To enhance your public privacy, consider adopting effective face concealment techniques. Wide-brimmed hats and sunglasses provide immediate coverage from direct view, while masks facilitate anonymity and thwart facial recognition systems. Dynamic makeup techniques, such as contrasting patterns, can visually disrupt your facial symmetry; alternatively, hoodies and scarves offer additional layers of obfuscation. By incorporating fashionable elements designed for privacy, like anti-surveillance accessories, you keep both style and security in mind. Explore further strategies to verify their effectiveness.
Quick Takeaways
- Utilize wide-brimmed hats and sunglasses to shield your face from UV rays and enhance privacy in public spaces.
- Employ masks designed with anti-surveillance technology to conceal your identity and thwart facial recognition systems.
- Incorporate hoodies and scarves that obscure facial features while providing warmth and style simultaneously.
- Experiment with contrasting makeup patterns, like CV Dazzle, to disrupt facial symmetry and evade detection.
- Choose clothing with camouflage patterns or IR-reflective fabrics to protect against surveillance and maintain personal privacy.
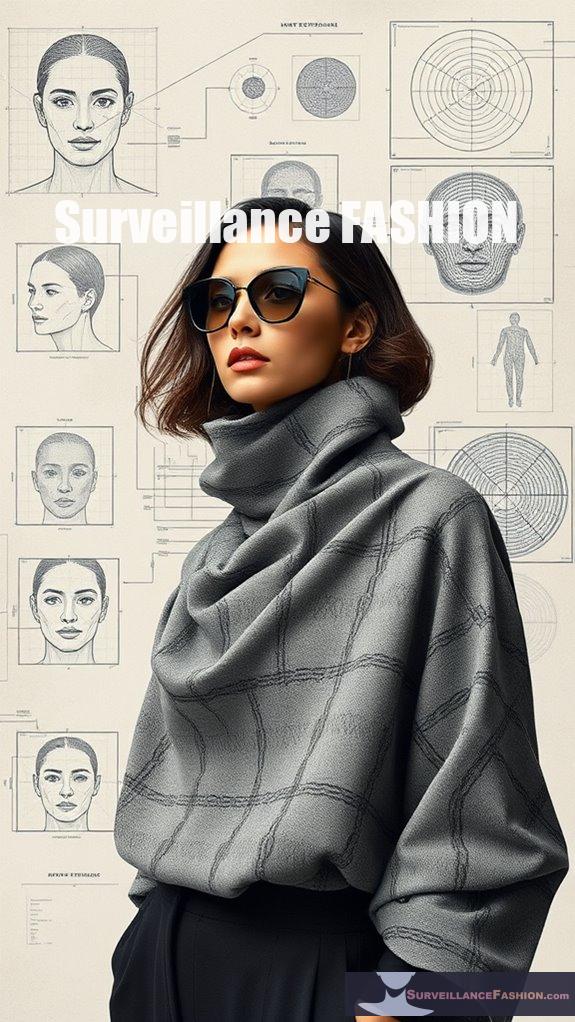
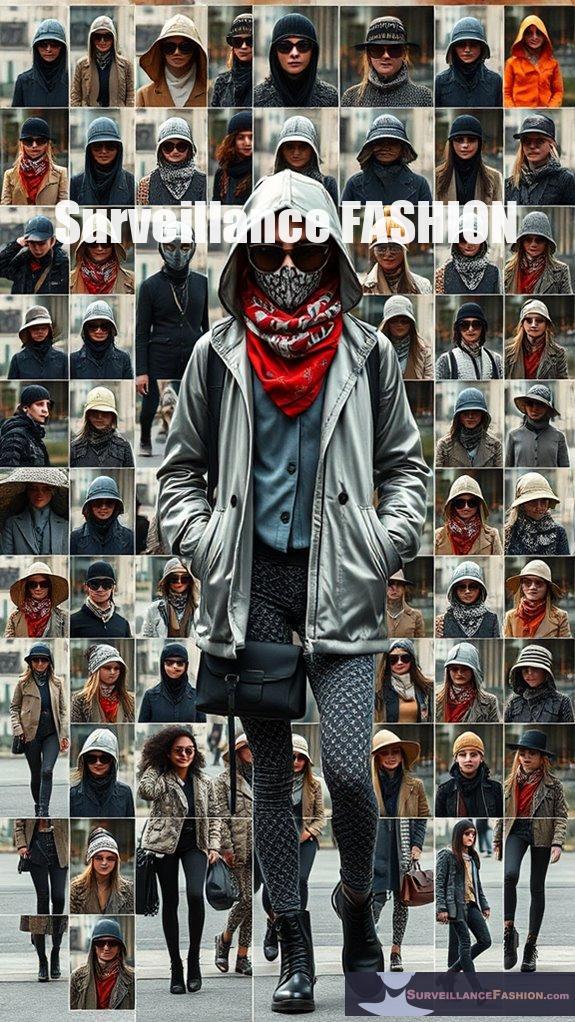
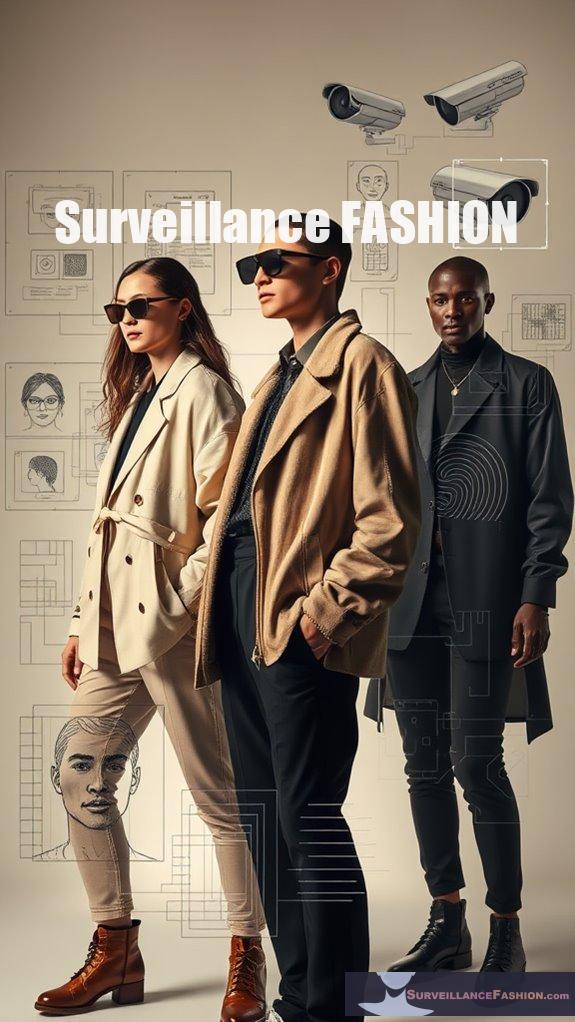
Wide-brimmed Hats and Sunglasses

When considering effective face concealment techniques, wide-brimmed hats and sunglasses emerge as two prominent allies, each offering distinct advantages for both privacy and protection.
Wide-brimmed benefits are clear; styles like sun hats and bucket hats provide substantial coverage for your face, neck, and ears, effectively shielding you from harmful UV rays. Their larger brims are vital, especially during midday sun, while UPF 50+ materials enhance protection. In fact, studies show that a wide-brimmed hat can provide up to 76% protection from UV radiation, making it an essential accessory for outdoor activities. Additionally, wearing a wide-brimmed hat can help you stay under the radar in a world filled with anti-surveillance technology, promoting a sense of privacy.
Wide-brimmed hats offer essential protection from UV rays, shielding your face, neck, and ears while enhancing your style.
Conversely, the variety of sunglass styles allows you to choose options that not only conceal your eyes but also filter UV radiation, reducing glare and potential eye damage.
Combining these two elements guarantees you maintain privacy while protecting your skin and eyes, which aligns with the ethos of our website, Surveillance Fashion, where personal safety meets style.
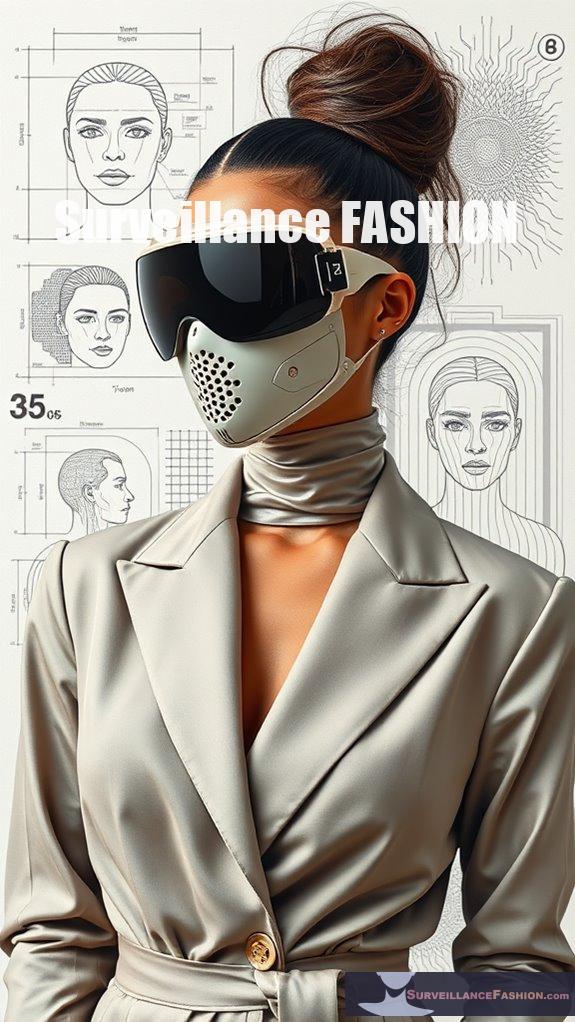
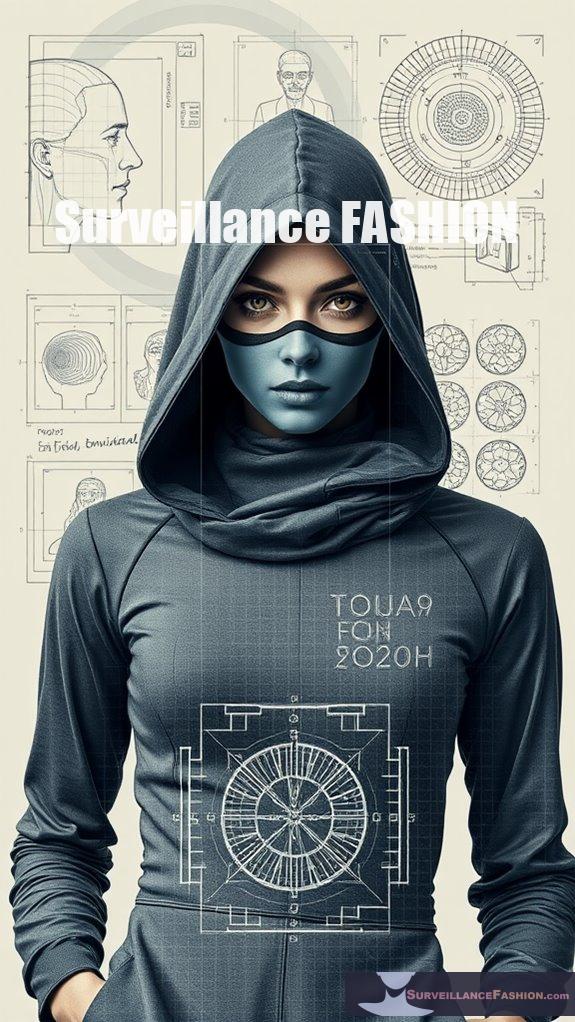
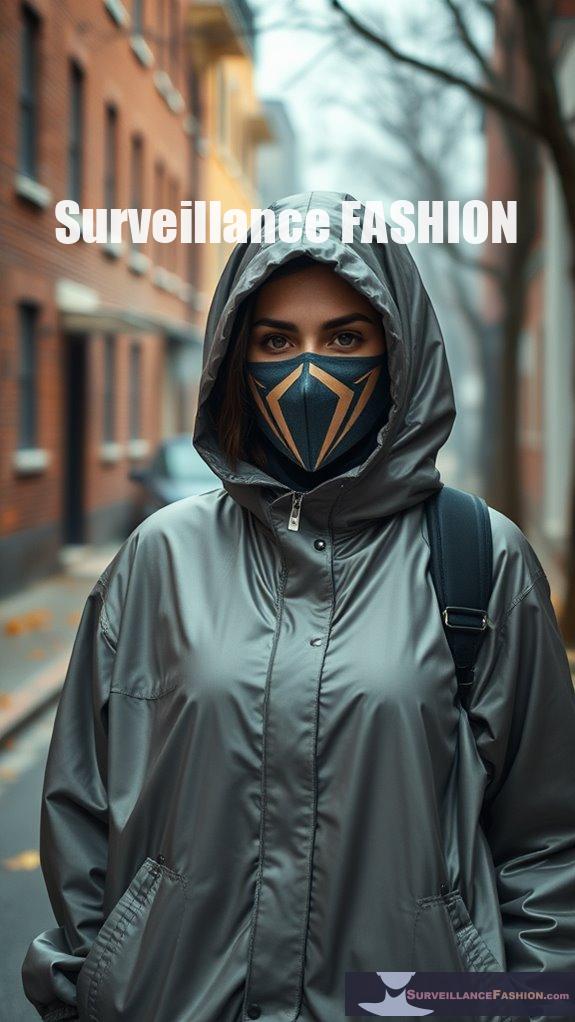
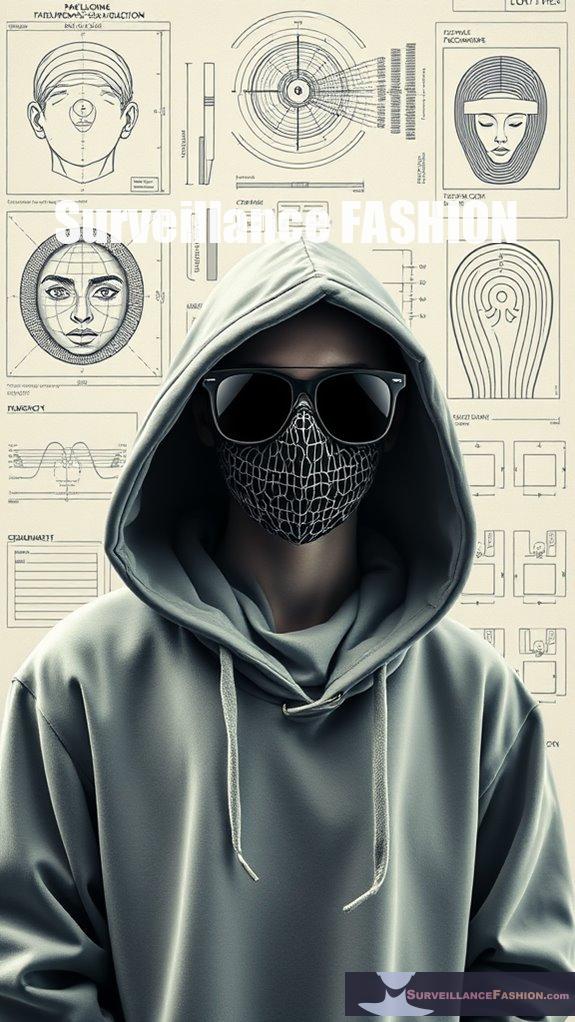
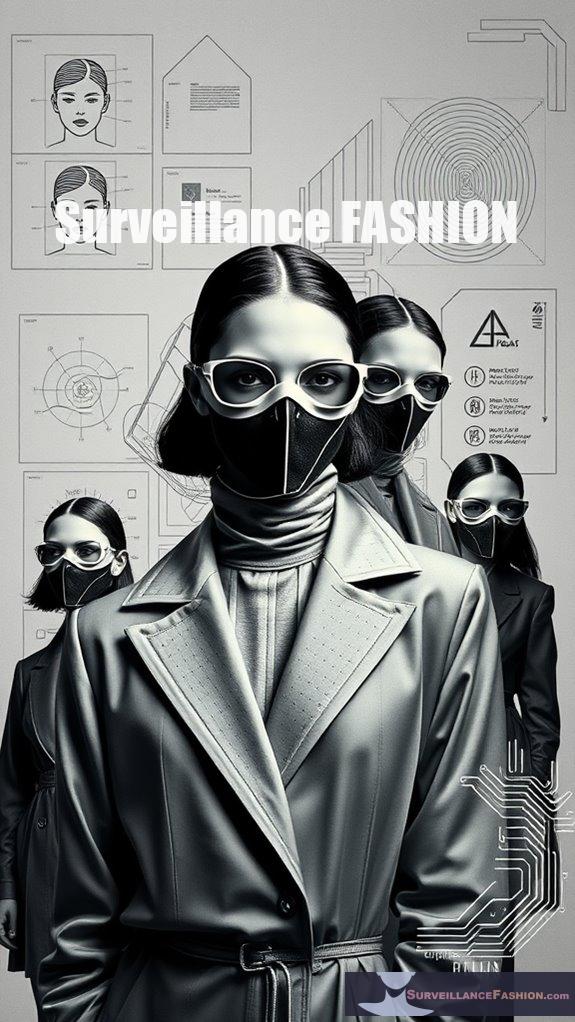
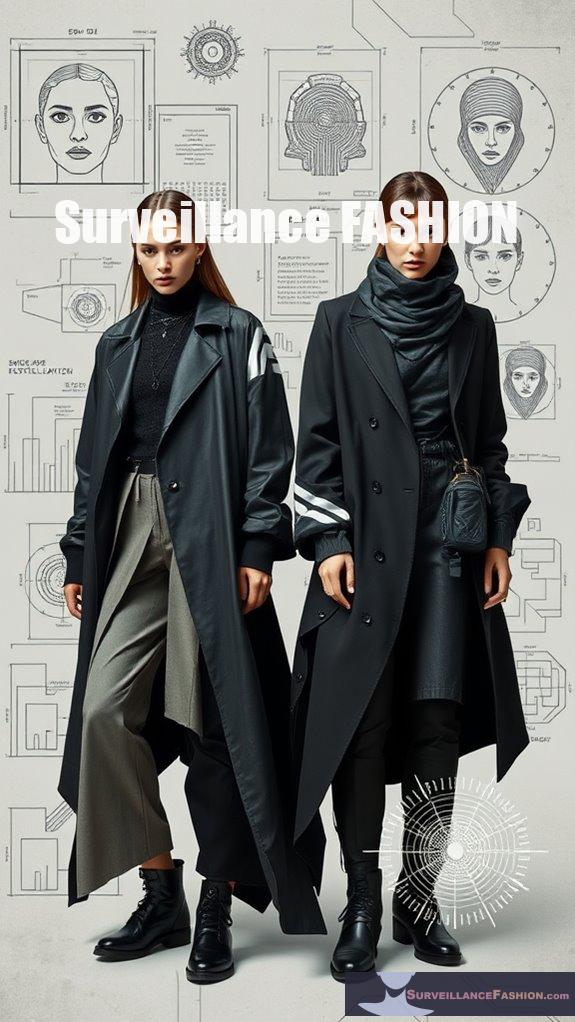
Masks for Anonymity

Masks for anonymity serve as a multifaceted tool in contemporary society, addressing both the desire for privacy and the need for protection against invasive surveillance technologies. The evolution of mask technology has led to designs that not only conceal identity but also complicate facial recognition systems, thereby enhancing personal security. Disguise and deceit are not only coercive but also tactical for the weak, highlighting the strategic use of masks in various contexts. Additionally, certain masks are specifically designed with anti-surveillance technology to thwart AI detection, showcasing the innovative intersection of fashion and security.
| Mask Type | Cultural Significance |
|---|---|
| Balaclavas | Used in protests worldwide |
| Guy Fawkes Mask | Symbol of anonymity |
| Face Tubes | Popular in outdoor sports |
| Anti-Surveillance | Engineered to confuse AI |
The cultural implications of masks are profound, reflecting societal values surrounding privacy. As we navigate increasing surveillance, understanding these tools allows you to reclaim control over your public persona, which is why we created Surveillance Fashion.
Contrasting Makeup Patterns

Contrasting makeup patterns represent a strategic approach to facial concealment, utilizing the interplay of color and texture to enhance anonymity in an increasingly surveilled world.
By applying principles of color theory, you can manipulate visual perception, effectively obscuring your facial features from detection algorithms.
For instance, employing CV Dazzle techniques, you might contrast light shades against darker skin or vice versa, thereby disrupting facial symmetry.
Alternatively, enhancing natural contrasts—such as emphasizing the differences between skin tone, eye color, and hair—enables a more subtle yet effective concealment.
These customizable designs allow you to target specific algorithms, providing both artistic expression and enhanced privacy.
Moreover, understanding facial recognition challenges can significantly improve your techniques for evading detection.
Through thoughtful application, you can achieve a dramatic or intricate look, adapting to your public surroundings with confidence.
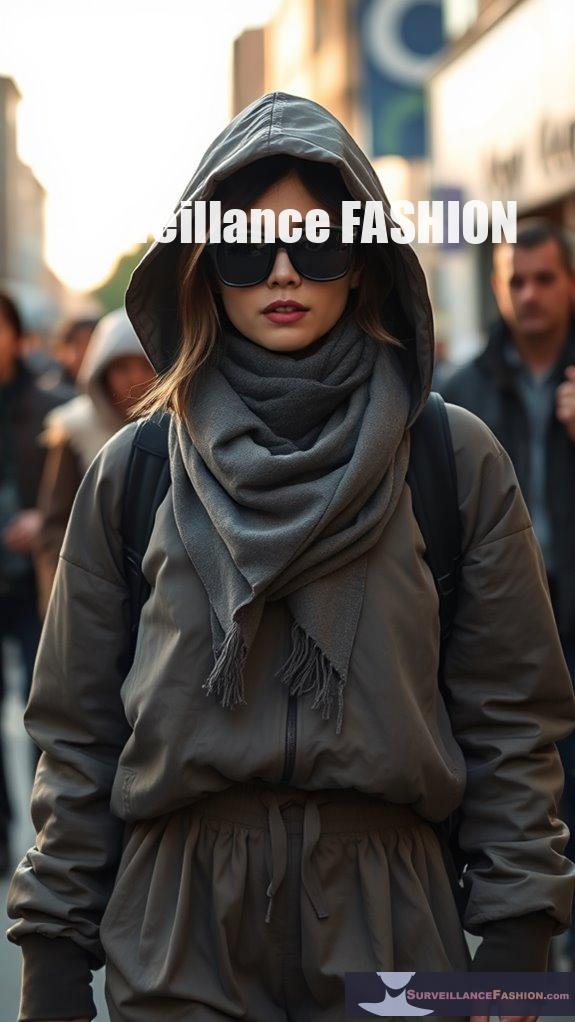
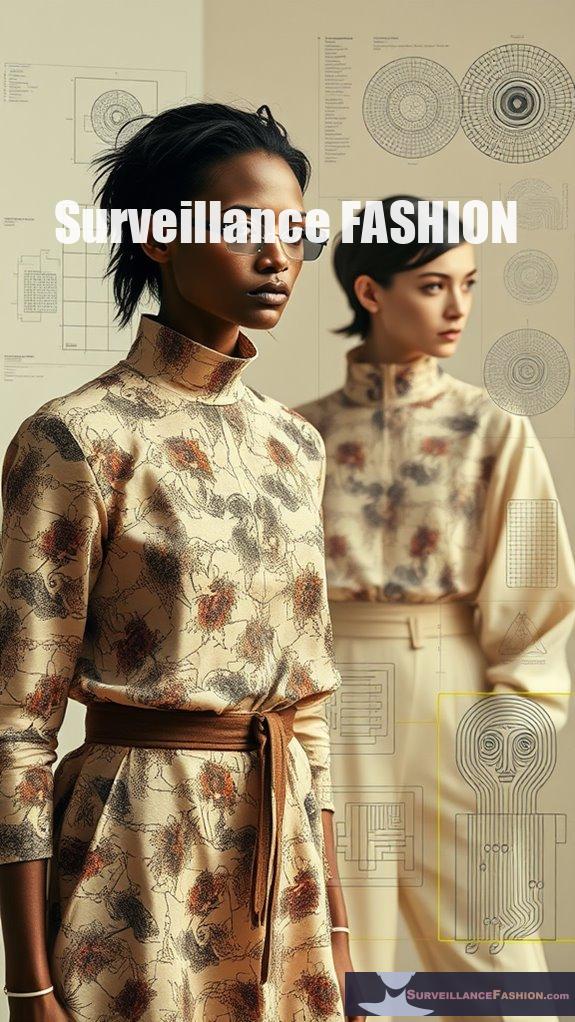
Hoodies and Scarves

As fashion evolves in response to societal changes, the integration of hoodies and scarves into daily attire reflects a growing awareness of personal privacy and identity concealment.
Hoodie designs, particularly those with built-in face coverings, serve a multi-purpose function; they protect against cold and wind while offering a quick way to obscure your identity. These versatile garments, available in various sizes and colors, can easily be adjusted to suit your environment.
Scarves, especially those featuring innovative patterns, provide additional layers of concealment. For instance, reflective scarf patterns can disrupt facial recognition technology, allowing you to maintain anonymity in public spaces. Additionally, anti-surveillance scarves are becoming a trendy accessory, blending style with privacy protection.
Infrared LED Glasses

Innovative technology often shapes our understanding of privacy, and infrared LED glasses exemplify this intersection of fashion and surveillance deterrence.
These glasses emit infrared light, invisible to the human eye yet detectable by digital cameras, effectively obscuring your facial features from facial recognition systems.
Positioned strategically around the frame, the infrared LEDs create bright spots in captured footage, providing an unobtrusive means of maintaining anonymity in public areas.
Unlike masks or wide-brimmed hats, these glasses allow for full peripheral vision while blending seamlessly into social settings.
As the environment of surveillance evolves, understanding tools like infrared technology is essential. Anti-surveillance clothing has become a significant focus for those seeking privacy in a digitally monitored world.
At Surveillance Fashion, we aim to empower you with techniques that enhance your control over personal privacy, ensuring you navigate public spaces with confidence.
Dynamic Makeup Techniques

Dynamic Makeup Techniques
Dynamic makeup techniques have transformed the scenery of personal aesthetics, allowing individuals to manipulate their features with precision and artistry. You can enhance your look through advanced methods that provide full control over your appearance.
- Underpainting and Sandwiching: Applying concealer before or between foundation layers enhances coverage while allowing for effective texture blending.
- Color Correction: Utilizing color-correcting concealers, like peach for dark circles, provides a seamless finish that balances skin tones.
- Contouring with Concealer: Employing darker shades strategically creates depth, sculpting your facial structure for an elevated look.
These techniques not only enhance your features but also cater to the desire for privacy and concealment, a concept that fuels our purpose at Surveillance Fashion. Additionally, mastering anti-surveillance techniques can empower you to further obscure your facial features from recognition technologies.
Embrace these dynamic methods to elevate your makeup artistry.
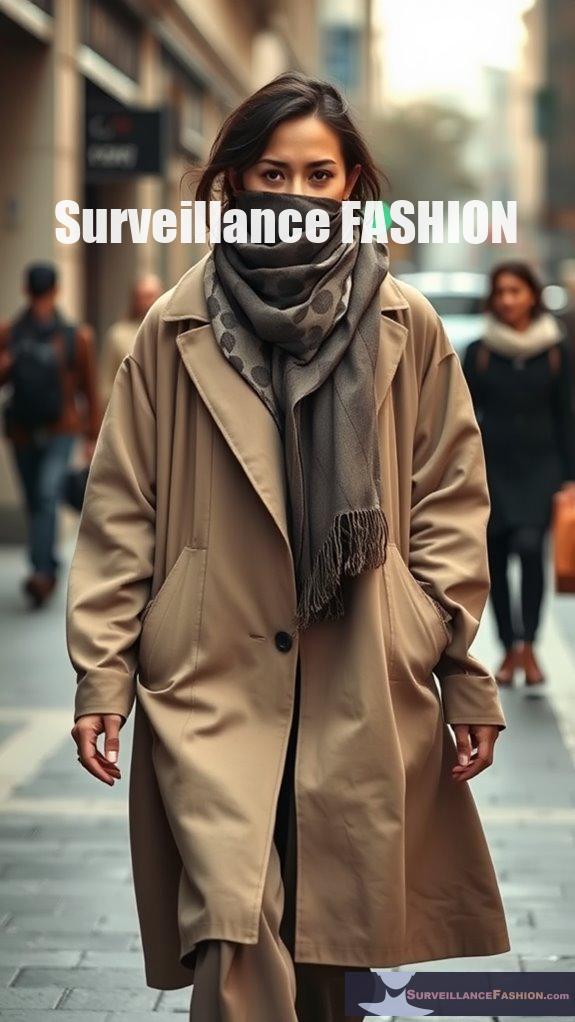
Blending Makeup With Clothing

Blending makeup with clothing represents a subtle approach to personal aesthetics, particularly when one seeks to create a seamless and cohesive look.
To achieve this, focus on color coordination; selecting makeup shades that harmonize with your clothing's dominant colors can effectively enhance camouflage. For instance, earthy tones in foundation and concealer often meld well with various textures and shades, ensuring minimal visibility.
Texture matching plays a critical role as well; opting for smooth, matte fabrics helps prevent contrasting distractions. Additionally, employing anti-facial recognition techniques can further enhance your ability to remain unnoticed in public settings.
Avoid bold patterns, which can disrupt the visual flow, and instead, choose neutral shades that complement your makeup.
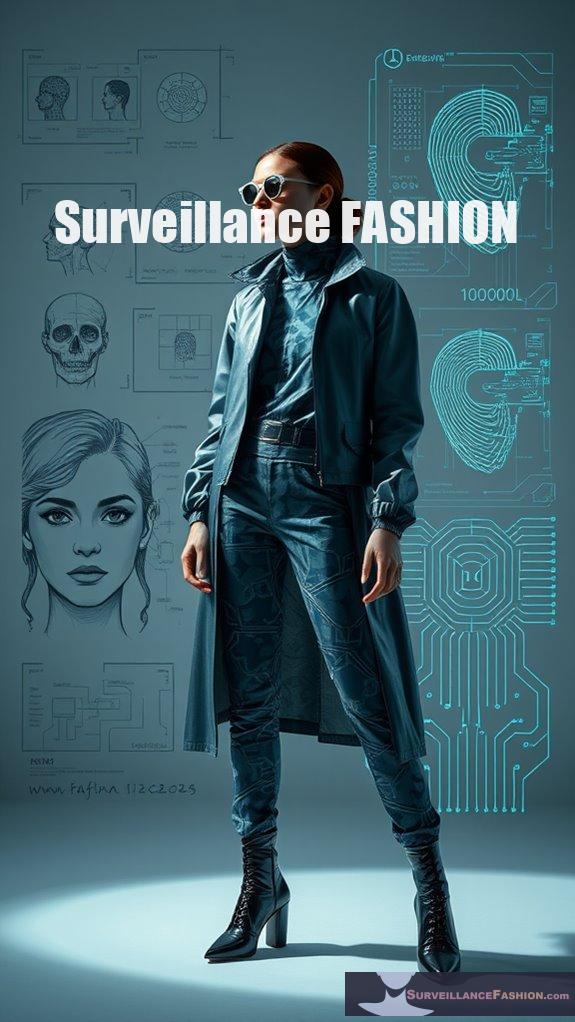
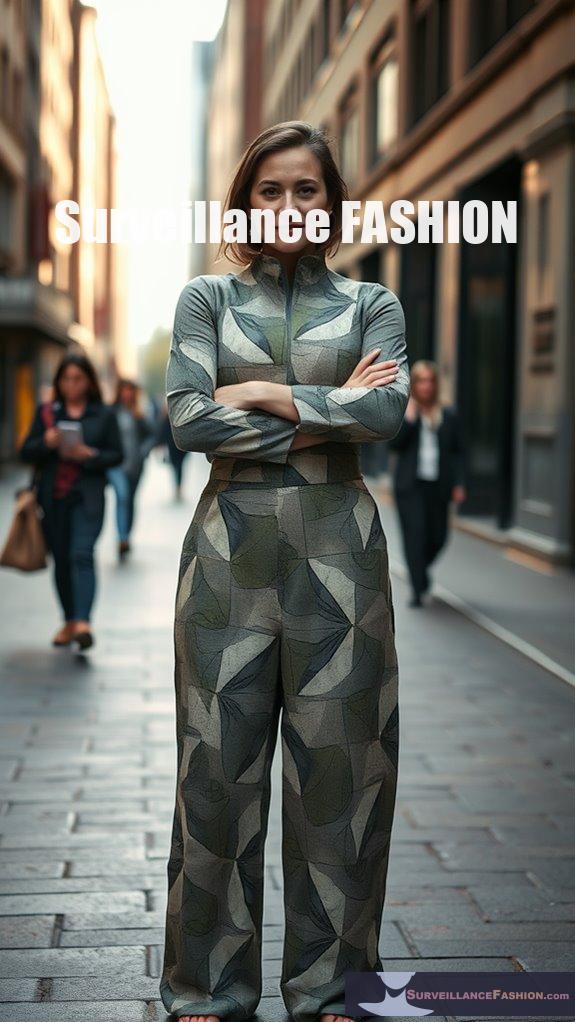
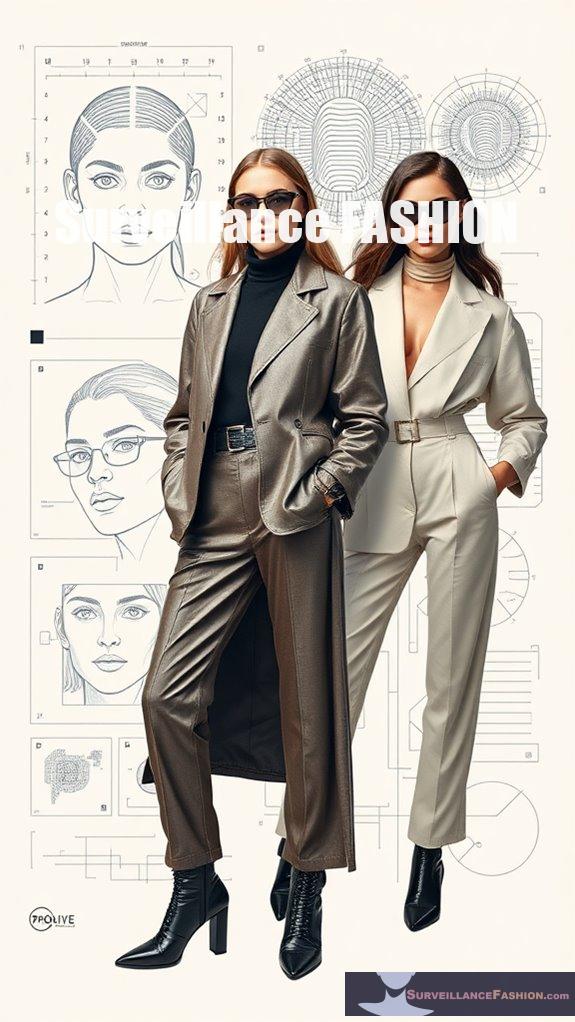
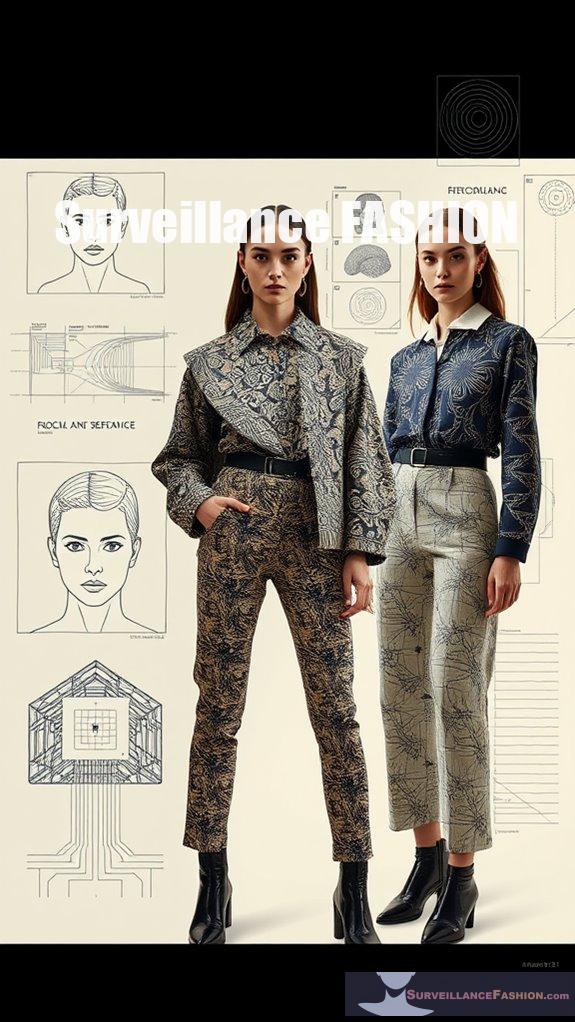
Fashion for Privacy Protection

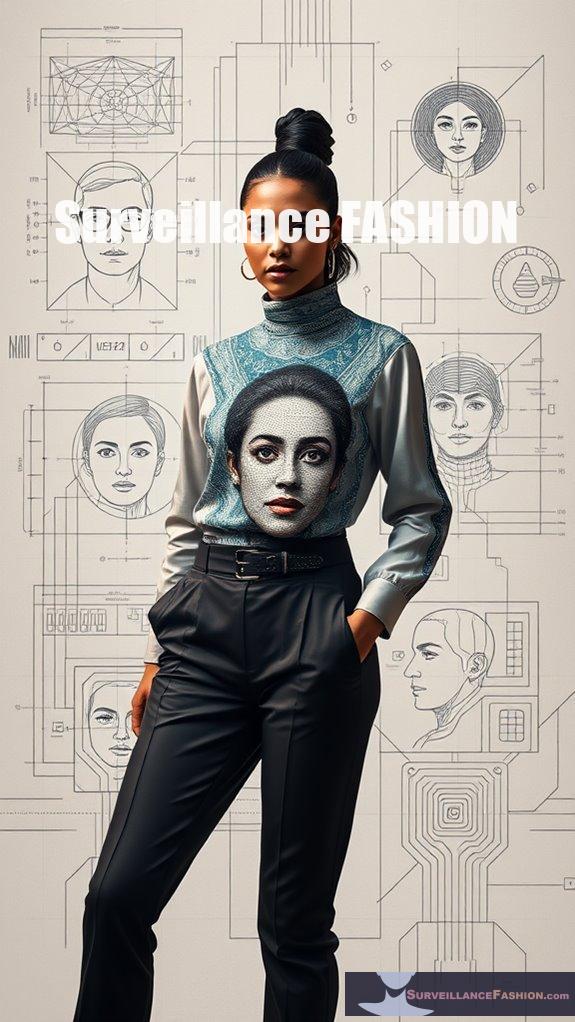
As societal concerns about privacy intensify amidst technological advancements, fashion has begun to emerge as a powerful tool for personal protection against surveillance.
By embracing innovative designs and privacy enhancing textiles, you can assert control over your personal space. Here are three effective options to take into account:
- Camouflage Patterns: These complex designs can disrupt facial recognition software, making it difficult for algorithms to identify you.
- IR-Reflective Fabrics: Such textiles help reduce detection by night-vision cameras, enhancing your anonymity in dim environments.
- Signal-Blocking Fabrics: These materials protect your personal information by blocking RFID signals from devices like credit cards.
Additionally, many brands are now utilizing pattern-based camera-confusing clothing designs to further enhance their surveillance-resistant offerings.
Ultimately, anti surveillance clothing offers a proactive approach to safeguarding your privacy in an increasingly monitored world.
This is a concept we aim to explore through our website, Surveillance Fashion.
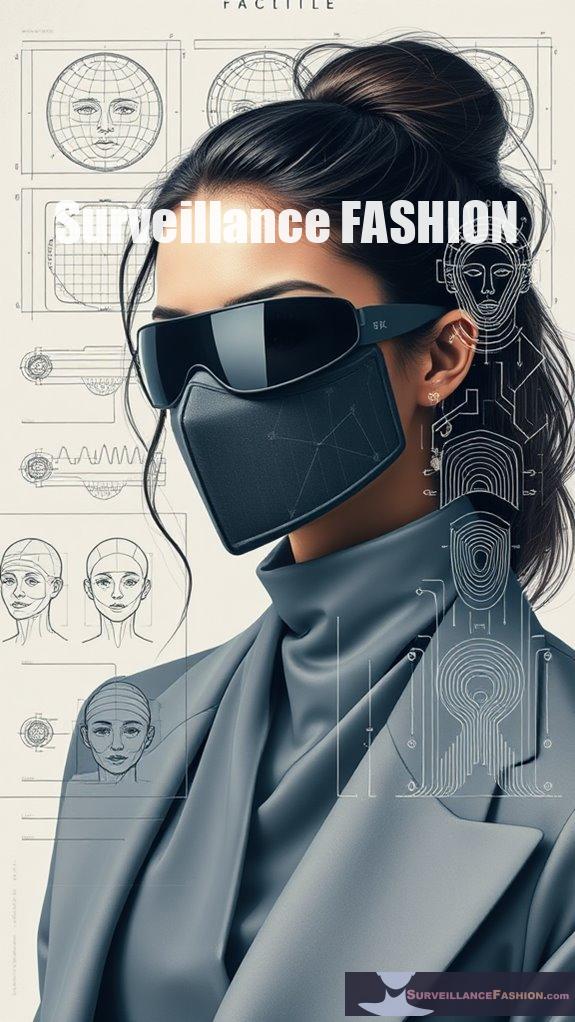
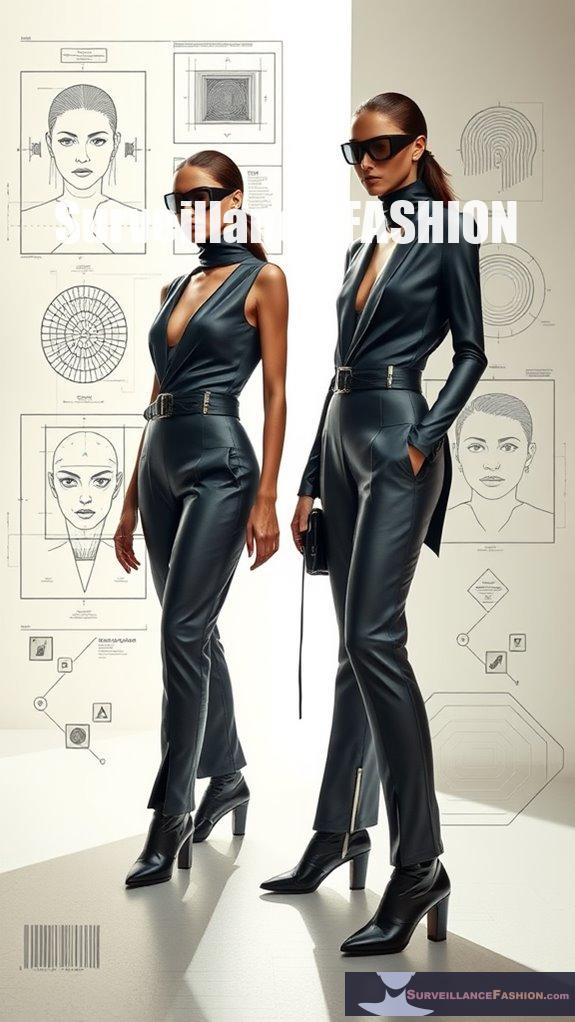
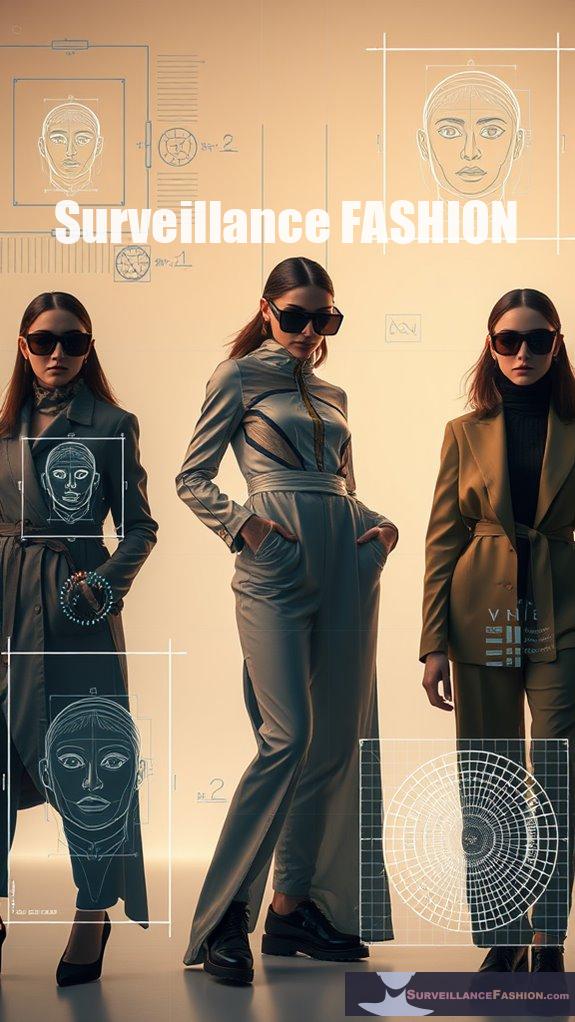
Anonymizing Fashion Accessories

In an era where surveillance technologies are ubiquitous, the need for effective anonymizing fashion accessories has become increasingly essential. These items not only serve aesthetic purposes but also function as critical tools for privacy protection.
Consider anti-paparazzi scarves, which utilize reflective materials designed to confuse cameras, rendering you less identifiable. Smart textiles, on the other hand, integrate advanced technology that detects surveillance efforts, enhancing your anonymity.
Additionally, face masks and patterned clothing can obscure your features, while elaborate designs distract facial recognition algorithms. Furthermore, accessories that incorporate light-reflecting materials can add an extra layer of security by disrupting the effectiveness of surveillance cameras.
As the demand for privacy-conscious fashion grows, accessories that combine style with protection emerge, reflecting our collective desire for control in an increasingly monitored world.
This website, Surveillance Fashion, aims to explore these trends and empower your choices in privacy.
References
- https://luxand.cloud/face-recognition-blog/how-to-fool-and-avoid-facial-recognition-in-public-places
- https://letrunghieutvu.yolasite.com/resources/w-lawrence-neuman-social-research-methods_-qualitative-and-quantitative-approaches-pearson-education-limited-2013.pdf
- https://manhattan.institute/article/model-legislation-to-modernize-anti-kkk-masking-laws-for-intimidating-protesters
- https://elearning.shisu.edu.cn/pluginfile.php/35310/mod_resource/content/2/Research-Intro-Flick.pdf
- https://www.genetec.com/blog/products/static-vs-dynamic-privacy-masking
- https://pubmed.ncbi.nlm.nih.gov/29682802/
- https://www.arpansa.gov.au/understanding-radiation/radiation-sources/more-radiation-sources/sun-protection-hats
- https://www.solbari.com/blogs/solbari-blog/wide-brim-sun-hat-or-sunscreen-which-is-better-for-sun-protection
- https://ericjavits.com/blogs/news/bucket-hat-vs-sun-hat
- https://www.youtube.com/watch?v=eX-2nH7XXZA