To protect your identity during protests, employ discreet digital practices like using VPNs and encrypted messaging, alongside physical disguises such as oversized clothing and creative face paint techniques. For instance, wear masks or oversized hats to obscure identifiable features while utilizing angular makeup designs to disrupt facial recognition systems. Engaging in community coordination further enhances collective privacy. As you continue exploring strategies, you'll uncover even more innovative methods for maintaining anonymity amidst rising surveillance challenges.
Quick Takeaways
- Use secure messaging apps like Signal or WhatsApp to communicate without risking interception.
- Wear masks and oversized clothing to obscure your identity from surveillance cameras.
- Avoid posting identifiable photos or check-ins on social media during protests.
- Utilize creative face paint techniques to disrupt facial recognition technology.
- Keep your devices and sensitive data secure and backed up before attending protests.
Protecting Your Identity During Protests

How can you navigate the complexities of identity protection while actively participating in protests? In a world where digital anonymity often feels elusive, taking proactive steps to safeguard your identity becomes essential, especially in the situation of mass gatherings where surveillance is prevalent.
You can start by utilizing secure communication tools to verify that your conversations remain private and encrypted. Apps like Signal or WhatsApp provide end-to-end encryption, making it far more difficult for unauthorized parties to intercept your messages. Additionally, anti-surveillance methods can help ensure that your communication remains confidential during protests. Grassroots movements often employ community coordination to share these methods effectively.
Furthermore, implementing digital security measures such as full-disk encryption on your devices can protect your data from prying eyes. When you're preparing to attend a protest, consider using a Virtual Private Network (VPN) or the Tor Browser, which helps conceal your IP address and browsing activity, further enhancing your digital anonymity. This way, you can engage in discussions and coordinate actions without fear of being tracked online. Protecting identity is crucial, particularly for those who rely on their devices for organizing protests.
It's vital to think about the physical aspects of identity protection as well. Wearing masks or headgear can obscure your face from surveillance cameras, but always be mindful of local laws regarding face concealment. Moreover, avoiding identifiable clothing or accessories—such as branded items or distinct tattoos—can help you blend into the crowd.
When posting about the protest on social media, refrain from check-ins or sharing images that might reveal your location or identity. This helps create an extra layer of protection for you and your fellow protesters.
Managing your online presence is another significant step. If you're involved in organizing or participating in protests, consider creating new social media accounts dedicated solely to these activities. This allows you to maintain a clear boundary between your personal life and your activism.
Keep in mind to keep these accounts private and avoid tagging others in your posts to protect their identities as well. Keeping event pages private can limit surveillance by authorities, allowing you to focus on the cause without the added stress of unwanted attention.
Before heading out, take some time to prepare your devices for potential confiscation by backing up data and confirming that any sensitive information is secured. Familiarizing yourself with common surveillance methods can empower you to navigate the protest environment more safely.
Carry emergency contact information on paper, as this can be invaluable in unexpected situations.
Ultimately, the key to successfully protecting your identity at protests lies in a blend of awareness and preparation. By understanding the risks and implementing these digital security measures alongside physical identity protection strategies, you can actively participate in meaningful social change while minimizing your exposure to surveillance.
At Surveillance Fashion, we emphasize the importance of being informed and equipped to navigate these challenges, fostering a sense of community among those who seek to advocate for their beliefs without compromising their privacy.
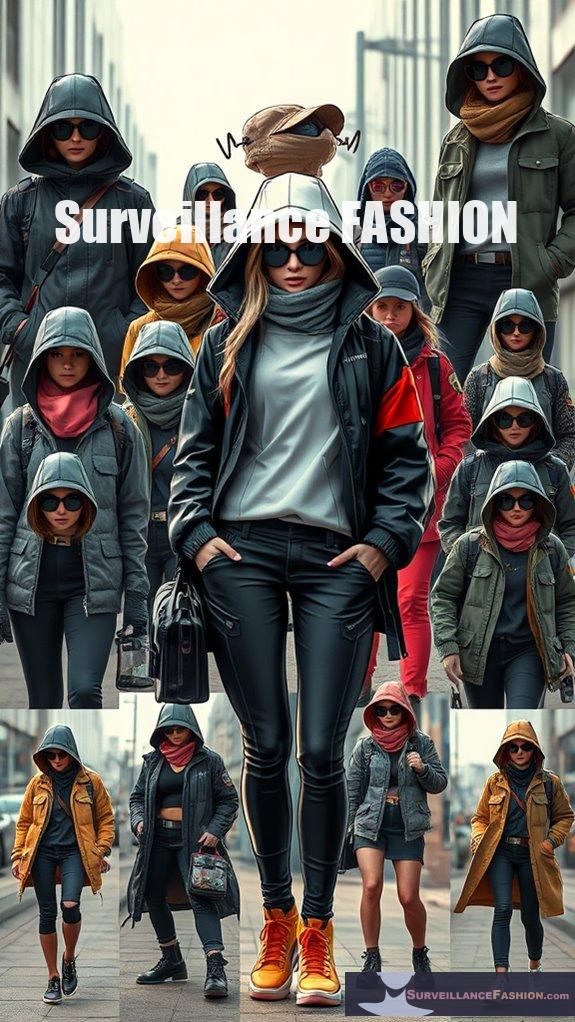
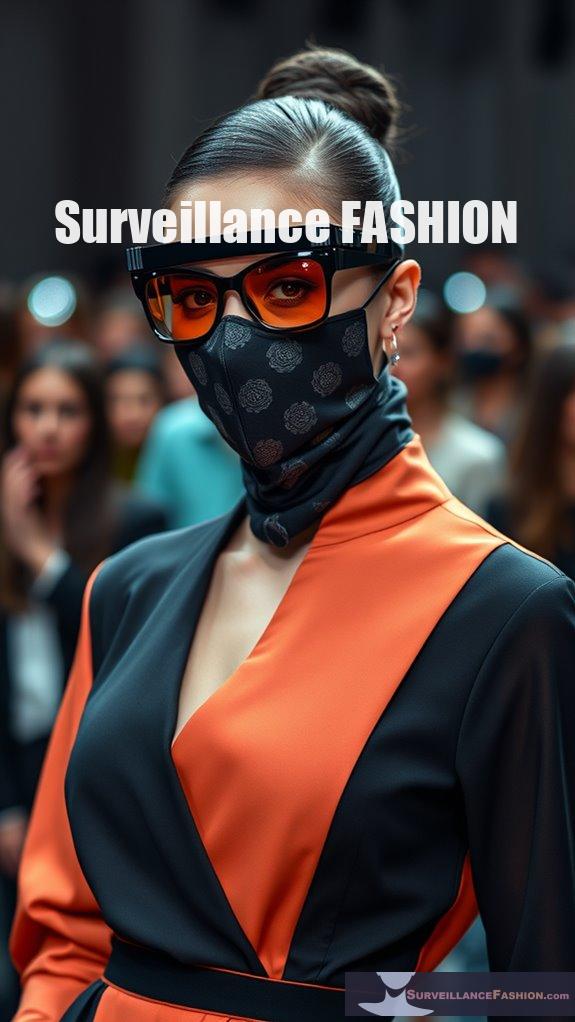
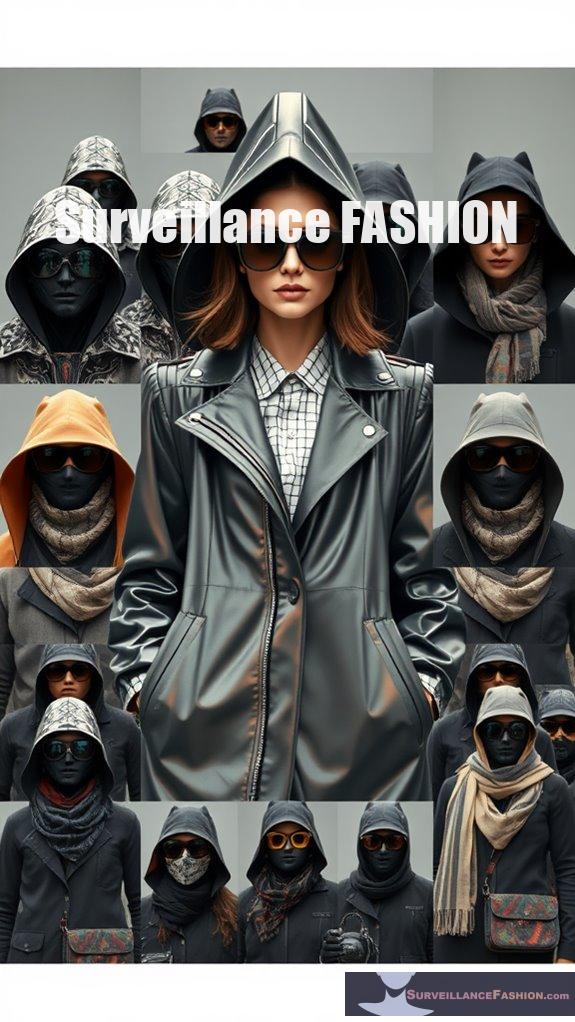
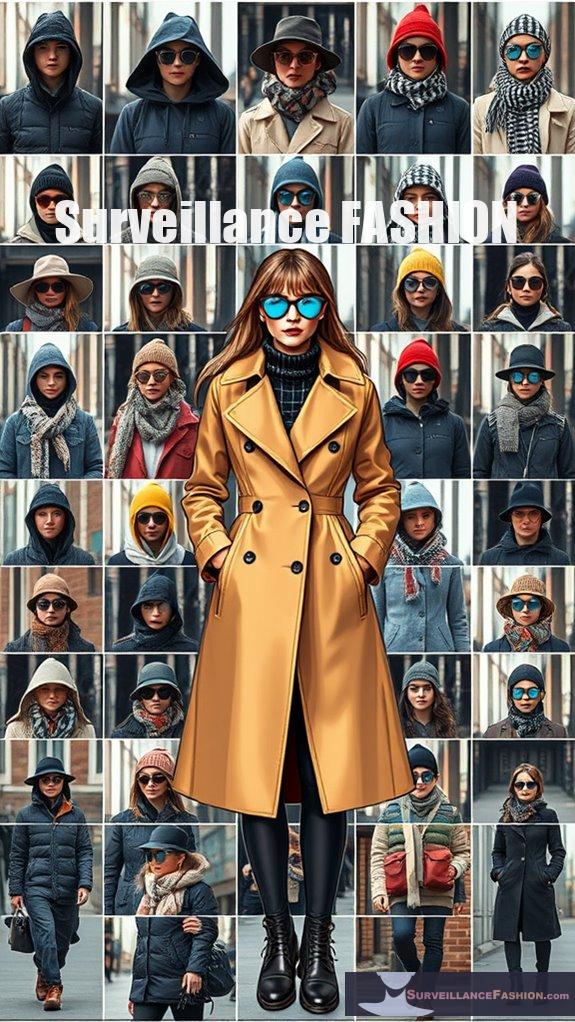
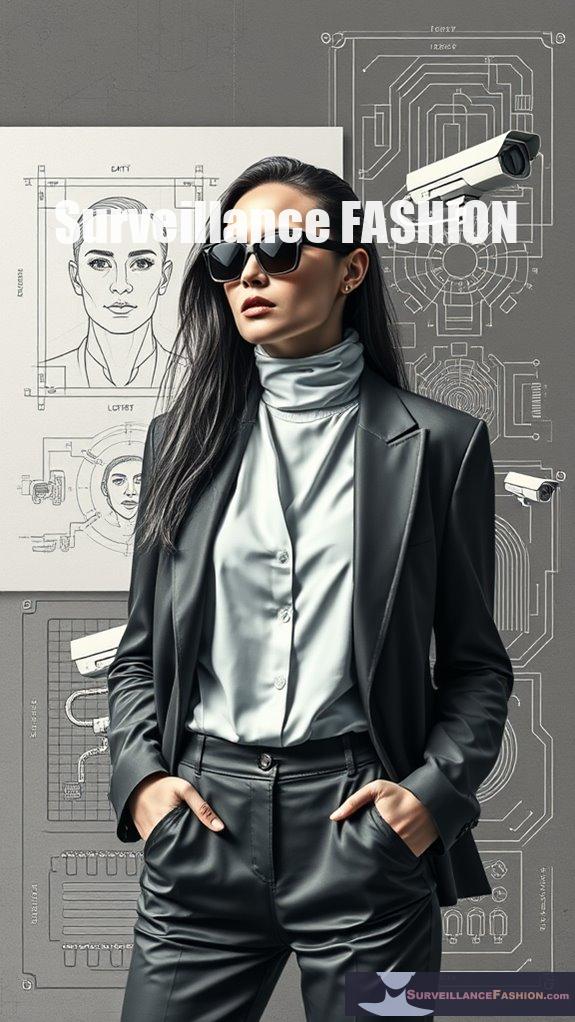
Disguising With Oversized Accessories
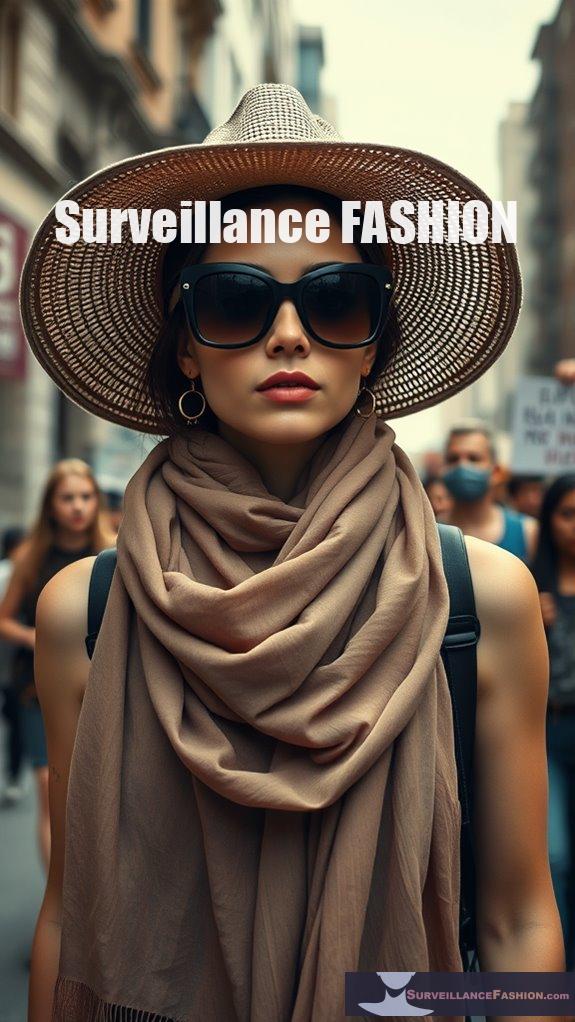
Oversized accessories play a significant role in enhancing your anonymity at protests, serving as practical tools for evading surveillance while allowing you to participate actively in social movements.
Consider these effective strategies:
- Opt for oversized clothing that conceals identifying features like birthmarks or tattoos, effectively reducing the visibility of your body shape. This approach aligns with the trend of anonymous silhouette-altering clothing that prioritizes discretion.
- Incorporate oversized headwear styles, such as hats or scarves, to obscure facial features and distinctive hairstyles.
- Use oversized sunglasses to obscure your eyes, making it more challenging for surveillance technology to recognize you.
- Avoid recognizable logos or vibrant colors, as neutral tones help you blend into the crowd seamlessly.
- Employing fashion ideas for cctv-defeating wearable technology can further enhance your ability to remain unnoticed in urban environments.
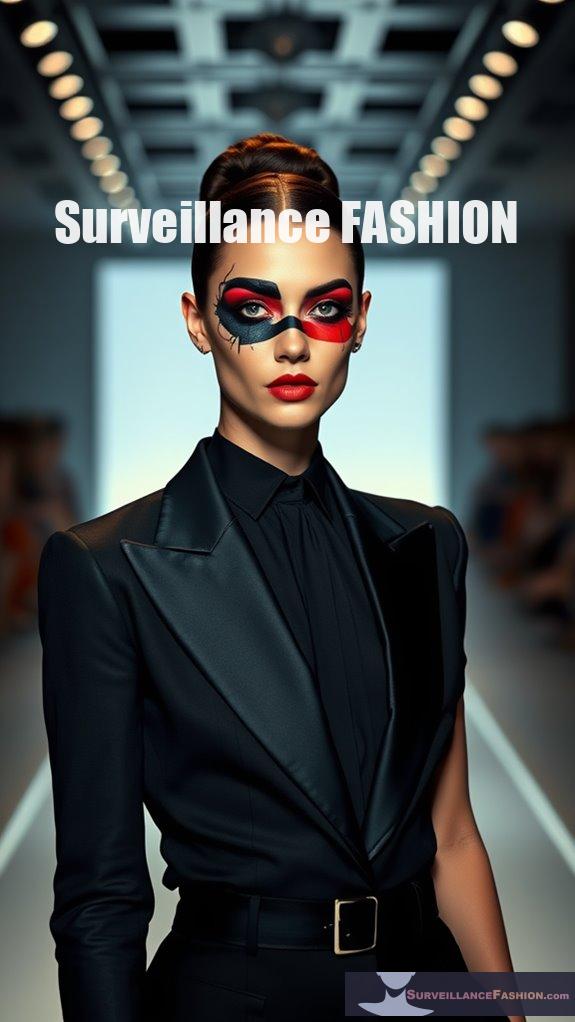
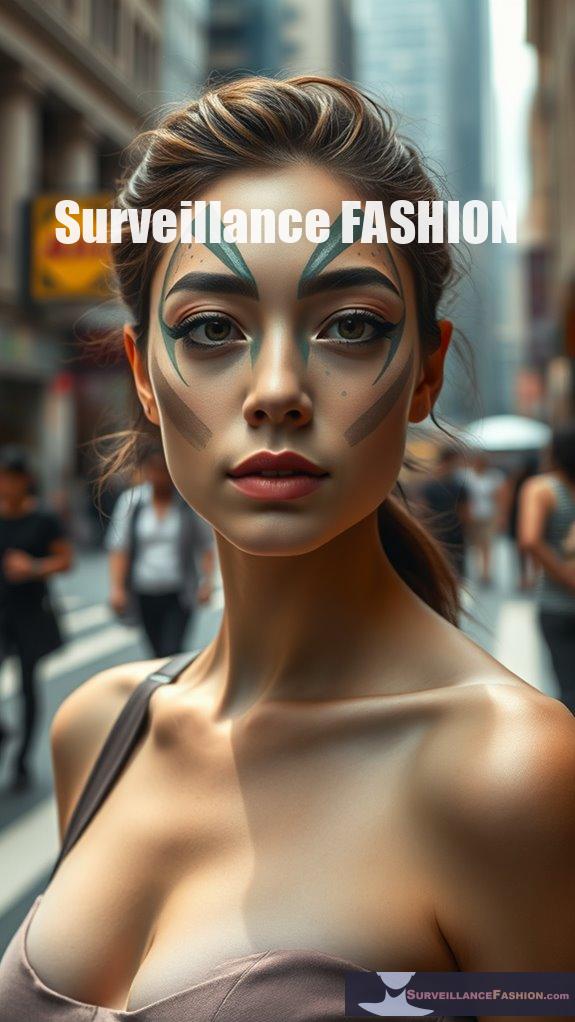
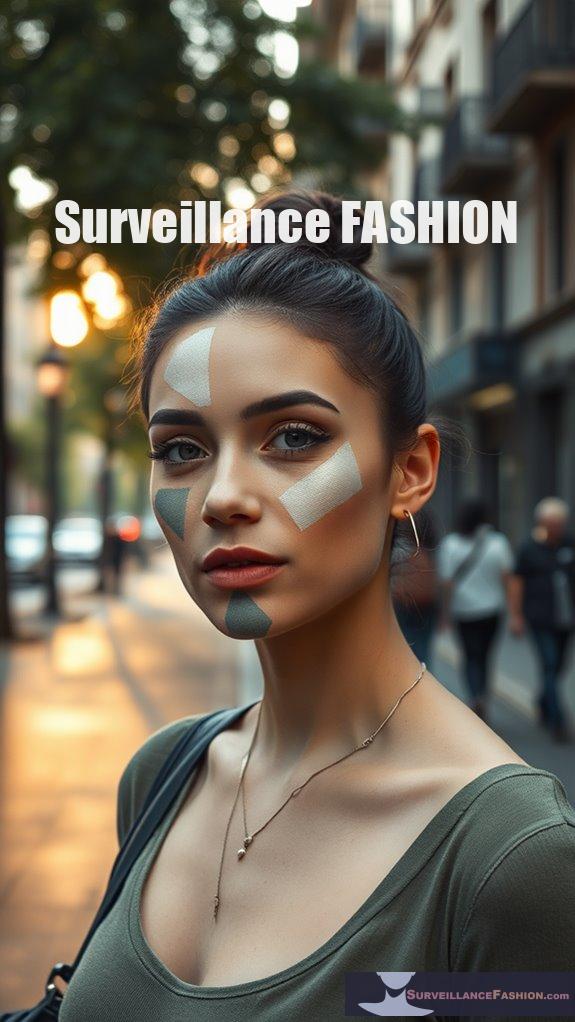
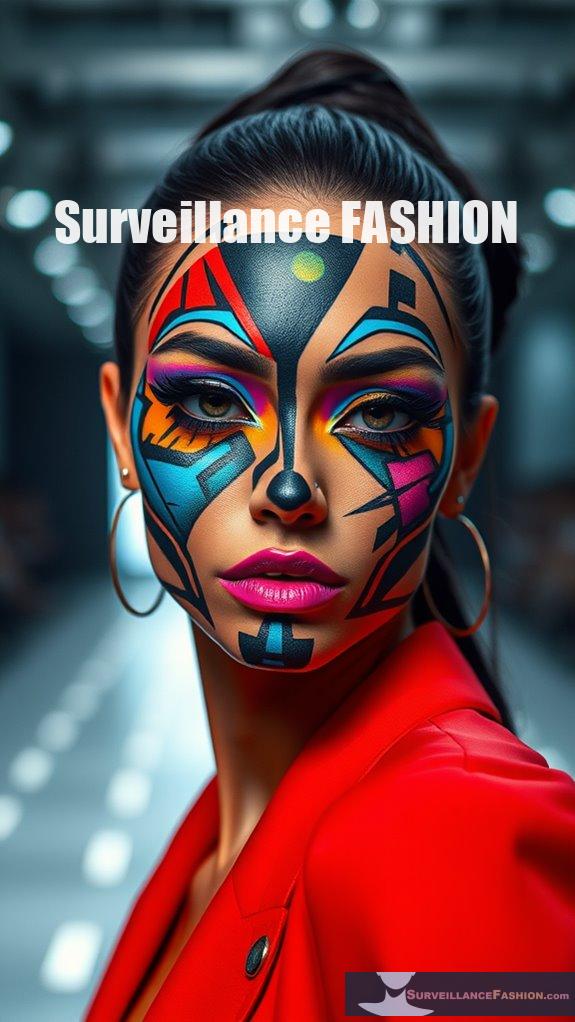
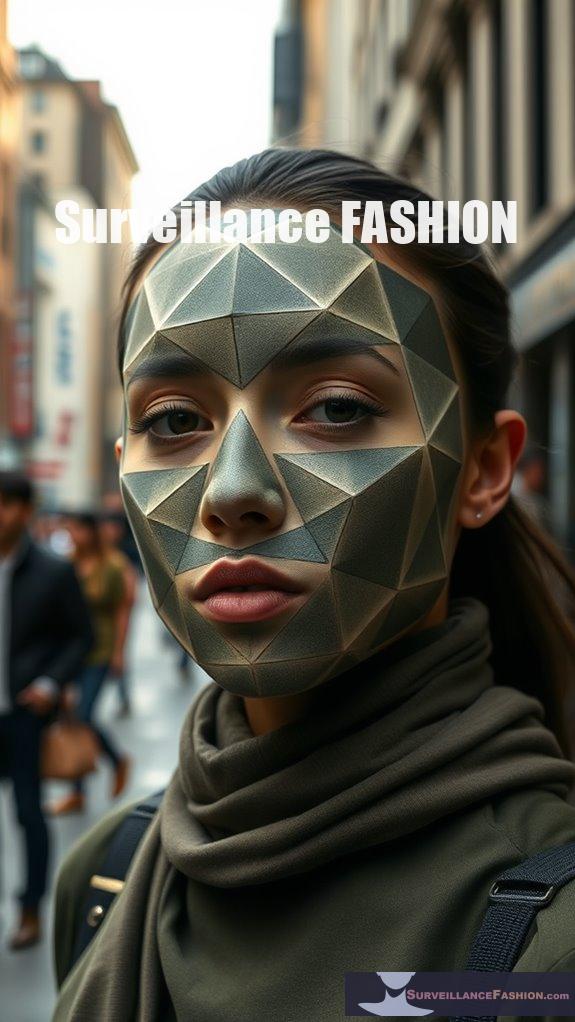
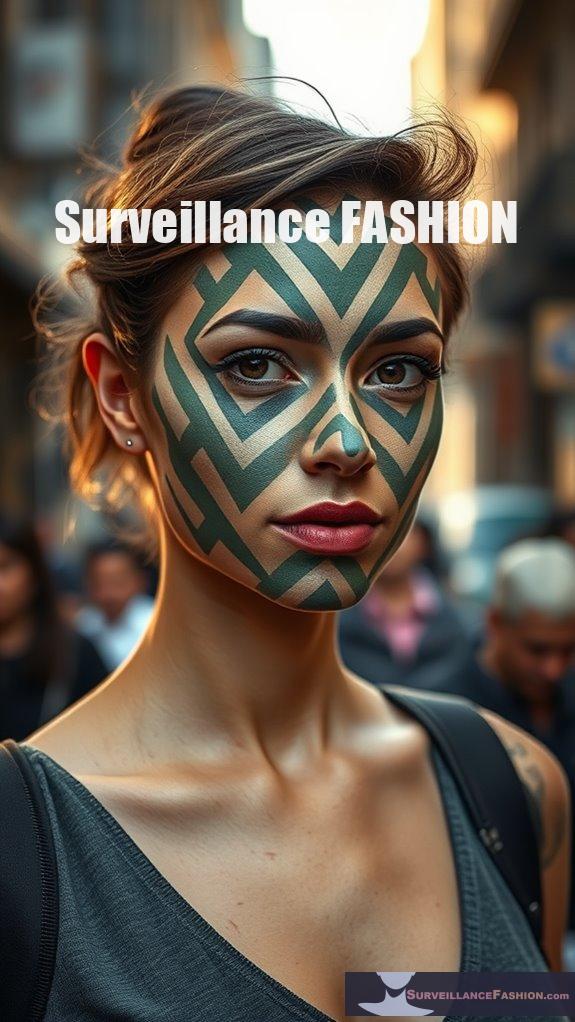
Masking With Creative Face Paint
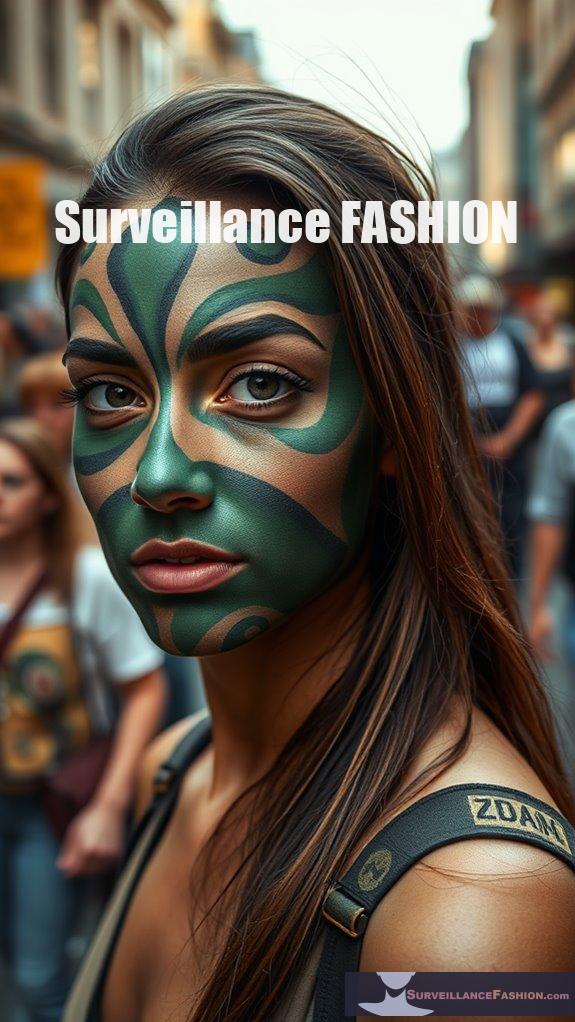
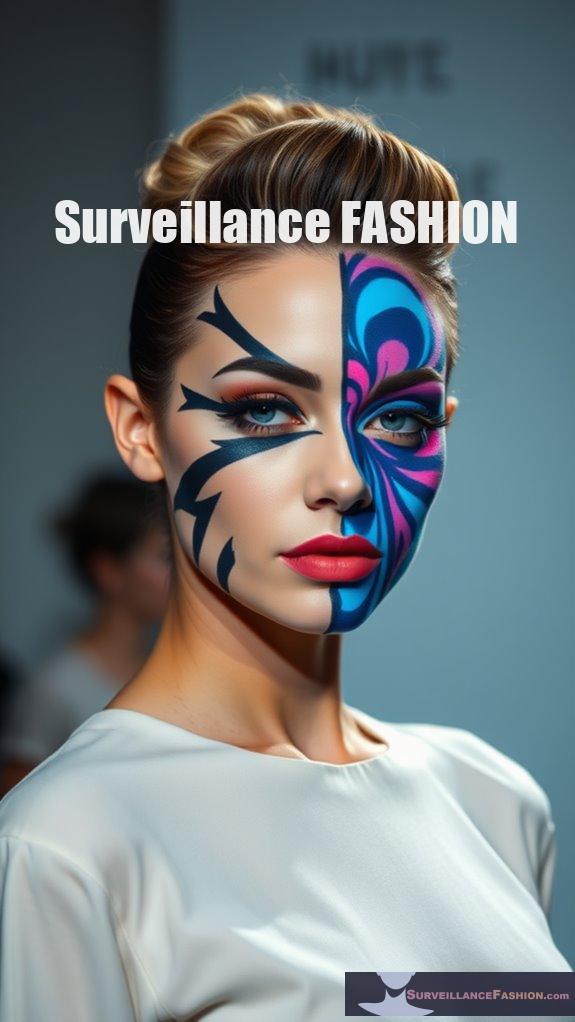
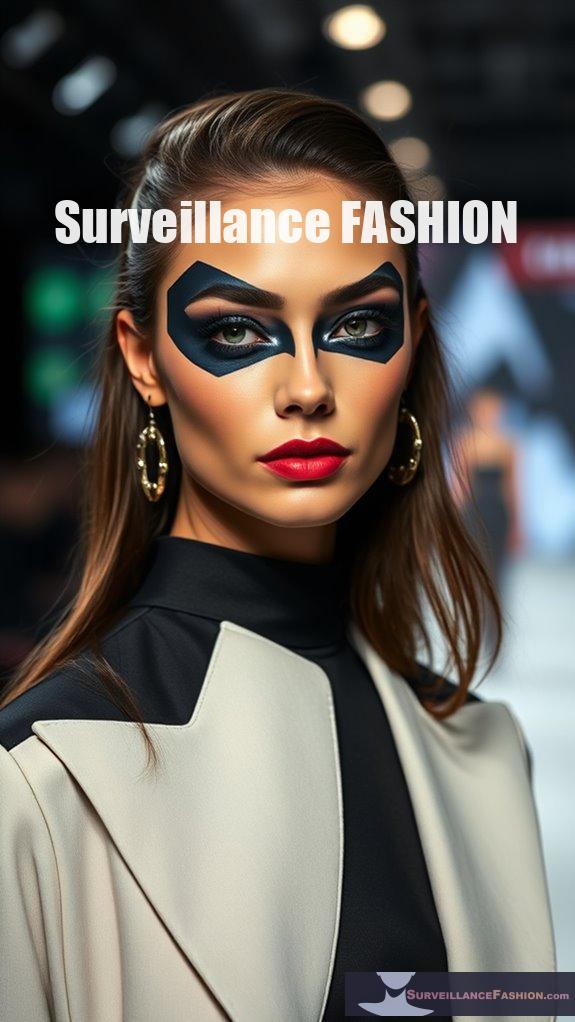
Creative face paint offers a unique and effective method for masking one's identity during protests, providing participants with an innovative approach to evade surveillance technology. By employing various masking techniques, such as CV Dazzle Makeup, which utilizes angular shapes and contrasting colors, you can obscure your facial features, making it harder for recognition algorithms to identify you. The use of dazzle makeup techniques can further enhance the effectiveness of your disguise.
Creative face paint is a powerful tool for obscuring identity and evading surveillance during protests.
Asymmetrical designs disrupt familiar patterns, while bright, bold colors draw attention away from your actual features. Techniques like nose bridge obscuration—covering the area where the nose, eyes, and forehead meet—further enhance your disguise. Additionally, incorporating unconventional hairstyles or thick black lines can amplify your creative expression, creating a striking visual statement against surveillance.
It's essential to remember that anti-facial recognition makeup techniques can vary in effectiveness depending on the technology used, so experimenting with different styles can yield better protection. While these methods may not fool advanced technology entirely, they serve as a powerful form of protest, and our website, Surveillance Fashion, aims to explore such innovative strategies, encouraging community involvement in identity protection.
References
- https://holistic-security.tacticaltech.org/chapters/act/4-1-4-protests-protect-your-identity-and-information.html
- https://banthescan.amnesty.org/wp-content/uploads/2024/04/Amnesty-Tech-Toolkit-FINAL36.pdf
- https://www.acludc.org/en/how-defend-against-police-surveillance-protests
- https://www.eff.org/deeplinks/2016/11/digital-security-tips-for-protesters
- https://www.vice.com/en/article/guide-protect-digital-privacy-during-protest/
- https://afrotech.com/heres-how-to-manipulate-tech-to-protect-your-privacy-at-protests
- https://wonderfulmachine.com/article/expert-advice-packing-for-a-protest/
- https://www.digitaltrends.com/news/cv-dazzle-makeup-facial-recognition-protests/
- https://www.codastory.com/authoritarian-tech/juggalo-paint-surveillance/
- https://www.themoscowtimes.com/2020/02/07/moscow-activists-protest-widespread-facial-recognition-with-face-paint-a69205