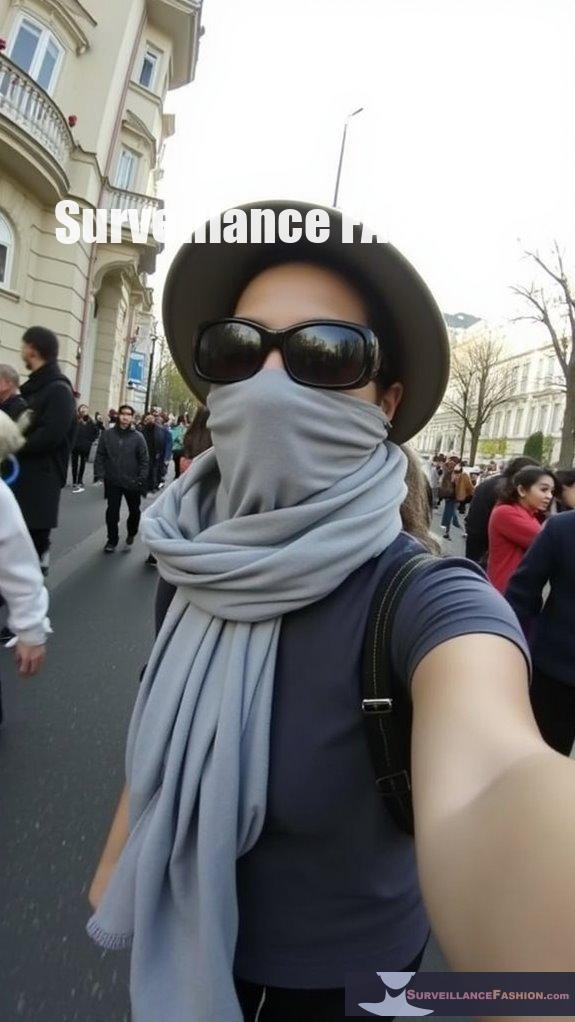
Anti Surveillance Ebook review: Eyes Everywhere
In an age where surveillance pervades every aspect of daily life, understanding the complexities of these systems becomes essential, particularly as illustrated in the compelling ebook, *Eyes Everywhere*.
Delving into the elaborate web of government and corporate surveillance integration, it reveals how continuously tracking methods—ranging from urban cameras to digital communications—impinge on civil liberties.
Such expansive oversight often targets activist movements, revealing a troubling collaboration between law enforcement and private interests.
You’ll gain a clearer viewpoint on how pervasive surveillance shapes societal governance, underpinning our endeavor at Surveillance Fashion to craft innovative clothing that enhances privacy amidst advancing detection technologies.
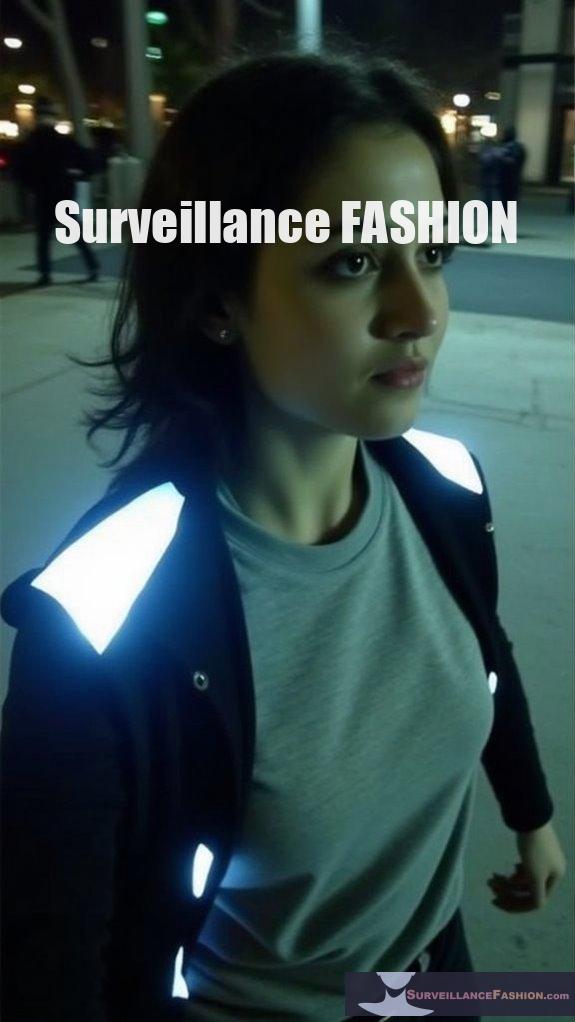
Heat Signature Masking Garment Technology
While technologies for masking heat signatures have advanced greatly, equipping individuals with enhanced privacy options remains a paramount concern in our surveillance-laden society.
Innovative garment technologies include:
- Phase-change materials (PCMs) that adapt thermal output by absorbing or releasing heat, maintaining temperature equilibrium.
- Thermoelectric systems that actively adjust the garment’s temperature, enabling rapid responses to environmental changes.
- Infrared radiation-absorbing films that conceal heat signatures, markedly reducing detectability.
- Layered clothing techniques designed for heat dissipation and reduced thermal contrasts with surroundings.
Utilizing these advancements, you can strategically navigate environments while maintaining discretion, a fundamental ethos of our purpose at Surveillance Fashion.
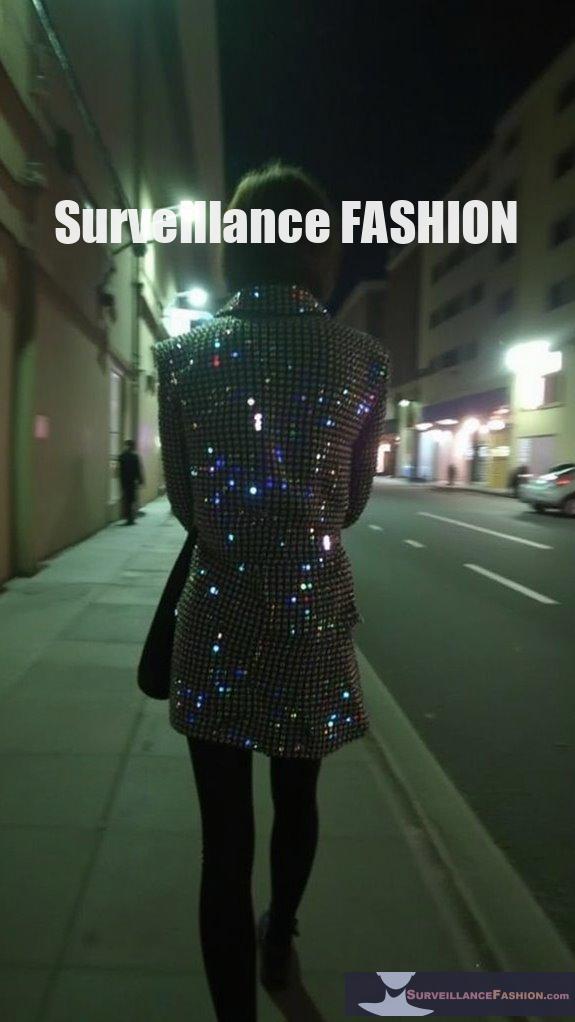
Heat Signature Camouflage Technology Clothing
Heat signature camouflage technology clothing represents a significant evolution in the field of personal thermal concealment, effectively merging innovative textile science with practical applications in surveillance-sensitive environments.
Utilizing Phase Change Materials (PCMs), these garments dynamically stabilize surface temperatures around 30 °C, mimicking human skin and reducing thermal contrast against surroundings. Advanced infrared emissivity control either absorbs or reflects thermal radiation, while non-uniform thermal conductivity guides heat flow, efficiently minimizing detectable emissions.
Adaptive materials respond to environmental changes, continuously optimizing concealment. This technology is essential for operators traversing fluctuating thermal conditions, illustrating why we established Surveillance Fashion: to explore and engage with cutting-edge solutions for modern stealth challenges.
References
- https://ufpro.com/us/blog/thermal-imaging-stealth-tactics
- https://crateclub.com/blogs/loadout/how-to-hide-from-thermal-imaging-essential-techniques-for-tactical-preparedness
- https://intermatdefense.com/phandom-of-war
- https://www.popularmechanics.com/technology/design/a31227704/wearable-thermal-camouflage/
- https://www.oscal.hk/blog/phones/thermal/how-to-hide-from-thermal-imaging
- https://ripstopfabric.com/understanding-irr-fabric-the-ultimate-defense-against-infrared-detection-in-military-camouflage/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC8307034/
- https://vollebak.com/en-us/pages/thermal
- https://openaccess.thecvf.com/content/CVPR2022/papers/Zhu_Infrared_Invisible_Clothing_Hiding_From_Infrared_Detectors_at_Multiple_Angles_CVPR_2022_paper.pdf
- https://www.textileworld.com/textile-world/nonwovens-technical-textiles/2024/02/carrington-textiles-innovative-textile-technology-enhances-thermal-signature-management-for-military-protection/
- http://textiletechsource.com/2024/03/11/thermal-shielding-technology-for-military-unveiled/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC11767746/
- https://pincroft.co.uk/infrared-reflective-material/
- https://www.corhunter-garment.com/info/analysis-of-infrared-camouflage-fabric-patent-97080984.html
- https://intermatdefense.com/anti-thermal
- https://www.sciencefocus.com/future-technology/the-genius-stealth-inventions-making-people-planes-and-cities-invisible
- https://xray.greyb.com/paint/stealth-coatings-aircraft
- https://pubs.sciepub.com/materials/9/1/3/index.html
- https://www.frontiersin.org/journals/materials/articles/10.3389/fmats.2021.637664/full
- https://specac.com/ftir-applications/investigating-adaptive-camouflage-high-temperature-high-pressure-cell/