Shadows confuse facial recognition systems because they obscure key features and distort facial contours, which can lead to misinterpretation during identification tasks. When light varies, shadows mask critical elements, making it nearly impossible for algorithms to differentiate unique characteristics effectively. For instance, harsh shadows or uneven illumination may lead to false contours and recognition errors, thereby complicating the identification process. Understanding these challenges serves as a foundation for innovative approaches, like those discussed at Surveillance Fashion, where artistic solutions are explored.
Quick Takeaways
- Shadows obscure key facial features, making it difficult for recognition algorithms to identify distinct elements of a face.
- Uneven illumination creates false contours, leading to misinterpretation of facial structures and characteristics.
- The direction of light affects visibility; horizontal lighting emphasizes width, while vertical lighting highlights height, complicating recognition.
- Harsh shadows mask critical edges and high-contrast regions necessary for accurate facial identification.
- Low-light conditions degrade image quality, challenging recognition algorithms to extract usable data effectively.
The Impact of Shadows on Facial Recognition Accuracy

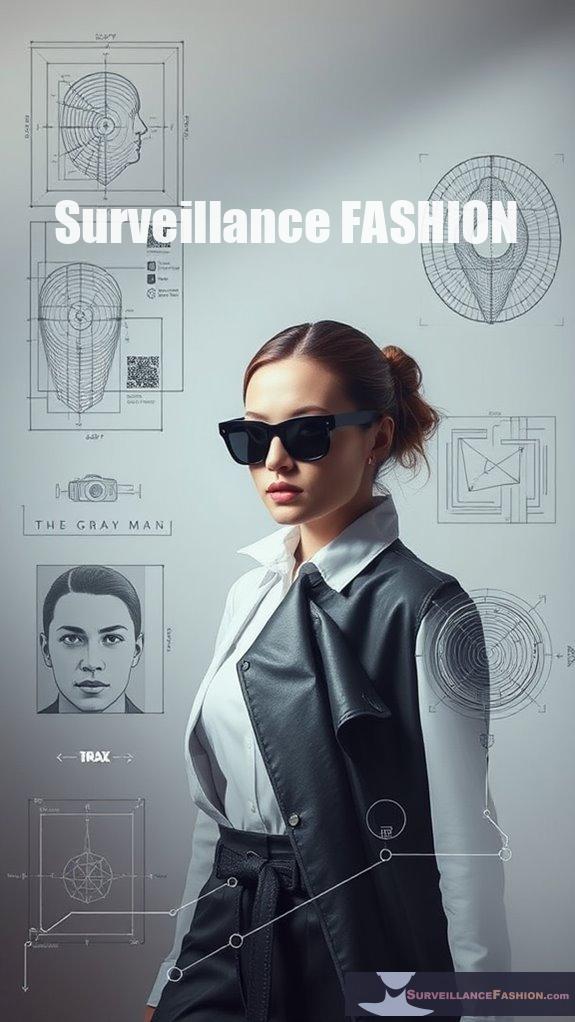
In a world increasingly reliant on technology, understanding the interplay between shadows and facial recognition systems becomes essential, especially when you consider how lighting conditions can dramatically alter the accuracy of these complex tools. As you explore the elaborate details of how facial recognition works, you may find yourself surprised at how something as seemingly innocuous as a shadow can derail an entire identification process.
Shadows and highlights can distort facial features markedly, creating what experts describe as "shadow distortion." When a face is illuminated unevenly, shadows obscure key elements, altering contours and ultimately making identification challenging. Envision standing under a harsh overhead light; the shadows that fall on your face might create false contours, leading a recognition system to misinterpret your features. In practical terms, this means that even the slightest variation in lighting conditions can have profound impacts on how well a system performs. Consistent lighting is essential for reliable identification and can significantly improve algorithm performance. Additionally, light projection methods can be utilized to intentionally obscure faces, further complicating recognition efforts. Research has shown that dynamic lighting techniques can also be employed to adaptively manipulate shadows, enhancing the ability to evade surveillance.
Shadows can significantly distort facial features, complicating recognition accuracy by obscuring key elements and altering contours.
The direction from which light hits a face is fundamental. If you consider the way shadows fall, you can appreciate that certain angles might enhance or hinder the visibility of distinct facial characteristics. For example, horizontal lighting may emphasize the width of a face, while vertical lighting might highlight its height. This interplay can either aid in face detection or create confusion, as shadows might obscure critical identifying features. Consequently, achieving uniform illumination becomes necessary for improving recognition accuracy.
In environments where lighting conditions fluctuate—such as outdoor settings or poorly lit rooms—recognition systems face substantial hurdles. Low-light scenarios often lead to image quality deterioration, complicating the algorithms' ability to extract usable data from facial images. These challenges aren't trivial; they require advanced solutions, including infrared technology that detects heat signatures, thereby bypassing the need for visible light altogether.
Further complicating matters, shadows can cause distortion that masks the very edges and high-contrast regions that recognition algorithms rely upon for effective identification. When you think about how recognition systems analyze images, it becomes clear that phase components, which provide structural information, are often compromised by the presence of harsh shadows. This is where innovative compensation methods come into play, such as Fourier analysis, which helps to restore images by accounting for shadows, enhancing the reliability of the overall system.
At Surveillance Fashion, we recognize these challenges and the importance of enhancing facial recognition accuracy. By developing techniques that address shadow compensation, we aim to improve the adaptability of these systems across various lighting conditions. For instance, methods like the Weighted Average Difference (SCWAD) estimate light direction to mitigate the impact of shadows, thereby facilitating more accurate face detection.
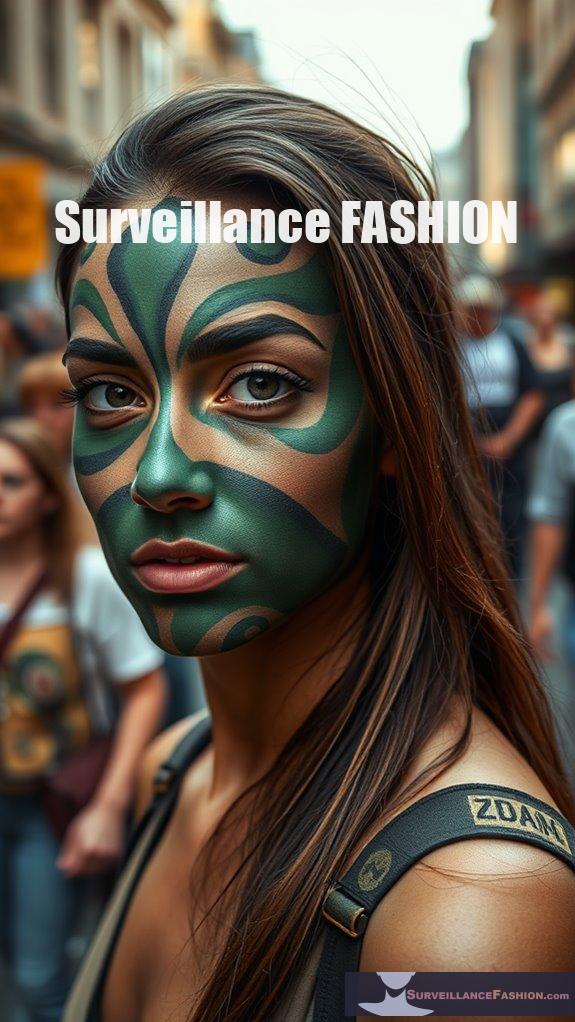
Disruptive Color Blocking Techniques
Shadows may obscure facial features, but disruptive color blocking techniques actively counteract the efficacy of facial recognition systems by manipulating visual perceptions. Techniques like CV Dazzle employ bold color patterns and high-contrast makeup to create visual asymmetry, effectively confusing algorithms that rely on expected facial structures. Additionally, CV Dazzle was designed to exploit vulnerabilities in algorithms, showcasing the innovative potential of these disruptive techniques. By darkening specific regions, such as brow lines, you can subtly disrupt recognition without attracting undue attention. Furthermore, traditional defenses like masks remain one of the most effective evasion methods against facial recognition systems, highlighting the importance of combining various strategies for optimal results.
Moreover, adversarial attacks introduce noise or patterns that challenge machine learning models while remaining imperceptible to the human eye. This innovative approach serves not only as a means of resistance against surveillance but also as a form of artistic expression, pushing the boundaries of personal identity. As facial recognition technology evolves, so must your strategies. Tools like Camera Adversaria exemplify the intersection of privacy and design, emphasizing the critical need to adapt in a digital society increasingly defined by surveillance. Additionally, incorporating anti-surveillance fashion can further enhance your ability to evade detection while making a bold statement. The use of disruptive color blocking can be particularly effective, transforming your makeup into a strategic tool against these technologies.
Reflective Materials Usage

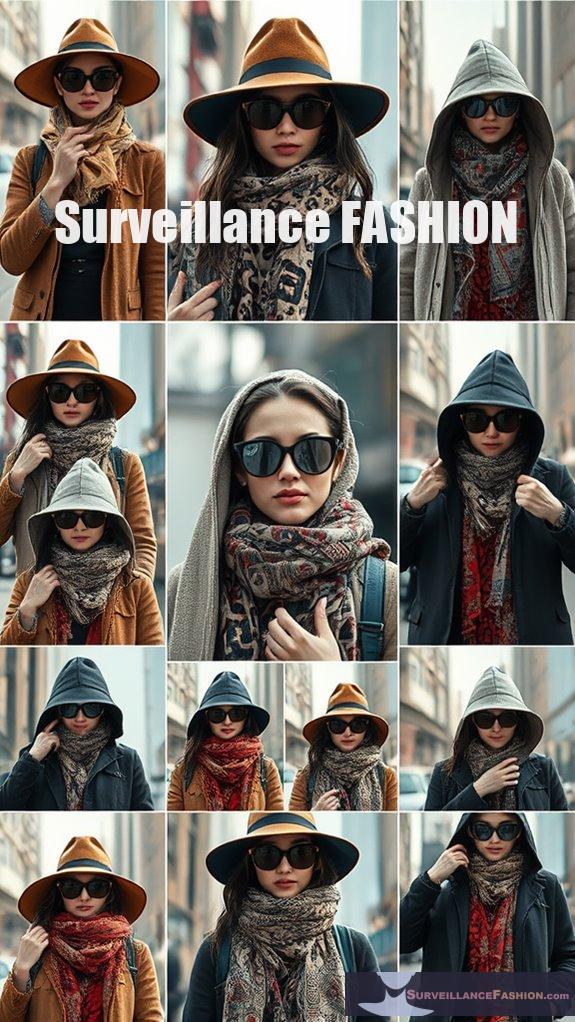
Reflective materials serve as a compelling tool in the ongoing effort to counteract facial recognition systems, effectively manipulating light and shadow to obscure identifiable features. By altering the grayscale balance critical for detection, these materials disrupt the algorithms facial recognition systems rely on. Interestingly, research indicates that shape is more critical for grayscale faces, highlighting how these reflective materials may further complicate detection by affecting the structural features of the face. In a similar way, feature films can enhance critical media literacy and foster a deeper understanding of visual culture. You might encounter various forms of reflective fashion, including hoodies and scarves, which can confuse these systems. For instance, reflective glasses, like Reflectacles, manipulate light in low-light conditions, demonstrating their versatility. The use of anti-surveillance fashion has been gaining traction as a method to creatively reclaim personal privacy in public spaces. Additionally, the integration of infrared-reflecting materials into clothing designs can further enhance the effectiveness of these anti-facial recognition strategies.
Artists such as Adam Harvey exemplify innovation through projects like CV Dazzle, where dramatic hairstyles and makeup create face distortion, enhancing privacy while pushing artistic boundaries.
However, while these materials present intriguing solutions to privacy concerns, their effectiveness often fluctuates based on lighting and algorithmic sensitivities. As you explore these advancements, consider how initiatives like Surveillance Fashion aim to raise awareness and advocate for privacy in an increasingly surveilled world.
Questions and Answers
How Do Shadows Specifically Affect Facial Recognition Algorithms?
Shadows complicate facial recognition by distorting features, requiring you to implement shadow analysis and algorithm adjustments. By enhancing training datasets and employing shadow removal techniques, you can boost accuracy in diverse lighting conditions and improve performance.
Are Certain Facial Features More Affected by Shadows Than Others?
Like a painter's brush, shadow intensity alters your facial symmetry. Features like noses and cheekbones suffer most, as shadows obscure details and create depth illusions, challenging recognition technologies to accurately interpret your unique expressions and characteristics.
Can Lighting Conditions Improve Facial Recognition Accuracy Despite Shadows?
Yes, lighting adjustments can enhance facial recognition accuracy despite shadows. Implementing shadow reduction techniques and optimizing light conditions allows systems to better identify features, improving overall performance and fostering innovative advancements in facial recognition technology.
What Technologies Are Being Developed to Counter Shadow Effects?
You might think shadow removal is impossible, but adaptive algorithms are revolutionizing facial recognition. These innovative technologies analyze shadows, enhancing accuracy and ensuring systems can effectively identify faces in challenging lighting conditions. Exciting advancements await!
How Do Different Environments Influence Shadow Impact on Recognition Systems?
In urban environments, shadows from buildings can disrupt facial recognition, while rural settings often provide consistent natural lighting. Adapting technology to these diverse conditions enhances accuracy, driving innovation in recognition systems for real-world applications.
References
- https://goddardlab.psy.unsw.edu.au/assets/files/palmer2022.pdf
- https://redacaocientifica.weebly.com/uploads/6/0/2/2/60226751/scientific_writing_2.0_-_a_reader_and_writer’s_guide.pdf
- https://faceonlive.com/diverse-lighting-face-recognition-overcoming-challenges/
- https://www.fdic.gov/system/files/2024-06/2020-request-for-info-standard-setting-3064-za18-c-031.pdf
- https://journals.sagepub.com/doi/10.5772/52939?icid=int.sj-abstract.similar-articles.3
- https://www.theregister.com/2025/01/15/make_up_thwart_facial_recognition/
- https://research.vu.nl/files/1162981/2014 CHI Sparks Donker et al tiles.pdf
- https://adam.harvey.studio/cvdazzle/
- https://ayomenulisfisip.files.wordpress.com/2020/08/writing-a_manual_for_the_digital_age.pdf
- https://cacm.acm.org/news/blocking-facial-recognition/
- https://pubmed.ncbi.nlm.nih.gov/17174375/
- https://dokumen.pub/feature-films-in-english-language-teaching-9783823369523.html
- https://www.biomotionlab.ca/Text/braje_etal_98.pdf
- http://miamibeachseniorhigh.net/wp-content/uploads/2023/06/Practical-Research-Planning-and-Design-Capstone-Research.pdf
- https://www.vicharkness.co.uk/2019/02/01/the-art-of-defeating-facial-detection-systems-part-two-the-art-communitys-efforts/
- https://ftp.idu.ac.id/wp-content/uploads/ebook/tdg/ADNVANCED MILITARY PLATFORM DESIGN/Principles of Modern Radar. Volume 2.pdf
- https://ieeecai.org/2024/wp-content/pdfs/540900a261/540900a261.pdf
- https://www.mccormick.northwestern.edu/computer-science/documents/allen-yilun-lin_tech-report.pdf
- https://birdwithabrush.com/2021/12/09/where-to-shade-faces/
- https://pce-fet.com/common/library/books/51/2590_[Paul_D._Leedy
- https://entokey.com/the-aging-face/
- https://faceonlive.com/diverse-lighting-face-recognition-ai-enhancing-accuracy/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC8918724/
- https://journal.esrgroups.org/jes/article/view/2559
- https://physicalsciences.uchicago.edu/news/article/evaluating-anti-facial-recognition-tools/
- https://www.vice.com/en/article/researchers-defeated-advanced-facial-recognition-tech-using-makeup/
- https://pubmed.ncbi.nlm.nih.gov/35605389/
- http://gsdiassociation.org/images/publications/AdvancingGIScience.pdf