Jewelry designers are innovating to block facial recognition, blending style with privacy protection. For example, Ewa Nowak’s “Incognito” uses brass components to obscure facial features, effectively confusing algorithms like Facebook’s DeepFace. Sara Sallam’s Orwell Jewelry Collection furthers this by employing asymmetrical designs to disrupt recognized geometries. Reflective materials and geometric patterns—integrated with fashion techniques—further enhance this concealment, providing you with options that marry aesthetics and autonomy. Discover more about these pioneering designs that challenge surveillance technology.
Quick Takeaways
- Ewa Nowak’s “Incognito” jewelry uses durable brass components to distort facial features and disrupt facial recognition algorithms effectively.
- Sara Sallam’s Orwell Jewelry Collection obscures key facial geometry with asymmetrical designs, preventing biometric tracking and enhancing privacy.
- Reflective face masks and jewelry utilize reflective materials to confuse depth-sensing technologies and disrupt biometric data collection.
- Geometric patterns in facial jewelry create illusions that challenge facial recognition algorithms while allowing for personal style expression.
- Face-masking jewelry incorporates artistic designs and materials like brass to obscure critical facial recognition points, promoting individuality and privacy.
Ewa Nowak’s “Incognito” Jewelry Design

In a world increasingly dominated by surveillance technologies, Ewa Nowak’s “Incognito” jewelry design emerges as a compelling response to the pervasive threat of facial recognition. Crafted from durable brass, this innovative piece comprises two round components covering the cheeks and a central piece between the eyes, effectively distorting facial features to disrupt algorithmic detection. This design not only embodies privacy aesthetics but also serves as a significant surveillance accessory, tested against Facebook’s DeepFace algorithm for effectiveness, and aligns with the growing trend of anti-facial recognition fashion that seeks to protect individual identities.
Addressing growing concerns about personal privacy, “Incognito” encourages you to reclaim anonymity in public spaces while making a bold fashion statement. As surveillance becomes ubiquitous, the potential for such designs to transform our interactions with technology and society is both necessary and intriguing, prompting crucial discussions about individual autonomy.
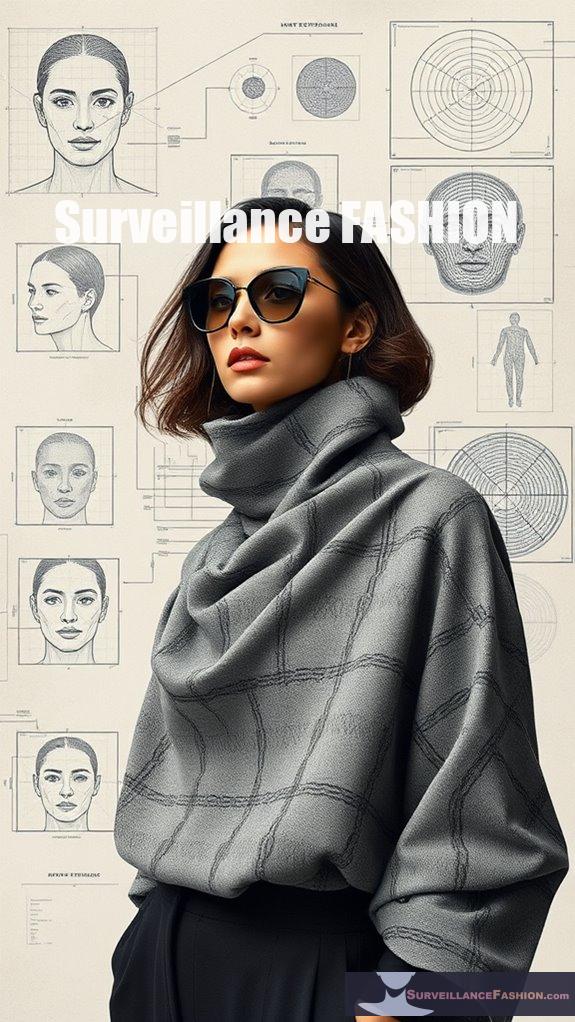
Sara Sallam’s Orwell Jewelry Collection

Sara Sallam’s Orwell Jewelry Collection represents a significant intersection of art, technology, and personal privacy. Named after George Orwell, the collection articulates concerns about modern surveillance, echoing themes from “1984.”
Each piece marries Orwellian aesthetics with functional beauty, obscuring key facial geometry to thwart recognition systems. For instance, the asymmetrical designs disrupt facial symmetry, while the ripple finish draws inspiration from historical Lover’s Eye jewelry. This innovative approach doesn’t merely serve as adornment; it actively protects against biometric tracking, including gait recognition. Additionally, the collection emphasizes the importance of anti facial recognition techniques that can help individuals maintain their privacy in a world increasingly dominated by surveillance. The collection also features jewelry for the chest designed to shield users from invasive monitoring associated with heart rate detection technology.
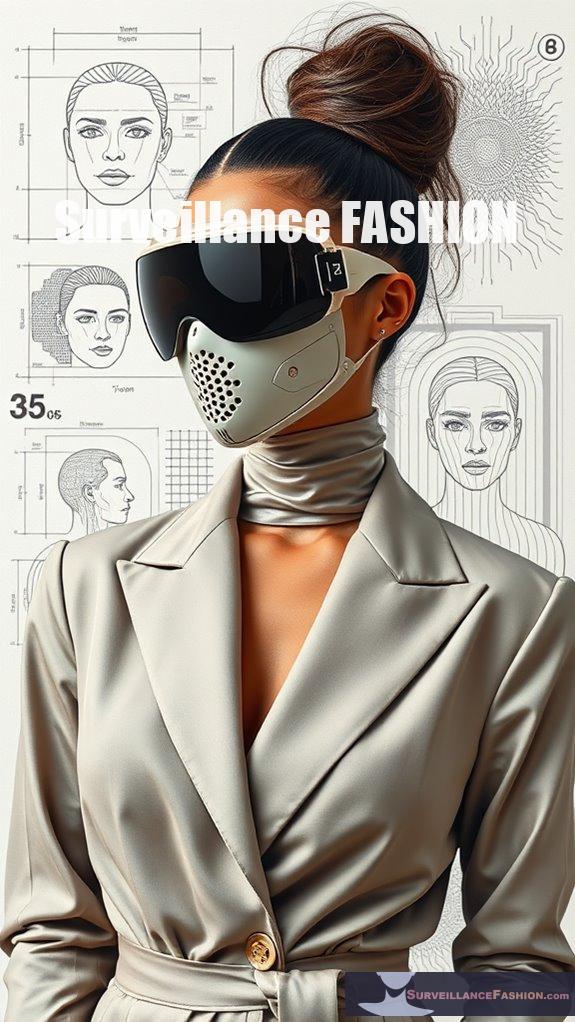
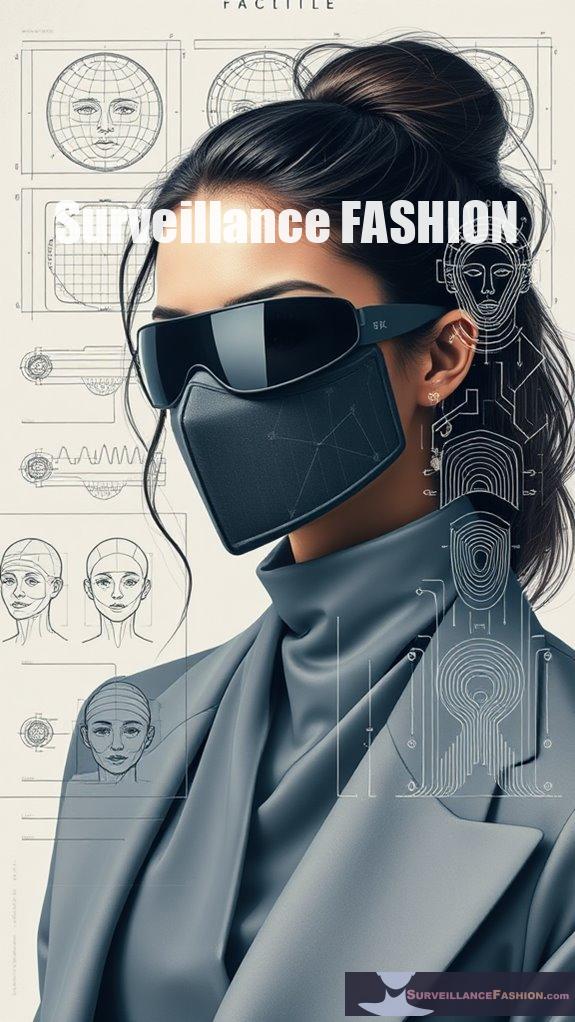
Reflective Face Masks and Jewelry

As concerns about surveillance technologies escalate, reflective face masks and jewelry emerge as innovative solutions designed to thwart facial recognition systems by distorting biometric data.
Utilizing reflective materials, these accessories effectively disrupt depth-sensing technologies, rendering your facial features nearly unrecognizable to algorithms.
For instance, retro-reflective fabrics can confuse infrared projections, while complex designs in brass and metal create asymmetrical shapes that challenge facial recognition software.
This duality of fashion and functionality addresses rising privacy concerns, making it increasingly viable for individuals to reclaim control over their personal data in public spaces. Moreover, the use of anti-surveillance fashion highlights a growing movement towards personal expression and privacy protection.
Geometric Patterns in Facial Jewelry

While you mightn’t immediately associate fashion with technological resistance, geometric patterns in facial jewelry serve a compelling purpose in the domain of anti-surveillance design. These elaborate designs create geometric illusions that disrupt pattern recognition algorithms, effectively masking your facial features.
Geometric facial jewelry blends fashion with anti-surveillance, disrupting recognition algorithms and masking your features with style.
- They draw inspiration from ancient tribal masks, blending artistry with utility.
- The asymmetrical shapes confuse algorithms, complicating facial recognition efforts.
- Crafted from materials like brass, they obscure key facial contours.
- Despite their protective nature, they remain visually appealing for public wear.
With the rise of surveillance technologies, incorporating such jewelry allows you to reclaim a sense of control. By embracing these geometric patterns, you not only express your style but also protect your privacy in an increasingly monitored world. Additionally, these designs tap into the concept of facial recognition blocking, allowing wearers to navigate public spaces with greater anonymity.
Innovative Materials for Surveillance Jewelry

Innovative materials in surveillance jewelry have emerged as a crucial component in the design of accessories that not only enhance personal style but also provide essential protection against intrusive monitoring technologies.
Among these materials, reflective coatings play an essential part, distorting facial features to confound facial recognition systems.
Furthermore, dielectric shielding is increasingly utilized to disrupt electromagnetic signals, effectively thwarting surveillance efforts.
Metal alloys, such as brass, are integrated into designs like the “Incognito” mask, while smart fabrics are being explored for their adaptability in blocking techniques.
As our desire for control over personal privacy intensifies, these innovative materials represent a significant advancement, allowing individuals to navigate an increasingly surveilled world with confidence, a key principle behind the creation of Surveillance Fashion. Additionally, the use of creative facial jewelry techniques highlights the intersection of art and technology in the fight against modern surveillance.
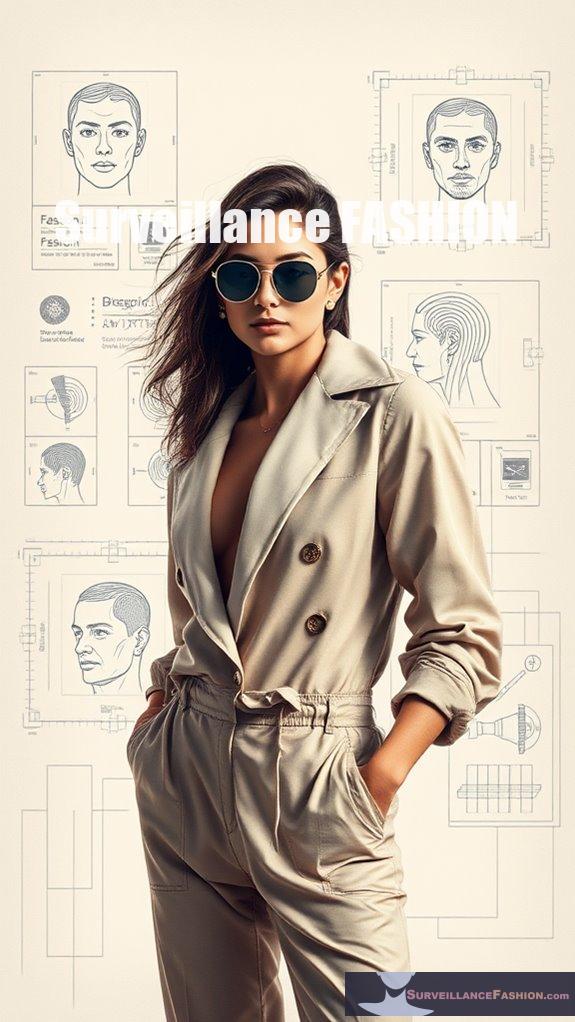
Combining Fashion With Privacy Protection
Jewelry that effectively blocks facial recognition technology represents a fascinating intersection of fashion and privacy protection, where aesthetic choices meet the pressing need for personal security in an increasingly monitored world.
This unique blend of privacy aesthetics and surveillance artistry empowers you to reclaim control over your identity.
Consider the following:
- Metal masks that transform security into style.
- Head ornaments designed to disrupt intrusive surveillance.
- Fashionable accessories that symbolize resistance against overreach.
- Innovative designs inspired by technological advancements.
In regions plagued by extensive surveillance, this jewelry serves not just as a protective barrier but also as a statement of defiance, reflecting a growing desire for autonomy in an era dominated by constant observation. Additionally, these pieces often utilize cutting-edge materials that enhance digital privacy while remaining chic and fashionable.
Future Trends in Biometric Disrupting Jewelry

As biometric technology continues to evolve, the future of jewelry that disrupts traditional identification methods is becoming increasingly promising.
You’ll find that biometric innovations are reshaping the terrain of wearable accessories, integrating biometric sensors for seamless user experiences while ensuring data security through blockchain technology.
These advancements facilitate personalized designs, where AI-driven customization tailors jewelry to reflect individual preferences and behavioral biometrics, creating unique user profiles.
AI-driven customization in biometric jewelry creates personalized designs that reflect individual preferences and unique user profiles.
Moreover, the rise of multimodal techniques enhances authentication accuracy, allowing for secure transactions without physical tokens.
As privacy technologies advance, there’s an urgent need for ethical considerations, including informed consent and transparency, which are essential to maintaining user trust in biometric jewelry.
This commitment to privacy is a core motivation behind our website, Surveillance Fashion.
Fashion That Thwarts Surveillance Technology

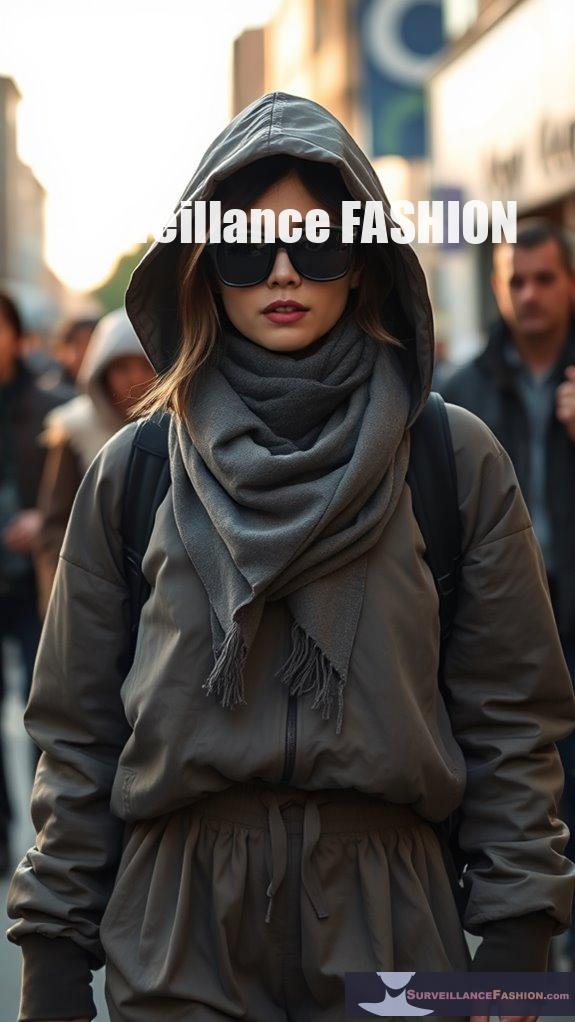
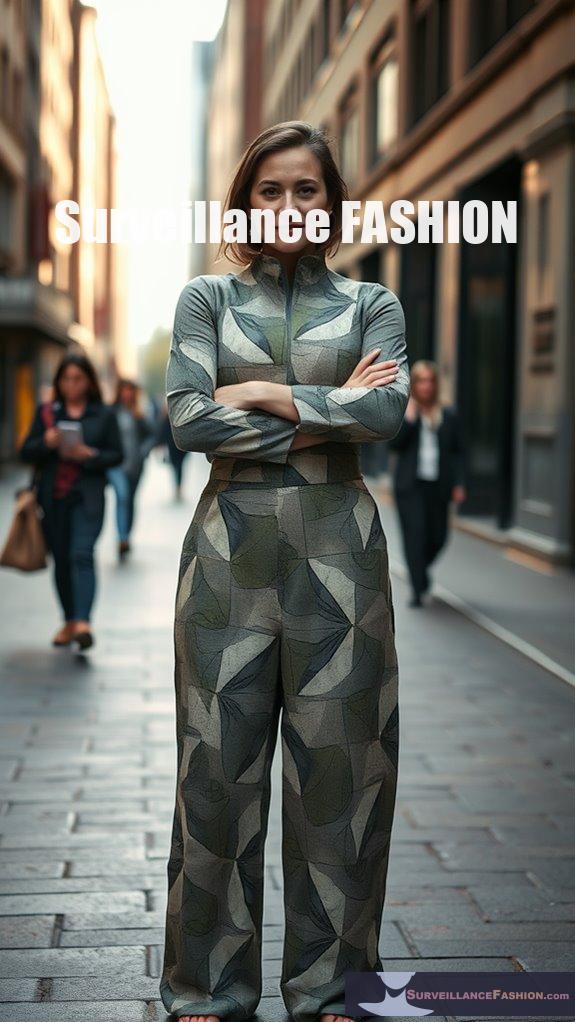
In light of the escalating concerns surrounding privacy and surveillance, fashion has emerged as a powerful medium to counteract the pervasive reach of monitoring technologies.
By employing innovative anti-surveillance techniques, designers create garments that challenge the omnipresence of facial recognition systems. You can explore various options that prioritize your autonomy and privacy:
- Signal-blocking fabrics that disrupt RFID tracking.
- IR-reflective materials to evade night vision cameras.
- Complex patterns that confuse facial recognition algorithms.
- Wearable technology that protects against heartbeat detection.
These advancements not only empower you to reclaim control over your personal space but also elevate artistic expression, making the fight for privacy visually compelling. Moreover, the incorporation of pattern-based camera-confusing designs showcases how fashion can be a form of resistance against technological overreach.
Consequently, embracing these styles fosters a culture of resistance against intrusive surveillance, as seen on platforms like Surveillance Fashion.
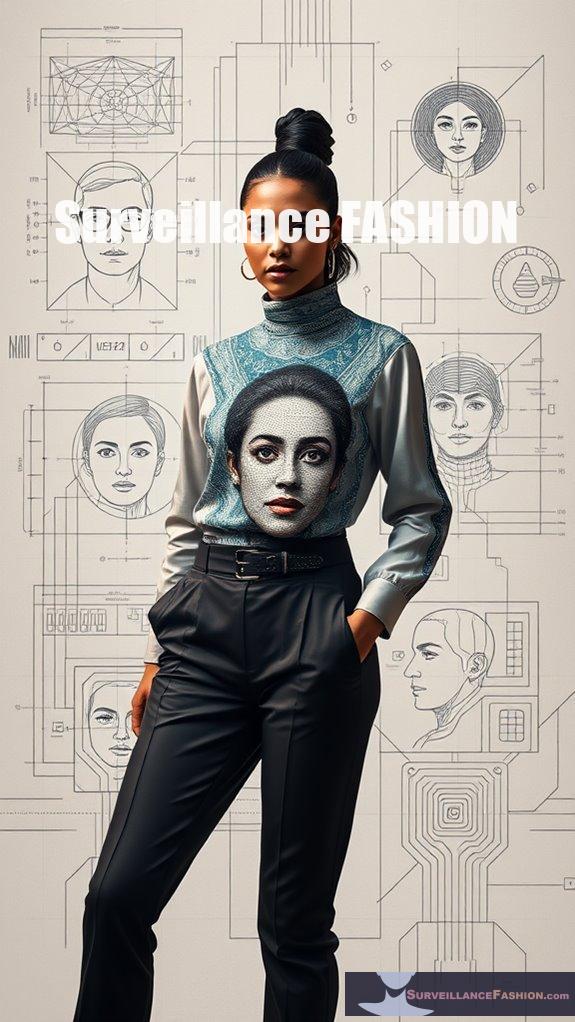
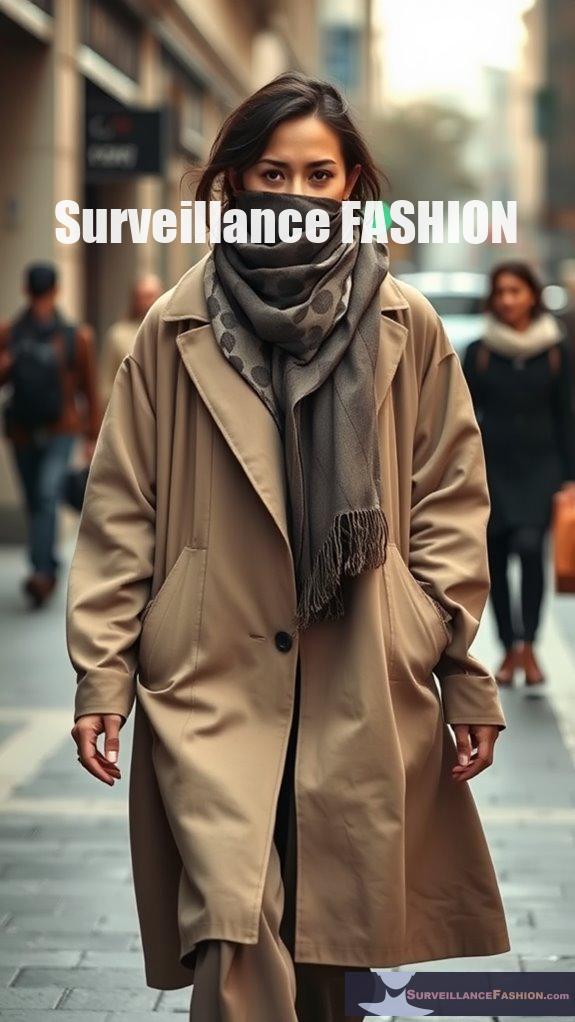
Jewelry That Masks Facial Features

Amid the ongoing dialogue about privacy and the implications of surveillance technology, an intriguing intersection has emerged, blending the domains of fashion and functionality through face-masking jewelry.
This innovative jewelry not only masks facial features, but also serves as a form of artistic expression, intertwining cultural significance with the desire for privacy. Many designs incorporate materials like brass, creating shapes that obscure key facial recognition points, while offering aesthetic appeal.
For instance, pieces resembling masks or abstract representations invite curiosity and challenge conventional design.
Artisans draw inspiration from diverse cultures, producing wearable art that enhances self-expression. As you consider your own choices, keep in mind that these pieces not only enhance your individuality but also empower you in the ongoing struggle against intrusive surveillance, an essential aspect that inspired the creation of this website, Surveillance Fashion. Additionally, these accessories are part of a growing trend in stealth accessories that aim to evade AI detection with style.
References
- https://www.internetandtechnologylaw.com/lawmakers-artists-facial-recognition/
- https://www.joeteacher.org/uploads/7/6/3/0/7630382/hacker_-_2012_rules_for_writers_7th_edition.pdf
- https://asiatimes.com/2019/09/jewelry-to-avoid-facial-recognition-cameras/
- https://bayanebartar.org/file-dl/library/IELTS2/IELTS-Writing-Maximiser.pdf
- https://www.dezeen.com/2020/06/11/anti-tracking-technology-surveillance-jewellery-sara-sallam-orwell/
- https://www.thisiscolossal.com/2019/08/incognito-by-ewa-nowak/
- https://www.lingexp.uni-tuebingen.de/z2/Morphology/baroni.rows
- https://www.onedaydesignchallenge.net/en/journal/the-success-of-incognito-the-jewellery-collection-designed-by-ewa-nowak
- https://www.ics.uci.edu/~dmdb/chandra/Enron2.1/words.txt
- https://www.dezeen.com/2019/07/30/ewa-nowak-anti-ai-mask-protects-wearers-from-mass-surveillance/