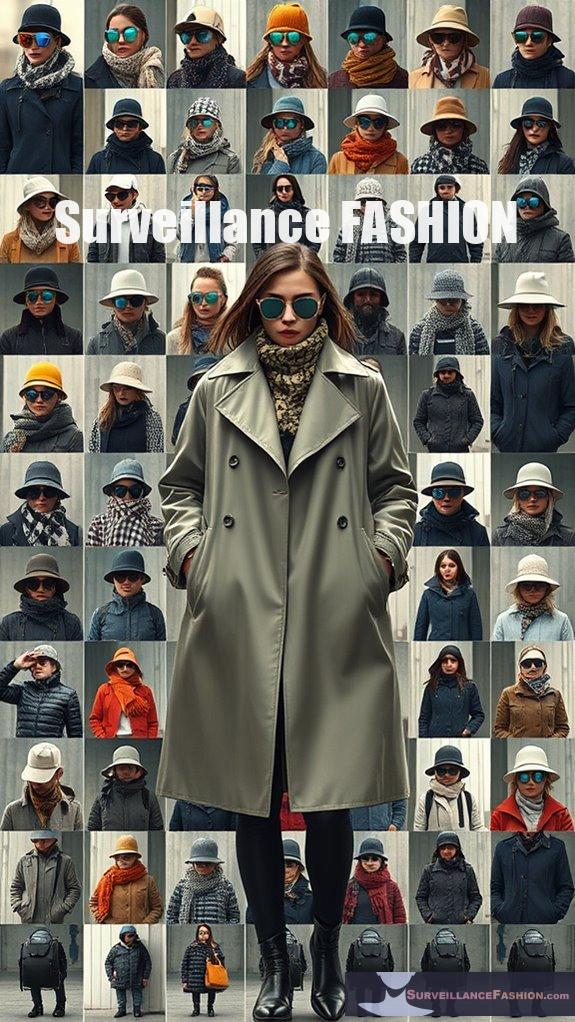
Infrared accessories protect your privacy from surveillance by utilizing materials designed to reflect infrared light, effectively obscuring your identity from various monitoring systems. For example, clothing made with infrared-reflective fabrics disrupts infrared-sensitive cameras, rendering you nearly invisible in public spaces. The integration of these technologies fosters a new wave of privacy-focused fashion, allowing for discreet anonymity. Our website, Surveillance Fashion, highlights these innovations, showcasing how they blend style with privacy concerns, revealing more perspectives into this changing environment.
Quick Takeaways
- Infrared accessories reflect IR light, disrupting the effectiveness of IR-sensitive cameras used in surveillance.
- Innovative fabrics engineered to block or reflect infrared wavelengths help conceal identity from thermal imaging systems.
- AI-generated patterns on clothing confuse facial recognition algorithms, enhancing wearer anonymity in public spaces.
- Strategic placement of infrared LEDs can obscure camera views, providing additional layers of privacy protection.
- The integration of privacy-enhancing materials in fashion raises awareness and addresses growing concerns over surveillance and personal data rights.
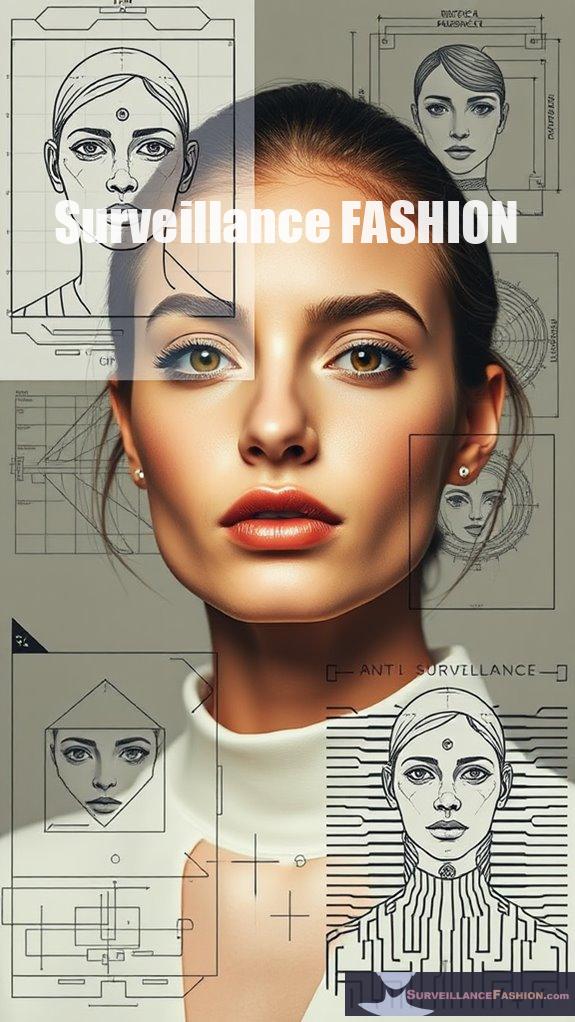
Understanding Infrared-Reflecting Materials
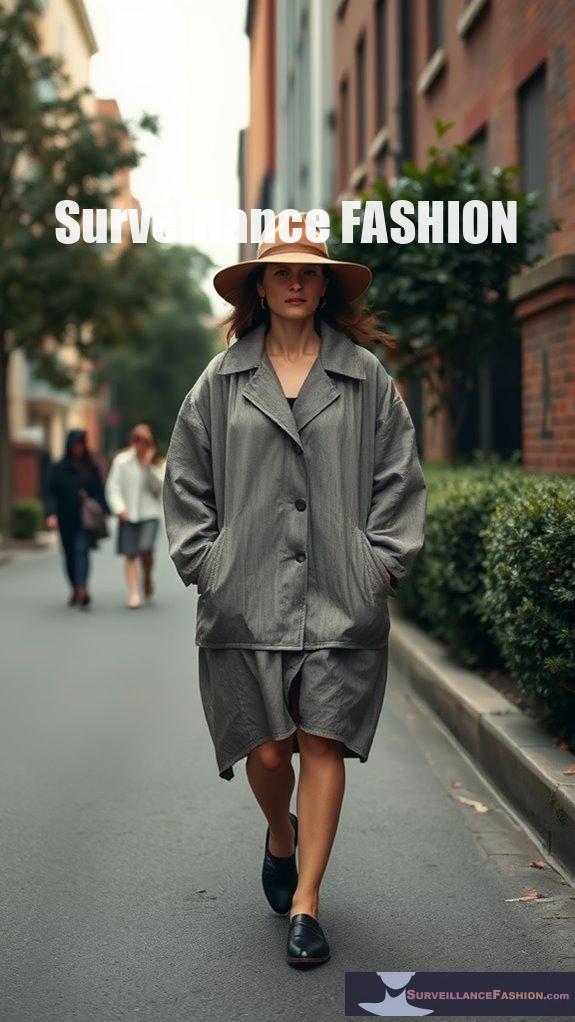
Understanding infrared-reflecting materials is essential for various applications ranging from thermal management to optical systems, especially as the demand for privacy and security technologies continues to rise. The development of anti-surveillance clothing has significantly influenced the market, promoting greater awareness of the need for such technologies.
These infrared materials, characterized by their high reflectivity and low absorbance, play an important role in ensuring ideal optical performance. For example, metals like silver and aluminum exhibit significant infrared reflectivity, making them ideal choices for coatings. Their multilayered designs minimize visual light reflection while maximizing infrared reflection, enhancing their effectiveness in thermal applications.
Moreover, understanding the index of refraction helps you select materials that interact favorably with infrared radiation. By choosing the right infrared materials, you can gain greater control over your privacy, critical in a world where surveillance is pervasive, a concept we've explored extensively at Surveillance Fashion. Additionally, the development of infrared-resistant fabrics has opened new avenues for creating fashionable privacy wear that can effectively shield individuals from unwanted surveillance.
Designing Effective DIY Accessories for Privacy Protection
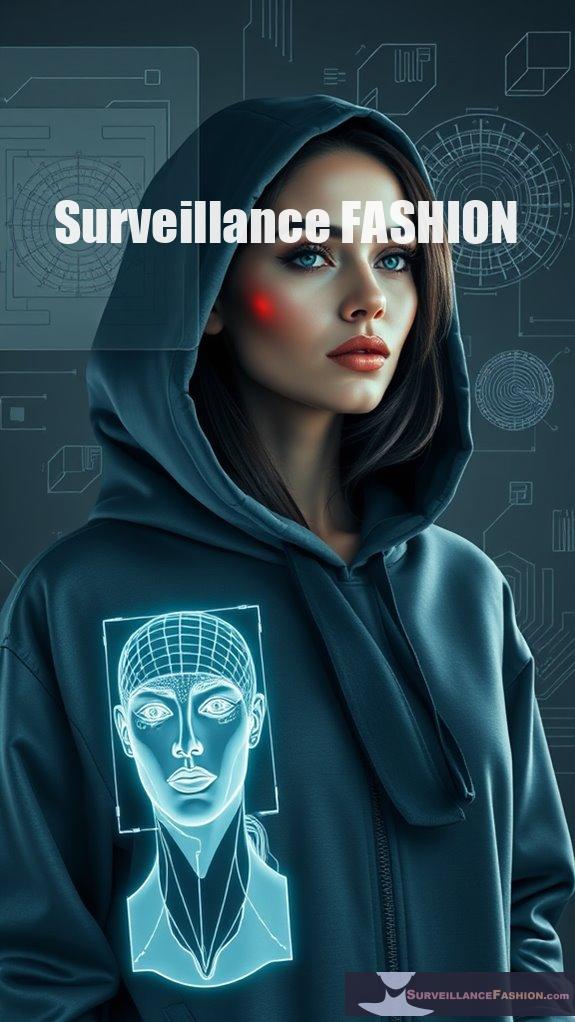
In an era increasingly defined by surveillance, the ability to craft your own privacy-protecting accessories can empower individuals to reclaim their anonymity in public spaces.
To design effective DIY accessories, consider the strategic placement of IR LEDs, ensuring they create strobe effects that can obscure camera views. For instance, integrating an array of IR LEDs into a "Camera-Shy Hoodie" can greatly disrupt night vision footage, rendering your image indistinguishable. The use of thermal imaging technology can be countered by these innovative designs, allowing for greater personal security.
Strategically placed IR LEDs can effectively obscure camera views, making your "Camera-Shy Hoodie" a powerful tool for privacy.
Moreover, utilizing off-the-shelf components like security camera IR arrays simplifies the assembly process, allowing for innovative customization. By harnessing low-voltage power supplies, you can enhance durability and portability. Additionally, incorporating infrared-blocking fabrics into your designs can provide an extra layer of protection against thermal imaging technologies.
Ultimately, these projects not only foster personal privacy but also contribute to a broader dialogue about surveillance, a core motivation behind our website, Surveillance Fashion.
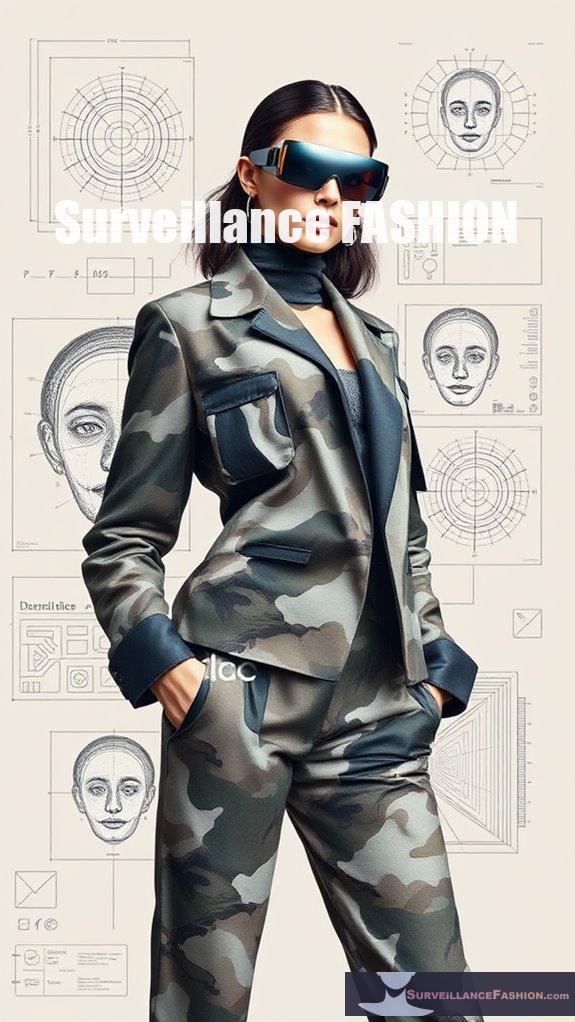
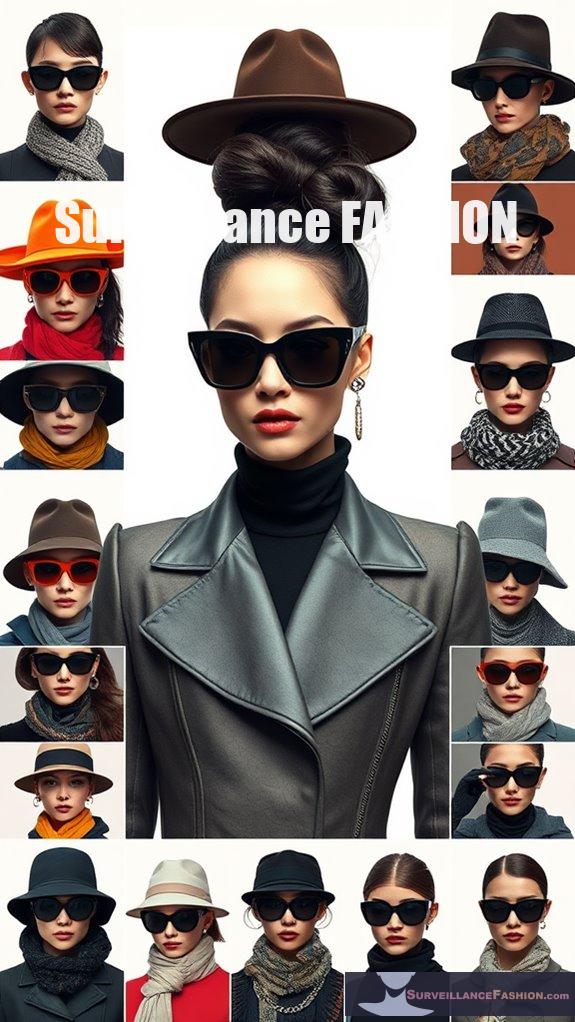
Clothing That Thwarts Facial Recognition
As concerns about surveillance continue to escalate, innovative clothing designed to thwart facial recognition technology emerges as a crucial response to privacy erosion in public spaces.
Cap_able, an Italian start-up, has developed privacy fashion that employs AI-generated patterns, effectively deceiving facial recognition systems. Tested with YOLO, a renowned object detection system, these garments, including jumpers and trousers, feature knitted adversarial patches that can make wearers appear as animals, thereby avoiding detection.
This face-specific protection allows individuals to maintain their identity without the need for face coverings. Such biometric defense not only enhances personal privacy in public but also sparks essential discussions about the implications of surveillance, a goal that aligns with the mission of our platform, Surveillance Fashion, to raise awareness on privacy rights. Additionally, these garments utilize infrared-reflecting materials that enhance their effectiveness against sophisticated camera systems.
Infrared-Reflective Fashion Innovations

The evolution of privacy-enhancing technologies has given rise to a new wave of fashion innovations, particularly in the domain of infrared-reflective materials. These fabrics, engineered to reflect infrared light, disrupt the functionality of IR-sensitive cameras, thereby providing wearers with a layer of anonymity in an era increasingly defined by surveillance.
As fashion technology evolves, designers are creatively integrating these materials into aesthetically pleasing garments, balancing privacy trends with style. For instance, IR-reflective jackets not only conceal the wearer from infrared detection but also serve as a statement piece.
Collaborations between fashion and technology are essential, as they drive the innovation needed to meet the growing demand for privacy-focused clothing, reflecting a society grappling with surveillance and data privacy concerns.
References
- https://www.sunellsecurity.com/smart-ir-cctv-cameras-enhancing-surveillance-with-intelligent-infrared-technology.html
- https://www.oclc.org/content/dam/research/publications/2015/oclcresearch-library-in-life-of-user.pdf
- https://www.ghopto.com/swir-cameras-and-accessories-in-security-surveillance/
- https://www.rand.org/content/dam/rand/pubs/research_reports/RR400/RR443-2/RAND_RR443-2.pdf
- https://montavue.com/blogs/news/what-is-an-infrared-security-camera-and-how-does-it-work
- https://doonuniversity.ac.in/admin/assets/uploads/docs/2023120515231835e218c20a.pdf
- https://www.edmundoptics.com/knowledge-center/application-notes/optics/the-correct-material-for-infrared-applications/
- https://www.nist.gov/document/nist-sp-250-94pdf
- https://www.photonics.com/Articles/Common_Infrared_Optical_Materials_and_Coatings_A/a25495
- https://www.physicsforums.com/threads/metals-as-infrared-reflectors-and-their-temperature.1003601/