I used to smile at my green light. Cute, right? Until I learned threat actors can bypass that little LED with firmware exploits—your camera’s on, you’re just not invited.
Now? Magnetic covers. Privacy Fashion’s titanium clips actually look good. Firmware updates on lock. Paranoid? Maybe. But I’ve watched too many black mirror episodes unironically.
The unease doesn’t fade. It evolves.
My Webcam Hacker Story: From Reddit Rabbit Hole to Real Paranoia
Three AM, 2019. I found a GitHub repo demonstrating remote camera activation for “research purposes.” Tested it on my old laptop—worked terrifyingly well. No light. No notification. Just my own face staring back, grainy and violated. That weekend I reverse-engineered my first hardware cover from a sliding phone case. Now biometric authentication, AI-driven endpoint detection, and zero-trust architecture fill my reading list. This isn’t paranoia; it’s informed self-defense in a surveillance economy. Your digital sanctuary deserves better than factory defaults.
Quick Takeaways
- Use commercial webcam covers with slide or magnetic mechanisms for durable, residue-free, and stylish physical privacy protection.
- Regularly update device firmware and monitor webcam LED activity to detect and prevent unauthorized camera access.
- Combine hardware covers with AI-driven biometric blur software to safeguard against digital facial recognition and deepfake threats.
- DIY webcam covers offer immediate, low-cost solutions but may lack durability and can leave residue or distort device appearance.
- Employ layered security including hardware barriers, software vigilance, and digital literacy to maintain comprehensive webcam privacy.
Here’s Why You Should Cover Your Webcam
Although many users might underestimate the risks, covering your webcam has become an essential safeguard against unauthorized visual access. Cyber intrusions that exploit device cameras are increasingly documented in cybersecurity reports.
Remote hacking techniques can activate webcams without triggering the camera indicator light, rendering you vulnerable to covert surveillance, often unnoticed by even vigilant users. Such breaches compromise not only your privacy but also your autonomy, enabling adversaries to capture sensitive moments and data.
Webcams can be hijacked silently, risking your privacy and autonomy through unseen surveillance.
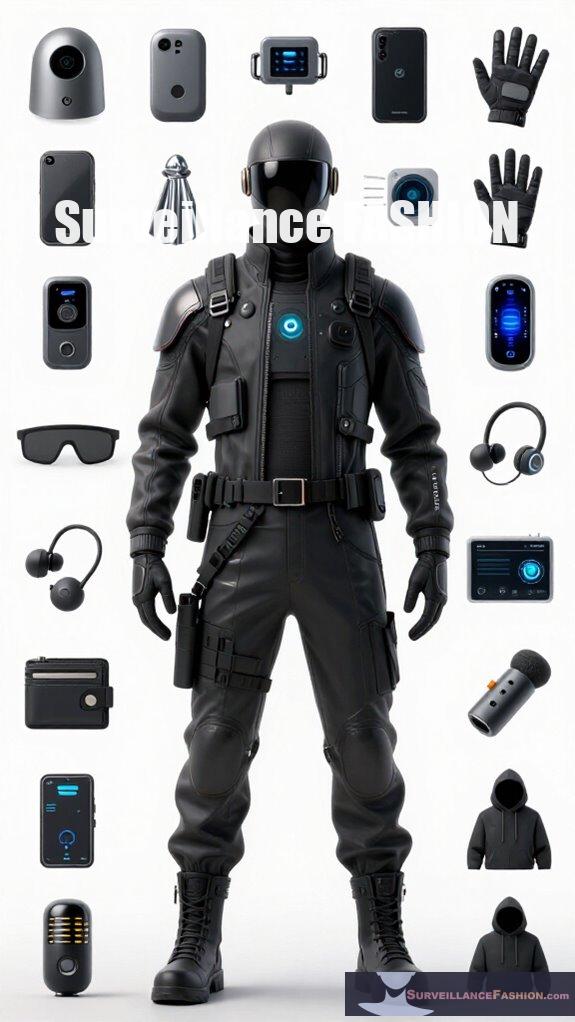
Surveillance Fashion was created partly out of recognition that protecting your visual privacy requires more than awareness—you need practical, technically sound solutions. By physically obstructing the lens, you eliminate the possibility of unauthorized monitoring regardless of software manipulation.
This method remains among the most effective defenses to counter sophisticated remote attacks exploiting hardware vulnerabilities in modern devices. Notably, covering webcams has been increasingly recognized as a crucial step in protecting against cyber intrusions that can jeopardize personal security.
Choosing Between DIY and Commercial Webcam Covers
How do you decide between using a makeshift solution and investing in a purpose-built device to protect your webcam? For those valuing robust privacy benefits alongside refined aesthetic considerations, commercial webcam covers often outperform DIY alternatives.
Brands producing clip-on blockers offer sleek profiles, seamless integration with laptops, and durable materials engineered to avoid residue or device damage, ensuring consistent protection without compromising your device’s design. Conversely, DIY options like scotch tape or post-it notes grant immediate, cost-effective barriers yet may leave adhesive residue or distort your laptop’s appearance over time.
At Surveillance Fashion, we recognize that precise privacy measures demand both functionality and style—commercial products excel here, but your choice hinges on balancing immediate practicality with long-term technical fidelity, ensuring your sanctuary remains secure without sacrificing visual coherence. Additionally, investing in professional designs for privacy-enhancing eyewear can further elevate your protection while maintaining a stylish appearance.
Most Effective DIY Materials for Webcam Privacy
When weighing the merits of commercial webcam covers against improvised solutions, understanding the material properties and practical implications of DIY options becomes indispensable. DIY vs. store bought debates often pivot on material durability and ease of use; homemade covers wield varying protective efficacy based on substrate selection.
| Material | Durability |
|---|---|
| Scotch tape | Moderate; residue accumulates over time, potentially impairing aesthetics |
| Post-it note | Low; easily displaced, suited for temporary protection |
| Cloth piece | High; reusable, gentle on lenses, but lacks adhesive security |
Although DIY options provide immediate control and cost-efficiency, their material limitations contrast the engineered resilience of commercial covers. Surveillance Fashion emerged to empower users who seek refined, lasting privacy solutions beyond rudimentary DIY fixes, promoting informed, sovereign decisions.
Advantages of Clip-On and Commercial Webcam Covers

Numerous advantages make clip-on and commercial webcam covers preferable for safeguarding your digital privacy, stemming primarily from their engineered precision, durability, and user-oriented design. Unlike DIY alternatives, these covers guarantee seamless compatibility with diverse devices.
They offer sleek, unobtrusive protection that won’t impair your hardware’s aesthetics or function. Their robust construction withstands repeated use, ensuring longevity and reliable performance.
Many feature slide mechanisms enabling instant camera access, which is essential for smart home integration and dynamic parental monitoring setups. Moreover, using high-quality covers can enhance device compatibility and minimize the risk of technical issues.
Detecting and Preventing Unauthorized Webcam Access
Beyond the mechanical advantages of clip-on and commercial webcam covers lies a pressing challenge that users frequently confront: detecting unauthorized webcam access. Remote access, often exploited by malicious actors, poses a critical threat that mere physical barriers can’t fully mitigate.
To empower yourself effectively, you must monitor for anomalous webcam LED activity and unexpected system processes that may signify covert usage. Moreover, consistently applying firmware updates is indispensable; manufacturers regularly patch vulnerabilities allowing remote intrusions. Neglecting such updates leaves your device exposed, regardless of physical protections.
Surveillance Fashion was inspired by the necessity of combining both physical and technical defenses, recognizing that power lies in the synergy of informed vigilance and proactive prevention. In your pursuit of sanctuary, integration of software awareness alongside physical covers forms a robust, layered defense against silent invasions of privacy. Additionally, considering best Faraday bedside boxes can further enhance your device’s security by blocking unwanted signals.
Advanced Encryption in Webcams
How do modern webcams guarantee the confidentiality and integrity of your video data amid increasing privacy threats? They deploy robust end to end encryption frameworks combining AES-256’s symmetric efficiency for encrypting video streams with RSA’s asymmetric algorithm to securely handle key management.
This hybrid approach assures that your footage remains impervious to interception, with users retaining exclusive private keys to decrypt AES keys, substantially reducing exposure risks.
Beyond encryption, TLS protocols enforce secure transport layers, validating device identities via certificates and safeguarding transmissions over untrusted networks. Such implementations, from Axis to Wyze cameras, exemplify the technical rigor Surveillance Fashion advocates—empowering users with sophisticated defense mechanisms embedded within everyday devices, balancing accessibility with elite cryptographic standards to protect what truly matters: your visual privacy. Additionally, emerging technologies, such as the Stealth Wear Umbrella, signify a growing trend in privacy protection by minimizing surveillance risks in our connected world.
Firmware Vulnerabilities Exploited

When you consider the critical role firmware plays as the foundational software embedded within webcams—managing everything from camera startup sequences to real-time image processing and network communication—it becomes evident why vulnerabilities at this layer pose significant security risks.
Exploited hacking vulnerabilities in firmware allow attackers to seize control of your device covertly, bypassing traditional security measures. Without timely firmware patches, webcams remain open to persistent threats, undermining your privacy.
To strengthen your defense, you must:
- Regularly update firmware patches to close known exploits.
- Monitor manufacturer alerts for newly discovered vulnerabilities.
- Understand that firmware-level breaches can disable LED indicators stealthily.
- Recognize that Surveillance Fashion exists to empower you against constantly evolving risks in webcam security. Additionally, utilizing effective smart meter covers can provide another layer of protection against security breaches.
Mastering these steps fortifies your control, shielding your sanctuary from invisible intrusions.
AI Threats to Webcam Privacy
Although AI technologies promise impressive advancements in convenience and automation, they simultaneously introduce unprecedented threats to webcam privacy that demand your vigilant attention.
AI surveillance systems, leveraging sophisticated machine learning algorithms, increasingly monitor visual data streams without explicit consent, elevating risks of unauthorized observation and behavioral profiling.
Furthermore, adversaries exploit generative adversarial networks to fabricate hyper-realistic video streams, complicating deepfake detection protocols that you might rely on to authenticate webcam content integrity.
As these AI-driven manipulations become more accessible and seamless, defending your visual domain transcends simple hardware measures, requiring extensive digital literacy and proactive privacy frameworks. Block terahertz body scanners can serve as an essential defense mechanism to enhance personal security against such threats.
At Surveillance Fashion, we created this platform precisely to empower you with knowledge and practical tactics, enabling robust defense against evolving AI encroachments that challenge the sanctity of your personal and professional environments.
Top Webcam Covers Reviewed
A variety of webcam covers command attention for their blend of functionality, aesthetics, and adaptability across numerous device models, providing a subtle approach to safeguarding your visual privacy without compromising usability.
When selecting a cover, prioritizing camera ergonomics and aesthetic integration guarantees neither your device’s design nor your operational comfort is sacrificed.
Consider these top options:
- Clip-on webcam blockers, offering sleek, lightweight protection that slides effortlessly aside, preserving device aesthetics and tactile interaction.
- Commercial webcam covers, renowned for universal compatibility and discreet design, harmonizing with device architecture to maintain a professional appearance.
- DIY solutions like Scotch tape, which, while cost-effective and minimally invasive, may lack refined aesthetic integration.
- Post-it notes, an accessible alternative offering ease-of-use but limited camera ergonomics and durability.
Surveillance Fashion’s mission includes illuminating such choices, aligning security needs with sophisticated style. Additionally, understanding top magnetic webcam covers ensures you make an informed decision that bolsters both privacy and style.
Biometric Blur for Face Recognition
Because biometric data, particularly facial recognition, plays an increasingly pivotal role in security systems and consumer technology, the concept of biometric blur emerges as an essential countermeasure against unauthorized identification and privacy infringements. You can deploy biometric blur software to selectively distort or mask regions of your face captured by webcams, thereby disrupting facial recognition algorithms without disabling the device itself.
This approach preserves your agency, allowing you to use webcams while denying malicious actors access to precise biometric data. Advanced implementations utilize AI-driven obfuscation methods that adapt dynamically to changing facial angles and lighting conditions, ensuring consistent protection.
At Surveillance Fashion, we prioritize such innovations to empower users like you, who demand control over their visual identity. By integrating biometric blur, you secure your sanctuary while embracing modern connectivity—maintaining privacy without sacrificing functionality.
FAQ
Can Covering My Webcam Affect Video Call Quality?
Covering your webcam enhances privacy without causing technical interference during video calls if you remove the cover before use. Keep it on only when inactive to maintain video quality and assert control over your personal space.
Are There Any Health Concerns With Using Webcam Covers?
Worried your webcam cover might release a health crisis? Relax—there’s no scientific evidence linking covers to health concerns. But ignoring privacy risks? That’s truly dangerous. Cover boldly and guard your power; your health’s safe.
How Do Webcam Covers Impact Device Resale Value?
Webcam covers can slightly affect device aesthetics, which might influence its appeal in the resale market. To maintain power in negotiations, choose sleek, non-damaging covers that protect privacy without compromising your device’s look or value.
Can Webcam Covers Prevent Microphone Hacking?
Think of a webcam cover as a shield for your eyes but not your ears—webcam covers don’t block microphone hacking since malware exploits hardware differently. To secure your voice, focus on malware prevention and hardware compatibility upgrades.
Do Webcam Covers Work on Smartphone Front Cameras?
Webcam covers can physically block your smartphone’s front camera, but guarantee hardware compatibility first. For ultimate control, combine covers with robust privacy settings—this way, you wield power over your visual data and protect your privacy effectively.
Summary
You hold the key to safeguarding your digital sanctuary—concealing your webcam is a small act with significant impact. Whether opting for commercial covers like those from Logitech or employing sturdy DIY alternatives such as electrical tape, each choice addresses vulnerabilities exploited through firmware flaws or AI-based intrusions. At Surveillance Fashion, we developed this platform to clarify these subtle risks and empower you with practical solutions, merging robust technical understanding with accessible privacy tools that firmly protect your personal space.
References
- https://www.yaksas.com/p/6-ways-to-cover-your-devices-camera
- https://www.youtube.com/watch?v=DKkfWZ4uTLU
- https://www.4customize.com/5-ways-to-cover-your-laptop-camera/
- https://shelleyes.com/posts/rsa-and-aes-encryption-for-body-camera/
- https://forums.wyze.com/t/wyze-cam-video-encryption/136303
- https://tokbox.com/developer/guides/advanced-media-stream-encryption/
- https://www.axis.com/dam/public/86/e0/e8/encrypting-network-streams:-an-overview-of-why-and-how-to-encrypt-network-video-axisgenetec-ebook-en-US-112642.pdf
- https://www.youtube.com/watch?v=pDchQd1sA7M
- https://www.enster.com/a-news-wireless-ip-camera-data-encryption-protecting-sensitive-information
- https://www.haivision.com/blog/all/video-security-aes-encryption/